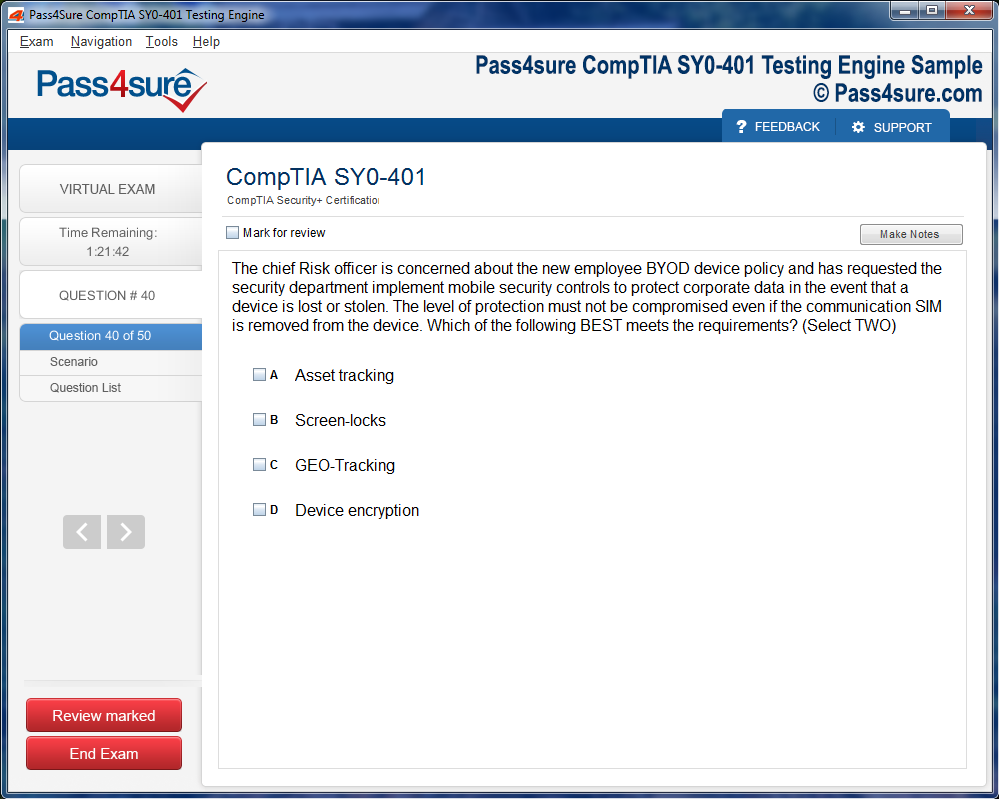
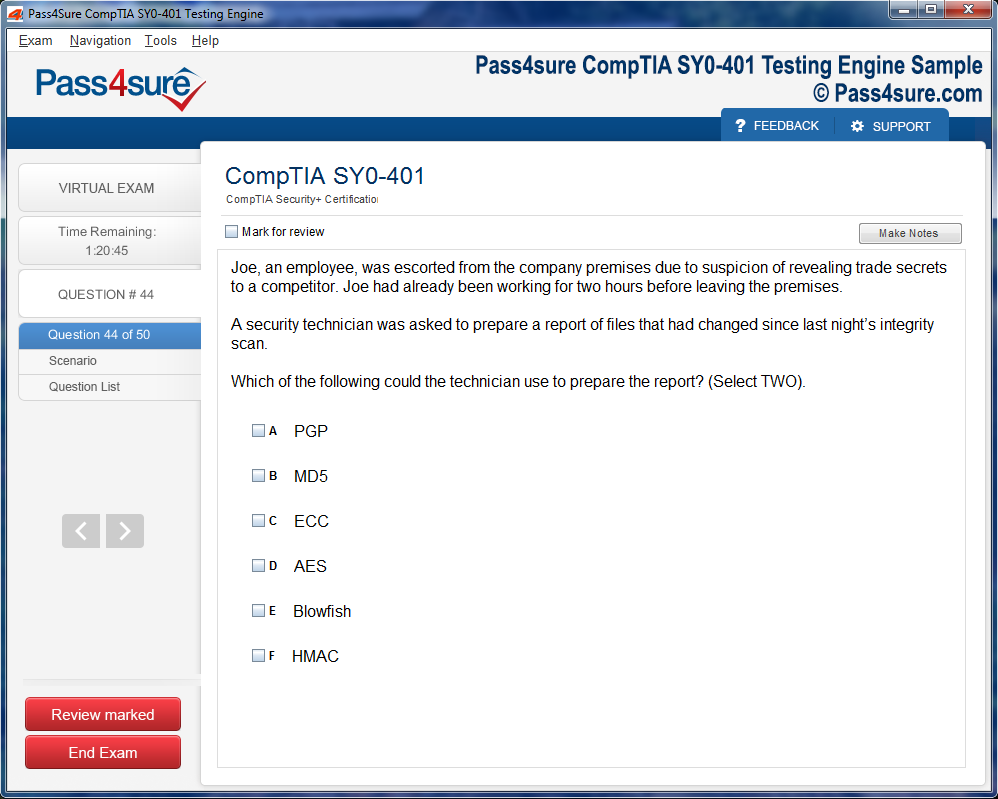
Product Screenshots
Frequently Asked Questions
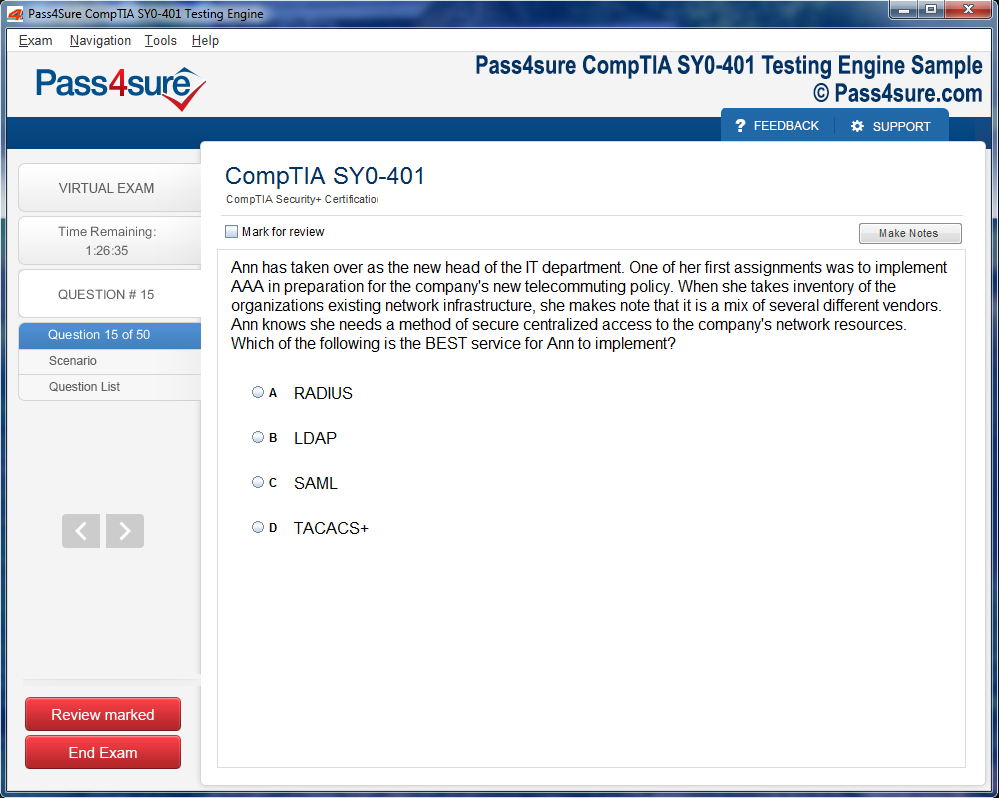
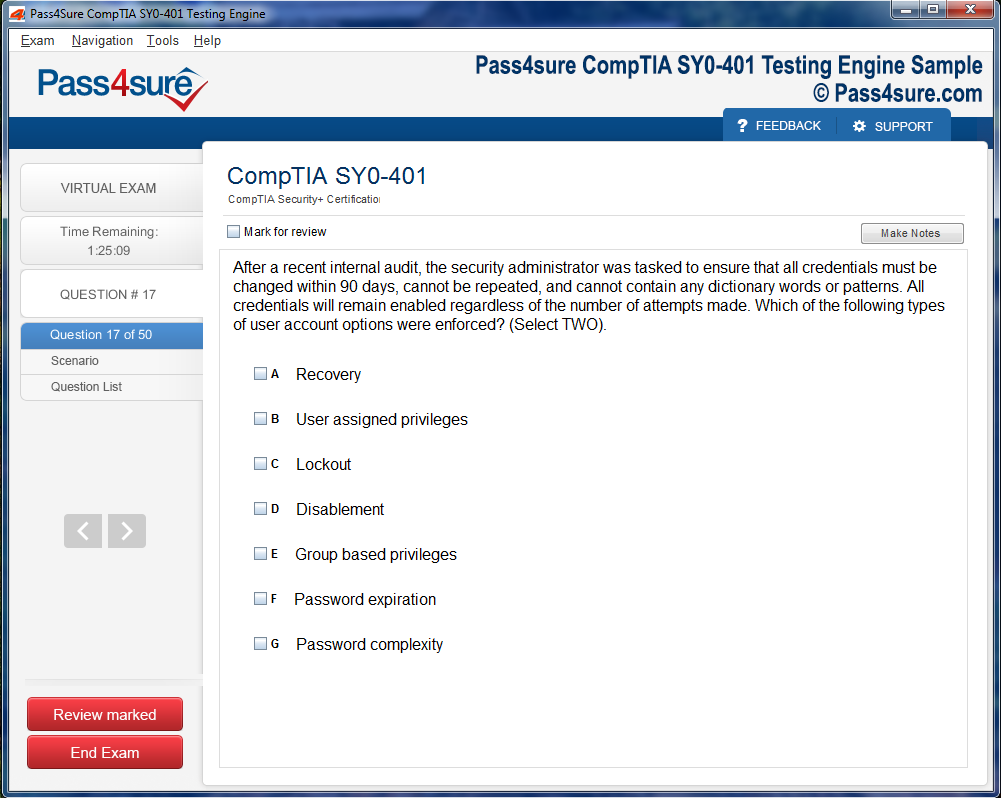
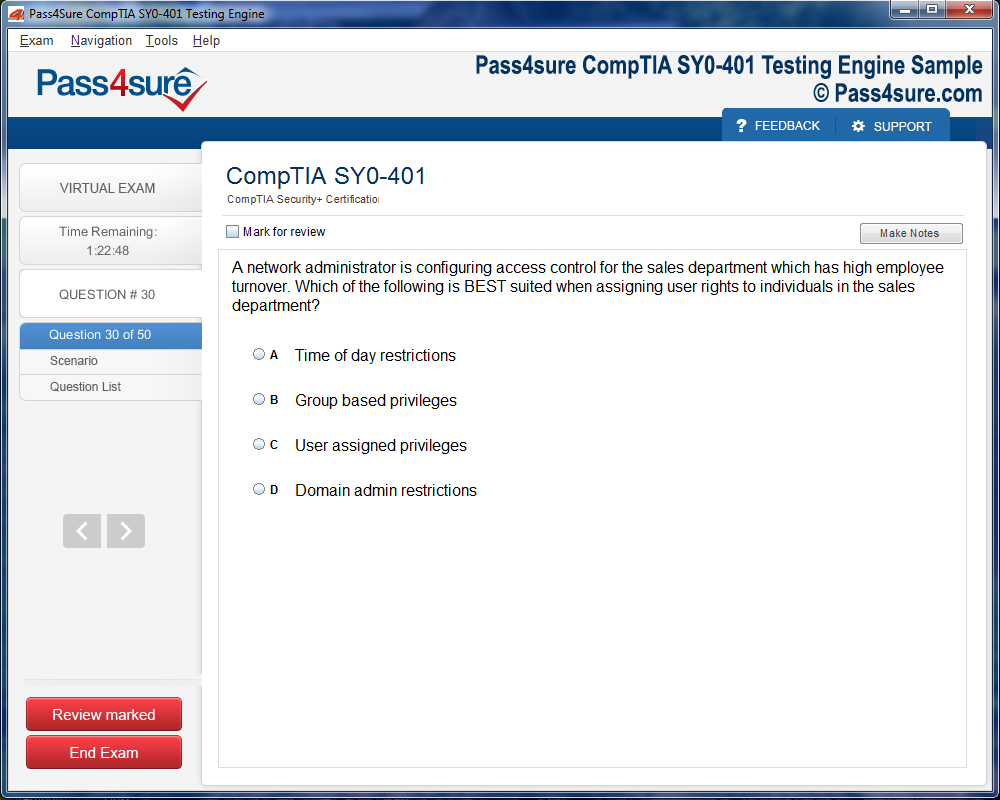
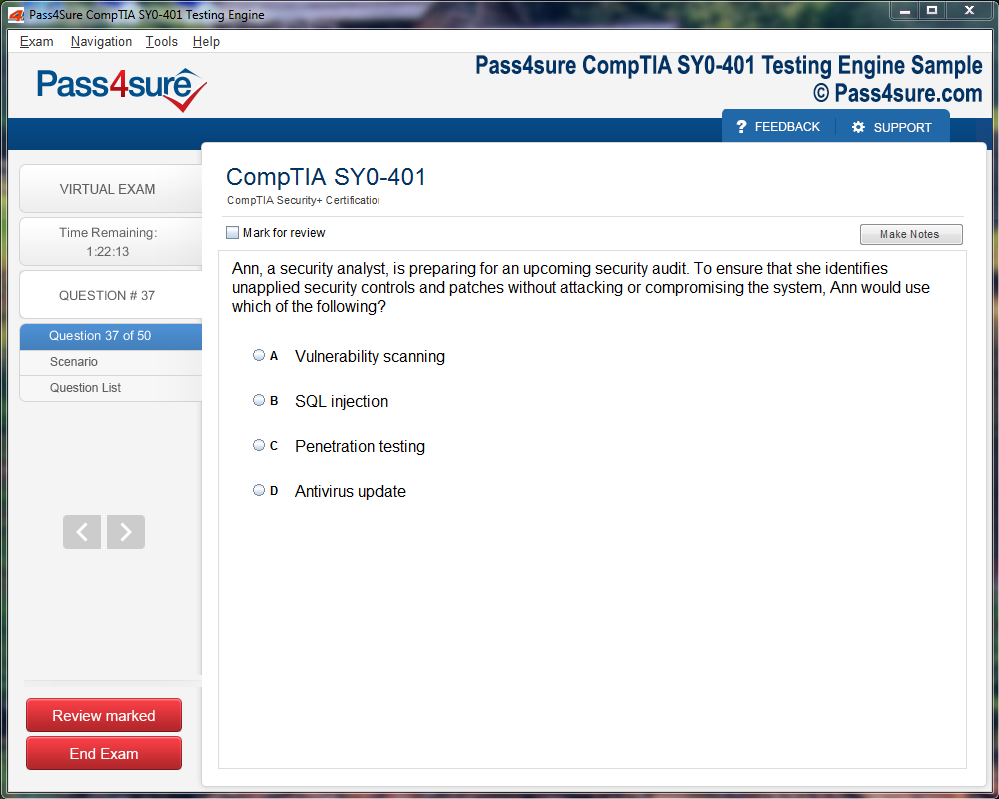
How does your testing engine works?
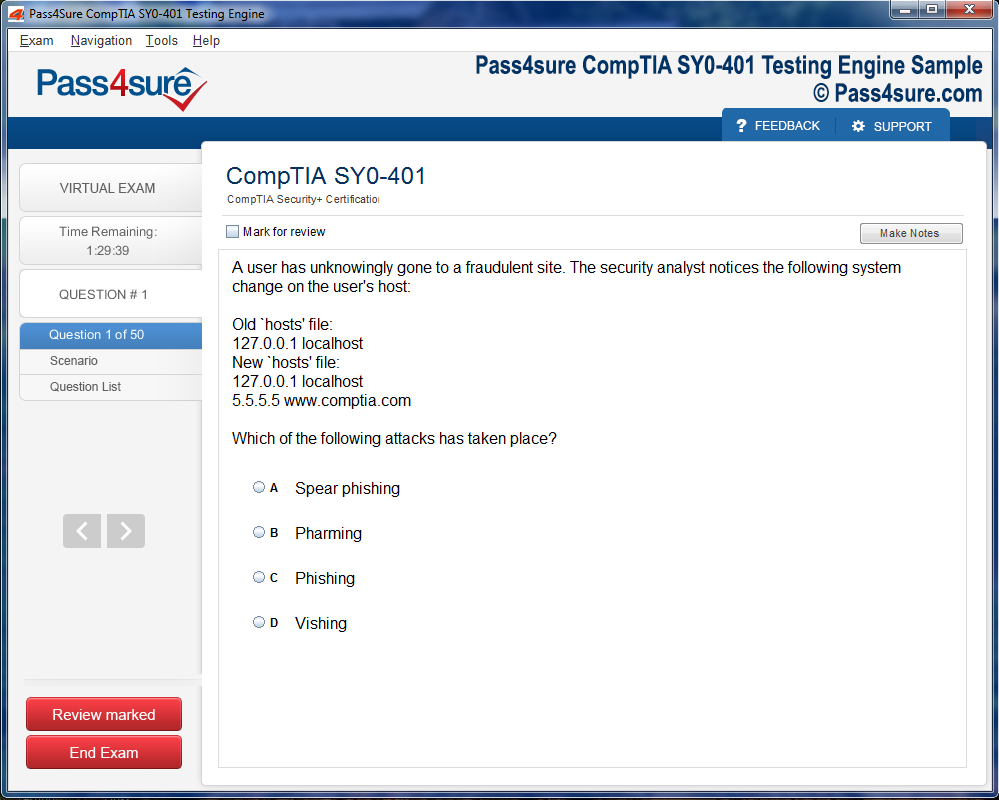
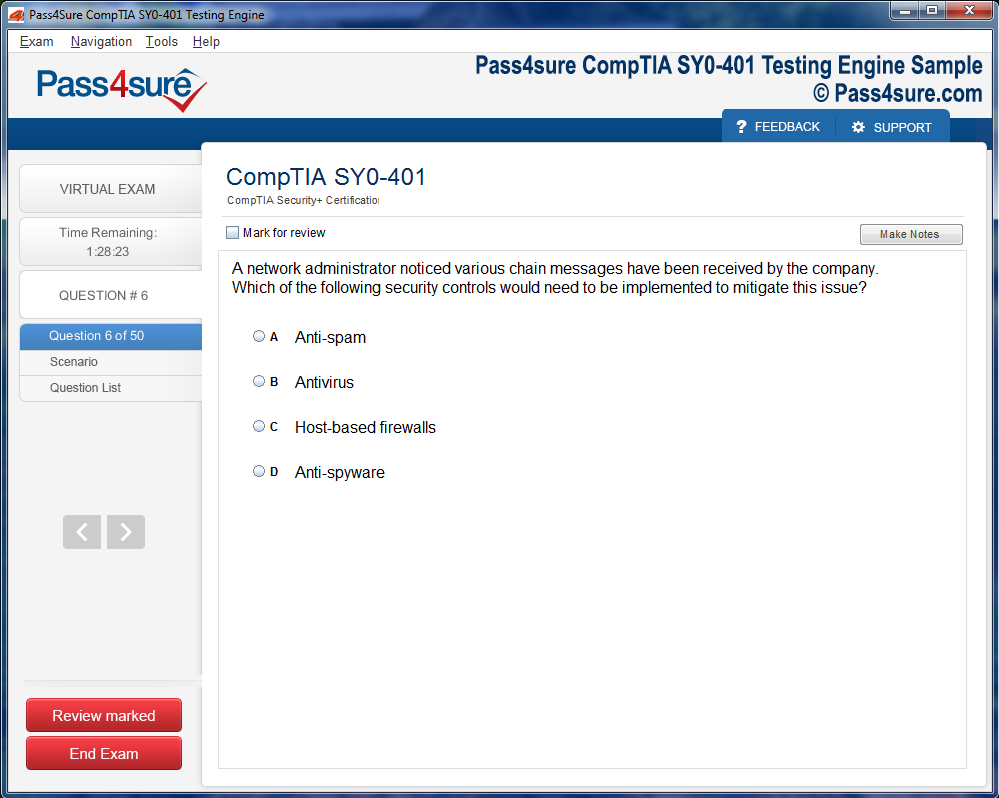
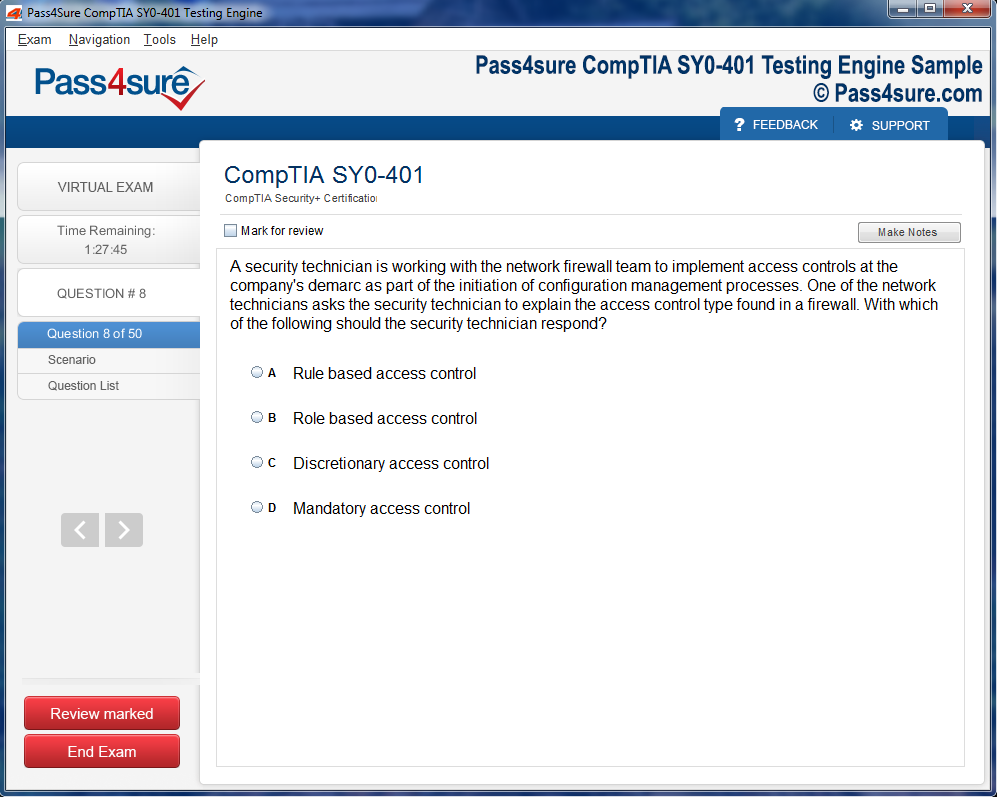
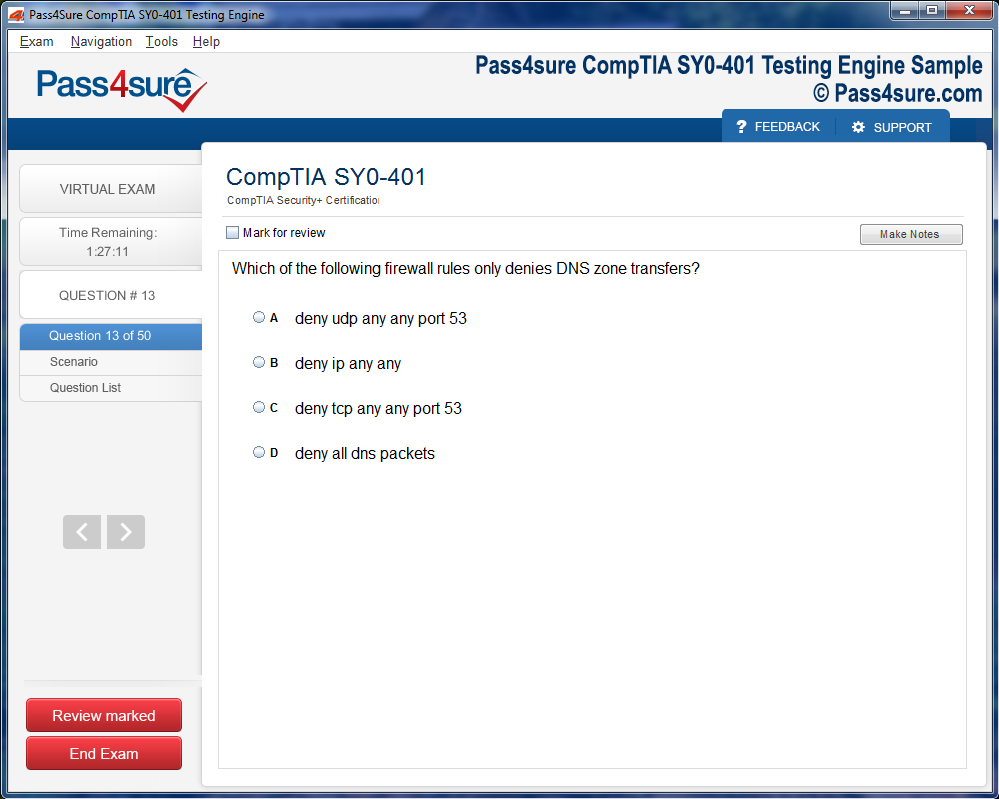
Once download and installed on your PC, you can practise test questions, review your questions & answers using two different options 'practice exam' and 'virtual exam'. Virtual Exam - test yourself with exam questions with a time limit, as if you are taking exams in the Prometric or VUE testing centre. Practice exam - review exam questions one by one, see correct answers and explanations.
How can I get the products after purchase?
All products are available for download immediately from your Member's Area. Once you have made the payment, you will be transferred to Member's Area where you can login and download the products you have purchased to your computer.
How long can I use my product? Will it be valid forever?
Pass4sure products have a validity of 90 days from the date of purchase. This means that any updates to the products, including but not limited to new questions, or updates and changes by our editing team, will be automatically downloaded on to computer to make sure that you get latest exam prep materials during those 90 days.
Can I renew my product if when it's expired?
Yes, when the 90 days of your product validity are over, you have the option of renewing your expired products with a 30% discount. This can be done in your Member's Area.
Please note that you will not be able to use the product after it has expired if you don't renew it.
How many computers I can download Pass4sure software on?
You can download the Pass4sure products on the maximum number of 2 (two) computers or devices. If you need to use the software on more than two machines, you can purchase this option separately. Please email sales@pass4sure.com if you need to use more than 5 (five) computers.
What are the system requirements?
Minimum System Requirements:
- Windows XP or newer operating system
- Java Version 8 or newer
- 1+ GHz processor
- 1 GB Ram
- 50 MB available hard disk typically (products may vary)
What operating systems are supported by your Testing Engine software?
Our testing engine is supported by Windows. Andriod and IOS software is currently under development.
100-890: Your Guide to Supporting Cisco Collaboration Devices
The modern enterprise relies heavily on collaboration technology to maintain productivity across distributed teams. Organizations today face the challenge of integrating various communication platforms while ensuring reliability and performance. The complexity of these systems requires professionals who possess specialized knowledge in configuring, managing, and troubleshooting collaboration infrastructure. This expertise becomes increasingly valuable as businesses expand their digital footprints and adopt hybrid work models that demand robust communication solutions.
Professional certification pathways provide structured approaches to mastering these essential competencies. The journey toward becoming proficient in collaboration device support involves hands-on experience with real-world scenarios and comprehensive preparation strategies. Microsoft's latest AI assistants demonstrate how artificial intelligence is reshaping the landscape of enterprise productivity tools. These advancements parallel the evolution happening within collaboration platforms, where intelligent automation and enhanced user experiences drive adoption and satisfaction rates across organizations of all sizes.
Quality Assurance Processes in Enterprise Communication Systems
Maintaining high standards in collaboration environments requires systematic approaches to quality control and performance monitoring. Organizations must establish clear benchmarks for acceptable service levels while implementing continuous improvement methodologies. The technical staff responsible for these systems needs to understand both the underlying architecture and the business requirements that drive deployment decisions. This dual perspective enables them to balance technical capabilities with organizational objectives effectively.
Testing protocols form an integral component of any successful collaboration deployment strategy. Teams must verify functionality across various scenarios, including peak usage periods and potential failure conditions. Mixed reality applications represent emerging frontiers that collaboration professionals should monitor closely. These immersive technologies may soon integrate with traditional communication platforms, creating new opportunities and challenges for support teams who must adapt to rapidly changing technological landscapes while maintaining operational stability.
Security Frameworks Protecting Collaborative Workspaces
The protection of sensitive communication channels remains paramount in today's threat landscape where malicious actors constantly seek vulnerabilities to exploit. Collaboration platforms handle confidential business discussions, proprietary information, and personal data that require robust security measures. Professionals supporting these systems must stay informed about emerging threats and implement defense strategies that address multiple attack vectors simultaneously. This proactive approach minimizes risk exposure while maintaining the seamless user experience that drives platform adoption.
Authentication mechanisms, encryption protocols, and access controls form the foundation of secure collaboration environments. Regular security audits help identify potential weaknesses before they can be exploited by unauthorized parties. Recent email breach incidents highlight the ongoing challenges organizations face in protecting communication channels. These real-world examples underscore the importance of comprehensive security training for support personnel who serve as the first line of defense against increasingly sophisticated cyber threats targeting collaboration infrastructure.
Scalability Considerations for Growing Communication Platforms
Organizations experience fluctuating demands on their collaboration infrastructure as they grow, merge, or restructure operations. The ability to scale systems efficiently without service disruptions represents a critical capability for support teams. Planning for expansion requires careful analysis of current utilization patterns, projected growth trajectories, and potential bottlenecks that could impede performance. These assessments inform decisions about hardware procurement, bandwidth allocation, and architectural modifications needed to accommodate future requirements.
Cloud-based solutions offer flexibility advantages over traditional on-premises deployments when addressing scalability challenges. However, hybrid approaches that combine both models often provide optimal results for organizations with diverse requirements. Premium feature transitions illustrate how vendors adjust their service tiers to accommodate different organizational needs. Support professionals must understand these evolving licensing models to provide accurate guidance when planning infrastructure investments that align with both technical requirements and budgetary constraints across various business units.
Integration Methodologies Connecting Disparate Communication Tools
Modern enterprises rarely rely on a single communication platform, instead operating diverse toolsets that serve different functional requirements. The challenge lies in creating cohesive experiences that allow seamless transitions between these systems without sacrificing functionality or user satisfaction. Integration specialists must possess deep knowledge of various application programming interfaces, data formats, and communication protocols. This technical foundation enables them to build connections that enhance rather than complicate the overall collaboration ecosystem.
Interoperability testing ensures that integrated systems function correctly under various conditions and usage patterns. Documentation of integration points and data flows helps troubleshooting efforts when issues arise during normal operations. Support lifecycle extensions affect long-term integration strategies that organizations must consider. These vendor commitments provide planning horizons for technology refresh cycles and help support teams prepare for eventual migrations while maintaining stable operations throughout transition periods that can span multiple years.
Performance Optimization Techniques Enhancing User Experiences
The responsiveness and reliability of collaboration tools directly impact user productivity and satisfaction levels across organizations. Performance optimization requires systematic analysis of system behaviors under various load conditions and user patterns. Support professionals employ specialized monitoring tools to identify bottlenecks, resource constraints, and configuration issues that degrade performance. These insights drive targeted improvements that deliver measurable enhancements to the overall user experience without requiring wholesale system replacements.
Network quality, endpoint capabilities, and server resources all contribute to perceived performance in collaboration environments. Balancing these factors requires holistic approaches that consider the entire communication path from end user to backend infrastructure. Machine learning certifications prepare professionals to leverage artificial intelligence for predictive performance management. These advanced techniques enable proactive identification of potential issues before they impact users, representing the next evolution in collaboration infrastructure support methodologies.
Troubleshooting Frameworks Resolving Common Device Issues
Systematic problem resolution approaches separate effective support professionals from those who rely on trial-and-error methods. Structured troubleshooting frameworks guide technicians through logical diagnostic sequences that efficiently identify root causes. These methodologies incorporate knowledge of common failure patterns, vendor-specific quirks, and environmental factors that influence system behavior. Documentation of resolution steps builds organizational knowledge bases that accelerate future troubleshooting efforts and reduce mean time to recovery.
Remote diagnostic capabilities have become increasingly important as distributed workforces expand across geographical boundaries. Support teams must master tools that enable effective problem resolution without physical access to affected devices or locations. Cloud career advancement opportunities demonstrate the broader industry trends toward remote infrastructure management. These same principles apply to collaboration device support where cloud-based management platforms provide centralized visibility and control across geographically dispersed deployments.
Capacity Planning Approaches Preventing Resource Shortages
Proactive resource management prevents performance degradations that occur when systems approach or exceed their operational limits. Capacity planning requires ongoing analysis of utilization trends, seasonal variations, and business growth projections. Support teams must translate these insights into concrete recommendations about infrastructure investments, configuration changes, or service level adjustments. This forward-looking approach minimizes reactive emergency responses that disrupt operations and consume disproportionate resources compared to planned upgrades.
Baseline establishment provides the reference points necessary for identifying abnormal resource consumption patterns that may indicate problems. Regular capacity reviews ensure that infrastructure remains aligned with evolving organizational requirements and usage patterns. Database specialty preparation emphasizes the importance of understanding data management fundamentals. These same principles apply to collaboration systems where call detail records, configuration databases, and user directories require careful management to ensure optimal system performance and reliable operations.
Vendor Relationship Management Maximizing Support Resources
Effective collaboration with equipment manufacturers and service providers enhances an organization's ability to resolve complex issues and plan strategic initiatives. Support professionals must understand vendor escalation processes, warranty terms, and available technical resources. Building productive relationships with vendor technical teams facilitates knowledge transfer and provides access to specialized expertise when internal capabilities prove insufficient. These partnerships become particularly valuable during major incidents or large-scale deployments that require vendor involvement.
Maintenance agreements and support contracts require careful evaluation to ensure alignment with organizational risk tolerance and operational requirements. Different service tiers offer varying response times, coverage hours, and included services that impact total cost of ownership. Systems operations certifications prepare professionals to navigate complex vendor relationships. These competencies prove valuable when negotiating contracts, managing renewals, and ensuring that purchased support services deliver expected value throughout their lifecycle.
Documentation Standards Creating Institutional Knowledge
Comprehensive documentation practices preserve critical information about system configurations, customization decisions, and troubleshooting experiences. Well-maintained documentation accelerates onboarding for new team members, facilitates knowledge transfer during staff transitions, and supports compliance requirements. Support teams must balance thoroughness with practicality, creating documentation that provides genuine value without becoming burdensome to maintain. Standardized templates and clear contribution guidelines help ensure consistency across the documentation library.
Version control and regular review cycles keep documentation current and relevant as systems evolve over time. Outdated information can mislead troubleshooting efforts or result in incorrect configuration changes that impact service quality. Administrator career paths emphasize documentation as a core professional competency. These best practices apply universally across technology domains where accurate record-keeping supports operational excellence and enables effective knowledge sharing.
Configuration Management Ensuring Consistent Device Behavior
Standardized configurations across collaboration device fleets simplify management and reduce troubleshooting complexity. Configuration management systems enable centralized control over device settings, firmware versions, and feature enablement across entire deployments. Support teams can implement changes consistently, roll back problematic updates, and maintain compliance with organizational standards. These capabilities become increasingly important as device counts grow and manual configuration approaches become impractical or error-prone.
Automated configuration deployment reduces the risk of human error while accelerating provisioning processes for new devices. Templates and policies ensure that devices consistently reflect current organizational requirements and security postures. Kubernetes fundamentals demonstrate container orchestration principles that parallel collaboration device management challenges. Both domains require systematic approaches to maintaining large fleets of similar but independently operating components that must work together cohesively.
Monitoring Infrastructure Detecting Problems Before User Impact
Comprehensive monitoring systems provide early warning of developing issues before they escalate into service-affecting incidents. Support teams deploy sensors and collectors that gather telemetry data from various system components, creating visibility into operational health. Alert thresholds trigger notifications when metrics deviate from expected ranges, enabling proactive intervention. This shift from reactive to proactive support reduces user impact and demonstrates the value of professional collaboration infrastructure management.
Dashboard visualization tools help support personnel quickly assess system status and identify trends that require attention. Historical data retention supports root cause analysis and capacity planning activities that inform strategic decisions. Kubernetes troubleshooting techniques illustrate advanced monitoring approaches applicable across technology domains. These sophisticated methods enable support teams to maintain high availability and performance standards even as system complexity increases.
Change Control Processes Minimizing Deployment Risks
Structured change management procedures protect production environments from unintended consequences of system modifications. Change control boards review proposed alterations, assess risks, and approve implementation plans before execution. This governance ensures that changes align with organizational objectives and receive appropriate testing and documentation. Support professionals must balance the need for agility with the importance of stability, implementing changes efficiently while minimizing service disruptions.
Rollback procedures provide safety nets when changes produce unexpected results or encounter unforeseen complications during implementation. Clear communication about planned changes helps users understand service windows and set appropriate expectations. Event monitoring strategies provide insights into change impact assessment. These monitoring capabilities enable support teams to quickly detect problems introduced by changes and execute recovery procedures before significant user impact occurs.
Service Level Management Meeting Organizational Expectations
Clearly defined service level agreements establish mutual understanding between support teams and business stakeholders about expected performance and availability. These agreements specify measurable objectives, response time commitments, and escalation procedures when targets are not met. Support professionals must track performance against these commitments, providing regular reports that demonstrate accountability and identify improvement opportunities. This transparency builds trust and justifies investments in infrastructure and staffing.
Continuous improvement initiatives address gaps between actual performance and service level targets through systematic problem-solving approaches. Root cause analysis of incidents reveals patterns that indicate systemic issues requiring architectural changes or process improvements. Headless service implementations demonstrate specialized deployment patterns that support specific use cases. Similarly, service level management requires tailored approaches that address unique organizational requirements and user expectations.
Training Programs Developing Internal Expertise
Investment in staff development ensures that support teams maintain current knowledge as collaboration technologies evolve rapidly. Formal training programs, vendor certifications, and hands-on laboratory experiences all contribute to building organizational capabilities. Support professionals who pursue continuous learning deliver greater value through improved problem-solving abilities and deeper technical understanding. Organizations benefit from reduced reliance on external consultants and faster resolution of complex issues.
Knowledge sharing sessions enable experienced team members to transfer specialized skills to colleagues, multiplying the impact of individual learning investments. Cross-training initiatives build redundancy that protects against single points of failure when key personnel are unavailable. Container orchestration education provides foundational skills increasingly relevant across technology domains. These competencies complement collaboration-specific expertise and position professionals to contribute across multiple organizational initiatives.
Disaster Recovery Planning Protecting Business Continuity
Comprehensive disaster recovery strategies ensure that collaboration services can be restored quickly following catastrophic failures or disasters. Recovery plans document procedures for rebuilding systems, restoring configurations, and recovering data from backup repositories. Regular testing validates these procedures and identifies gaps that could delay recovery during actual incidents. Support teams must maintain current documentation and ensure that all necessary resources remain accessible even when primary systems are unavailable.
Recovery time objectives and recovery point objectives drive technical decisions about backup frequency, redundancy levels, and failover capabilities. Business impact analysis helps prioritize recovery efforts when multiple systems require attention simultaneously. Advanced programming concepts illustrate the depth of technical knowledge required for complex system design. These same analytical approaches apply when architecting resilient collaboration infrastructures that maintain service availability despite component failures.
Mobile Device Integration Supporting Remote Workers
The proliferation of smartphones and tablets as collaboration endpoints introduces unique support challenges related to device diversity and user expectations. Support teams must master multiple operating systems, application versions, and network connectivity scenarios. Mobile device management platforms help standardize configurations and security policies across heterogeneous device populations. These tools enable remote troubleshooting and application deployment that would otherwise require extensive manual intervention.
Bandwidth constraints and cellular network characteristics impact mobile collaboration experiences differently than traditional wired or wireless LAN connections. Support professionals must understand these distinctions when troubleshooting audio or video quality complaints from mobile users. File handling techniques demonstrate low-level programming skills that inform advanced troubleshooting approaches. These technical foundations enable support personnel to understand application behaviors and diagnose problems that surface only under specific network conditions.
Codec Management Optimizing Media Quality
Audio and video codec selection significantly impacts bandwidth consumption, quality, and interoperability in collaboration environments. Support teams must understand codec characteristics, negotiation processes, and quality trade-offs when configuring systems. Different codecs offer varying compression ratios, processing requirements, and bandwidth efficiency that suit specific deployment scenarios. Proper codec management ensures optimal resource utilization while maintaining acceptable user experiences across diverse network conditions.
Transcoding capabilities enable communication between endpoints supporting different codec sets, expanding interoperability at the cost of additional processing resources. Bandwidth management policies may restrict codec choices during periods of network congestion to preserve overall system performance. Data storage fundamentals provide context for understanding how collaboration systems manage recorded content. These storage considerations influence retention policies, archive strategies, and backup approaches that support organizations must implement.
Analytics Platforms Driving Data-Informed Decisions
Business intelligence tools analyze collaboration usage patterns, identifying trends that inform strategic planning and resource allocation decisions. Support teams leverage these insights to optimize system configurations, predict capacity requirements, and demonstrate return on investment for infrastructure expenditures. Analytics platforms aggregate data from multiple sources, creating comprehensive views of organizational collaboration behaviors. These perspectives reveal opportunities for improving user experiences and increasing platform adoption rates.
Custom reporting capabilities enable stakeholders to access relevant metrics without requiring direct system access or specialized technical knowledge. Dashboard automation ensures that decision-makers receive timely information about system performance and usage trends. Information era navigation explores data analysis in broader contexts applicable to collaboration analytics. These analytical approaches help organizations extract maximum value from the telemetry data their collaboration systems generate.
Regulatory Compliance Maintaining Legal Requirements
Industry regulations and data protection laws impose requirements on collaboration system implementations regarding data handling, retention, and privacy protections. Support professionals must understand applicable compliance frameworks and ensure that system configurations align with legal obligations. Regular compliance audits verify adherence to these requirements and identify potential violations before they result in penalties. Documentation demonstrating compliance becomes critical during regulatory reviews or legal proceedings.
Encryption requirements, data sovereignty considerations, and user consent mechanisms all impact collaboration system design and operation. Multi-jurisdictional organizations face particularly complex compliance landscapes requiring specialized expertise to navigate successfully. String manipulation precision exemplifies attention to detail necessary in technical work. This same meticulousness applies when implementing compliance controls that protect organizations from regulatory risks while enabling effective collaboration capabilities.
High Availability Architectures Eliminating Single Failure Points
Redundancy design principles ensure that collaboration services remain available despite individual component failures that inevitably occur in complex systems. High availability architectures distribute functionality across multiple servers, network paths, and geographic locations. Support teams must understand failover mechanisms, state synchronization, and session preservation techniques that enable seamless service continuation when components fail. These capabilities transform collaboration platforms from convenient tools into mission-critical business systems that organizations depend upon constantly.
Load balancing algorithms distribute user sessions across available resources while monitoring component health to detect failures quickly. Automated failover processes minimize service interruptions by redirecting traffic away from failed components without manual intervention. Service stability mechanisms illustrate modern approaches to maintaining consistent access to distributed applications. These architectural patterns apply directly to collaboration environments where users expect reliable connectivity regardless of underlying infrastructure conditions or maintenance activities.
Network Segmentation Strategies Improving Security Posture
Isolating collaboration traffic onto dedicated network segments reduces attack surfaces while improving performance through reduced broadcast domains and optimized quality of service policies. Network segmentation requires careful planning to ensure proper routing between segments while maintaining security boundaries that prevent unauthorized access. Support teams must coordinate with network administrators to implement segmentation strategies that balance security requirements against operational complexity and user convenience.
Virtual LANs and software-defined networking technologies enable flexible segmentation approaches that adapt to changing organizational requirements. Firewall rules and access control lists enforce security policies at segment boundaries while allowing legitimate collaboration traffic to flow freely. Secure file transfer methods demonstrate practical security implementations for specific use cases. These same security-conscious approaches inform collaboration network design where protecting sensitive communications requires multiple defensive layers.
Authentication Integration Streamlining User Access
Single sign-on implementations eliminate redundant authentication prompts that frustrate users and reduce security through password proliferation. Integrating collaboration platforms with enterprise identity management systems centralizes access control and simplifies user provisioning processes. Support teams must configure authentication protocols, certificate exchanges, and attribute mapping that enable seamless integration while maintaining security. These technical integrations deliver improved user experiences and reduce administrative overhead associated with account management.
Multi-factor authentication adds security layers that protect against credential theft and unauthorized access attempts. Conditional access policies enforce additional verification requirements based on user location, device posture, or risk assessments. Cisco certification resources provide pathways for developing expertise in network-centric technologies. These vendor-specific competencies complement broader collaboration knowledge and enable support professionals to design comprehensive solutions.
Quality of Service Prioritizing Critical Communication Traffic
Network congestion can severely degrade real-time collaboration experiences when audio and video packets compete with bulk data transfers for bandwidth. Quality of service mechanisms prioritize time-sensitive collaboration traffic over less critical data flows, ensuring acceptable performance during periods of network stress. Support teams must work with network administrators to implement end-to-end QoS policies that preserve packet prioritization across routing boundaries and carrier connections.
Traffic classification identifies collaboration packets requiring priority treatment while marking mechanisms communicate these requirements to network devices. Bandwidth reservation ensures that minimum throughput levels remain available for collaboration services regardless of other network demands. CISI credentials represent specialized knowledge domains relevant to specific industries. Similarly, collaboration support requires deep understanding of specialized protocols and behaviors that distinguish these systems from generic network applications.
Protocol Analysis Diagnosing Complex Communication Issues
Packet capture tools reveal the actual network conversations occurring between collaboration endpoints and infrastructure components. Support professionals skilled in protocol analysis can decode these captures to identify misconfigurations, incompatibilities, or performance bottlenecks that manifest as user-reported problems. This deep technical capability separates advanced troubleshooters from those limited to configuration-level diagnostics, enabling resolution of subtle issues that other approaches cannot address effectively.
Session Initiation Protocol traces show call setup sequences, codec negotiations, and error conditions that explain connection failures or quality problems. Media stream analysis reveals packet loss, jitter, and latency measurements that correlate with user-perceived quality degradations. Specialized examination preparation develops focused expertise in particular technology areas. These concentrated learning approaches prove effective when mastering complex protocols central to collaboration system operations.
Firmware Management Maintaining Device Currency
Regular firmware updates deliver bug fixes, security patches, and feature enhancements that improve collaboration device performance and reliability. Support teams must balance the benefits of current firmware against the risks of introducing new issues through untested updates. Staged rollout approaches allow validation on limited device populations before widespread deployment, minimizing potential impact from problematic releases. Version tracking ensures that device populations remain consistent and supportable.
Automated update mechanisms simplify firmware distribution across large device fleets while providing rollback capabilities when problems emerge. Testing protocols verify critical functionality following updates before returning devices to production service. Archer administration exemplifies vendor-specific management competencies required for specialized platforms. These same principles apply when maintaining collaboration device firmware across diverse product lines.
API Utilization Extending Platform Capabilities
Application programming interfaces enable custom integrations that extend collaboration platform functionality beyond out-of-box capabilities. Support teams with development skills can create automation scripts, custom reports, and workflow integrations that address unique organizational requirements. API documentation and software development kits provide the resources necessary to build these extensions while maintaining supportability and upgrade compatibility. These customizations differentiate adequate collaboration deployments from optimized implementations tailored to specific business processes.
RESTful APIs and webhooks enable event-driven integrations that trigger actions in external systems based on collaboration platform activities. Authentication and rate limiting protect API endpoints from abuse while ensuring fair resource allocation among competing consumers. SecurID foundations address authentication technologies increasingly integrated with collaboration platforms. These security integrations enhance protection against unauthorized access while supporting modern identity management approaches.
Database Maintenance Preserving System Performance
Collaboration platforms rely on backend databases that store configurations, user information, and call detail records. Regular database maintenance prevents performance degradations that occur as data volumes grow over time. Index optimization, statistics updates, and data purging routines keep databases operating efficiently under production loads. Support teams must schedule these maintenance activities during appropriate windows while monitoring their impact on system availability and responsiveness.
Backup verification ensures that database recovery procedures will function correctly when needed during disaster recovery scenarios. Transaction log management prevents storage consumption issues that could halt system operations when log volumes exhaust available disk space. Data loss prevention specialists focus on protecting sensitive information across enterprise systems. These same data protection principles apply to collaboration databases containing confidential communications and personal information.
Certificate Lifecycle Management Maintaining Trust Relationships
Digital certificates enable encrypted communications and authenticate system components within collaboration infrastructures. Certificate expiration causes service disruptions when endpoints reject connections from systems presenting invalid credentials. Support teams must track certificate expiration dates, renew certificates before expiration, and deploy updated certificates across affected systems. Automated monitoring alerts personnel to approaching expiration deadlines, preventing outages caused by expired certificates.
Certificate authorities, trust chains, and revocation checking mechanisms all impact how systems validate presented credentials during connection establishment. Wildcard certificates and subject alternative names provide flexibility in certificate deployment across multiple systems. Advanced DLP certifications demonstrate progression in specialized security domains. These deepening expertise levels parallel the growing sophistication required as collaboration security implementations mature.
Bandwidth Calculation Provisioning Adequate Network Resources
Accurate bandwidth estimation ensures that network connections can support planned collaboration loads without quality degradations. Support teams must account for codec choices, concurrent session counts, and protocol overhead when calculating requirements. Conservative estimates include growth margins that accommodate usage increases without requiring immediate infrastructure upgrades. These capacity projections inform network design decisions and circuit procurement activities.
Burst traffic patterns during peak usage periods require higher instantaneous bandwidth than average consumption calculations might suggest. Compression technologies and bandwidth optimization features reduce network demands but require processing resources at endpoints. Enterprise implementations address scalability challenges in large organizational contexts. These scaled deployments demand careful resource planning that accounts for aggregate demands across entire user populations.
Interoperability Testing Validating Multi-Vendor Environments
Organizations frequently deploy collaboration products from multiple vendors, creating interoperability challenges that require systematic testing to identify and resolve. Support teams must verify call flows between different systems, confirming that audio, video, and data channels function correctly across vendor boundaries. Standards compliance alone does not guarantee interoperability, as vendors implement optional features differently and interpret specifications in varying ways that can cause compatibility issues.
Test plans document specific scenarios requiring validation while results tracking identifies recurring problems that may require vendor escalation or workaround development. Interoperability labs provide controlled environments for testing without impacting production systems or users. Environmental security foundations address broader security contexts applicable across technology platforms. These holistic security perspectives inform comprehensive protection strategies for complex multi-vendor collaboration environments.
Cost Optimization Maximizing Infrastructure Investment Returns
Total cost of ownership includes initial procurement expenses, ongoing maintenance costs, and operational overhead associated with collaboration infrastructure. Support teams contribute to cost optimization through efficient resource utilization, lifecycle planning, and operational excellence that minimizes unplanned expenditures. Right-sizing deployments prevents over-provisioning waste while ensuring adequate capacity for current and projected needs. These balanced approaches deliver required capabilities within budgetary constraints.
Cloud versus on-premises deployment models offer different cost structures and operational characteristics that suit varying organizational requirements and constraints. Hybrid approaches combine both models to leverage respective strengths while mitigating weaknesses. Security infrastructure advancement represents continued professional development in specialized domains. These progressive competency levels enable professionals to tackle increasingly complex challenges as their careers advance.
User Adoption Strategies Driving Platform Utilization
Technical excellence alone does not guarantee successful collaboration platform deployments without corresponding user adoption that realizes intended benefits. Support teams contribute to adoption through responsive assistance, user education, and feedback incorporation that improves platform usability. Monitoring adoption metrics reveals which features users embrace and which require additional promotion or simplification. These insights guide ongoing enhancement efforts that increase platform value and user satisfaction.
Champion programs identify enthusiastic users who promote platform capabilities within their departments through peer influence and informal training. Gamification approaches reward desired behaviors while making platform engagement more enjoyable and memorable. Environmental security expertise demonstrates mastery in particular technology domains through recognized credentials. These achievements signal commitment to professional excellence that enhances career prospects and organizational contributions.
Accessibility Compliance Ensuring Inclusive Communication
Collaboration platforms must accommodate users with diverse abilities through accessibility features that remove barriers to effective participation. Support teams ensure that caption services, screen reader compatibility, and keyboard navigation alternatives function correctly across platform features. Regulatory requirements and organizational values both drive accessibility implementations that expand collaboration access to all employees regardless of physical or cognitive limitations.
Testing with actual users who rely on accessibility features reveals usability issues that theoretical compliance checks might miss. Alternative input methods and output modalities ensure that collaboration platforms serve users with visual, auditory, or motor impairments effectively. Level advancement recognizes progressive skill development in specialized technical areas. These credential progressions provide clear pathways for career advancement and expertise deepening.
Geographic Distribution Supporting Global Organizations
Multinational organizations require collaboration infrastructures that span multiple regions while accounting for varying network conditions, regulatory environments, and user requirements. Support teams must coordinate across time zones to provide continuous coverage and maintain consistent service experiences globally. Regional deployments balance centralized management with local responsiveness to connectivity challenges and cultural preferences that influence collaboration tool adoption and usage patterns.
Latency considerations impact media quality in geographically dispersed deployments where round-trip times affect interactive experiences. Content delivery networks and regional presence points reduce these delays by positioning resources closer to end users. Virtualization security addresses protection requirements for modern infrastructure approaches. These security considerations apply equally to collaboration platforms increasingly deployed on virtualized infrastructure.
Incident Response Procedures Minimizing Service Disruptions
Structured incident management processes ensure systematic responses to service-affecting problems regardless of when they occur. Support teams follow defined escalation paths, communication protocols, and resolution workflows that minimize confusion during high-pressure situations. Incident commanders coordinate response activities across multiple teams when complex problems require diverse expertise. Post-incident reviews identify improvement opportunities that strengthen organizational resilience against similar future incidents.
Status communication keeps stakeholders informed about incident progress, estimated resolution times, and workaround availability during outages. Transparency builds trust and manages expectations when problems cannot be resolved immediately. Advanced virtualization security builds upon foundational concepts with deeper technical implementations. These progressive learning paths enable professionals to develop specialized expertise that differentiates them in competitive employment markets.
Asset Management Tracking Infrastructure Components
Comprehensive asset inventories document collaboration infrastructure components, their configurations, and relationships to other systems. Accurate asset tracking supports capacity planning, maintenance scheduling, and incident response activities that require detailed system knowledge. Configuration management databases link physical and logical assets to create complete infrastructure pictures. These information repositories become increasingly valuable as deployments grow and staff turnover occurs.
Automated discovery tools maintain current asset information by regularly scanning networks to identify deployed devices and their characteristics. Lifecycle tracking highlights aging equipment requiring replacement before failures disrupt services. Security access management focuses on controlling system access through various authentication and authorization mechanisms. These identity management competencies complement collaboration expertise where controlling who can access communication systems proves critical for security.
Patch Management Maintaining Security Currency
Security vulnerabilities discovered in collaboration software require timely patching to prevent exploitation by malicious actors. Support teams must evaluate patches, test them in non-production environments, and deploy them according to organizational change control procedures. Critical security patches may require expedited deployment outside normal maintenance windows when vulnerability severity justifies operational risk. Comprehensive patch tracking ensures no systems remain vulnerable due to missed updates.
Dependency management identifies which systems require updates when patches affect shared libraries or underlying operating system components. Rollback planning provides recovery paths when patches introduce unexpected problems or incompatibilities. Advanced access management represents deeper expertise in identity and access control domains. These advanced competencies enable professionals to design sophisticated security architectures that protect sensitive collaboration environments.
Performance Baseline Establishment Creating Reference Points
Initial performance measurements create baselines against which future metrics are compared to identify degradations or improvements. Support teams collect comprehensive data during stable operation periods to establish normal behavior patterns. These baselines inform capacity planning, troubleshooting activities, and quality assessments. Without established baselines, determining whether current performance is acceptable becomes subjective rather than data-driven.
Seasonal variations and business cycle impacts require multiple baseline sets representing different operational states. Threshold tuning ensures that alerts trigger appropriately without generating false alarms from normal variations. Comprehensive certifications validate broad competency across technology domains through rigorous examinations. These credentials demonstrate commitment to professional development and mastery of complex subject matter.
Automation Development Reducing Manual Effort
Repetitive support tasks consume valuable time that could be applied to higher-value activities requiring human judgment and creativity. Automation scripts handle routine operations, status checks, and standard configurations without manual intervention. Support teams with scripting capabilities create these automations, improving consistency while freeing personnel for complex problem-solving. Well-designed automation includes error handling and logging that enables troubleshooting when scripts encounter unexpected conditions.
Workflow orchestration platforms coordinate multi-step processes spanning multiple systems through defined sequences of automated actions. Approval gates incorporate human oversight where appropriate while automation handles mechanical execution steps. Data security specialists concentrate on protecting information assets across their entire lifecycle. These data protection principles apply directly to collaboration systems handling sensitive business communications.
Disaster Simulation Testing Recovery Procedures
Regular disaster recovery testing validates documented procedures and identifies gaps before actual emergencies occur. Support teams execute recovery processes in controlled environments, measuring time requirements and noting unexpected challenges. Test results drive procedure refinements that improve recovery efficiency and reliability. Without regular testing, recovery plans become outdated as systems evolve, potentially failing when needed most.
Tabletop exercises engage stakeholders in scenario discussions without actual system disruptions, building familiarity with response procedures. Full-scale tests verify end-to-end recovery capabilities by actually rebuilding systems from backup repositories. Enhanced data protection advances security knowledge into specialized implementations. These deeper competencies enable professionals to address sophisticated threats targeting high-value collaboration data.
Capacity Modeling Projecting Future Requirements
Mathematical models project future capacity needs based on current trends, planned business initiatives, and historical growth patterns. Support teams use these projections to justify infrastructure investments before capacity constraints impact service quality. Accurate modeling requires understanding business drivers behind collaboration usage rather than simply extrapolating historical data. These strategic perspectives align technical planning with organizational objectives.
What-if scenarios explore capacity implications of various business outcomes, enabling contingency planning for different futures. Sensitivity analysis identifies which assumptions most significantly impact projections, focusing validation efforts on critical factors. Identity security expertise specializes in authentication and access control technologies. These focused competencies prove valuable as collaboration platforms integrate with enterprise identity management systems.
Vendor Evaluation Selecting Optimal Solutions
Technology refresh cycles require periodic evaluation of collaboration product offerings to ensure continued alignment with organizational needs. Support teams contribute technical assessments that complement business and financial analyses during selection processes. Proof-of-concept deployments validate vendor claims about capabilities, performance, and integration possibilities. These hands-on evaluations reveal practical considerations that product literature and demonstrations may not fully disclose.
Total cost of ownership calculations include support requirements, training needs, and integration efforts beyond initial acquisition costs. Reference checks with existing customers provide insights into vendor support quality and product maturity. Advanced identity management builds upon foundational authentication knowledge with sophisticated implementations. These progressive credentials demonstrate increasing expertise levels that employers value.
Migration Planning Transitioning Between Platforms
Platform migrations represent significant undertakings requiring careful planning to minimize user disruption while avoiding data loss. Support teams develop detailed migration plans specifying cutover sequences, rollback triggers, and success criteria. Phased approaches reduce risk by migrating user populations incrementally rather than attempting simultaneous transitions. These staged migrations provide learning opportunities that inform subsequent phases.
Coexistence periods allow parallel operation of old and new platforms while users transition gradually. Data migration tools transfer historical information, configurations, and user preferences to new systems. Comprehensive identity security represents broad mastery across authentication and authorization domains. These extensive competencies enable professionals to lead complex security initiatives spanning multiple technologies.
Sustainability Initiatives Reducing Environmental Impact
Energy efficiency considerations influence collaboration infrastructure design decisions as organizations pursue environmental responsibility goals. Support teams can contribute by optimizing resource utilization, consolidating underutilized systems, and implementing power management features. Virtualization and cloud migrations often reduce overall energy consumption compared to traditional dedicated hardware deployments. These sustainability improvements frequently align with cost reduction objectives.
Equipment lifecycle management includes responsible disposal of retired hardware through certified recycling programs. Carbon footprint analysis informs procurement decisions by considering operational energy requirements alongside functional capabilities. Modern workplace credentials validate expertise in contemporary collaboration platforms. These certifications demonstrate proficiency with current technologies that organizations actively deploy.
Remote Support Techniques Assisting Distributed Users
Geographically dispersed user populations require support approaches that deliver effective assistance without physical presence. Remote control tools enable technicians to troubleshoot endpoint issues by directly observing and manipulating devices. Screen sharing and co-browsing capabilities allow support personnel to guide users through complex procedures. These remote techniques expand support coverage while reducing travel costs and response times.
Remote diagnostic commands retrieve system logs, configuration details, and status information necessary for troubleshooting. Self-service portals empower users to resolve common problems independently through knowledge base articles and troubleshooting wizards. Endpoint administration competencies address device management across diverse endpoint types. These skills complement collaboration expertise where endpoint configuration significantly impacts user experiences.
Compliance Reporting Demonstrating Regulatory Adherence
Automated reporting systems generate compliance documentation required for regulatory audits and internal governance processes. Support teams configure these reporting systems to capture necessary metrics while protecting sensitive information from unauthorized access. Regular report review identifies potential compliance violations requiring remediation before formal audits occur. These proactive approaches minimize regulatory risks while demonstrating organizational commitment to legal obligations.
Audit trails document configuration changes, access events, and administrative actions that compliance frameworks require organizations to track and retain. Report customization accommodates varying compliance requirements across different regulatory jurisdictions. Specialized support expertise focuses on specific platform components requiring deep technical knowledge. These specialized competencies enable professionals to address complex issues within particular technology areas.
User Feedback Integration Improving Service Delivery
Systematic collection and analysis of user feedback reveals improvement opportunities that might otherwise remain hidden. Support teams implement multiple feedback channels including surveys, suggestion systems, and direct communication. Categorizing feedback identifies recurring themes that warrant prioritization in enhancement roadmaps. This user-centric approach ensures that support services and platform capabilities evolve in response to actual user needs rather than assumed requirements.
Feedback loop closure informs users about actions taken in response to their suggestions, demonstrating that their input produces tangible results. Participation incentives encourage broader feedback submission that provides more representative insights into user experiences. Messaging administration credentials validate expertise in email and messaging systems. These competencies complement collaboration knowledge in organizations where multiple communication platforms require integrated support.
Knowledge Transfer Mechanisms Preserving Organizational Expertise
Structured mentorship programs pair experienced support personnel with newer team members to accelerate skill development. Knowledge transfer extends beyond technical procedures to include organizational context, relationship dynamics, and informal practices that contribute to effectiveness. Cross-training initiatives prepare Kubernetes security for multiple team members to handle specialized tasks, reducing vulnerability to key person dependencies. These succession planning activities protect organizational capabilities against turnover impacts.
Documentation of troubleshooting experiences captures both technical solutions and diagnostic reasoning that led to successful resolutions. Case study development transforms individual experiences into learning opportunities for entire teams. Communities of practice enable support professionals across organizations to share insights and collaborate on common challenges. These knowledge sharing mechanisms multiply individual learning investments across entire professional communities.
Career Development Pathways Advancing Professional Growth
The collaboration technology field offers diverse career trajectories spanning technical specialist roles, management positions, and architecture functions. Support professionals can advance by deepening technical expertise, developing leadership capabilities, or broadening knowledge across related technology domains. Certification programs provide structured learning paths and industry-recognized credentials that validate capabilities. Strategic career planning aligns skill development with market demands and personal interests.
Professional networking through industry associations and user groups exposes practitioners to best practices and emerging trends. Conference attendance and continuing education maintain currency in rapidly evolving technology Kubernetes right fit landscapes. Lateral moves into related fields such as network engineering, security, or application development broaden perspectives and create versatile skill sets. These diverse experiences enhance problem-solving capabilities and career resilience.
Conclusion
The journey toward excellence in supporting Cisco collaboration devices encompasses far more than simple technical proficiency with specific products. This comprehensive exploration has illuminated the multifaceted nature of modern collaboration infrastructure support, where technical competence intersects with business acumen, security consciousness, and user advocacy. Organizations depend on collaboration platforms as fundamental business enablers rather than optional conveniences, elevating the importance of professional support that ensures reliability, security, and optimal performance across diverse deployment scenarios.
The foundation principles covered in established essential concepts around deployment strategies, quality assurance, security frameworks, and scalability considerations that underpin successful collaboration implementations. These fundamentals create the bedrock upon which advanced capabilities are built, ensuring that support professionals approach their responsibilities with systematic methodologies rather than ad-hoc reactions to immediate challenges. The emphasis on integration methodologies, performance optimization, and troubleshooting frameworks reflects the complex realities of modern enterprise environments where collaboration tools must interoperate seamlessly with diverse existing systems while meeting demanding user expectations.
Advanced implementation techniques elevated the discussion beyond basics into sophisticated topics like high availability architectures, protocol analysis, and API utilization that distinguish expert practitioners from novice support personnel. The coverage of network segmentation strategies, authentication integration, and quality of service mechanisms demonstrates how collaboration support intersects with broader infrastructure disciplines. This interdisciplinary nature requires support professionals to develop knowledge spanning multiple technology domains while maintaining deep expertise in collaboration-specific capabilities. The discussion of firmware management, certificate lifecycle, and bandwidth calculation illustrates the attention to detail necessary for maintaining production environments where small oversights can cascade into significant service disruptions.
The final section's focus on operational excellence and career development pathways acknowledged that technical skills alone prove insufficient for long-term success in this dynamic field. Incident response procedures, asset management, and patch management represent operational disciplines that transform reactive support into proactive service delivery. The emphasis on automation development, capacity modeling, and migration planning reflects the strategic contributions that advanced support professionals make beyond day-to-day troubleshooting activities. These higher-level capabilities position collaboration support personnel as valuable business partners who contribute to organizational success through technology enablement.
Throughout this comprehensive guide, the recurring theme of continuous learning emerges as perhaps the most critical success factor for collaboration support professionals. The rapid pace of technological evolution means that today's cutting-edge capabilities become tomorrow's baseline expectations. Organizations increasingly rely on collaboration platforms to support flexible work arrangements, global operations, and digital transformation initiatives. This expanding scope creates both opportunities and challenges for support professionals who must continually update their skills while maintaining operational excellence in production environments. The certification pathways and professional development opportunities discussed throughout these sections provide structured approaches to maintaining currency and demonstrating expertise.
Security considerations permeate every aspect of collaboration support, from initial deployment through ongoing operations and eventual platform migrations. The sensitive nature of business communications combined with increasingly sophisticated threat actors requires constant vigilance and defense-in-depth approaches. Support professionals serve as crucial guardians of organizational communication security through proper configuration management, timely patching, and incident detection. This security responsibility extends beyond technical controls to include user education, compliance reporting, and collaboration with dedicated security teams on broader organizational protection strategies.
The user experience focus emphasized throughout these discussions reflects the ultimate purpose of collaboration infrastructure: enabling effective human communication that drives business results. Technical excellence that delivers poor user experiences fails to achieve organizational objectives regardless of how sophisticated the underlying implementation may be. Support professionals must balance technical optimization with usability considerations, ensuring that security controls and performance tuning enhance rather than hinder the collaboration experiences that drive platform adoption and value realization. This user-centric perspective requires empathy, communication skills, and business understanding that complement technical competencies.
Looking forward, collaboration technology continues evolving toward increasing intelligence, automation, and integration with emerging capabilities like artificial intelligence and extended reality. Support professionals who position themselves at the forefront of these developments will find abundant opportunities to contribute meaningfully to organizational success. The fundamental principles covered throughout this guide provide enduring foundations that remain relevant even as specific technologies evolve. The systematic approaches to problem-solving, capacity planning, and continuous improvement transcend particular products or platforms, creating transferable skills that serve professionals throughout their careers across various technology domains.
Top Cisco Exams
- 200-301 - Cisco Certified Network Associate (CCNA)
- 350-401 - Implementing Cisco Enterprise Network Core Technologies (ENCOR)
- 350-701 - Implementing and Operating Cisco Security Core Technologies
- 300-410 - Implementing Cisco Enterprise Advanced Routing and Services (ENARSI)
- 350-601 - Implementing and Operating Cisco Data Center Core Technologies (DCCOR)
- 300-715 - Implementing and Configuring Cisco Identity Services Engine (300-715 SISE)
- 300-710 - Securing Networks with Cisco Firewalls
- 350-501 - Implementing and Operating Cisco Service Provider Network Core Technologies (SPCOR)
- 200-901 - DevNet Associate (DEVASC)
- 350-801 - Implementing Cisco Collaboration Core Technologies (CLCOR)
- 400-007 - Cisco Certified Design Expert
- 300-415 - Implementing Cisco SD-WAN Solutions (ENSDWI)
- 300-420 - Designing Cisco Enterprise Networks (ENSLD)
- 200-201 - Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
- 500-220 - Cisco Meraki Solutions Specialist
- 300-620 - Implementing Cisco Application Centric Infrastructure (DCACI)
- 300-425 - Designing Cisco Enterprise Wireless Networks (300-425 ENWLSD)
- 100-150 - Cisco Certified Support Technician (CCST) Networking
- 300-730 - Implementing Secure Solutions with Virtual Private Networks (SVPN 300-730)
- 820-605 - Cisco Customer Success Manager (CSM)
- 350-201 - Performing Cybersecurity Using Cisco Security Technologies (CBRCOR)
- 300-815 - Implementing Cisco Advanced Call Control and Mobility Services (CLASSM)
- 300-510 - Implementing Cisco Service Provider Advanced Routing Solutions (SPRI)
- 300-430 - Implementing Cisco Enterprise Wireless Networks (300-430 ENWLSI)
- 300-435 - Automating Cisco Enterprise Solutions (ENAUTO)
- 300-515 - Implementing Cisco Service Provider VPN Services (SPVI)
- 300-440 - Designing and Implementing Cloud Connectivity (ENCC)
- 700-805 - Cisco Renewals Manager (CRM)
- 300-445 - Designing and Implementing Enterprise Network Assurance
- 300-720 - Securing Email with Cisco Email Security Appliance (300-720 SESA)
- 350-901 - Developing Applications using Cisco Core Platforms and APIs (DEVCOR)
- 300-610 - Designing Cisco Data Center Infrastructure for Traditional and AI Workloads
- 300-725 - Securing the Web with Cisco Web Security Appliance (300-725 SWSA)
- 300-635 - Automating Cisco Data Center Solutions (DCAUTO)
- 300-630 - Implementing Cisco Application Centric Infrastructure - Advanced
- 300-220 - Conducting Threat Hunting and Defending using Cisco Technologies for Cybersecurity
- 300-215 - Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR)
- 300-615 - Troubleshooting Cisco Data Center Infrastructure (DCIT)
- 500-445 - Implementing Cisco Contact Center Enterprise Chat and Email (CCECE)
- 500-420 - Cisco AppDynamics Associate Performance Analyst
- 100-140 - Cisco Certified Support Technician (CCST) IT Support
- 300-745 - Designing Cisco Security Infrastructure
- 100-160 - Cisco Certified Support Technician (CCST) Cybersecurity
- 500-470 - Cisco Enterprise Networks SDA, SDWAN and ISE Exam for System Engineers (ENSDENG)
- 300-820 - Implementing Cisco Collaboration Cloud and Edge Solutions