Exam Code: 312-49v10
Exam Name: Computer Hacking Forensic Investigator
Certification Provider: ECCouncil
Corresponding Certification: CHFI
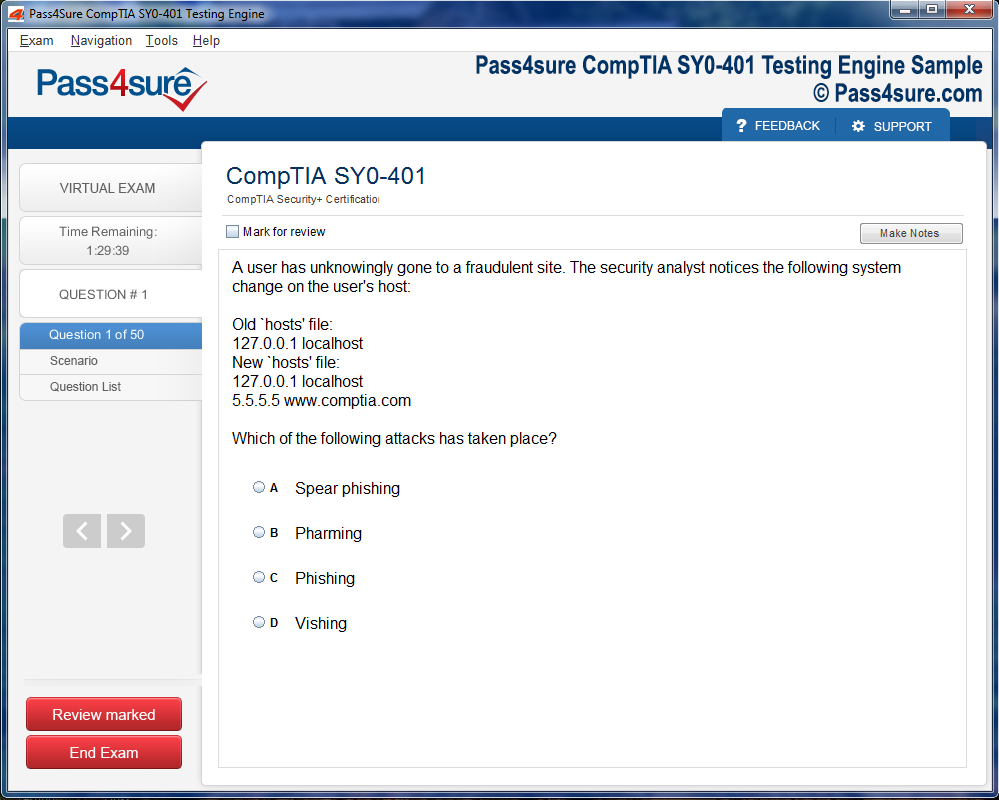
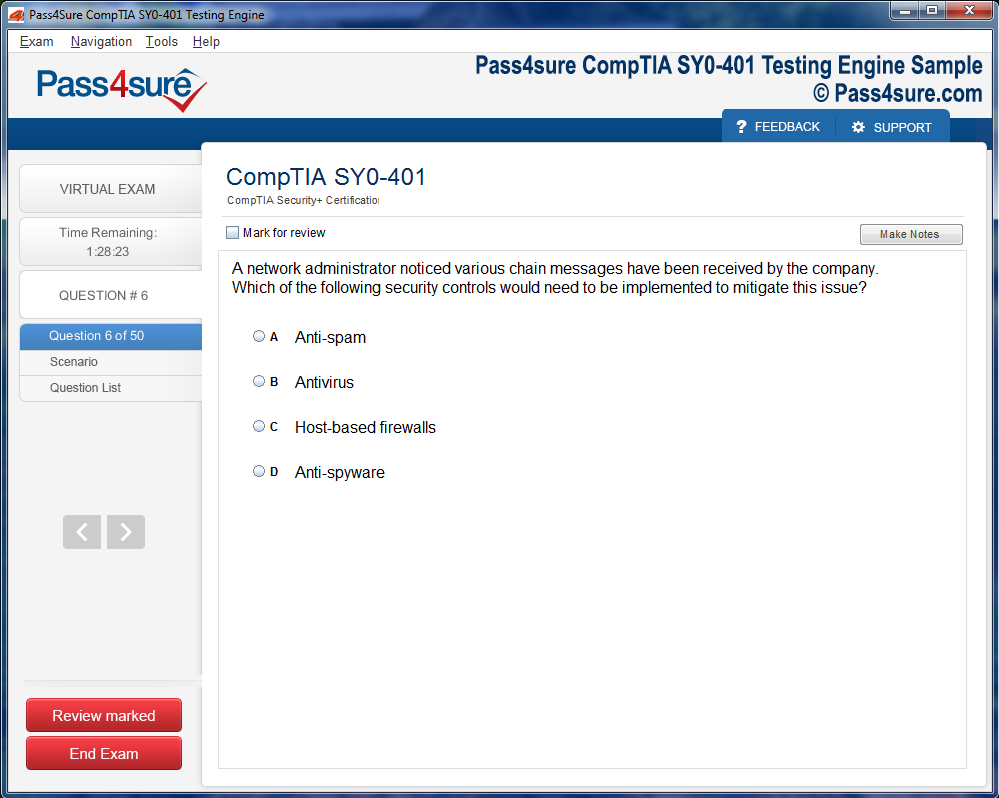
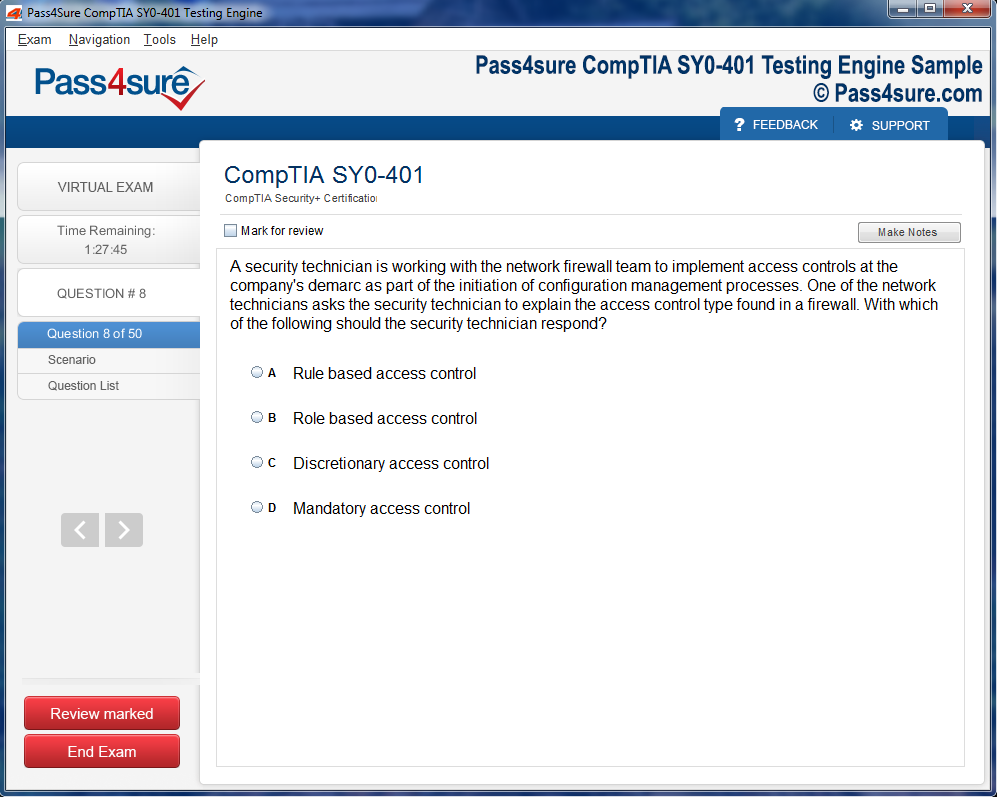
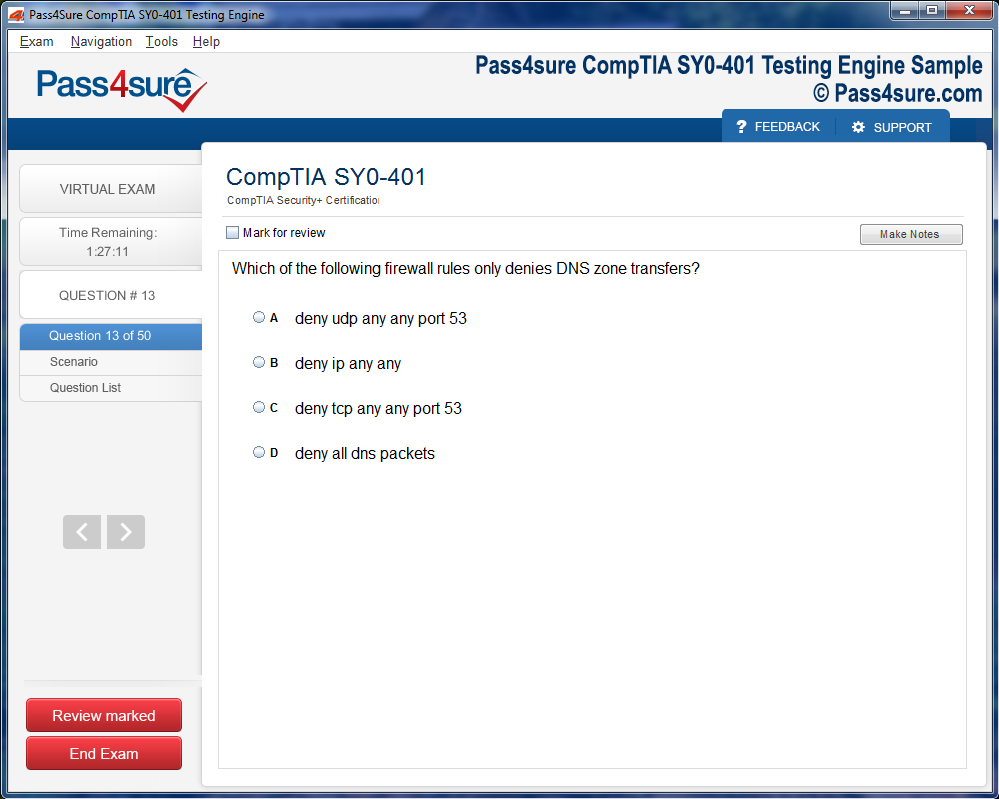
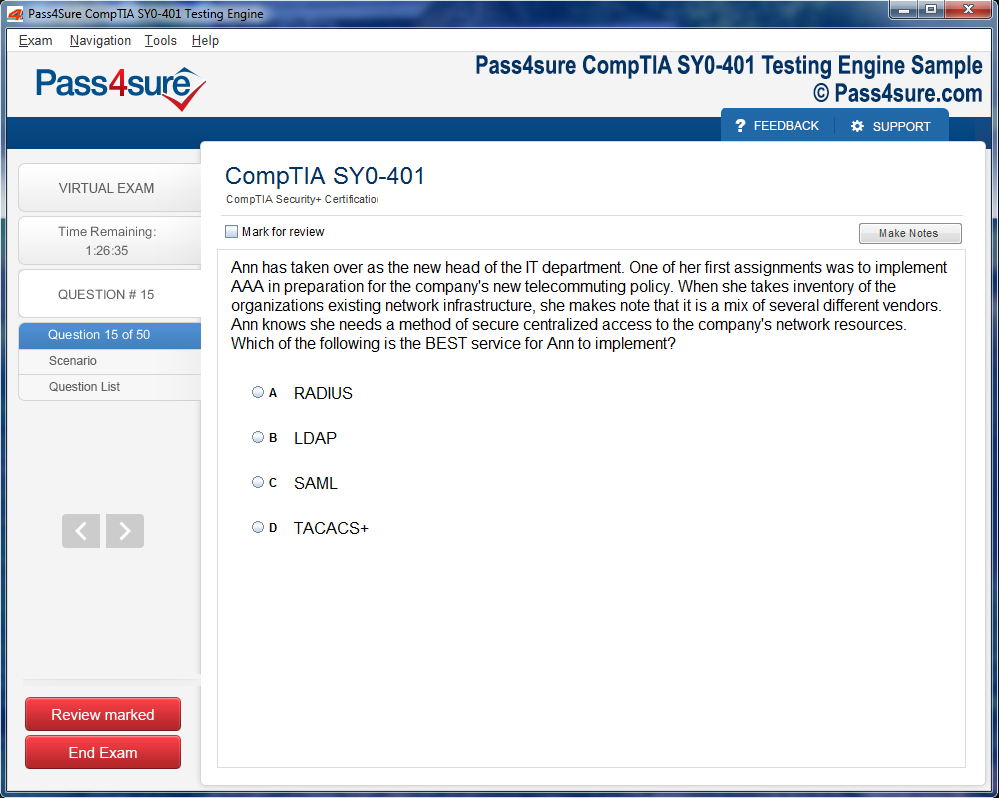
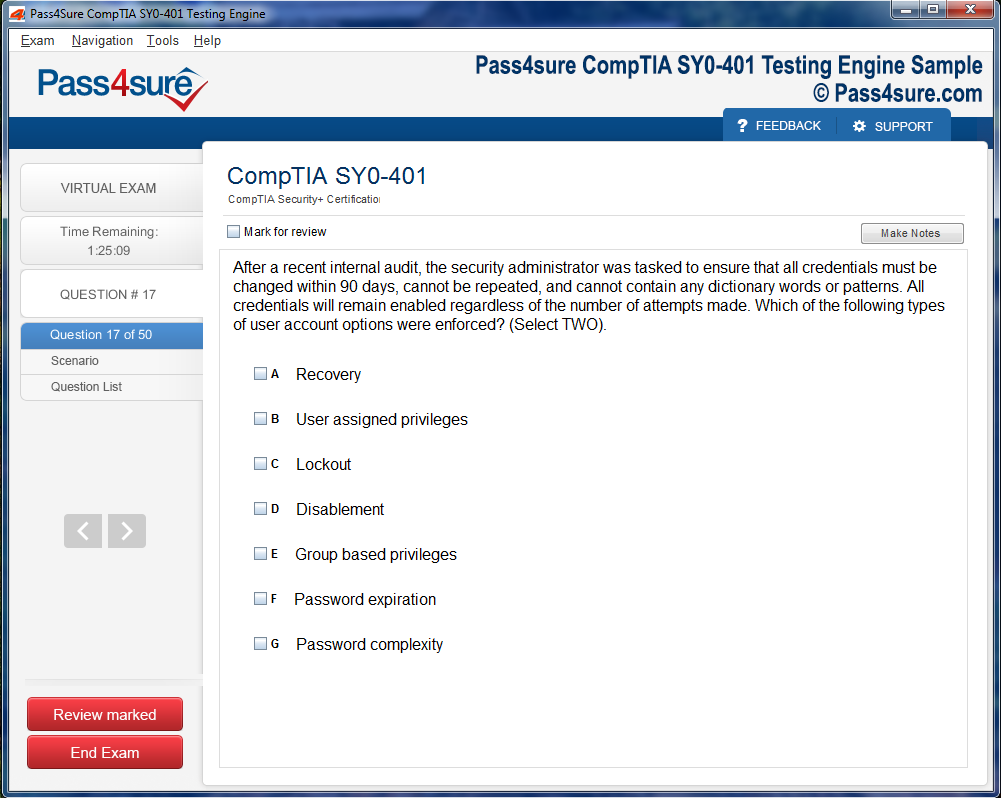
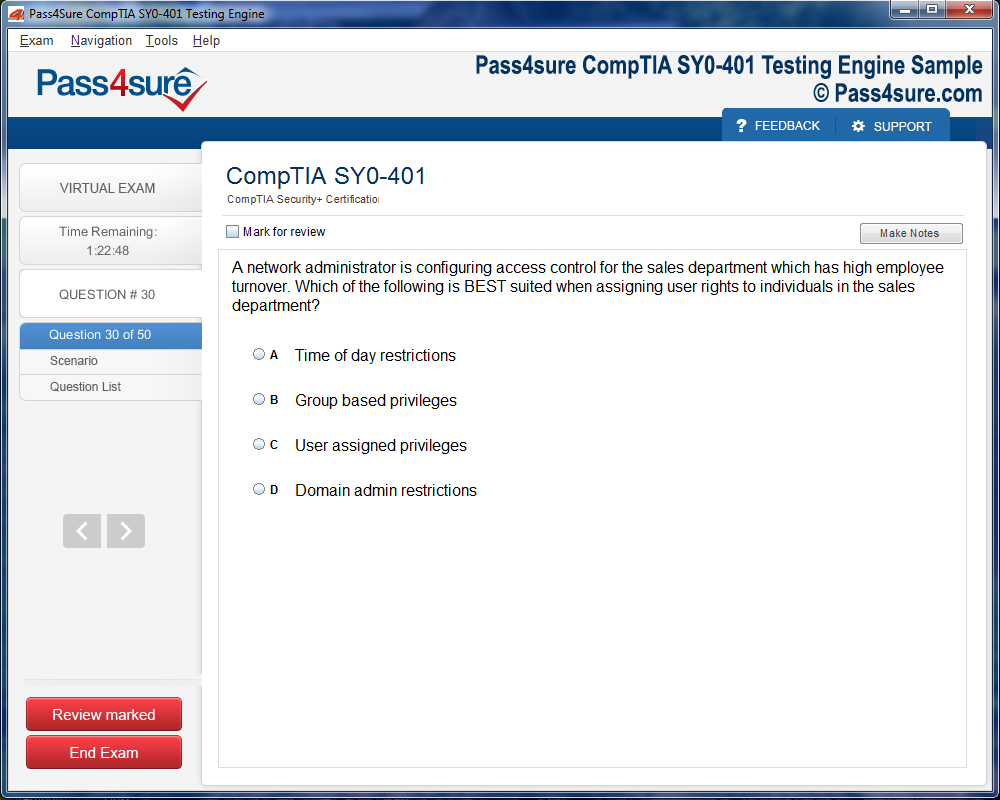
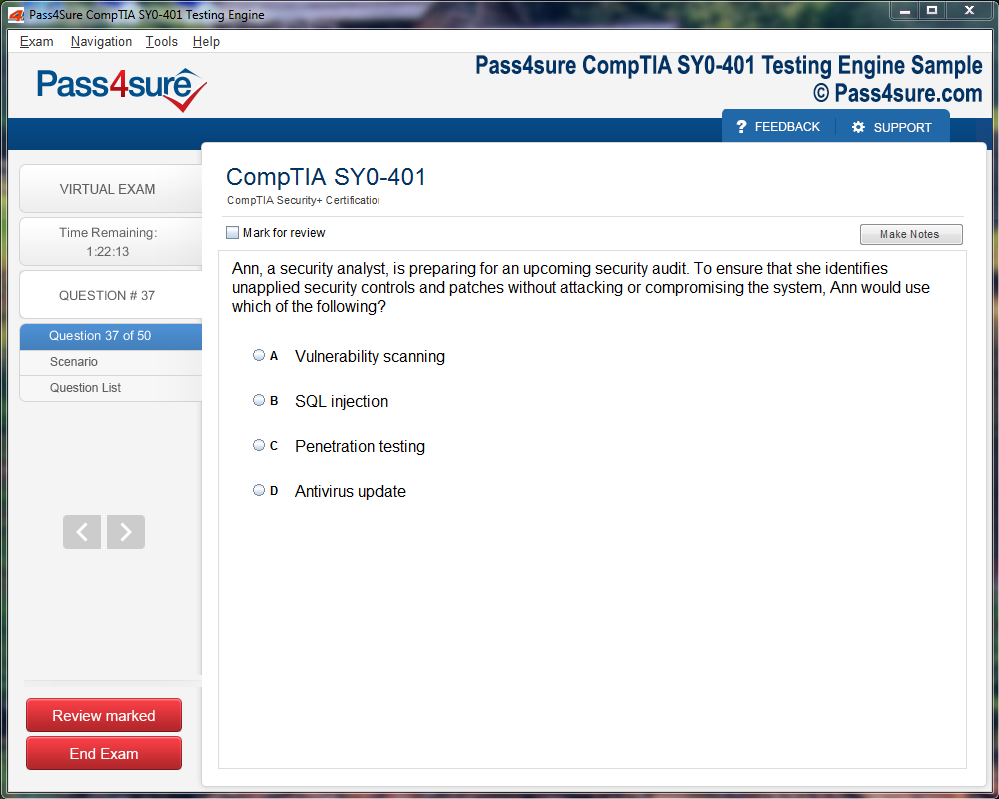
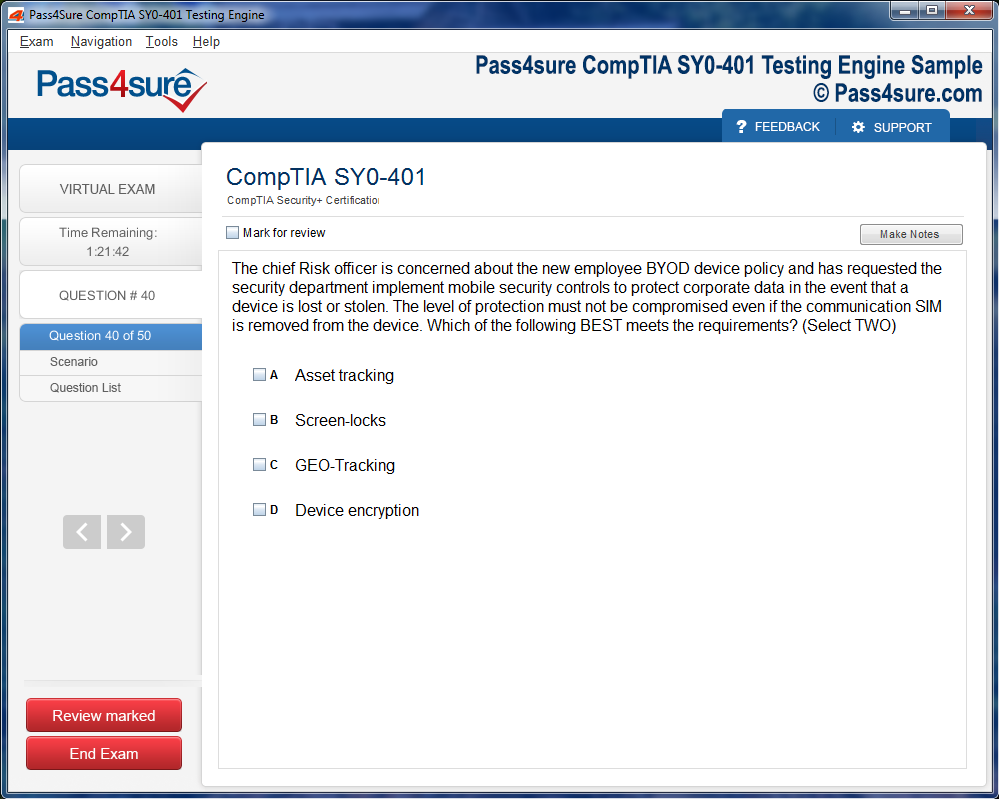
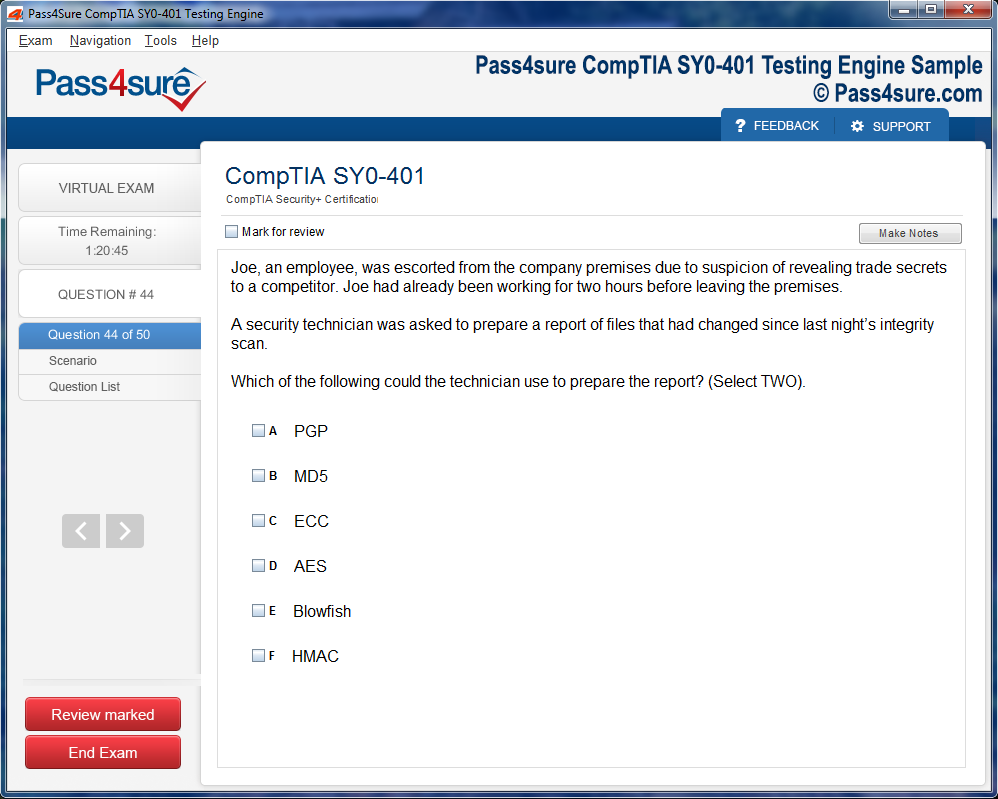
Product Screenshots
Frequently Asked Questions
How does your testing engine works?
Once download and installed on your PC, you can practise test questions, review your questions & answers using two different options 'practice exam' and 'virtual exam'. Virtual Exam - test yourself with exam questions with a time limit, as if you are taking exams in the Prometric or VUE testing centre. Practice exam - review exam questions one by one, see correct answers and explanations.
How can I get the products after purchase?
All products are available for download immediately from your Member's Area. Once you have made the payment, you will be transferred to Member's Area where you can login and download the products you have purchased to your computer.
How long can I use my product? Will it be valid forever?
Pass4sure products have a validity of 90 days from the date of purchase. This means that any updates to the products, including but not limited to new questions, or updates and changes by our editing team, will be automatically downloaded on to computer to make sure that you get latest exam prep materials during those 90 days.
Can I renew my product if when it's expired?
Yes, when the 90 days of your product validity are over, you have the option of renewing your expired products with a 30% discount. This can be done in your Member's Area.
Please note that you will not be able to use the product after it has expired if you don't renew it.
How often are the questions updated?
We always try to provide the latest pool of questions, Updates in the questions depend on the changes in actual pool of questions by different vendors. As soon as we know about the change in the exam question pool we try our best to update the products as fast as possible.
How many computers I can download Pass4sure software on?
You can download the Pass4sure products on the maximum number of 2 (two) computers or devices. If you need to use the software on more than two machines, you can purchase this option separately. Please email sales@pass4sure.com if you need to use more than 5 (five) computers.
What are the system requirements?
Minimum System Requirements:
- Windows XP or newer operating system
- Java Version 8 or newer
- 1+ GHz processor
- 1 GB Ram
- 50 MB available hard disk typically (products may vary)
What operating systems are supported by your Testing Engine software?
Our testing engine is supported by Windows. Andriod and IOS software is currently under development.
ECCouncil 312-49v10: Common Mistakes to Avoid During Your Study
The labyrinthine nature of the 312-49v10 syllabus often ensnares candidates in a vortex of cognitive overload. Attempting to internalize network forensics, malware analysis, and cryptographic subtleties simultaneously can lead to a mental saturation point where retention plummets precipitously. Cognitive overload does not merely slow learning; it actively erodes confidence, engendering a sense of intellectual futility. To navigate this, one must segment learning into digestible, interlinked modules that reinforce each other without overwhelming the neural substrates responsible for long-term memory consolidation.
The allure of multitopic cramming is deceptive. Candidates may believe that immersing themselves in a torrent of concepts accelerates mastery. Yet, the mind operates not in a linear fashion but through associative networks. Knowledge blossoms when interconnected nodes—such as threat modeling, intrusion countermeasures, and security policy enforcement—are revisited cyclically, allowing synaptic pathways to solidify. Sporadic bursts of frantic study, no matter how intense, fail to cement these cognitive linkages, leaving aspirants vulnerable to perplexing exam questions that demand integrative reasoning.
The Subtle Tyranny of Superficial Familiarity
A pernicious impediment in EC-Council preparation is the seduction of superficial familiarity. Encountering terms like asymmetric encryption or honeypot deployment may engender a false sense of mastery, yet without deliberate interrogation of each concept, understanding remains ephemeral. Superficial familiarity cultivates cognitive illusions, where learners mistakenly believe that recognition equates to comprehension. This phenomenon is particularly treacherous in scenarios where nuanced distinctions—such as differentiating between active and passive reconnaissance—determine the correctness of an answer.
Engagement that transcends mere recognition involves deconstructing frameworks, questioning methodologies, and simulating practical applications. Candidates must dissect attack vectors, scrutinize protocol vulnerabilities, and reimagine defense mechanisms in varying contexts. Only through this iterative, reflective process does comprehension crystallize, transforming abstract knowledge into actionable insight. Without it, candidates are ill-prepared for questions demanding not just recollection but synthesis, analysis, and judicious application.
The Seduction of External Distractions
Distractions manifest not only as overt interruptions but also as subtle erosions of mental acuity. The pervasive presence of digital stimuli—notifications, emails, and social media—fractures attention, diminishing the brain's capacity for sustained analytical focus. Even the most resilient aspirant finds that intermittent attention reduces the fidelity of memory encoding, particularly when grappling with multifaceted subjects like intrusion detection algorithms or cryptographic key management.
The antidote lies in crafting an environment of intentional isolation. This is not merely physical seclusion but the cultivation of temporal sanctuaries where cognitive resources are fully devoted to intricate content. Techniques such as temporal chunking, Pomodoro cycles, or ritualized pre-study preparation can scaffold concentration, allowing the mind to traverse complex domains with precision. In these deliberate silences, understanding deepens, and the mind’s natural proclivity for pattern recognition accelerates, turning rote memorization into intuitive insight.
The Insidious Nature of Misaligned Priorities
Strategic misalignment in study priorities often sabotages aspirants despite diligent effort. Many over-invest in familiar areas, basking in the comfort of competence while neglecting zones of vulnerability. For instance, a candidate adept at penetration testing may undervalue mastery in system auditing, threat intelligence interpretation, or compliance standards. This imbalance creates asymmetrical proficiency, leaving gaps that can be exploited by the nuanced demands of the 312-49v10 exam.
Mitigating this requires rigorous self-auditing and honest appraisal of knowledge lacunae. Candidates must adopt a dynamic, feedback-driven approach, continuously recalibrating study intensity based on emerging weaknesses. This is not a static endeavor; it demands iterative reassessment, agile adaptation, and a willingness to confront uncomfortable areas of incompetence. Only through this disciplined orchestration does preparation evolve from superficial coverage to holistic mastery.
The Tyranny of Impatience
Impatience is an omnipresent adversary in the learning odyssey. Many aspirants, driven by anxiety or external pressures, succumb to the temptation of rapid progression through practice questions without deliberate reflection. This superficial engagement inhibits the cognitive processes essential for deep learning: analysis, synthesis, and metacognition. True mastery emerges not from speed but from contemplative iteration, where each scenario is dissected to understand underlying principles and decision-making logic.
Deliberate practice demands patience, a willingness to traverse familiar ground repeatedly, and a focus on understanding the rationale behind both correct and erroneous approaches. It is in this measured rhythm that expertise is cultivated, transforming the candidate from a passive receiver of information into an active architect of knowledge. This method ensures readiness not merely for rote queries but for questions requiring nuanced judgment, adaptive reasoning, and integrative problem-solving.
The Mirage of Memorization
Relying on rote recall cultivates an illusory mastery that falters under nuanced scrutiny. Memorization seduces learners into believing that familiarity equates to fluency, yet complex scenarios often expose superficial comprehension. The EC-Council 312-49v10 test, with its intricate problem-solving demands, uncovers these deficiencies. Candidates who traverse only the surface of concepts may struggle to transpose memorized fragments into adaptive strategies, revealing the brittle underpinnings of their preparation.
Memorized knowledge lacks elasticity. When confronted with unexpected permutations of network intrusions or sophisticated threat matrices, static recall becomes insufficient. It is the dynamic interplay of conceptual understanding and applied reasoning that forges genuine competence. Learners must engage in cognitive gymnastics, transforming static information into malleable problem-solving tools capable of withstanding the flux of real-world scenarios.
Neglecting the Peripheries
Focusing exclusively on frequently appearing topics engenders an asymmetrical understanding. The exam’s architecture encompasses a vast continuum of skills, including reconnaissance, post-exploitation maneuvering, and governance frameworks. Candidates who sideline peripheral yet pivotal domains risk encountering unanticipated challenges. Mastery demands a panoramic approach, assimilating both central tenets and nuanced subfields, ensuring preparedness for the exam’s multidimensional landscape.
The danger lies in the seductive simplicity of repetitive practice sets. These exercises often spotlight high-probability question clusters, inadvertently narrowing intellectual horizons. True competence emerges from deliberate immersion in underrepresented areas, cultivating cognitive dexterity and reinforcing the capacity to tackle unforeseen complexities.
The Alchemy of Error Analysis
Mistakes harbor latent educational alchemy when approached with reflective rigor. Engaging passively with incorrect responses squanders these opportunities. Candidates who systematically dissect errors illuminate cognitive blind spots, fortifying both technical prowess and analytical sophistication. Recording missteps, discerning recurring patterns, and revisiting frail knowledge segments catalyze profound learning.
Error analysis transcends mere correction; it fosters anticipatory reasoning. By interrogating the rationale behind flawed selections, learners cultivate the aptitude to foresee pitfalls and adapt strategies accordingly. This iterative self-examination bridges the chasm between theoretical acumen and applied dexterity, nurturing a resilient intellectual architecture capable of withstanding the exam’s stochastic challenges.
Harmonizing Theory and Praxis
Cognitive assimilation flourishes when theoretical constructs are married to practical enactments. Knowledge of cryptography, intrusion detection, and network vulnerabilities attains profundity only when instantiated in active experimentation. Lab simulations, scenario-based exercises, and collaborative study endeavors create an experiential crucible wherein abstract principles crystallize into actionable competence.
Candidates who integrate theoretical comprehension with iterative practice develop cognitive symbiosis. This fusion enhances retention, sharpens analytical agility, and cultivates adaptability under evaluative duress. The synergy between conceptual understanding and tangible application is not merely advantageous; it is indispensable for navigating the intricate tapestry of ethical hacking assessments.
Cognitive Diversification
The human intellect thrives on heterogeneity of stimuli. Diversifying study modalities—through immersive labs, peer discussions, and reflective journaling—prevents cognitive ossification. Monotonous repetition risks intellectual atrophy, whereas multidimensional engagement invigorates memory consolidation and strategic reasoning.
A diversified cognitive regimen cultivates resilience against the unpredictable vectors of exam content. By juxtaposing contrasting perspectives, learners acquire the versatility to recalibrate thought processes in real time, rendering them impervious to rote-centric pitfalls. This mental agility transforms preparation from procedural drudgery into an explorative, high-yield endeavor.
Bridging Conceptual Chasms
Complexity often resides in the interstices between discrete knowledge domains. Overreliance on isolated practice questions neglects these conceptual lacunae, leaving candidates vulnerable to integrative challenges. Ethical hacking demands not only mastery of discrete techniques but the capacity to synthesize knowledge across reconnaissance, exploitation, and mitigation.
Bridging these chasms requires deliberate scaffolding of cognition. Learners must weave discrete threads of understanding into cohesive, operational frameworks. This synthesis cultivates fluency, enabling practitioners to navigate multifaceted scenarios with composure and precision, translating abstract comprehension into strategic execution.
The Mirage of Memorization
Many aspirants fall into the alluring trap of rote memorization, believing that cramming terminologies, acronyms, and procedural steps suffices for mastery. This approach cultivates a fragile comprehension, a mere veneer of knowledge. In cybersecurity, theoretical familiarity without experiential reinforcement often evaporates under pressure. The cognitive scaffolding provided by hands-on engagement is indispensable; without it, candidates may find themselves paralysed when confronted with unconventional scenarios or adaptive adversaries. Memorization can illuminate definitions, but it rarely nurtures the adaptive thinking or improvisational acumen required for intricate penetration testing challenges.
Ignoring the Nuances of Threat Landscapes
Cyber threats are not monolithic. Each vector carries subtle intricacies that demand more than textbook familiarity. Novices frequently overlook the ephemeral nature of exploit kits, polymorphic malware, and social engineering nuances. An exploit that succeeded yesterday may fail today due to minor system updates or configuration variations. Without immersing oneself in continuous experimentation, candidates remain blind to the mutable characteristics of threat landscapes. Recognizing patterns, deviations, and anomalies requires both keen observation and tactile interaction with simulated networks and attack scenarios, cultivating an almost instinctual awareness of digital ecosystems.
The Underestimation of Cognitive Fatigue
Ethical hacking and penetration testing require sustained cognitive agility. Exams like EC-Council 312-49v10 are designed not merely to evaluate recall but the candidate's ability to navigate cascading complexities under time pressure. Many underestimate the toll of cognitive fatigue, assuming that intellectual prowess alone suffices. Extended lab sessions, iterative simulations, and scenario-based exercises condition the mind to maintain analytical acuity. Regularly challenging oneself in environments that mimic real-world stressors enhances endurance and sharpens decision-making, transforming reactive thinking into anticipatory strategy.
Disregarding the Interplay Between Offense and Defense
A profound misunderstanding among candidates is the segregation of offensive and defensive paradigms. Ethical hacking is a dialectic process where attack and defense inform one another. Understanding exploitation techniques illuminates defensive countermeasures, and vice versa. Candidates who silo these disciplines risk partial comprehension. Laboratory practice and scenario-based drills facilitate this synthesis, revealing the feedback loop between penetration strategies and mitigation policies. This dynamic awareness empowers learners to anticipate vulnerabilities, preempt adversarial maneuvers, and respond with precision during exams and real-world applications alike.
Neglecting Documentation and Analytical Reporting
Practical skills are only valuable when effectively communicated. Many candidates underestimate the role of meticulous documentation and analytical reporting in ethical hacking. The ability to translate technical findings into coherent, actionable reports is as crucial as exploiting a vulnerability itself. Simulations that incorporate post-exploitation reporting cultivate this skill, requiring learners to justify methodologies, detail evidence, and propose remediation strategies. Developing a disciplined reporting practice bridges the gap between operational success and professional credibility, ensuring that technical mastery is both recognized and actionable.
Overlooking Adaptive Learning Strategies
Static study plans and rigid learning schedules often impede progress. Cybersecurity is an evolving domain; methods, tools, and threats mutate with alarming velocity. Aspirants who cling solely to fixed curricula may find their knowledge outdated or irrelevant. Adaptive learning strategies, such as iterative lab rotations, scenario modifications, and reflective practice, foster a growth-oriented mindset. Candidates learn to pivot, reassess assumptions, and embrace experimental approaches. This agility translates directly into exam performance, where unanticipated scenarios challenge the inflexibility of memorized responses, favoring those who have internalized the art of adaptive problem-solving.
The Perils of Superficial Networking Knowledge
Networking is the backbone of cybersecurity, yet it is frequently treated superficially in preparation. Understanding protocols, packet structures, and topology configurations demands more than cursory attention. Candidates often memorize port numbers or protocol definitions without grasping their functional interplay. Hands-on packet analysis, traffic simulation, and network architecture labs reveal subtleties that theory alone cannot convey. The ability to diagnose latency, recognize anomalous flows, and anticipate protocol-specific vulnerabilities separates superficial learners from proficient practitioners, embedding a tactical intuition essential for both examinations and fieldwork.
The Perils of Superficial Comprehension
Many aspirants succumb to the illusion of understanding, mistaking cursory familiarity for mastery. In the labyrinthine corridors of cybersecurity concepts, a superficial grasp can be perilous. Topics like penetration testing, cryptographic protocols, and intrusion detection require more than rote memorization; they demand cognitive synthesis, where interconnections between theory and practical execution are fully apprehended. Skimming through study guides without probing the underlying rationale fosters fragile knowledge structures, vulnerable to disruption under exam pressure. True comprehension arises from iterative exploration, questioning assumptions, and contextualizing information within broader cybersecurity frameworks.
Cognitive Fatigue and Retention Decay
An insidious adversary of exam readiness is cognitive fatigue, often overlooked in conventional preparation discourse. Prolonged study marathons without strategic recuperation precipitate retention decay, where previously assimilated knowledge becomes elusive. The brain, akin to a sophisticated computational matrix, requires intervals of restorative quiescence to consolidate neural pathways. Integrating mindful pauses, light physical activity, and mental decompression techniques sustains vigilance and fortifies memory consolidation. Candidates attuned to these rhythms demonstrate superior recall and resilience during high-stakes assessments, where sustained attention is non-negotiable.
Overconfidence and Misjudged Proficiency
A subtle yet treacherous phenomenon is overconfidence, where candidates overestimate their command of complex subjects. The seductive assurance of prior success can induce neglect of rigorous review and practical application. Misjudged proficiency frequently manifests in unanticipated weaknesses during simulation exercises, revealing gaps in procedural fluency or theoretical depth. Cultivating metacognitive awareness, through reflective self-assessment and adaptive feedback, mitigates this risk. Embracing humility as a cognitive posture encourages continual recalibration of strategies and fosters incremental mastery.
Ignoring Contextual Application
Knowledge in abstraction is insufficient for exams demanding situational acuity. The EC-Council 312-49v10 evaluation not only tests familiarity with terminologies but probes the ability to deploy skills in contextualized scenarios. Ignoring the nuances of application, such as network topology analysis, attack vector prioritization, and vulnerability mitigation sequencing, compromises effectiveness. Immersive exercises that simulate real-world conditions cultivate adaptive expertise, enabling candidates to navigate ambiguous problem statements with discernment and agility. Contextual intelligence emerges from iterative practice, scenario deconstruction, and reflective synthesis of outcomes.
Emotional Dysregulation During Preparation
Emotional dynamics exert a profound influence on learning efficacy, often underestimated by aspirants. Anxiety, frustration, or despondency can sabotage concentrated effort, skewing cognitive appraisal and eroding problem-solving capacity. Conversely, cultivating emotional regulation, through mindfulness, controlled breathing, or cognitive reframing, enhances focus, resilience, and creative reasoning. Candidates who integrate emotional awareness into study regimens experience amplified retention, enhanced analytical clarity, and an ability to respond dynamically to unforeseen challenges within the examination environment.
Neglecting Practical Experimentation
Cybersecurity mastery transcends theoretical knowledge; practical experimentation is indispensable. Candidates who overlook hands-on engagement with lab environments risk conceptual abstraction divorced from operational proficiency. Configuring firewalls, deploying virtual networks, and simulating attack scenarios provide tangible reinforcement of theoretical constructs. Iterative experimentation reveals latent intricacies, sharpens analytical acuity, and fosters procedural intuition. The interplay between practice and reflection transforms knowledge into actionable competence, equipping aspirants to confront both structured assessments and unpredictable real-world challenges with confidence.
The Subtle Art of Question Dissection
Mastering content is merely a fragment of exam triumph. The cerebral tapestry of examination demands acute analytical prowess, a nimbleness of cognition that transforms rote knowledge into strategic acumen. Candidates frequently succumb not to ignorance but to the labyrinthine subtleties embedded within question phrasing. Words carefully selected to elicit confusion or guide misapprehension can pivot an otherwise assured examinee into a state of uncertainty. Recognizing these lexical nuances is tantamount to decoding an esoteric cipher, where each term may conceal a pivotal clue, and each scenario beckons meticulous parsing. Cultivating the habit of interrogative scrutiny—identifying the essence of the problem, delineating constraints, and discerning the intended outcome—renders one impervious to the beguiling traps of misinterpretation.
Temporal Allocation and Cognitive Equilibrium
Time, an inexorable arbiter of success, is often mismanaged by aspirants. A single intransigent question can usurp the temporal bandwidth intended for multiple items, engendering cognitive strain and precipitating suboptimal performance. Mastery lies not merely in knowledge retention but in the orchestration of temporal economy, balancing rapid cognition with methodical precision. Each question warrants an equilibrium of focus: neither cursory neglect nor obsessive rumination should dominate. A measured approach, attuned to the rhythm of the examination, allows for comprehensive coverage, preventing both the hasty misstep and the paralysis induced by over-analysis.
The Elegance of Eliminative Reasoning
When certainty falters, the judicious employment of eliminative reasoning emerges as a formidable stratagem. Systematically excluding implausible alternatives heightens the probability of selecting the correct answer, transforming uncertainty into a calculable advantage. This technique, a cerebral sieve, filters distractions and distills clarity from ambiguity. When coupled with informed conjecture, it empowers candidates to transcend mere memorization, leveraging analytical dexterity to optimize outcomes. In essence, educated guessing becomes not a fallback but a tactical maneuver, a cognitive fulcrum upon which exam success pivots.
Scenario-Based Cognition and Contextual Acuity
Many examination items are not merely questions but microcosms of real-world scenarios, demanding a fusion of contextual acuity and applied reasoning. Candidates who navigate these scenarios superficially often overlook latent cues, misaligning their responses with the nuanced intent of the item. Immersing oneself in scenario-based cognition entails envisioning the practical implications of each variable, hypothesizing consequences, and aligning decisions with both explicit and implicit directives. This cognitive simulation cultivates a multidimensional understanding, enabling the examinee to traverse complex questions with confidence and foresight.
Strategic Review and Error Mitigation
A meticulous review is the guardian against inadvertent errors, often overlooked by even the most diligent candidates. Re-examination of flagged items, particularly those riddled with intricate detail, can illuminate subtle discrepancies previously unnoticed. Structured review transforms second-glance scrutiny from a perfunctory exercise into an instrument of precision, amplifying accuracy and reinforcing mastery. By integrating a systematic reassessment into the examination workflow, candidates safeguard against lapses induced by fatigue or oversight, ensuring that their performance reflects both knowledge and meticulous attention.
Cognitive Resilience and Stress Modulation
Examination success is inextricably linked to psychological equilibrium. The confluence of high stakes, complex material, and time constraints can catalyze stress, impairing memory retrieval and analytical acuity. Cultivating cognitive resilience—through disciplined breathing, adaptive pacing, and mental rehearsal—fortifies the mind against these pressures. Stress modulation is not merely ancillary; it is a fulcrum upon which clarity and composure balance, enabling candidates to execute strategies with deliberation rather than impulsivity. The most adept examinees navigate the dual terrain of intellectual challenge and psychological pressure with equal dexterity.
Integrating Strategic Insights with Mastery
Ultimately, the nexus of content mastery and strategic execution defines examination performance. Knowledge without strategy is impotent; strategy without understanding is precarious. Candidates who harmonize these elements approach each item not as a puzzle to be brute-forced but as a cognitive landscape to be traversed with foresight and discernment. They cultivate an intellectual choreography, moving fluidly between comprehension, elimination, contextual reasoning, and review, transforming each question into an opportunity to demonstrate precision and analytical artistry.
The Danger of Relying on Outdated Resources
Finally, one of the most insidious mistakes is using outdated or incomplete study materials. The field of ethical hacking and cybersecurity evolves rapidly, with new vulnerabilities, tools, and protocols emerging continually. Resources that do not reflect current best practices or exam updates may provide misleading guidance, resulting in knowledge gaps.
Candidates relying on older guides may encounter obsolete terminology, deprecated tools, or archaic procedures. For instance, a security exploit referenced in legacy material may no longer be relevant, while newer attack vectors or defensive strategies are omitted. This discrepancy can breed confusion and misdirected study effort, eroding the efficacy of preparation and sapping confidence.
Cross-referencing multiple sources, including official EC-Council updates, contemporary articles, and interactive labs, ensures a panoramic and current understanding. Engaging with community discussions, forums, or study groups can illuminate emergent trends, reinforce practical application, and foster a dynamic cognitive map of cybersecurity landscapes. This syncretic approach cultivates resilience against the pitfalls of static knowledge.
A further hazard lies in overconfidence spawned by outdated practice tests. Memorizing questions that no longer mirror the current exam framework may inflate perceived readiness while leaving critical areas unexamined. Candidates might glide through familiar scenarios yet falter when confronted with contemporary threats or nuanced protocols. This illusory competence can be perilous, both in examination and real-world scenarios.
Equally subtle is the cognitive inertia induced by entrenched materials. When learners anchor on legacy references, their mental models of attack vectors, penetration techniques, and defensive mechanisms calcify, obstructing adaptability. In an arena defined by ceaseless innovation, such rigidity undermines strategic acuity. Incorporating updated resources with continuous review, hands-on practice, and deliberate experimentation fosters a holistic mastery that transcends rote memorization.
Moreover, embracing emergent technologies and paradigms sharpens analytical dexterity. Experimentation with virtual labs, simulation environments, and sandboxed exploits allows candidates to interrogate theoretical knowledge in a controlled yet authentic context. Observing the interplay between novel attack vectors and evolving defense protocols cultivates anticipatory thinking, a faculty indispensable for ethical hackers navigating the labyrinthine domains of modern cybersecurity.
Equally crucial is a nuanced understanding of the temporal dimension of vulnerabilities. Not all exploits are static; some mutate, while patch cycles and firmware updates can obsolesce once-critical weaknesses. Resources failing to account for this temporal dynamism impart a misleading impression of permanence, while practitioners steeped in current intelligence remain attuned to transient threats and ephemeral system flaws.
Immersion in communities and forums offers another vector for resilience against obsolescence. Peer discourse often surfaces emerging zero-day exploits, evolving regulatory requirements, and unconventional attack methodologies absent from mainstream literature. Such interactions nurture heuristic flexibility, enabling candidates to adapt conceptual frameworks and operational tactics in real time.
Finally, integrating updated resources with strategic study rituals, methodical note-taking, and scenario-based problem solving cements a durable, practical knowledge base. Those who remain tethered to antiquated guides risk the twin perils of redundancy and inadequacy. Conversely, candidates who champion a philosophy of continuous renewal align themselves not merely with exam success but with the enduring exigencies of real-world cybersecurity practice.
The Illusion of Comprehensive Knowledge
A pervasive misstep among aspiring ethical hackers is succumbing to the illusion of comprehensive knowledge. One might amass vast quantities of study material, memorize technical jargon, or simulate known exploits, yet still harbor critical blind spots. This phenomenon, often exacerbated by an overreliance on static resources, masks the inherent complexity of cybersecurity domains. Knowledge, in this context, is not a mere aggregation of facts but a dynamic interplay of situational understanding, adaptive strategy, and experiential insight.
Illusory competence frequently manifests when candidates encounter unconventional system architectures or hybridized attack vectors absent from traditional learning texts. An exploit pattern that succeeds in a virtual lab may falter when confronted with nuanced real-world system behaviors. Without a mindset attuned to adaptation and iterative problem solving, learners risk cultivating brittle expertise that collapses under the weight of unforeseen contingencies.
Moreover, ethical hacking is an arena defined by polymorphic threats. Malware, social engineering schemes, and zero-day vulnerabilities often evade standard heuristics, rendering rote memorization insufficient. Embracing cognitive elasticity—flexibility of thought, rapid synthesis of novel information, and anticipatory reasoning—becomes paramount. Those who mistake breadth of content for depth of understanding may find themselves ill-prepared for the fluid, unpredictable landscapes of live penetration testing.
Cognitive Overload and Strategic Misalignment
Another subtle yet formidable hazard is cognitive overload. The sheer volume of cybersecurity concepts, from network protocols and cryptographic algorithms to threat intelligence frameworks, can overwhelm even seasoned learners. When compounded by outdated resources or repetitive rote exercises, mental saturation can precipitate errors in judgment, misapplication of techniques, and ultimately, a decline in learning efficacy.
Strategic misalignment often accompanies overload. Candidates may prioritize familiar content at the expense of emerging topics, skewing preparation toward comfort zones rather than areas of highest practical significance. For instance, overemphasis on deprecated attack tools can consume cognitive bandwidth that would be better allocated to understanding contemporary vulnerabilities, cloud security paradigms, or advanced threat modeling. Recognizing the limits of one’s cognitive reservoir and distributing focus deliberately is essential for cultivating both competence and confidence.
Equally important is metacognition—awareness and regulation of one’s own learning processes. Ethical hackers who actively monitor their comprehension, evaluate the reliability of sources, and iteratively recalibrate study strategies mitigate the risk of cognitive bottlenecks. Conversely, those who passively consume outdated content may unknowingly entrench misconceptions, compounding the challenges posed by evolving technological ecosystems.
The Seduction of Simplistic Frameworks
Simplistic frameworks, though appealing for their apparent clarity, often conceal more than they reveal. Step-by-step guides or prescriptive methodologies can lull candidates into complacency, fostering a mechanical approach devoid of critical inquiry. While frameworks provide useful scaffolding, overreliance may inhibit the development of analytical reasoning necessary to navigate ambiguous scenarios or hybridized attack surfaces.
Cybersecurity is intrinsically probabilistic. No two systems respond identically to penetration attempts, and no singular methodology guarantees success. Ethical hackers must therefore cultivate the capacity to interrogate assumptions, anticipate countermeasures, and improvise tactically. Simplistic adherence to procedural scripts may yield superficial results in controlled exercises but falters when confronted with adaptive adversaries or atypical configurations.
Moreover, the seductive clarity of frameworks can mask underlying epistemic uncertainty. Candidates may falsely equate procedural compliance with mastery, neglecting the deeper conceptual foundations that underpin security principles. Integrating theoretical insight with hands-on experimentation, and juxtaposing multiple frameworks for comparative analysis, nurtures a nuanced comprehension resilient to the limitations of prescriptive instruction.
Temporal Fluidity of Vulnerabilities
A dimension often underappreciated by learners is the temporal fluidity of vulnerabilities. Security weaknesses are seldom static; they evolve in response to patch cycles, software updates, and shifting threat landscapes. An exploit effective yesterday may be rendered obsolete today, while novel attack vectors emerge with increasing frequency. Resources that fail to capture this temporal dynamism impart a distorted sense of permanence, undermining the practitioner’s preparedness for real-world engagements.
Temporal fluidity extends beyond technical exploits to procedural and regulatory dimensions. Compliance requirements, ethical guidelines, and best practice protocols are subject to continual revision. Ethical hackers who neglect these temporal shifts risk both operational inefficacy and inadvertent violations of legal or ethical boundaries. Continuous monitoring of updates, integration of real-time threat intelligence, and iterative validation of knowledge against current standards are indispensable for sustaining relevance.
Understanding temporal fluidity also sharpens anticipatory reasoning. Candidates attuned to ephemeral threats can forecast likely exploit trajectories, model system vulnerabilities under evolving conditions, and proactively devise mitigations. This foresight transforms static learning into strategic intelligence, bridging the gap between academic preparation and operational competency.
Experiential Learning as a Cornerstone
Experiential learning is arguably the most potent antidote to the pitfalls of outdated or superficial resources. Simulated environments, virtual labs, and controlled penetration exercises immerse candidates in lifelike scenarios, enabling the translation of abstract knowledge into actionable skill. This immersion cultivates situational awareness, hones tactical improvisation, and reinforces the cognitive pathways essential for complex problem solving.
Active experimentation encourages reflective learning. Each interaction with a system, each test of an exploit, produces feedback that refines both technique and understanding. Learners develop a metacognitive loop: hypothesize, implement, observe, and adjust. This iterative process cultivates not only technical proficiency but also the analytical acumen necessary to anticipate novel threats and devise resilient defenses.
Moreover, experiential learning nurtures an appreciation for systemic interdependencies. Security breaches rarely occur in isolation; they exploit the interplay of hardware, software, human factors, and procedural vulnerabilities. Practical engagement illuminates these interconnections, transforming abstract diagrams and theoretical constructs into tangible, operational insight. Candidates who prioritize such immersive experiences cultivate the dexterity and foresight indispensable for real-world cybersecurity challenges.
Community Intelligence and Collaborative Insight
No candidate thrives in isolation. The cybersecurity domain is inherently collaborative, reliant on shared intelligence, peer review, and community vigilance. Engagement with forums, study groups, and professional networks exposes learners to diverse perspectives, emergent techniques, and heuristic strategies that may be absent from conventional texts. This collective intelligence functions as a real-time corrective to outdated or incomplete resources, offering immediate insight into contemporary threats, tools, and methodologies.
Collaborative environments also foster epistemic humility. Exposure to divergent experiences and unconventional problem-solving approaches challenges assumptions and broadens cognitive flexibility. Candidates who internalize this dynamic benefit not merely from accumulated knowledge but from an enhanced capacity to synthesize, evaluate, and apply insights in novel contexts.
Furthermore, community engagement accelerates the identification of patterns and anomalies. Collective discussions often surface subtle trends in attack methodologies, emerging defensive architectures, and innovative exploit mitigations. For learners, participation in these networks provides both situational awareness and a scaffold for strategic foresight, ensuring that preparation remains contemporaneous with the evolving threat landscape.
The Intricacies of Lexical Subtleties
Examinations, particularly those with nuanced professional content, are replete with lexical subtleties that often elude cursory reading. Each word carries the potential to redirect thought, to bifurcate understanding into clarity or confusion. Candidates must cultivate an almost forensic attention to diction, discerning between terms that appear synonymous yet possess discrete implications. Prepositions, modifiers, and auxiliary verbs can transform the trajectory of a question entirely, necessitating a meticulous parsing of syntax. This hyperawareness elevates simple reading to a form of intellectual exegesis, where the candidate interrogates each clause, each phrase, and each embedded condition as if deciphering an arcane manuscript.
The most sagacious examinees treat questions not as static prompts but as dynamic cognitive entities. Each scenario is a puzzle whose resolution is encoded in its vocabulary. For instance, temporal qualifiers like “initially” or “ultimately” can alter the sequence of reasoning required, while conditional phrasing such as “if…then” structures the logical pathway of analysis. By internalizing these subtleties, candidates develop a mental acuity that transcends rote memorization, approaching questions with strategic foresight.
Harmonizing Speed with Precision
Time management is not merely about counting minutes but orchestrating cognitive tempo. Rapid execution without comprehension invites catastrophic error, while protracted rumination saps energy and engenders stress. Achieving a harmonious balance between speed and precision requires not only practice but the development of an instinctual sense of pacing. Experienced candidates learn to calibrate their mental tempo, shifting seamlessly from rapid recognition in familiar domains to slower, contemplative analysis in areas of ambiguity.
This mental choreography is augmented by the ability to recognize patterns of question types. Certain items, by their structure or content, signal the necessity for swift resolution, while others demand careful scrutiny. Training oneself to detect these patterns allows for the strategic allocation of cognitive resources, minimizing the risk of bottlenecking on particularly convoluted questions and ensuring a steady, resilient approach throughout the examination.
The Subtle Power of Pattern Recognition
Pattern recognition is an underappreciated yet formidable component of examination mastery. Beyond factual knowledge, candidates who cultivate the ability to intuit structural patterns, recurring scenario frameworks, and thematic consistencies gain a disproportionate advantage. Such recognition functions as a mental shorthand, reducing cognitive load and accelerating decision-making.
This process is not mere rote pattern matching but an active, interpretive engagement. For example, identifying a familiar scenario archetype may suggest the presence of distractors crafted to exploit common misconceptions. Awareness of these patterns permits candidates to anticipate pitfalls, bypassing superficial allure and zeroing in on the substantive elements that dictate correctness. The capacity to recognize and leverage such recurring structures is the hallmark of an expert examinee.
Cognitive Flexibility in Scenario Navigation
Examination questions often present multifaceted scenarios, interweaving variables that must be reconciled through flexible cognition. Candidates who rigidly adhere to linear reasoning may falter when confronted with complex interactions or counterintuitive contingencies. Cognitive flexibility—the ability to pivot mental strategies, to reassess assumptions in real time—is therefore indispensable.
Flexible cognition is cultivated through iterative exposure to diverse question types and hypothetical constructs. By rehearsing mental simulations, candidates train themselves to navigate ambiguity with confidence, to evaluate alternatives, and to anticipate the ramifications of different choices. This adaptability transforms the examination from a static test of knowledge into a dynamic interplay of analysis, synthesis, and discernment.
The Strategic Role of Mental Rehearsal
Mental rehearsal, a technique often relegated to the periphery of preparation, wields profound influence over examination outcomes. By visualizing the process of encountering questions, deliberating choices, and allocating attention, candidates embed procedural fluency into memory. Such rehearsal fortifies cognitive pathways, ensuring that strategic execution becomes almost reflexive under the duress of timed assessment.
This technique extends beyond mere visualization of steps; it encompasses emotional conditioning. Anticipating stressors, rehearsing composure, and simulating the cognitive tension of the exam environment inoculates candidates against anxiety-induced impairment. The mind, having experienced a controlled rehearsal of the testing scenario, responds with calibrated efficiency when confronted with the actual challenge.
Error Analysis as a Learning Catalyst
Error analysis is an often-overlooked instrument of mastery. Beyond the immediate desire to achieve a correct answer lies the deeper opportunity to examine missteps, uncover reasoning flaws, and refine cognitive heuristics. Each error represents a latent insight, a clue to underlying vulnerabilities in comprehension or strategy.
Candidates who systematically dissect their mistakes cultivate a self-corrective feedback loop. By cataloging the types of errors—whether lexical misinterpretation, hasty judgment, or misaligned reasoning—they develop targeted interventions. This iterative refinement process not only reduces future mistakes but fosters a resilient mindset attuned to continual improvement, ensuring that knowledge and strategy evolve synergistically.
Scenario Anticipation and Proactive Reasoning
Proactive reasoning entails anticipating potential question trajectories before committing to an answer. By predicting likely outcomes, identifying embedded traps, and pre-emptively evaluating contingencies, candidates convert passive reading into active strategizing. This forward-thinking approach mitigates the risk of being ensnared by cleverly worded scenarios, allowing examinees to navigate complex questions with foresight and confidence.
Scenario anticipation also intersects with analytical triangulation. By cross-referencing multiple elements within a question and mentally modeling the interplay of conditions, candidates construct a cognitive map that guides decision-making. This preemptive modeling transforms the exam from a reactive challenge into a terrain navigable with deliberate insight, reducing reliance on chance or instinctual guessing.
Harnessing Cognitive Chunking
Cognitive chunking, the grouping of information into manageable conceptual units, is a powerful technique for processing intricate examination content. By organizing disparate facts, rules, and scenarios into coherent clusters, candidates reduce mental load, increase retrieval speed, and enhance accuracy. Chunking transforms overwhelming complexity into digestible structures, allowing rapid assessment of options without sacrificing analytical depth.
Effective chunking requires strategic foresight. Candidates must determine which elements are contextually interdependent, which principles recur across scenarios, and which cues are pivotal for discriminating between options. This meta-cognitive awareness elevates simple memory recall to a sophisticated cognitive strategy, one that converts the labyrinthine landscape of questions into a navigable architecture of interlinked concepts.
The Imperative of Adaptive Focus
Adaptive focus is the capacity to modulate attentional intensity in response to question complexity and cognitive fatigue. Candidates must oscillate between broad overview when scanning scenarios and micro-level scrutiny when evaluating nuanced details. The failure to adjust focus appropriately often results in oversight, misinterpretation, or inefficient time usage.
Cultivating adaptive focus entails both practice and mindfulness. Techniques such as deliberate pacing, momentary cognitive resetting, and selective attention allocation enhance the brain’s ability to deploy resources judiciously. Through this adaptive control, candidates maintain vigilance without succumbing to cognitive depletion, ensuring sustained performance across the duration of the examination.
The Allure of Passive Learning
Passive learning is a siren that lures many candidates into a deceptive comfort zone. Simply reading textbooks or watching tutorial videos without active engagement fosters ephemeral understanding. In cybersecurity, ephemeral knowledge is perilous; protocols, exploit frameworks, and encryption algorithms must be internalized through rigorous interaction. Active learning strategies—such as problem-solving exercises, whiteboard mapping, or peer discussion—stimulate cognitive elasticity. By interrogating concepts, experimenting with simulations, and synthesizing disparate knowledge threads, learners construct robust mental schemas that endure under exam pressure. The dichotomy between passive familiarity and active mastery often defines the boundary between mediocrity and excellence.
Disregarding Interdisciplinary Integration
A frequent oversight is treating cybersecurity knowledge in isolation, without appreciating its interdisciplinary interconnections. Network security, cryptography, ethical hacking, and regulatory compliance exist not as discrete silos but as an interconnected web. Ignoring these linkages reduces analytical versatility and diminishes the capacity to navigate multifaceted exam scenarios. Candidates who cultivate integrative thinking—mapping correlations between protocols, vulnerabilities, and mitigation strategies—develop a cognitive framework that supports rapid inference and adaptive decision-making. Interdisciplinary synthesis transforms rote memorization into dynamic, situational intelligence.
The Mirage of Shortcuts
Many aspirants succumb to the illusion of shortcuts, chasing quick fixes through condensed guides or memorization apps. This approach cultivates brittle knowledge susceptible to failure when confronted with nuanced questions. The EC-Council 312-49v10 assessment rewards depth, contextual awareness, and procedural dexterity, which cannot be circumvented by superficial expedience. Embracing deliberate, iterative practice—where challenging concepts are dissected, tested, and revisited—fortifies cognitive resilience. Shortcuts may promise efficiency, but only sustained, methodical engagement guarantees enduring proficiency and exam readiness.
The Seduction of Over-specialization
While deep knowledge in specific domains is valuable, over-specialization can generate blind spots. Candidates who concentrate exclusively on favored topics, such as cryptography, may neglect equally critical areas like network monitoring, intrusion analysis, or vulnerability assessment. This imbalance manifests in uneven performance, where strengths mask underlying deficiencies. Strategic breadth, paired with depth, ensures comprehensive coverage. A disciplined rotation across topics, integrating both foundational and advanced subjects, creates a balanced cognitive portfolio that supports holistic competence under timed conditions.
Mismanagement of Study Environment
The study environment profoundly influences concentration, retention, and engagement. Cluttered, noisy, or distracting spaces compromise attention and cognitive throughput, while well-structured environments enhance focus. Optimal environments are curated to minimize interruptions, regulate lighting, and support ergonomic posture. Sensory modulation—through ambient sound, aromatherapy, or controlled visual stimuli—can further augment cognitive receptivity. Candidates who cultivate disciplined environmental awareness transform their study sessions into immersive, high-efficiency learning experiences.
The Tyranny of Perfectionism
Perfectionism, while superficially virtuous, can sabotage progress. Candidates fixated on flawless comprehension or execution often experience paralysis, procrastination, or excessive revision cycles. The pursuit of unattainable standards diverts energy from practical application and iterative learning. Embracing a mindset of progressive refinement—where errors are leveraged as learning opportunities—enhances resilience and knowledge consolidation. In cybersecurity preparation, calculated imperfection fosters experimentation, creativity, and adaptive problem-solving, attributes essential for both exams and professional practice.
Avoiding Self-Assessment
Neglecting self-assessment is akin to navigating a labyrinth blindfolded. Without evaluating one’s strengths and weaknesses through quizzes, mock exams, or scenario-based exercises, candidates cannot identify gaps or calibrate their study strategies. Self-assessment provides crucial feedback loops, enabling targeted reinforcement and reducing wasted effort on topics already mastered. Iterative evaluation cultivates metacognitive awareness, allowing candidates to anticipate challenges, adapt pacing, and refine approaches. Regular, rigorous self-assessment is a compass guiding preparation toward maximal efficacy.
Underestimating Complexity of Practical Scenarios
Exam questions often simulate real-world dilemmas, demanding synthesis of multiple concepts. Candidates who underestimate this complexity may apply rote procedures without critical judgment, leading to errors. Practical scenarios frequently require interpreting ambiguous information, prioritizing interventions, and anticipating consequences. Engaging with practice labs, capture-the-flag exercises, and scenario mapping develops analytical agility, enhancing the ability to navigate multifactorial challenges. Mastery emerges not from isolated knowledge units but from the capacity to orchestrate diverse cognitive elements in concert.
Neglecting Emerging Threat Paradigms
The cybersecurity landscape evolves relentlessly, introducing novel attack vectors, threat paradigms, and defensive technologies. Candidates who anchor preparation solely in established knowledge risk obsolescence. Understanding emerging threats—such as AI-driven intrusion, advanced persistent threats, or zero-day exploits—demands continuous engagement with current research, whitepapers, and practical experimentation. Anticipatory knowledge enhances exam performance by providing context for scenario-based questions and cultivating cognitive flexibility in evaluating unconventional solutions. Candidates attuned to evolution within the field demonstrate both preparedness and professional foresight.
Cognitive Overload Through Excessive Content
Excessive content consumption without strategic filtration generates cognitive overload, where the volume of information surpasses the brain’s processing capacity. This phenomenon erodes retention, induces anxiety, and diminishes problem-solving acuity. Prioritization, selective focus, and thematic clustering of content allow candidates to navigate complexity without overwhelming their cognitive bandwidth. Structured synthesis, summarization, and conceptual mapping reduce mental clutter, enabling deeper comprehension and efficient retrieval. Managing information influx is as critical as mastering content itself, ensuring sustainable and effective preparation.
The Pitfall of Ignoring Review Cycles
Review is not a passive ritual but a critical mechanism for knowledge consolidation. Ignoring structured review cycles leads to progressive decay of memory traces, particularly for intricate technical details. Spaced repetition, iterative practice, and cyclical reinforcement strengthen neural encoding, enhancing long-term retention. Candidates who incorporate systematic review transform transient learning into durable competence. Strategic reflection and revisitation of previously studied material mitigate the risk of forgotten concepts, ensuring comprehensive preparedness even under temporal constraints.
Disregarding Cognitive Anchoring Techniques
Cognitive anchoring—associating new knowledge with established mental frameworks—is a potent tool for retention and retrieval. Candidates who neglect anchoring struggle to contextualize complex concepts, leading to fragmented understanding. Anchoring techniques, such as analogical reasoning, narrative structuring, and cross-linking with prior knowledge, embed information within a durable cognitive scaffold. These strategies facilitate rapid recall during exam scenarios, where the ability to navigate interconnected ideas under pressure is paramount. Effective anchoring converts isolated data points into coherent, actionable intelligence.
Misjudging the Complexity of Web Application Security
A recurrent miscalculation among EC-Council candidates is underestimating the labyrinthine intricacies of web application security. Superficial knowledge of cross-site scripting, SQL injections, or session hijacking often fails to translate into actionable skill. Web platforms are living architectures, constantly patched, reconfigured, and optimized. Candidates who neglect the experiential examination of these ecosystems cannot appreciate the subtleties of layered vulnerabilities. Lab exercises that simulate real-world web infrastructures illuminate the interdependencies between front-end logic, back-end databases, and authentication mechanisms, cultivating an intuition for exploitation that transcends rote theory.
The Fallacy of Single-Domain Focus
Aspiring ethical hackers frequently pigeonhole their studies, obsessively focusing on one domain—such as network penetration or malware analysis—while neglecting complementary disciplines. Cybersecurity is inherently interdisciplinary. Reconnaissance, vulnerability assessment, exploitation, post-exploitation, and reporting form a cohesive continuum. Neglecting any link in this chain diminishes overall efficacy. Structured simulation exercises compel candidates to traverse multiple domains within a single scenario, revealing synergies and emergent challenges. This holistic comprehension nurtures fluency in both strategy and execution, an indispensable asset for exams that prize applied competence over mere recollection.
Overlooking Social Engineering Dynamics
Social engineering remains one of the most potent, yet frequently undervalued, vectors in penetration testing. Candidates often regard it as ancillary, relegated to theoretical consideration. However, successful exploitation of human factors demands acute psychological acuity and practical rehearsal. Role-playing simulations, phishing scenario drills, and behavioral analysis exercises cultivate sensitivity to human susceptibilities, communication patterns, and anomaly detection. Neglecting this dimension produces a myopic understanding of security, where technological prowess cannot compensate for unrecognized human vulnerabilities, both in examination contexts and operational practice.
Neglecting Endpoint and Mobile Security
Endpoints and mobile devices represent a sprawling, heterogeneous landscape. Many candidates assume that mastery of desktop or server security suffices, overlooking the nuances inherent in mobile operating systems, app sandboxing, and device-specific exploit vectors. Practical engagement with virtualized endpoints, mobile emulators, and exploit frameworks fosters familiarity with platform-specific idiosyncrasies. Understanding application permissions, inter-process communication, and ephemeral session management provides the cognitive scaffolding for rapid identification of threats and countermeasures. Without hands-on exposure, candidates risk the illusion of competence, knowing procedures conceptually but failing to execute them reliably.
The Consequences of Ignoring Vulnerability Lifecycle
Vulnerabilities are not static phenomena; they traverse a lifecycle from discovery to exploitation to mitigation. Many learners overlook this temporal dimension, memorizing static exploits without understanding their evolution or remediation implications. Hands-on labs that simulate vulnerability discovery, patch deployment, and exploit adaptation cultivate temporal reasoning. Candidates learn to anticipate emergent weaknesses, adapt methodologies dynamically, and appreciate the interconnectedness of discovery, exploitation, and defense. This perspective transforms isolated technical knowledge into strategic insight, enhancing both practical proficiency and examination performance.
Misapprehending Cryptographic Applications
Cryptography is a domain rich with abstruse principles and subtle pitfalls. Candidates often memorize algorithms, key lengths, and hash functions without internalizing their practical applications, strengths, and limitations. Experiential engagement—configuring encryption protocols, analyzing cipher weaknesses, and simulating attacks—renders abstract concepts tangible. For instance, implementing asymmetric and symmetric encryption in lab networks elucidates performance trade-offs, attack vectors, and potential vulnerabilities. Without such exposure, candidates retain a superficial awareness of cryptographic theory but remain incapable of nuanced application in scenarios demanding real-time judgment.
Overlooking Log Analysis and Forensic Skills
Digital forensics is a cornerstone of ethical hacking, yet its significance is frequently underestimated. Candidates may familiarize themselves with terminology and toolsets but lack the hands-on experience needed to reconstruct timelines, analyze logs, or trace intrusion patterns. Lab-based exercises that involve interpreting system logs, recovering deleted files, and correlating multi-source data cultivate investigative instincts. This practice fosters the analytical rigor necessary for identifying subtle attack signatures, understanding adversary behavior, and crafting comprehensive incident reports—capabilities that theory alone cannot instill.
Underestimating the Power of Iterative Failure
Failure is often stigmatized, yet in ethical hacking education, it serves as a catalyst for mastery. Candidates who avoid experimentation to prevent mistakes curtail their learning potential. Simulation platforms provide safe arenas for iterative failure, enabling repeated attempts at complex exploits, misconfigurations, and defensive bypasses. Each unsuccessful attempt crystallizes understanding, revealing hidden dependencies and overlooked vectors. Over time, these micro-failures accumulate into cognitive resilience, sharpening analytical judgment and reinforcing procedural memory. Avoiding failure, conversely, fosters brittle knowledge that collapses under unexpected examination scenarios.
Misjudging the Importance of Patch Management and Update Analysis
Patch management is frequently trivialized in preparatory study. Candidates may know the theoretical importance of updates but fail to appreciate the operational nuances of applying patches without disruption or introducing new vulnerabilities. Practical exercises involving controlled patch deployment, version testing, and regression analysis cultivate a meticulous approach to system maintenance. Understanding the cascading effects of updates, their timing, and compatibility with security policies equips candidates with foresight, enabling them to anticipate and mitigate emergent vulnerabilities both in labs and real-world networks.
Disregarding the Psychological Component of Red Team Exercises
Red team operations are not purely technical exercises; they demand psychological acuity, strategic deception, and adaptive improvisation. Candidates unacquainted with these dimensions may execute technically correct procedures but fail to achieve meaningful outcomes. Participation in simulated red team scenarios enhances situational awareness, adaptive reasoning, and anticipatory strategy formulation. Observing human and systemic responses to intrusion attempts provides insight into defense mechanisms and behavioral patterns, transforming mechanical knowledge into nuanced operational competence.
Neglecting the Integration of Security Tools
The proliferation of cybersecurity tools—scanners, intrusion detection systems, packet analyzers—can overwhelm candidates who focus solely on memorizing functionalities. True proficiency emerges when these tools are integrated into coherent workflows. Hands-on labs enable learners to configure multi-tool pipelines, interpret cross-tool data, and derive actionable intelligence from composite outputs. Understanding the interplay between automation, manual analysis, and strategic decision-making cultivates operational dexterity, ensuring that candidates are prepared to translate tool output into meaningful, context-sensitive actions.
The Pitfalls of Over-Reliance on Study Guides
Study guides, while convenient, can create cognitive complacency. Candidates who rely excessively on condensed materials often develop tunnel vision, internalizing selective examples rather than cultivating generalizable problem-solving frameworks. Experiential learning, scenario simulation, and self-directed experimentation challenge assumptions, revealing gaps that guides cannot anticipate. Integrating structured labs with independent exploration fosters adaptive cognition, enabling learners to navigate novel exam scenarios and complex real-world challenges with confidence.
Ignoring Lateral Thinking in Security Scenarios
Cybersecurity is as much a mental discipline as a technical one. Candidates who rely solely on linear reasoning often falter when confronted with multi-step, non-obvious attack paths. Lateral thinking—considering unconventional angles, exploiting indirect vectors, and anticipating cascading effects—is cultivated through complex lab exercises, scenario reconstruction, and adversarial simulations. Practicing cognitive flexibility prepares candidates to identify hidden opportunities and threats, enhancing both exam performance and operational ingenuity.
Overlooking the Interconnection Between Policy and Technical Practice
Technical proficiency alone is insufficient without an understanding of policy frameworks and regulatory constraints. Ethical hackers must navigate a landscape where legality, compliance, and operational mandates intersect with technical execution. Hands-on exercises that simulate real-world constraints—such as permissions, access controls, and audit requirements—foster an appreciation of this interplay. Recognizing the consequences of misalignment between policy and practice ensures that candidates can perform ethical assessments responsibly, demonstrating competence that extends beyond technical acumen to professional judgment.
Conclusion
Avoiding common pitfalls is the key to succeeding in the EC-Council 312-49v10 exam. Consistency, hands-on practice, and thoughtful study strategies form the foundation of effective preparation, while overreliance on practice questions, poor time management, and outdated resources can silently undermine progress. Candidates who approach their studies with discipline, curiosity, and adaptability not only improve exam performance but also cultivate skills that extend beyond the test, empowering them to navigate the dynamic world of cybersecurity with confidence.
True mastery emerges when preparation is intentional, mistakes are transformed into learning opportunities, and knowledge is continuously applied in practical scenarios. By embracing these principles, aspirants position themselves for success, achieving both the certification and the real-world proficiency that the EC-Council 312-49v10 embodies.
Top ECCouncil Exams
- 312-50v13 - Certified Ethical Hacker v13
- 312-39v2 - Certified SOC Analyst (CSA) v2
- 312-38 - Certified Network Defender
- 712-50 - EC-Council Certified CISO
- 212-89 - EC-Council Certified Incident Handler
- 312-85 - Certified Threat Intelligence Analyst
- 212-82 - Certified Cybersecurity Technician
- 312-50 - CEH Certified Ethical Hacker (312-50v9)
- 312-39 - Certified SOC Analyst
- 312-97 - Certified DevSecOps Engineer (ECDE)
- 312-49v11 - Computer Hacking Forensic Investigator
- 312-49 - Computer Hacking Forensic Investigator
- 312-49v10 - Computer Hacking Forensic Investigator
- 312-40 - Certified Cloud Security Engineer
- 312-76 - EC-Council Disaster Recovery Professional
- 312-50v12 - Certified Ethical Hacker v12 Exam
- 212-81v3 - EC-Council Certified Encryption Specialist
- ECSS - EC-Council Certified Security Specialist