Exam Code: 300-215
Exam Name: Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR)
Certification Provider: Cisco
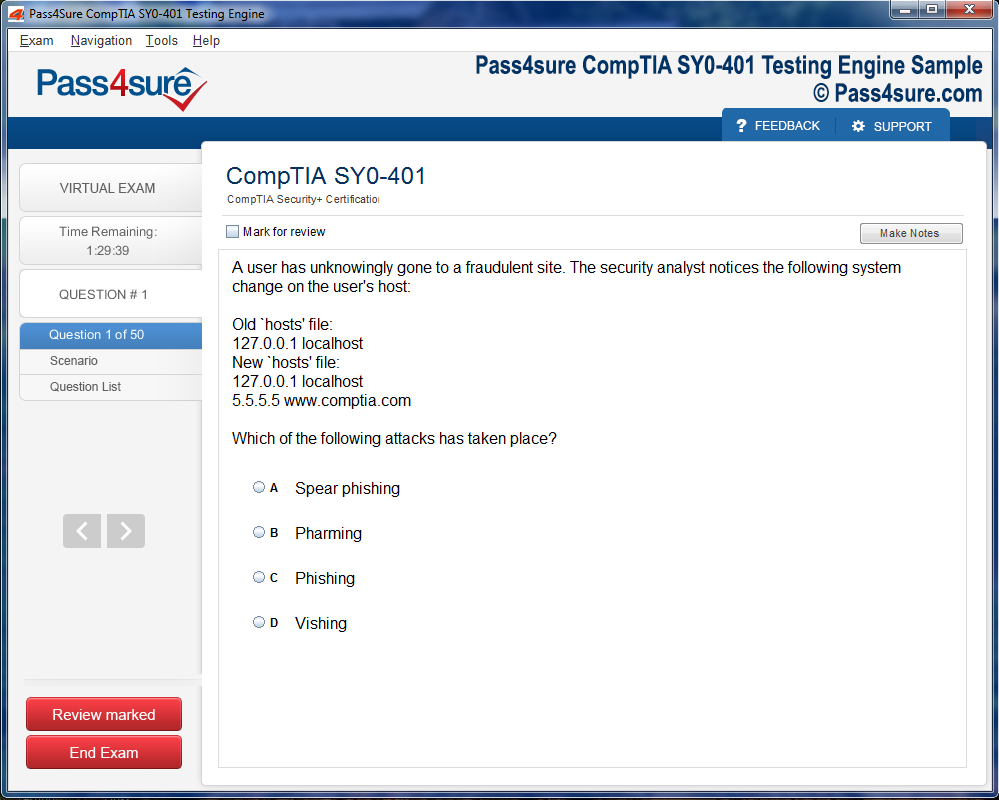
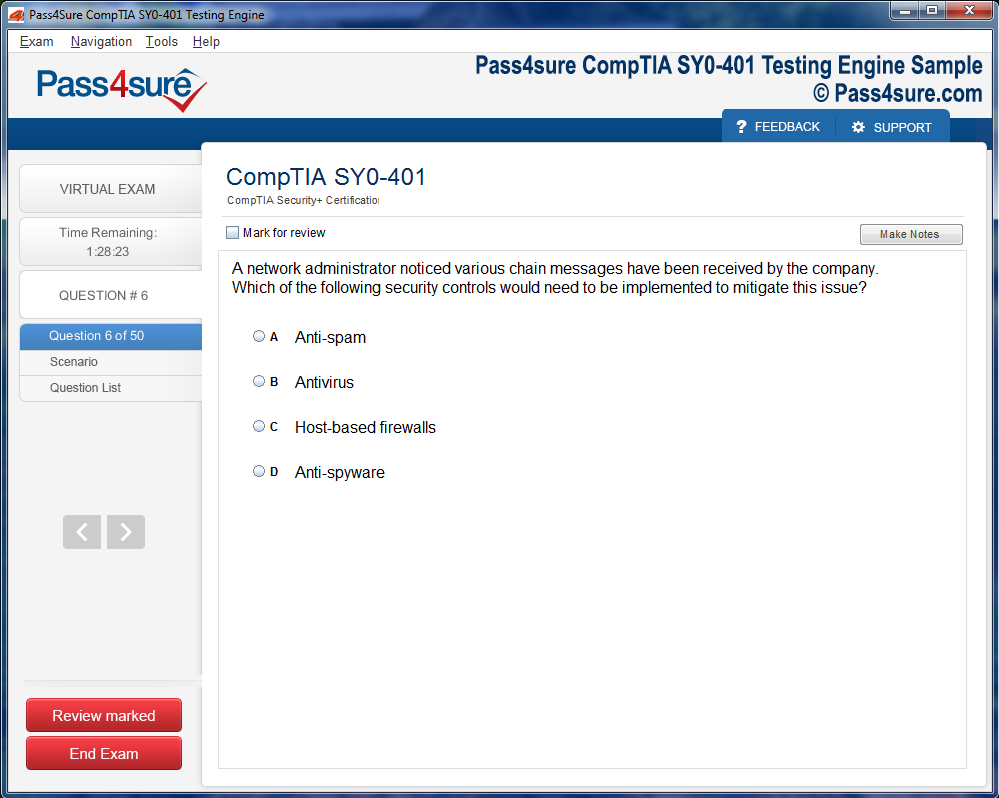
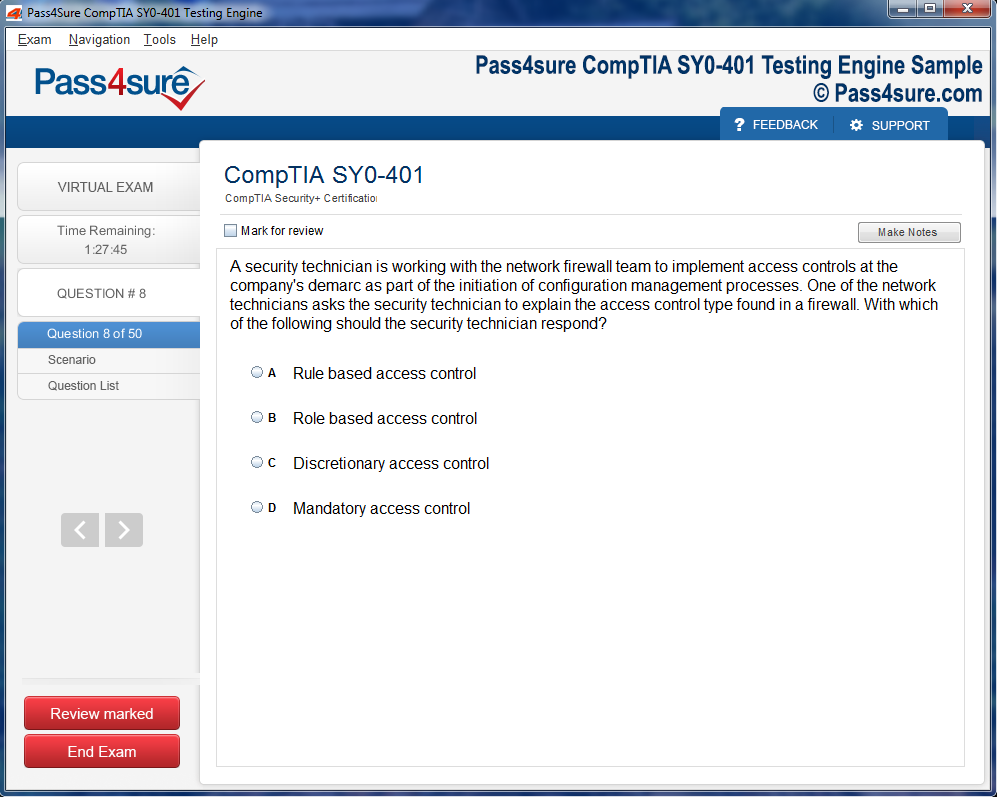
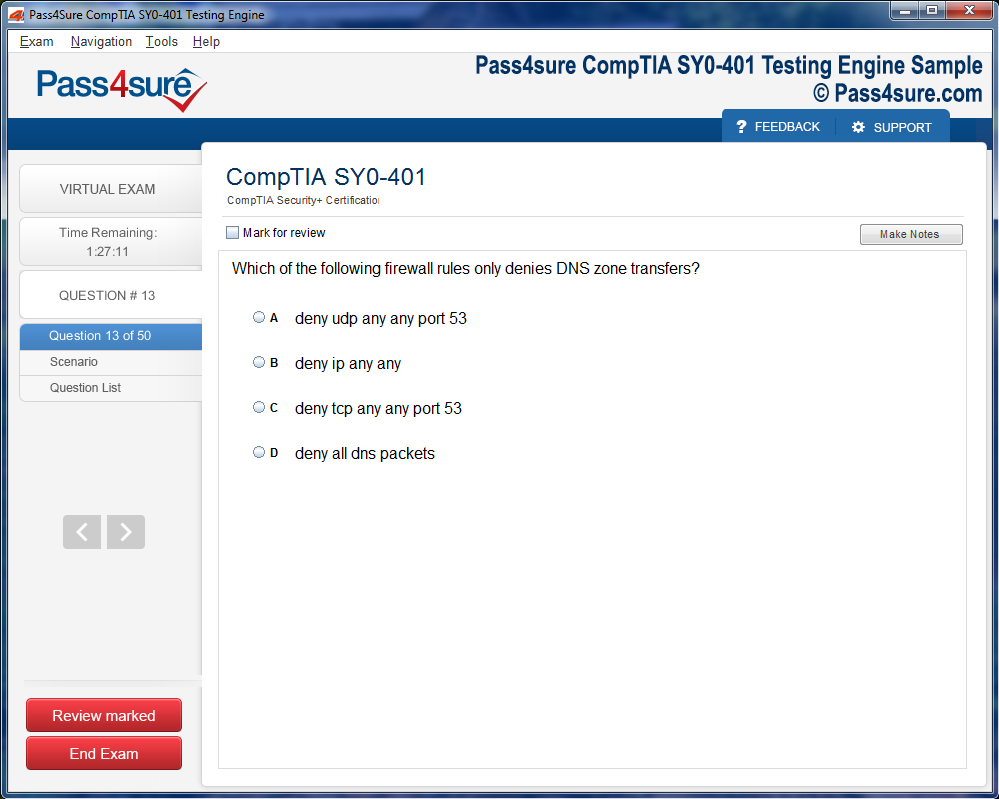
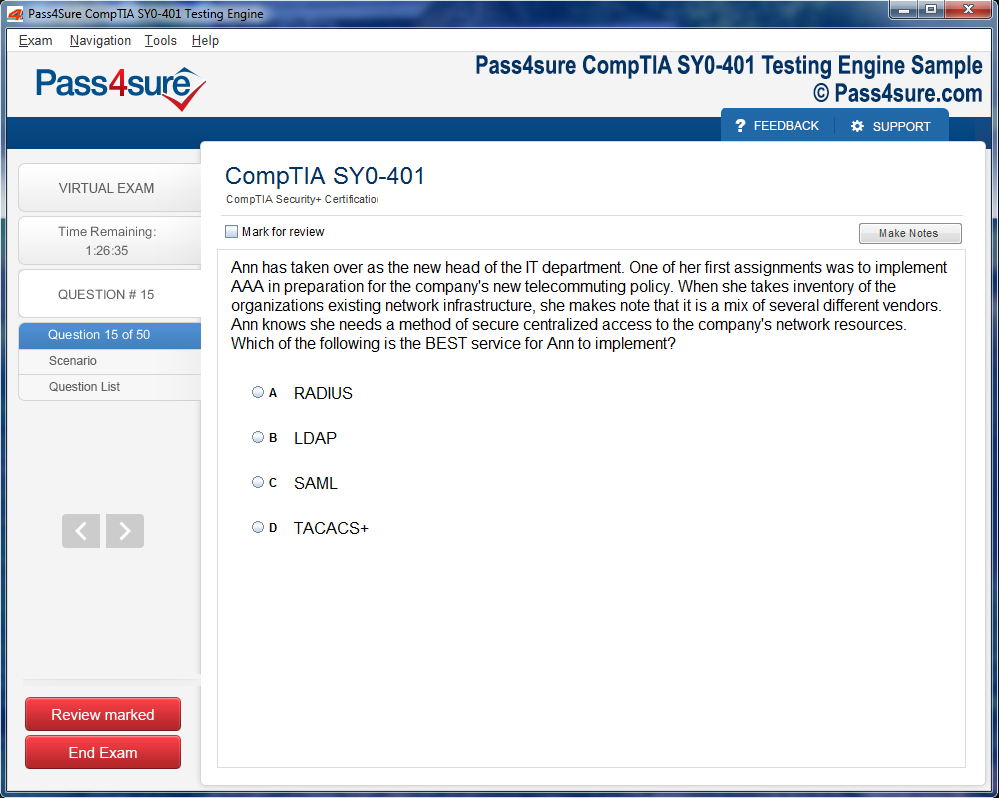
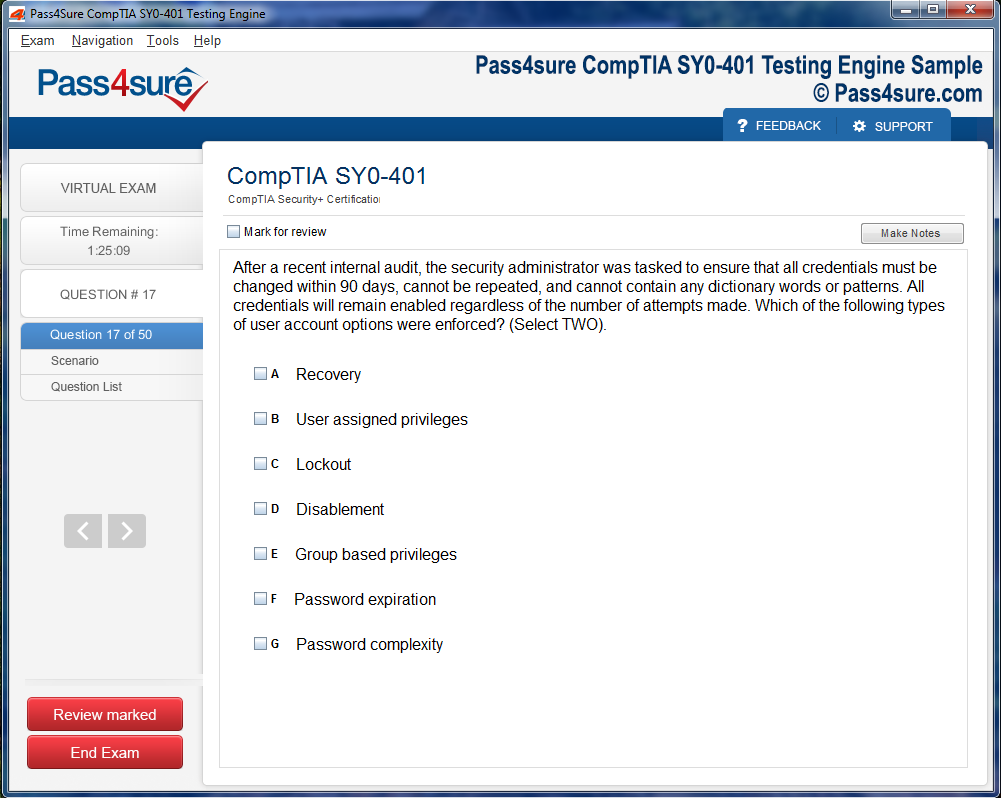
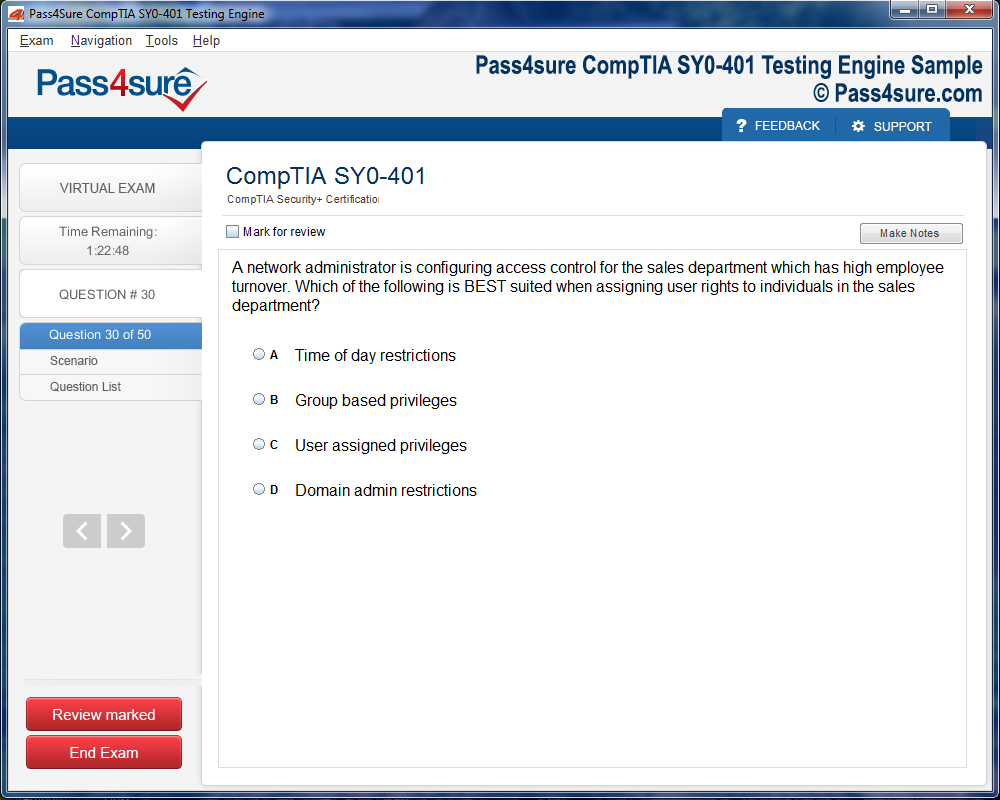
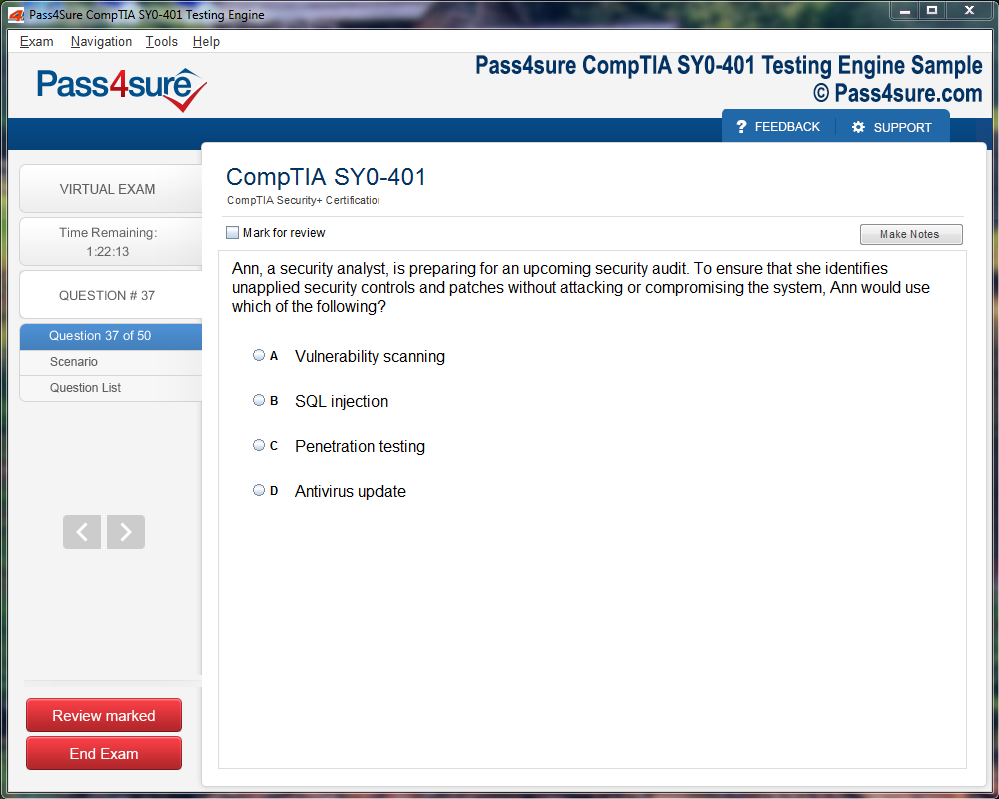
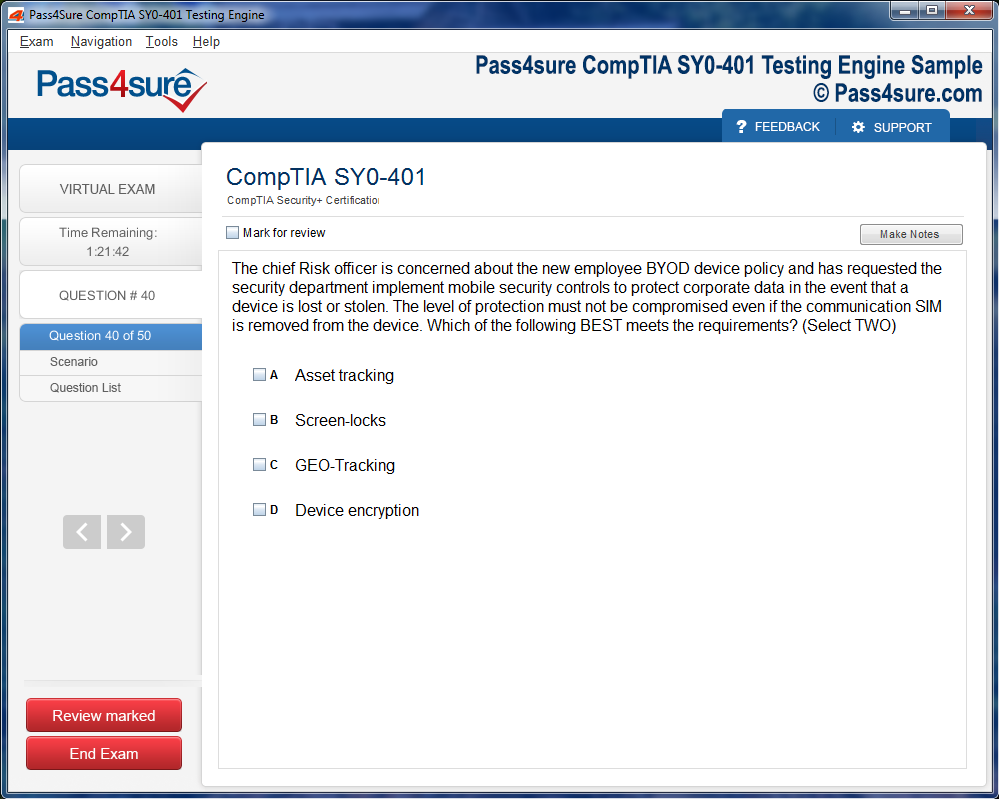
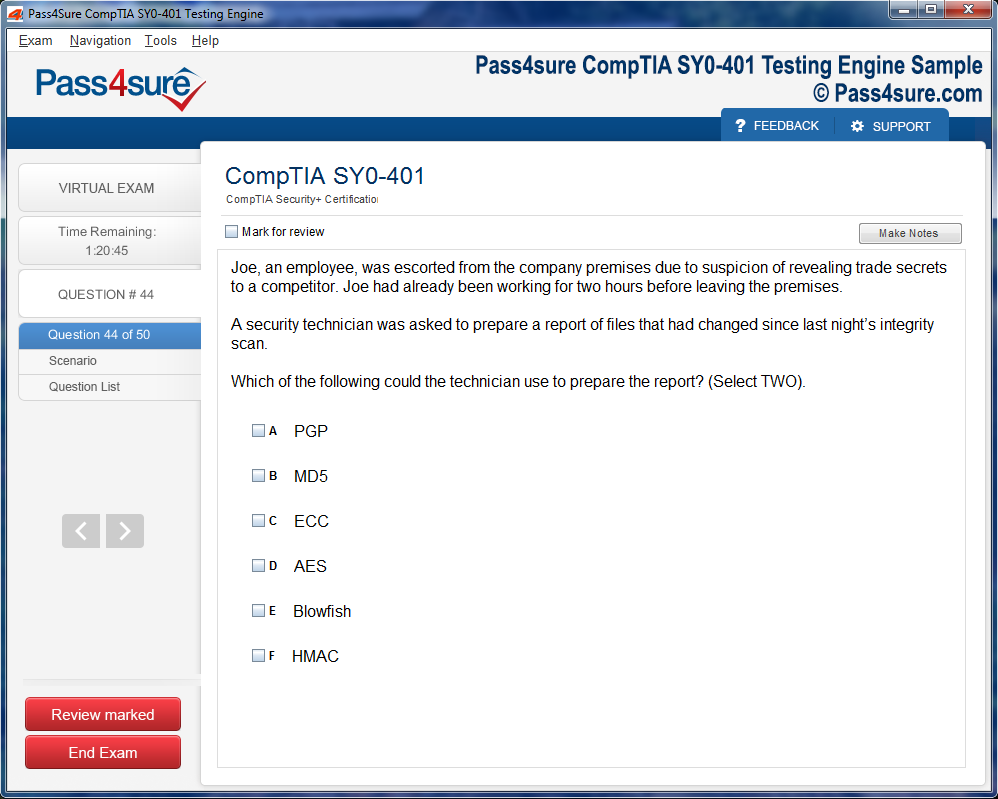
Product Screenshots
Frequently Asked Questions
How does your testing engine works?
Once download and installed on your PC, you can practise test questions, review your questions & answers using two different options 'practice exam' and 'virtual exam'. Virtual Exam - test yourself with exam questions with a time limit, as if you are taking exams in the Prometric or VUE testing centre. Practice exam - review exam questions one by one, see correct answers and explanations.
How can I get the products after purchase?
All products are available for download immediately from your Member's Area. Once you have made the payment, you will be transferred to Member's Area where you can login and download the products you have purchased to your computer.
How long can I use my product? Will it be valid forever?
Pass4sure products have a validity of 90 days from the date of purchase. This means that any updates to the products, including but not limited to new questions, or updates and changes by our editing team, will be automatically downloaded on to computer to make sure that you get latest exam prep materials during those 90 days.
Can I renew my product if when it's expired?
Yes, when the 90 days of your product validity are over, you have the option of renewing your expired products with a 30% discount. This can be done in your Member's Area.
Please note that you will not be able to use the product after it has expired if you don't renew it.
How many computers I can download Pass4sure software on?
You can download the Pass4sure products on the maximum number of 2 (two) computers or devices. If you need to use the software on more than two machines, you can purchase this option separately. Please email sales@pass4sure.com if you need to use more than 5 (five) computers.
What are the system requirements?
Minimum System Requirements:
- Windows XP or newer operating system
- Java Version 8 or newer
- 1+ GHz processor
- 1 GB Ram
- 50 MB available hard disk typically (products may vary)
What operating systems are supported by your Testing Engine software?
Our testing engine is supported by Windows. Andriod and IOS software is currently under development.
300-215 Exam: Step Up as a Cisco Certified CyberOps Specialist
The 300-215 exam represents a critical milestone for cybersecurity professionals aiming to validate their expertise in security operations and threat detection. This certification path demands comprehensive preparation, hands-on experience, and a thorough grasp of network security fundamentals. Candidates who pursue this credential demonstrate their commitment to staying current with evolving cyber threats and defense mechanisms. The certification validates skills in security monitoring, event analysis, and incident response procedures that organizations worldwide desperately need. Professionals holding this certification often find themselves at the forefront of defending enterprise networks against sophisticated attacks.
Preparation for the 300-215 requires building a solid foundation across multiple domains of cybersecurity knowledge. Candidates must demonstrate proficiency in security event management, threat intelligence, and forensic analysis. The exam tests real-world scenarios that mirror actual security operations center challenges. Success depends on both theoretical knowledge and practical application of security concepts. Many professionals complement their Cisco studies with related credentials to broaden their skill sets. For instance, Power BI opportunities can enhance data visualization capabilities crucial for security reporting. The intersection of cybersecurity and data analytics creates valuable career advancement pathways.
Security Event Monitoring Principles That Drive Effective Threat Detection
Security event monitoring forms the backbone of any robust cybersecurity program. Organizations generate massive volumes of log data daily, requiring sophisticated tools and methodologies to identify genuine threats among countless benign events. The 300-215 exam extensively covers SIEM platforms, log correlation techniques, and alert tuning strategies. Candidates must understand how to configure monitoring tools to capture relevant security events without overwhelming analysts with false positives. Effective monitoring requires balancing sensitivity with specificity to ensure critical threats receive immediate attention.
The complexity of modern security environments demands integration between various monitoring systems and analytical platforms. Security professionals often leverage business intelligence tools to create comprehensive dashboards that present threat data in actionable formats. Those interested in enhancing their analytical capabilities integrate Jira with analytics. This integration demonstrates the broader trend of connecting security operations with project management and workflow automation. The ability to correlate security events across multiple data sources separates competent analysts from exceptional ones.
Incident Response Procedures for Contemporary Cyber Threats
Incident response represents one of the most critical competencies tested in the 300-215 examination. When security incidents occur, organizations need professionals who can quickly assess the situation, contain the threat, and orchestrate recovery efforts. The exam evaluates candidates on their ability to follow established incident response frameworks while adapting to unique circumstances. Successful incident responders must balance speed with thoroughness, ensuring they collect sufficient forensic evidence while preventing further damage. The certification validates knowledge of containment strategies, eradication techniques, and recovery procedures.
Modern incident response increasingly relies on integrated platforms that streamline communication and documentation throughout the response lifecycle. Security teams benefit from tools that facilitate collaboration between analysts, management, and other stakeholders. Understanding how various enterprise systems interconnect proves valuable for comprehensive incident management. Professionals seeking broader enterprise platform Dynamics 365 CRM essentials. While focused on customer relationship management, these platforms often intersect with security operations through compliance tracking and stakeholder communication. The ability to navigate enterprise ecosystems enhances overall incident response effectiveness.
Network Traffic Analysis Techniques for Identifying Malicious Activity
Network traffic analysis remains a fundamental skill for CyberOps specialists. The 300-215 exam tests candidates on their ability to examine packet captures, identify anomalous patterns, and distinguish legitimate traffic from potential threats. Professionals must understand common network protocols, their normal behavior patterns, and indicators of compromise. Traffic analysis requires patience and attention to detail, as malicious actors increasingly employ sophisticated techniques to blend their activities with legitimate network communications. The exam scenarios often present complex traffic patterns requiring multi-layered analysis.
Mastering network analysis demands familiarity with various capture and analysis tools. Candidates must demonstrate proficiency in filtering large packet captures to isolate relevant communications. The skill extends beyond simple pattern recognition to understanding the context and business impact of discovered anomalies. Organizations value analysts who can translate technical findings into business-relevant risk assessments. Those building comprehensive technology skill sets might also investigate Dynamics 365 sales consultant requirements. Understanding how different enterprise roles approach data analysis provides valuable perspective for security professionals communicating with diverse stakeholders.
Endpoint Security Controls and Detection Capabilities
Endpoint security has evolved significantly as organizations embrace remote work and cloud services. The 300-215 exam covers endpoint detection and response platforms, host-based intrusion detection systems, and endpoint hardening strategies. Candidates must understand how to deploy, configure, and monitor endpoint security solutions across diverse operating systems and device types. The certification validates knowledge of behavioral analysis techniques that identify malicious activities even when traditional signature-based approaches fail. Effective endpoint security requires understanding both prevention and detection capabilities.
The integration of endpoint security with broader security operations creates comprehensive visibility across the entire attack surface. Modern security operations centers rely on centralized platforms that aggregate endpoint telemetry with network and application data. This holistic approach enables faster threat detection and more effective response coordination. Professionals seeking to expand their understanding of enterprise financial Dynamics 365 finance consultant expertise. While seemingly unrelated to endpoint security, understanding financial system architectures helps security professionals better protect these critical business applications. Cross-functional knowledge strengthens overall security posture.
Threat Intelligence Integration for Proactive Defense Strategies
Threat intelligence transforms reactive security operations into proactive defense programs. The 300-215 exam evaluates candidates on their ability to consume, analyze, and operationalize threat intelligence from various sources. Professionals must understand different intelligence types, including strategic, tactical, and operational intelligence. The certification tests knowledge of threat actor groups, their tactics, techniques, and procedures. Effective threat intelligence programs require establishing processes for continuous intelligence gathering, analysis, and dissemination to relevant stakeholders.
Implementing threat intelligence involves integrating feeds and indicators into existing security tools and workflows. Candidates must demonstrate understanding of standardized threat intelligence formats and sharing protocols. The exam covers how organizations can leverage both commercial and open-source intelligence sources. Many security professionals pursue multiple certifications to build comprehensive skill sets. Those interested in enterprise CCNP enterprise journey insights. Network security and threat intelligence intersect when analyzing infrastructure-level attacks and understanding how threats propagate through enterprise environments. Combining certifications creates powerful career opportunities.
Security Automation and Orchestration for Efficient Operations
Security automation and orchestration represent the future of security operations centers. The 300-215 exam covers SOAR platforms, playbook development, and automated response actions. Candidates must understand which security tasks benefit from automation and which require human judgment. The certification validates knowledge of scripting languages, API integration, and workflow automation. Effective automation reduces analyst workload, accelerates response times, and ensures consistent execution of standard operating procedures. Organizations implementing automation report significant improvements in mean time to detection and response.
Developing automation capabilities requires understanding both security processes and the underlying technologies that enable orchestration. Candidates must demonstrate proficiency in defining clear automation criteria and maintaining appropriate human oversight. The exam tests knowledge of common automation use cases and potential pitfalls. Advanced networking certifications complement automation skills by providing deeper infrastructure understanding. Those pursuing expert-level CCIE service provider preparation. Understanding provider networks helps security professionals design automation that accounts for complex routing scenarios and service provider integration points. Comprehensive knowledge drives more effective automation strategies.
Vulnerability Management Processes for Continuous Risk Reduction
Vulnerability management constitutes a critical ongoing process for maintaining security posture. The 300-215 exam tests candidates on vulnerability assessment methodologies, prioritization frameworks, and remediation tracking. Professionals must understand how to conduct comprehensive vulnerability scans, interpret results, and communicate findings to technical and non-technical stakeholders. The certification covers common vulnerability scoring systems and how to contextualize vulnerabilities based on organizational risk tolerance. Effective vulnerability management balances thoroughness with operational constraints.
Organizations must establish sustainable vulnerability management programs that integrate with change management and patch deployment processes. The exam evaluates knowledge of vulnerability lifecycle management from discovery through verification of remediation. Candidates must demonstrate understanding of compensating controls when immediate patching proves impossible. Security professionals often benefit from understanding how various certification paths intersect. Those interested in advanced security credentials CCIE security evolution perspectives. The evolution of security certifications reflects changing threat landscapes and technological advances. Staying current with certification trends helps professionals plan long-term career development strategies.
Forensic Analysis Fundamentals for Post-Incident Investigation
Digital forensics provides critical capabilities for understanding the full scope and impact of security incidents. The 300-215 exam covers evidence collection procedures, chain of custody requirements, and common forensic tools. Candidates must understand how to preserve volatile and non-volatile data while maintaining forensic integrity. The certification tests knowledge of file system analysis, memory forensics, and artifact interpretation. Successful forensic analysts combine technical skills with meticulous documentation practices. Forensic findings often support legal proceedings, requiring adherence to strict procedural standards.
Conducting thorough forensic investigations requires understanding various operating systems, file formats, and storage technologies. The exam evaluates candidates on their ability to reconstruct attacker activities from available evidence. Professionals must demonstrate knowledge of anti-forensic techniques attackers employ to cover their tracks. Those pursuing comprehensive Cisco expertise new CCIE exam insights. Understanding how expert-level certifications evolve helps professionals anticipate future skill requirements. Forensic capabilities complement broader CyberOps competencies by providing depth in post-incident analysis.
Compliance and Regulatory Frameworks Affecting Security Operations
Compliance requirements significantly influence security operations center design and procedures. The 300-215 exam addresses how various regulatory frameworks impact security monitoring, incident response, and data handling. Candidates must understand common compliance standards including PCI DSS, HIPAA, and GDPR requirements. The certification covers documentation requirements, audit procedures, and reporting obligations. Security professionals must balance operational efficiency with compliance mandates. Organizations face significant penalties for compliance failures, making this knowledge critical for CyberOps specialists.
Implementing compliant security operations requires ongoing attention to evolving regulations and industry standards. The exam tests knowledge of control mapping and how security tools can facilitate compliance reporting. Candidates must demonstrate understanding of data retention requirements and privacy considerations. Professionals building comprehensive infrastructure CCIE enterprise infrastructure certification. Enterprise infrastructure certifications provide foundational knowledge that supports compliance implementation. Understanding how security controls integrate with broader infrastructure helps ensure compliant and effective security operations.
Analytical Thinking and Problem-Solving Skills for Security Challenges
Analytical thinking represents perhaps the most valuable skill for CyberOps professionals. The 300-215 exam tests candidates through scenario-based questions requiring multi-step reasoning and creative problem-solving. Security analysts must synthesize information from multiple sources, identify patterns, and draw accurate conclusions under time pressure. The certification validates ability to approach ambiguous situations methodically while remaining flexible when initial hypotheses prove incorrect. Strong analytical skills separate competent technicians from strategic security leaders.
Developing analytical capabilities requires practice with diverse security scenarios and continuous learning. Candidates benefit from exposure to different problem-solving frameworks and decision-making methodologies. The exam rewards those who can think critically about security challenges rather than simply memorizing technical facts. Professionals seeking to enhance analytical skills GMAT practice test strategies. While focused on business school admission, analytical frameworks transfer across disciplines. Critical thinking skills developed through diverse challenges strengthen overall problem-solving capabilities.
Communication Skills for Effective Security Team Collaboration
Communication skills prove essential for CyberOps professionals working in team environments. The 300-215 exam includes scenarios requiring clear documentation, stakeholder reporting, and cross-functional collaboration. Security analysts must translate technical findings into language appropriate for different audiences. The certification validates ability to create concise incident reports, present findings to management, and coordinate with other IT teams. Effective communication accelerates incident response and improves overall security posture. Organizations value analysts who can bridge technical and business perspectives.
Developing strong communication skills requires practice and feedback from diverse stakeholders. Candidates must demonstrate understanding of different reporting formats and presentation techniques. The exam tests knowledge of escalation procedures and when to involve senior leadership. Many professionals enhance their preparation through structured practice resources. Those preparing for graduate free GRE practice resources. While targeting different objectives, practice tests develop test-taking skills applicable across certification exams. Time management and question interpretation skills transfer to professional certifications.
Continuous Learning Mindsets for Long-Term Career Success
The cybersecurity field evolves rapidly, demanding commitment to continuous learning. The 300-215 certification represents one milestone in an ongoing professional development journey. Successful CyberOps specialists maintain curiosity about emerging threats, new technologies, and evolving best practices. The exam tests current knowledge, but the field requires constant skill updating. Professionals must develop sustainable Practice tests with step learning habits including reading security research, attending conferences, and participating in professional communities. Career longevity depends on adaptability and willingness to embrace new concepts.
Building a continuous learning practice involves setting aside regular time for professional development activities. Candidates should explore diverse learning resources including blogs, podcasts, webinars, and hands-on labs. The certification process itself teaches valuable learning strategies applicable to future credentials. Those interested in standardized test GRE scoring strategies. Structured preparation approaches transfer to professional certification pursuits. Understanding how to deconstruct complex topics and build comprehensive knowledge helps professionals tackle increasingly challenging certifications.
Laboratory Practice Requirements for Hands-On Skill Development
Hands-on laboratory experience proves indispensable for 300-215 exam preparation. Reading documentation and watching videos provide theoretical knowledge, but practical skills develop only through direct tool interaction. Candidates should establish personal lab environments where they can safely experiment with security tools and techniques. The exam includes performance-based questions requiring actual configuration and troubleshooting skills. Organizations increasingly prioritize candidates with demonstrable practical abilities over those with purely theoretical knowledge. Laboratory practice builds confidence and reveals knowledge gaps requiring additional study.
Effective laboratory practice involves recreating realistic scenarios that mirror production environments. Candidates should practice with the same tools and platforms covered in exam objectives. Regular hands-on sessions reinforce theoretical concepts and develop muscle memory for common tasks. Resources for building skills extend beyond traditional security domains. Those interested in Cassandra for scalable systems. Understanding distributed data systems helps security professionals protect these increasingly common architectures. Cross-domain knowledge strengthens overall technical capabilities.
Time Management Strategies for Exam Day Success
Time management during the 300-215 exam significantly impacts performance. The exam presents numerous questions requiring careful analysis within limited timeframes. Candidates must develop strategies for quickly identifying question requirements and allocating appropriate effort. Some questions deserve only brief attention while others require detailed analysis. The certification tests not only knowledge but also decision-making under time pressure. Practicing with timed mock exams helps calibrate pacing and identify personal weaknesses. Successful candidates enter the exam with clear time allocation strategies.
Developing effective time management requires understanding personal strengths and weaknesses. Candidates should identify question types they handle quickly versus those requiring more deliberation. The exam allows marking questions for later review, enabling strategic time allocation. Those pursuing various credentialing paths might investigate free GRE resources. Free practice resources help build test-taking endurance without financial investment. Skills developed through any rigorous exam preparation strengthen performance across different certification programs.
Study Group Benefits for Collaborative Learning Experiences
Study groups provide valuable collaborative learning opportunities for 300-215 candidates. Discussing concepts with peers reinforces understanding and reveals alternative perspectives. Group members can share resources, quiz each other, and work through difficult topics together. The certification journey need not be solitary, and many professionals find motivation through peer interaction. Study groups create accountability structures that help maintain consistent preparation schedules. Explaining concepts to others deepens personal understanding and identifies knowledge gaps requiring additional attention.
Effective study groups establish clear goals, meeting schedules, and participation expectations. Members should contribute equally and respect diverse learning styles and knowledge levels. Online platforms enable remote collaboration when geographic proximity proves challenging. Professionals developing various analytical unsupervised learning patterns. Machine learning concepts increasingly intersect with cybersecurity through behavior analysis and anomaly detection. Understanding advanced analytical techniques positions security professionals for future technological shifts.
Career Advancement Opportunities After Certification Achievement
Achieving the 300-215 certification opens numerous career advancement opportunities. Organizations actively seek professionals with validated CyberOps skills amid ongoing talent shortages. The credential demonstrates commitment to professional development and mastery of critical security operations competencies. Certified professionals often command higher salaries and gain access to senior positions. The certification serves as a foundation for pursuing advanced Cisco credentials or complementary certifications from other vendors. Career progression in cybersecurity rewards those who continuously expand their skills and credentials.
Planning long-term career development involves identifying desired roles and the certifications they require. Professionals should research job postings to understand market demands and skill gaps. The 300-215 represents one component of a comprehensive professional development strategy. Those interested in business process lean principles and practices. Lean methodologies apply to security operations through process optimization and waste elimination. Cross-functional knowledge enables security professionals to contribute strategic value beyond purely technical domains.
Industry Recognition and Professional Credibility Enhancement
Cisco certifications carry significant industry recognition and credibility. The 300-215 credential signals to employers, clients, and peers that you possess validated expertise in security operations. Industry recognition translates to increased professional opportunities and respect within the cybersecurity community. The certification demonstrates willingness to submit your knowledge to objective evaluation. Many organizations require or strongly prefer certified candidates for security positions. Professional credibility built through certification facilitates networking, mentorship, and knowledge-sharing opportunities.
Maintaining certification requires ongoing professional development and periodic recertification. Cisco's continuing education requirements ensure certified professionals stay current with evolving technologies. The investment in certification pays dividends throughout your career through expanded opportunities and professional recognition. Those building development Java application development foundations. Programming capabilities enhance security professionals' ability to automate tasks and understand application vulnerabilities. Diverse technical skills create more valuable and versatile security practitioners.
Resource Optimization Strategies for Efficient Exam Preparation
Efficient exam preparation requires strategic resource allocation across study materials, practice exams, and hands-on labs. Candidates face countless study options requiring discernment about which resources provide optimal value. The 300-215 demands balancing breadth across all exam topics with sufficient depth in each area. Quality study resources trump quantity, and focused preparation outperforms scattered efforts. Successful candidates identify authoritative sources early and commit to comprehensive coverage. Resource optimization includes both material selection and time allocation across different preparation activities.
Developing an efficient study plan involves assessing current knowledge, identifying gaps, and allocating time proportionally. Candidates should front-load difficult topics while maintaining regular review of mastered material. The certification journey teaches valuable project management skills applicable beyond exam preparation. Professionals working with business virtual cubes in TM1. Understanding multidimensional data structures supports security reporting and analytics capabilities. Knowledge gained through diverse technical exploration strengthens overall professional capabilities and career prospects.
Advanced Technical Skills and Practical Implementation Strategies
Advanced technical proficiency separates competent CyberOps professionals from exceptional ones. The 300-215 exam tests deep understanding of security technologies, their configuration, and optimal deployment patterns. Candidates must demonstrate mastery of complex scenarios requiring integration of multiple security tools and techniques. The certification validates ability to design, implement, and maintain sophisticated security operations capabilities. Organizations need specialists who can navigate the complexity of modern security architectures while maintaining operational efficiency. Technical depth combined with practical implementation experience creates highly valuable professionals.
Modern security operations increasingly rely on containerized applications and orchestration platforms. Understanding these technologies helps security professionals protect contemporary infrastructure. The evolution away from monolithic architectures toward microservices creates new security challenges requiring specialized knowledge. Professionals interested in container security should investigate Kubernetes evolution without Docker. Container orchestration platforms fundamentally changed application deployment and security models. Security specialists must understand these platforms to effectively protect modern application environments and implement appropriate controls.
Advanced Threat Hunting Methodologies for Proactive Security
Threat hunting represents proactive security operations seeking threats that evade automated detection. The 300-215 exam covers hypothesis-driven hunting methodologies, hunt team organization, and metrics for measuring hunting effectiveness. Candidates must understand how to formulate testable hypotheses based on threat intelligence and environmental knowledge. The certification tests ability to use advanced query languages and analysis techniques for uncovering hidden threats. Successful threat hunters combine technical skills with creative thinking and persistence. Organizations implementing hunting programs report discovering threats that resided undetected for extended periods.
Effective threat hunting requires establishing baseline understanding of normal environment behavior. Hunters must recognize subtle deviations indicating potential compromise. The exam evaluates knowledge of common attack patterns and the artifacts they leave across different data sources. Those managing container Helm2 versus Helm3 choices. Package management decisions impact security posture and operational efficiency. Understanding infrastructure management tools helps security professionals identify misconfigurations and potential vulnerabilities in deployment pipelines.
Security Orchestration Platforms for Workflow Automation
Security orchestration platforms revolutionized security operations through automated workflow execution. The 300-215 exam tests candidates on SOAR platform capabilities, playbook design, and integration patterns. Professionals must understand how to connect disparate security tools through API integration and standardized data formats. The certification covers decision logic, conditional branching, and error handling within automated workflows. Effective orchestration reduces response times while ensuring consistent execution of standard procedures. Organizations report significant efficiency gains after implementing orchestration platforms.
Designing effective playbooks requires deep understanding of security processes and the tools executing them. Candidates must demonstrate knowledge of common orchestration use cases and implementation best practices. The exam evaluates ability to balance automation with appropriate human oversight and decision points. Security professionals CKS exam preparation strategies. Kubernetes security certifications complement CyberOps credentials by validating container security knowledge. Multi-cloud and containerized environments demand security specialists with diverse platform expertise.
Cloud Security Operations and Hybrid Environment Management
Cloud security operations present unique challenges compared to traditional on-premises environments. The 300-215 exam addresses cloud-specific security monitoring, shared responsibility models, and multi-cloud management. Candidates must understand how to adapt traditional security operations practices for cloud platforms. The certification tests knowledge of cloud-native security services and integration with existing security tools. Hybrid environments combining on-premises and cloud resources create complexity requiring sophisticated monitoring and correlation capabilities. Organizations migrating to cloud platforms need professionals who understand both paradigms.
Implementing effective cloud security operations requires understanding provider-specific tools and limitations. The exam covers common cloud security misconfigurations and monitoring strategies for detecting them. Candidates must demonstrate knowledge of identity and access management in cloud contexts. Those interested in container Kubernetes control plane components. Understanding orchestration platform architecture helps security professionals implement appropriate controls and monitoring. Deep platform knowledge enables more effective security operations.
Ethical Hacking Perspectives for Defensive Operations
Understanding attacker methodologies strengthens defensive capabilities. The 300-215 exam benefits from knowledge of common attack techniques and tools. Security operations professionals must think like attackers to anticipate potential intrusion vectors. The certification tests ability to recognize attack indicators and understand attack progression. Defensive operations improve when analysts understand offensive tactics, techniques, and procedures. Organizations increasingly value security professionals with both offensive and defensive expertise. Ethical hacking knowledge provides context for interpreting security alerts and prioritizing response efforts.
Developing offensive security knowledge complements CyberOps specialization. Candidates should familiarize themselves with common exploitation frameworks and attack methodologies. The exam rewards understanding of the full attack lifecycle from reconnaissance through post-exploitation. Security EC-Council certification pathways for ethical hacking credentials. Offensive security certifications provide systematic coverage of attack techniques. Combining defensive and offensive knowledge creates well-rounded security professionals capable of anticipating and countering sophisticated threats.
Data Protection Strategies Across Enterprise Environments
Data protection forms a core objective of security operations programs. The 300-215 exam covers data loss prevention technologies, encryption implementation, and data governance. Candidates must understand how to monitor for unauthorized data access and exfiltration attempts. The certification tests knowledge of classification schemes and appropriate controls for different data sensitivity levels. Effective data protection requires balancing security with operational usability. Organizations face regulatory requirements mandating specific data protection measures. Security operations teams must implement monitoring that validates ongoing compliance.
Implementing comprehensive data protection demands understanding data flows across enterprise systems. The exam evaluates knowledge of common data exfiltration techniques and detection strategies. Candidates must demonstrate familiarity with encryption protocols and key management practices. Those interested in storage EMC certification programs. Storage platform expertise supports implementation of data protection controls. Understanding underlying storage architectures helps security professionals design effective data security strategies.
Field Service Integration for Security Device Management
Security device management presents operational challenges requiring systematic approaches. The 300-215 exam addresses device lifecycle management, configuration management, and change control. Candidates must understand how to maintain security device configurations across large deployments. The certification tests knowledge of centralized management platforms and automation for configuration enforcement. Effective device management prevents configuration drift that creates security gaps. Organizations struggle with maintaining consistent security postures across distributed infrastructure. Systematic management processes reduce vulnerabilities introduced through misconfigurations.
Implementing device management programs requires integration with IT service management platforms. The exam covers documentation requirements and change approval workflows for security devices. Candidates should understand how to track device inventories and ensure timely patching. Professionals working across Dynamics 365 Field Service capabilities. Field service platforms facilitate coordination of physical device maintenance and upgrades. Understanding service management systems helps security teams coordinate device lifecycle activities.
Financial System Protection Through Security Operations
Financial systems represent high-value targets requiring robust security operations. The 300-215 exam includes scenarios involving protection of sensitive financial data and transaction monitoring. Candidates must understand specific threats facing financial applications and appropriate countermeasures. The certification tests knowledge of fraud detection techniques and financial transaction anomaly analysis. Security operations for financial systems demand particular attention to data integrity and availability. Regulatory requirements impose strict monitoring and reporting obligations. Organizations operating financial systems face severe consequences from security failures.
Protecting financial systems requires understanding their unique architectures and vulnerabilities. The exam evaluates knowledge of common financial system attack vectors and detection strategies. Candidates should demonstrate familiarity with financial compliance frameworks. Those interested in financial platform Dynamics 365 Finance certification paths. Understanding financial system architectures helps security professionals implement appropriate controls. Knowledge of business processes strengthens ability to identify truly anomalous activities.
Enterprise Resource Planning Security Fundamentals
Enterprise resource planning systems consolidate critical business functions requiring comprehensive security. The 300-215 exam addresses ERP-specific security challenges including segregation of duties and privileged access management. Candidates must understand how to monitor ERP systems for unauthorized access and suspicious activities. The certification tests knowledge of ERP audit logging and correlation with network security events. Effective ERP security operations require collaboration between security teams and business process owners. Organizations rely on ERP systems for core operations, making their protection paramount.
Implementing ERP security monitoring demands understanding system architectures and integration points. The exam covers common ERP vulnerabilities and configuration weaknesses. Candidates should demonstrate knowledge of role-based access control and authorization models. Professionals seeking ERP platform Dynamics 365 Fundamentals for ERP. Foundational ERP knowledge helps security specialists understand what they protect. Business process awareness enables more effective security operations and risk prioritization.
Marketing Platform Security and Data Privacy
Marketing platforms collect and process substantial personal data requiring careful security. The 300-215 exam includes scenarios involving customer data protection and privacy compliance. Candidates must understand marketing platform vulnerabilities and appropriate monitoring strategies. The certification tests knowledge of data privacy regulations affecting marketing operations. Security teams must balance marketing effectiveness with privacy protection. Organizations face significant penalties for mishandling customer data collected through marketing activities. Effective security operations ensure marketing platforms comply with data protection requirements.
Protecting marketing platforms requires understanding their data flows and third-party integrations. The exam evaluates knowledge of common marketing platform security weaknesses. Candidates should demonstrate familiarity with consent management and data subject rights. Those working with marketing Dynamics 365 Marketing certifications. Marketing platform expertise helps security professionals understand business requirements. Balancing security with marketing objectives requires understanding both domains.
Log Management Foundations for Security Analytics
Effective log management underpins successful security operations. The 300-215 exam extensively covers log collection, normalization, and retention strategies. Candidates must understand how to configure log sources for optimal security visibility. The certification tests knowledge of log parsing, field extraction, and correlation techniques. Comprehensive log management enables retrospective analysis and compliance reporting. Organizations generate overwhelming log volumes requiring strategic collection and retention policies. Security operations depend on having relevant logs available when incidents occur.
Implementing robust log management requires understanding diverse log formats and collection mechanisms. The exam evaluates knowledge of centralized logging architectures and scalability considerations. Candidates should demonstrate proficiency with log analysis tools and query languages. Those pursuing Splunk expertise might investigate SPLK-1001 certification preparation. Log management platform certifications complement CyberOps credentials. Specialized tool knowledge enhances overall security operations capabilities.
Search Processing Language Mastery for Security Queries
Search processing languages enable powerful security data analysis. The 300-215 exam tests ability to construct complex queries for threat hunting and investigation. Candidates must understand query syntax, performance optimization, and result interpretation. The certification covers statistical functions, field transformations, and data aggregation techniques. Effective query construction separates junior analysts from senior practitioners. Organizations value professionals who can extract actionable intelligence from vast log repositories. Query mastery accelerates investigations and enables sophisticated threat detection.
Developing query expertise requires extensive practice with real-world datasets. The exam evaluates ability to translate security questions into effective queries. Candidates should understand query performance implications and optimization strategies. Security professionals SPLK-1002 certification requirements. Advanced search capabilities unlock platform potential. Query language proficiency represents a career-differentiating skill.
Data Visualization Techniques for Security Reporting
Data visualization transforms raw security data into actionable insights. The 300-215 exam addresses dashboard design, chart selection, and reporting best practices. Candidates must understand how to present security metrics to different audiences. The certification tests knowledge of visualization types and their appropriate use cases. Effective visualizations communicate complex security postures clearly and concisely. Organizations rely on dashboards for monitoring security operations and communicating with leadership. Poor visualizations obscure important trends and hinder decision-making.
Creating effective security visualizations requires understanding both data and audience needs. The exam evaluates knowledge of interactive dashboards versus static reports. Candidates should demonstrate ability to highlight key metrics and trends. Those developing reporting SPLK-1003 certification objectives. Visualization expertise enhances communication effectiveness. Clear reporting builds stakeholder confidence in security operations.
Enterprise Security Management Across Distributed Infrastructures
Managing security across distributed infrastructures presents significant challenges. The 300-215 exam covers multi-site monitoring, centralized management, and distributed response coordination. Candidates must understand how to maintain consistent security postures across geographic locations. The certification tests knowledge of remote site monitoring and bandwidth-constrained log collection. Effective distributed security operations require balancing centralization with local autonomy. Organizations operating globally need security professionals who understand distributed architecture challenges. Coordination across time zones and teams demands clear processes and communication.
Implementing distributed security operations requires robust management platforms and processes. The exam evaluates knowledge of hierarchical management structures and delegation models. Candidates should demonstrate understanding of challenges specific to distributed environments. Security SPLK-1004 data administration concepts. Data management in distributed environments requires careful planning. Scalable architectures support growing security operations.
Advanced Troubleshooting Methods for Security Tools
Troubleshooting security tools requires systematic diagnostic approaches. The 300-215 exam tests ability to identify and resolve common tool issues. Candidates must understand log collection failures, correlation problems, and integration issues. The certification covers troubleshooting methodologies and escalation procedures. Effective troubleshooting minimizes security blind spots caused by tool failures. Organizations depend on functioning security tools for threat detection and response. Quick problem resolution maintains operational effectiveness and security visibility.
Developing troubleshooting expertise requires understanding tool architectures and common failure modes. The exam evaluates ability to use diagnostic tools and interpret error messages. Candidates should demonstrate knowledge of vendor support resources and escalation paths. Those maintaining security platforms SPLK-1005 certification content. Platform administration skills ensure reliable security operations. Tool reliability directly impacts security effectiveness.
Strategic Implementation and Career Development Pathways
Strategic security operations implementation requires aligning technical capabilities with business objectives. The 300-215 exam tests understanding of how security operations support organizational goals. Candidates must demonstrate ability to communicate security value to non-technical stakeholders. The certification validates knowledge of metrics that demonstrate security program effectiveness. Successful CyberOps specialists bridge technical and business perspectives. Organizations need security professionals who understand both threat landscapes and business imperatives. Strategic thinking separates tactical operators from security leaders.
Career development in cybersecurity demands continuous skill expansion and certification pursuit. Professionals must identify emerging technologies and acquire relevant competencies. The field rewards those who anticipate market needs and develop skills proactively. Understanding diverse technology domains creates more valuable professionals. Those building advanced SPLK-2001 certification pathways. Advanced platform certifications demonstrate deep expertise. Specialized credentials open doors to senior positions and leadership roles.
Metrics Development for Security Operations Effectiveness
Meaningful metrics enable continuous security operations improvement. The 300-215 exam covers key performance indicators, measurement methodologies, and reporting cadences. Candidates must understand which metrics demonstrate security program value. The certification tests knowledge of balancing leading and lagging indicators. Effective metrics programs track trends rather than point-in-time snapshots. Organizations struggle with defining actionable security metrics that drive improvement. Poorly chosen metrics create busywork without improving security posture.
Implementing metrics programs requires stakeholder engagement and clear objective definition. The exam evaluates understanding of common metric pitfalls and manipulation risks. Candidates should demonstrate knowledge of benchmark data and peer comparisons. Security professionals developing reporting capabilities SPLK-2002 certification content. Advanced reporting techniques support executive communication. Data-driven decision making improves security operations effectiveness.
Incident Classification Systems for Consistent Response
Incident classification ensures consistent response across security teams. The 300-215 exam addresses classification criteria, severity definitions, and escalation thresholds. Candidates must understand how to categorize diverse security events appropriately. The certification tests knowledge of classification schemes and their operational impact. Proper classification drives appropriate resource allocation and response urgency. Organizations need clear classification systems to manage incident queues effectively. Inconsistent classification creates confusion and delayed responses.
Developing classification systems requires balancing granularity with simplicity. The exam evaluates understanding of common classification dimensions and attributes. Candidates should demonstrate knowledge of dynamic reclassification as investigations progress. Those pursuing advanced cloud SPLK-2003 certification requirements. Cloud security monitoring demands specialized knowledge. Platform-specific expertise enhances overall security capabilities.
Team Building Strategies for Security Operations Centers
Building effective security operations teams requires careful planning and development. The 300-215 exam covers team structures, skill development, and retention strategies. Candidates must understand different SOC organizational models and their tradeoffs. The certification tests knowledge of shift schedules, handoff procedures, and team communication. Successful SOCs balance specialization with cross-training for operational resilience. Organizations struggle with recruiting and retaining qualified security personnel. Thoughtful team development reduces turnover and improves capabilities.
Implementing effective team structures requires understanding workload patterns and skill requirements. The exam evaluates knowledge of career progression paths within security operations. Candidates should demonstrate understanding of training programs and skill development. Security professionals SPLK-3001 enterprise deployment concepts. Enterprise-scale implementations require specialized knowledge. Large environment management skills prepare professionals for senior roles.
Vendor Management Practices for Security Services
Vendor management plays critical roles in comprehensive security programs. The 300-215 exam addresses vendor selection criteria, contract management, and performance monitoring. Candidates must understand how to evaluate security service providers. The certification tests knowledge of service level agreements and vendor accountability. Effective vendor management ensures third parties meet security requirements. Organizations increasingly rely on external providers for specialized security capabilities. Poor vendor management creates security gaps and operational inefficiencies.
Implementing vendor management programs requires clear requirements and evaluation frameworks. The exam evaluates understanding of vendor risk assessments and ongoing monitoring. Candidates should demonstrate knowledge of vendor relationship management best practices. Those working with SPLK-3002 certification pathways. Platform architecture knowledge supports vendor solution evaluation. Technical depth enables more effective vendor management.
Tabletop Exercise Design for Incident Response Readiness
Tabletop exercises validate incident response capabilities without operational disruption. The 300-215 exam covers exercise design, facilitation techniques, and improvement identification. Candidates must understand how to create realistic scenarios testing specific capabilities. The certification tests knowledge of exercise objectives and success criteria. Regular exercises reveal gaps in plans, tools, and team readiness. Organizations conducting exercises respond more effectively during actual incidents. Exercise programs create continuous improvement cycles.
Designing effective exercises requires understanding organizational risks and response procedures. The exam evaluates knowledge of exercise types and appropriate use cases. Candidates should demonstrate ability to facilitate exercises and capture SPLK-3003 certification objectives. Enterprise security administration skills support comprehensive security programs. Administrative expertise enables effective program implementation.
Knowledge Management Systems for Security Operations
Knowledge management preserves organizational security expertise. The 300-215 exam addresses documentation practices, knowledge base design, and information sharing. Candidates must understand how to capture and disseminate security knowledge. The certification tests knowledge of different documentation types and maintenance strategies. Effective knowledge management reduces dependency on individual experts. Organizations lose critical security knowledge through employee turnover. Systematic knowledge capture builds institutional capabilities.
Implementing knowledge management requires balancing comprehensiveness with maintainability. The exam evaluates understanding of documentation platforms and collaboration tools. Candidates should demonstrate knowledge of knowledge base organization and search SPLK-4001 certification content. Analytics skills support data-driven security operations. Knowledge management and analytics together create powerful capabilities.
Compliance Automation for Continuous Validation
Compliance automation reduces manual effort while improving accuracy. The 300-215 exam covers automated control testing, compliance reporting, and evidence collection. Candidates must understand which compliance activities benefit from automation. The certification tests knowledge of compliance frameworks and control mapping. Effective automation provides continuous compliance visibility. Organizations face increasing regulatory requirements demanding efficient compliance programs. Manual compliance processes scale poorly and introduce errors.
Implementing compliance automation requires understanding regulatory requirements and technical controls. The exam evaluates knowledge of automated testing tools and validation techniques. Candidates should demonstrate understanding of audit evidence requirements. Security professionals working with Splunk enterprise platforms might investigate SPLK-5001 certification pathways. Enterprise deployment skills support large-scale compliance monitoring. Scalable architectures enable comprehensive compliance automation.
Cloud Migration Security Considerations for Operations Teams
Cloud migration transforms security operations significantly. The 300-215 exam addresses migration planning, hybrid environment monitoring, and cloud-native security. Candidates must understand how cloud adoption changes security operations. The certification tests knowledge of migration phases and associated security considerations. Successful migrations maintain security visibility throughout the transition. Organizations struggle with security gaps during cloud adoption. Careful planning prevents migration-related security incidents.
Implementing secure cloud migrations requires understanding both source and target environments. The exam evaluates knowledge of cloud security architectures and service models. Candidates should demonstrate familiarity with cloud provider security tools. Those developing cloud security SPLK-5002 certification requirements. Cloud platform certifications validate specialized knowledge. Multi-cloud expertise positions professionals for diverse opportunities.
Application Development Security Integration Methods
Security integration with application development improves software quality. The 300-215 exam covers secure development practices, security testing, and DevSecOps principles. Candidates must understand how to embed security into development workflows. The certification tests knowledge of static analysis, dynamic testing, and security requirements. Effective DevSecOps reduces vulnerabilities in production applications. Organizations shifting left catch security issues earlier and cheaper. Security operations teams benefit from higher-quality applications.
Implementing DevSecOps requires collaboration between security and development teams. The exam evaluates understanding of CI/CD pipeline security integration. Candidates should demonstrate knowledge of developer security training and secure coding standards. Security professionals interested in development frameworks might review CoreSpring certification content. Understanding development frameworks helps security professionals review code effectively. Cross-functional knowledge enables better security integration.
Agile Security Operations for Rapid Response
Agile methodologies transform security operations through iterative improvement. The 300-215 exam addresses agile principles applied to security operations. Candidates must understand how to balance security rigor with operational agility. The certification tests knowledge of sprint planning, retrospectives, and incremental delivery. Agile security operations adapt quickly to changing threats. Organizations benefit from faster security improvements and response capabilities. Traditional waterfall approaches prove too slow for dynamic threat landscapes.
Implementing agile security operations requires cultural and process changes. The exam evaluates understanding of agile ceremonies and artifacts adapted for security. Candidates should demonstrate knowledge of backlog management and prioritization techniques. Those working with agile frameworks CSP-Assessor certification pathways. Agile certification demonstrates process expertise. Combining technical and process knowledge creates well-rounded professionals.
Network Programmability Skills for Security Automation
Network programmability enables powerful security automation. The 300-215 exam covers API interactions, scripting for network devices, and infrastructure as code. Candidates must understand how to programmatically configure and monitor network security devices. The certification tests knowledge of common network APIs and automation frameworks. Programmable networks enable rapid response to threats. Organizations implementing network automation realize significant efficiency gains. Manual configuration proves too slow for contemporary threat landscapes.
Implementing network programmability requires understanding both networking and programming. The exam evaluates knowledge of REST APIs, Python networking libraries, and automation tools. Candidates should demonstrate ability to write scripts for common security tasks. Security professionals developing Cisco automation AppDynamics certification options. Application performance monitoring integrates with security operations. Comprehensive monitoring improves threat detection and response.
Contact Center Security for Customer Data Protection
Contact centers process sensitive customer information requiring robust security. The 300-215 exam includes scenarios involving contact center security monitoring. Candidates must understand unique threats facing customer service operations. The certification tests knowledge of recording security, data masking, and access controls. Effective contact center security balances customer experience with data protection. Organizations face regulatory requirements for customer data handling. Security operations must monitor for insider threats and data exfiltration.
Implementing contact center security requires understanding both technology and business processes. The exam evaluates knowledge of quality monitoring and compliance recording. Candidates should demonstrate familiarity with PCI DSS requirements for payment data. Those working with contact center technologies Cisco contact center certifications. Contact center platform expertise supports security implementation. Understanding business requirements enables appropriate security controls.
Advanced Collaboration Security for Distributed Teams
Collaboration platforms create security challenges requiring specialized monitoring. The 300-215 exam addresses collaboration platform security, data loss prevention, and access management. Candidates must understand how to secure video conferencing, messaging, and file sharing. The certification tests knowledge of collaboration platform vulnerabilities and countermeasures. Distributed work models increase reliance on collaboration tools. Organizations must balance collaboration convenience with security requirements. Effective security operations monitor collaboration platforms for misuse.
Implementing collaboration security requires understanding platform capabilities and limitations. The exam evaluates knowledge of encryption, access controls, and external sharing policies. Candidates should demonstrate familiarity with collaboration platform audit logging. Security professionals working with Cisco collaboration collaboration security certifications. Platform-specific security knowledge enables effective protection. Specialized credentials demonstrate focused expertise.
IoT Security Operations for Connected Device Management
Internet of Things deployments introduce unique security challenges. The 300-215 exam covers IoT device monitoring, network segmentation, and firmware management. Candidates must understand how to secure diverse IoT ecosystems. The certification tests knowledge of IoT protocols and device authentication. Effective IoT security requires specialized approaches beyond traditional endpoints. Organizations deploying IoT face expanded attack surfaces. Security operations must account for resource-constrained devices.
Implementing IoT security operations demands understanding device capabilities and limitations. The exam evaluates knowledge of IoT-specific threats and detection strategies. Candidates should demonstrate familiarity with IoT security frameworks. Those working with Cisco IoT security certifications. IoT platform expertise supports secure deployments. Specialized knowledge positions professionals for emerging opportunities.
Conclusion
The journey to achieving the 300-215 Cisco Certified CyberOps Specialist certification represents a comprehensive professional development undertaking that extends far beyond simple exam preparation. Explored the multifaceted nature of modern security operations, encompassing foundational concepts, advanced technical implementations, and strategic career development considerations. Successful candidates must demonstrate proficiency across diverse domains including security event monitoring, incident response, threat hunting, forensic analysis, and security automation. The certification validates both theoretical knowledge and practical skills essential for protecting contemporary enterprise environments against sophisticated cyber threats.
Throughout this extensive exploration, we have examined how CyberOps specialists must balance technical depth with strategic thinking. The role demands continuous learning as threat actors evolve their tactics and technologies advance. Professionals pursuing this certification benefit from understanding adjacent technology domains including cloud platforms, container orchestration, application development, and business intelligence. The intersection of cybersecurity with these complementary fields creates opportunities for security specialists to deliver greater organizational value. Cross-functional knowledge enables more effective communication with diverse stakeholders and supports implementation of comprehensive security programs that align with business objectives.
The technical competencies required for CyberOps excellence span network traffic analysis, endpoint security, threat intelligence integration, vulnerability management, and security orchestration. Professionals must master diverse tools and platforms while developing the analytical thinking skills that enable effective threat detection and investigation. Laboratory practice proves indispensable for building the hands-on expertise that differentiates competent analysts from exceptional ones. Time management, study group participation, and strategic resource allocation contribute to efficient exam preparation that maximizes learning while minimizing wasted effort.
Beyond individual technical skills, successful CyberOps professionals must understand team dynamics, communication strategies, and organizational change management. Security operations centers function as collaborative environments where clear communication and knowledge sharing directly impact effectiveness. Building sustainable security programs requires attention to metrics development, incident classification, vendor management, and continuous improvement through tabletop exercises. Organizations increasingly recognize that security effectiveness depends not only on technology deployment but also on processes, people, and organizational culture.
The career opportunities available to certified CyberOps specialists continue expanding as organizations face persistent talent shortages in cybersecurity. The 300-215 certification provides industry recognition that opens doors to advanced positions and increased compensation. However, the certification represents one milestone in an ongoing professional journey rather than a final destination. The cybersecurity field rewards those who maintain curiosity, embrace continuous learning, and adapt to emerging technologies and evolving threats. Professionals who combine technical expertise with business acumen position themselves for leadership roles where they can shape security strategy and drive organizational transformation.
Looking forward, CyberOps professionals must prepare for continued evolution in security operations. Cloud adoption, artificial intelligence, quantum computing, and other emerging technologies will create new security challenges requiring specialized knowledge. The skills developed through pursuing the 300-215 certification provide a foundation for adapting to these future changes. Professionals who build diverse technical competencies, understand business contexts, and maintain flexible mindsets will thrive regardless of how the field evolves. The investment in certification and continuous professional development pays dividends throughout careers that increasingly span multiple decades.
Top Cisco Exams
- 200-301 - Cisco Certified Network Associate (CCNA)
- 350-401 - Implementing Cisco Enterprise Network Core Technologies (ENCOR)
- 350-701 - Implementing and Operating Cisco Security Core Technologies
- 300-410 - Implementing Cisco Enterprise Advanced Routing and Services (ENARSI)
- 350-601 - Implementing and Operating Cisco Data Center Core Technologies (DCCOR)
- 300-715 - Implementing and Configuring Cisco Identity Services Engine (300-715 SISE)
- 300-710 - Securing Networks with Cisco Firewalls
- 350-501 - Implementing and Operating Cisco Service Provider Network Core Technologies (SPCOR)
- 350-801 - Implementing Cisco Collaboration Core Technologies (CLCOR)
- 200-901 - DevNet Associate (DEVASC)
- 400-007 - Cisco Certified Design Expert
- 300-415 - Implementing Cisco SD-WAN Solutions (ENSDWI)
- 300-420 - Designing Cisco Enterprise Networks (ENSLD)
- 200-201 - Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
- 500-220 - Cisco Meraki Solutions Specialist
- 300-620 - Implementing Cisco Application Centric Infrastructure (DCACI)
- 300-425 - Designing Cisco Enterprise Wireless Networks (300-425 ENWLSD)
- 300-730 - Implementing Secure Solutions with Virtual Private Networks (SVPN 300-730)
- 100-150 - Cisco Certified Support Technician (CCST) Networking
- 350-201 - Performing Cybersecurity Using Cisco Security Technologies (CBRCOR)
- 820-605 - Cisco Customer Success Manager (CSM)
- 300-815 - Implementing Cisco Advanced Call Control and Mobility Services (CLASSM)
- 300-510 - Implementing Cisco Service Provider Advanced Routing Solutions (SPRI)
- 300-430 - Implementing Cisco Enterprise Wireless Networks (300-430 ENWLSI)
- 300-435 - Automating Cisco Enterprise Solutions (ENAUTO)
- 300-515 - Implementing Cisco Service Provider VPN Services (SPVI)
- 300-440 - Designing and Implementing Cloud Connectivity (ENCC)
- 700-805 - Cisco Renewals Manager (CRM)
- 300-445 - Designing and Implementing Enterprise Network Assurance
- 300-720 - Securing Email with Cisco Email Security Appliance (300-720 SESA)
- 350-901 - Developing Applications using Cisco Core Platforms and APIs (DEVCOR)
- 300-610 - Designing Cisco Data Center Infrastructure for Traditional and AI Workloads
- 300-725 - Securing the Web with Cisco Web Security Appliance (300-725 SWSA)
- 300-615 - Troubleshooting Cisco Data Center Infrastructure (DCIT)
- 300-630 - Implementing Cisco Application Centric Infrastructure - Advanced
- 300-635 - Automating Cisco Data Center Solutions (DCAUTO)
- 300-215 - Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR)
- 300-820 - Implementing Cisco Collaboration Cloud and Edge Solutions
- 500-445 - Implementing Cisco Contact Center Enterprise Chat and Email (CCECE)
- 300-745 - Designing Cisco Security Infrastructure
- 300-220 - Conducting Threat Hunting and Defending using Cisco Technologies for Cybersecurity
- 100-160 - Cisco Certified Support Technician (CCST) Cybersecurity
- 500-470 - Cisco Enterprise Networks SDA, SDWAN and ISE Exam for System Engineers (ENSDENG)
- 500-420 - Cisco AppDynamics Associate Performance Analyst
- 100-140 - Cisco Certified Support Technician (CCST) IT Support