Exam Code: HPE6-A79
Exam Name: Aruba Certified Mobility Expert Written Exam
Certification Provider: HP
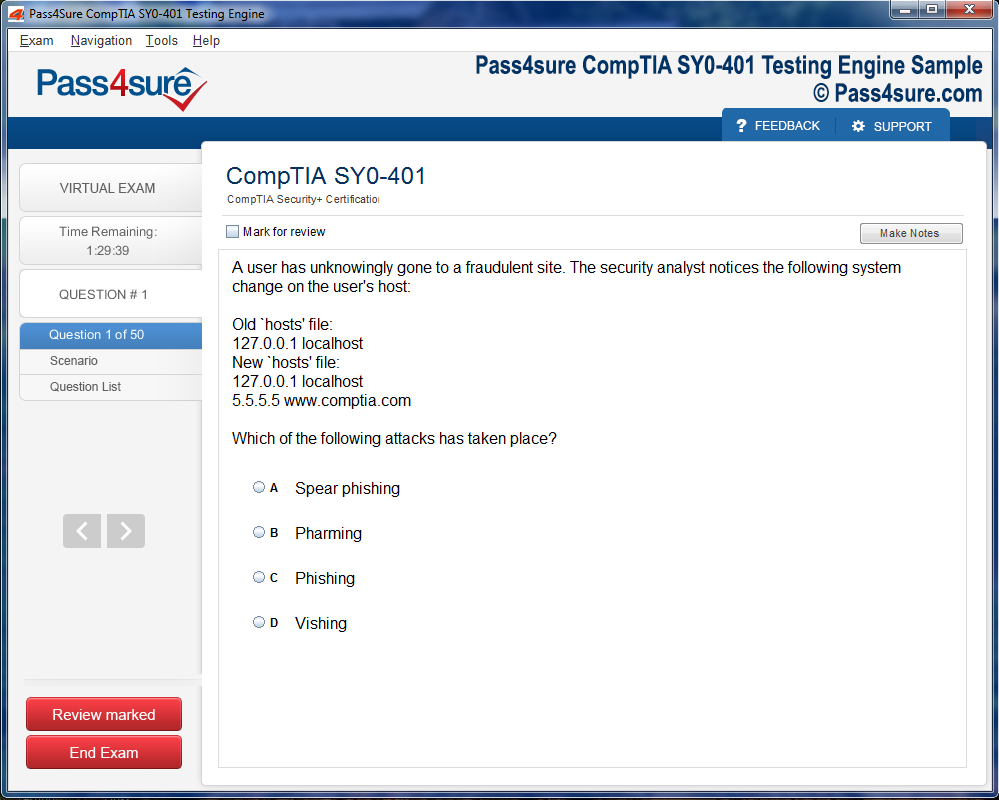
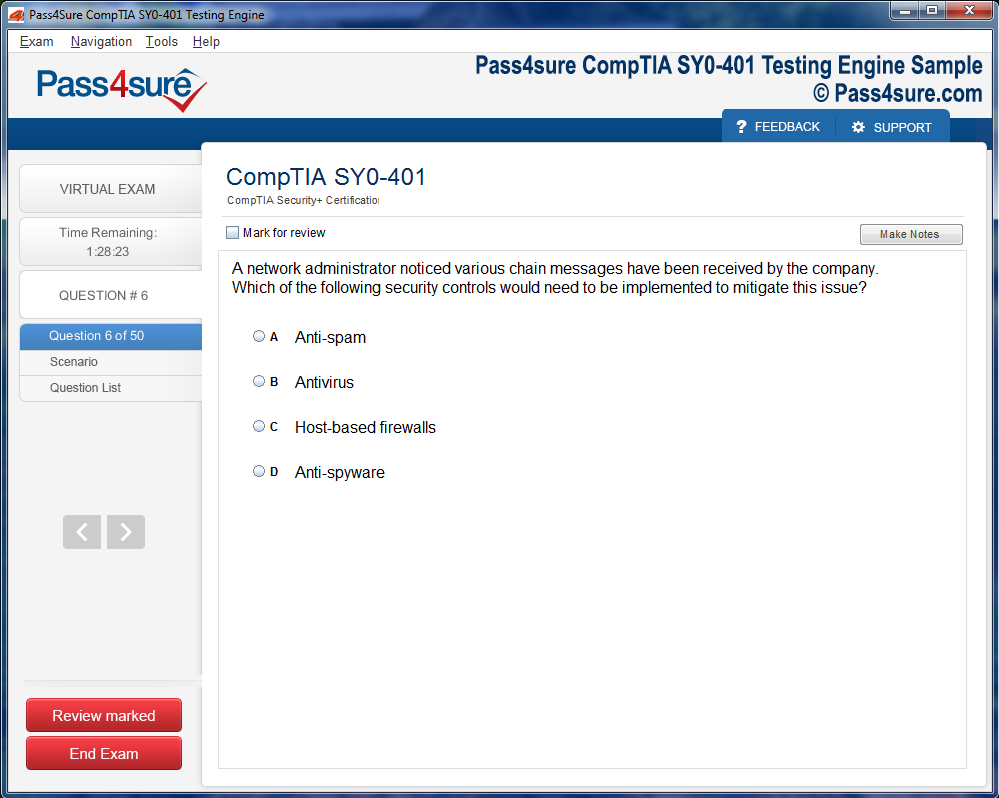
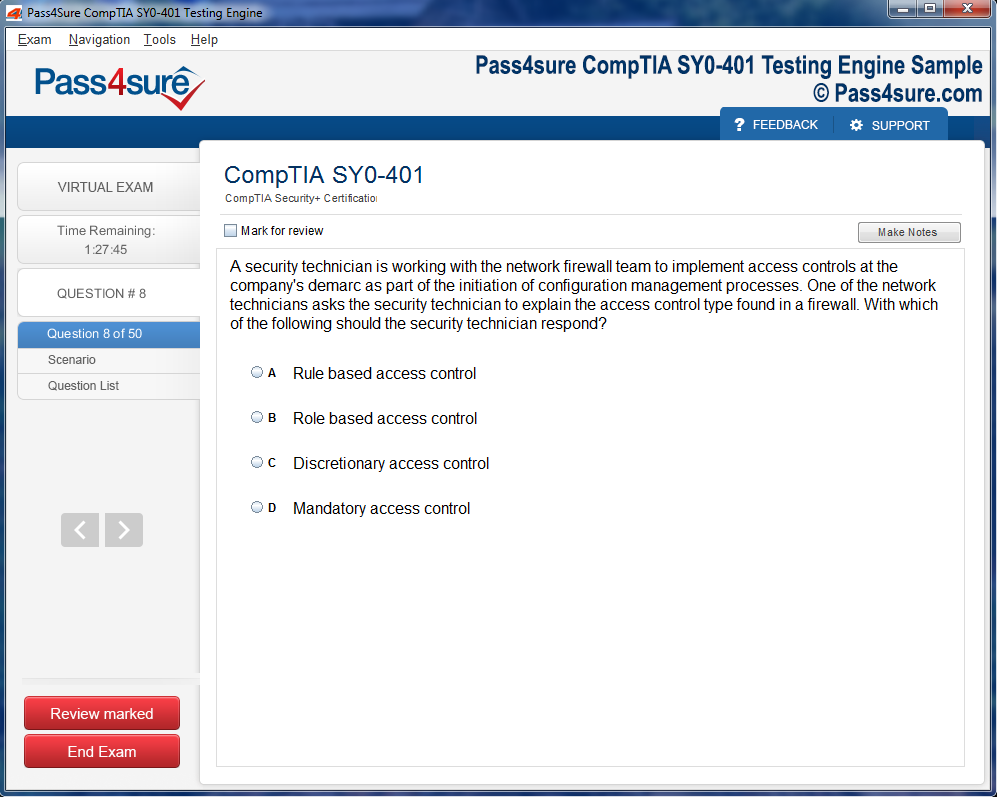
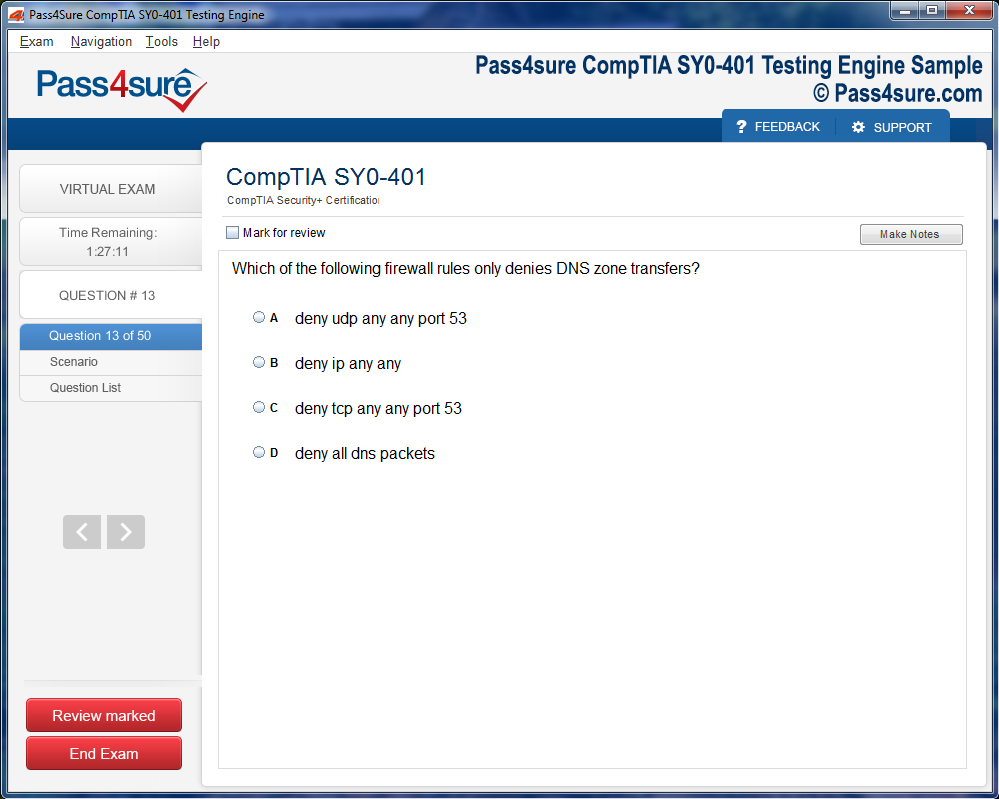
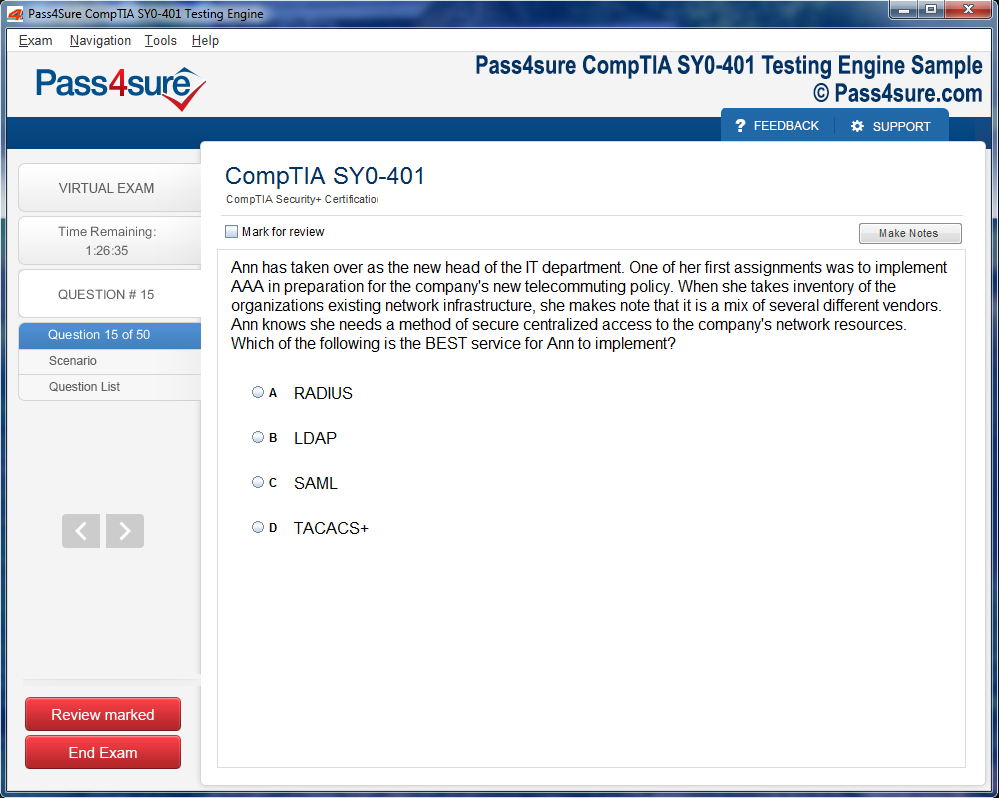
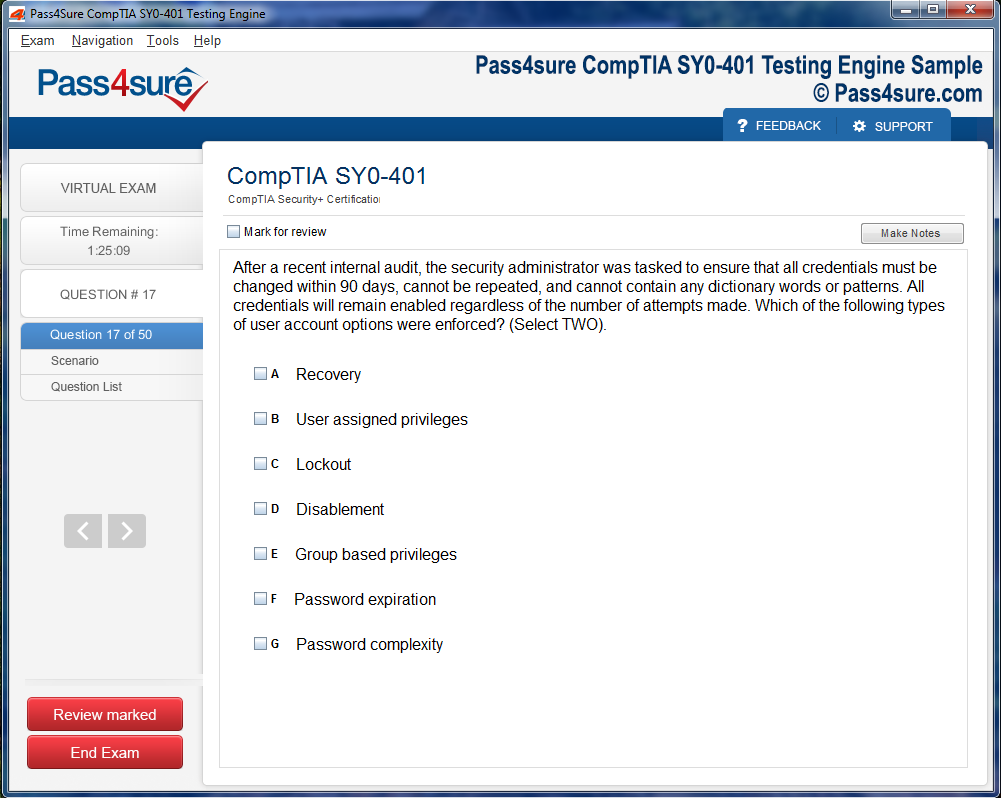
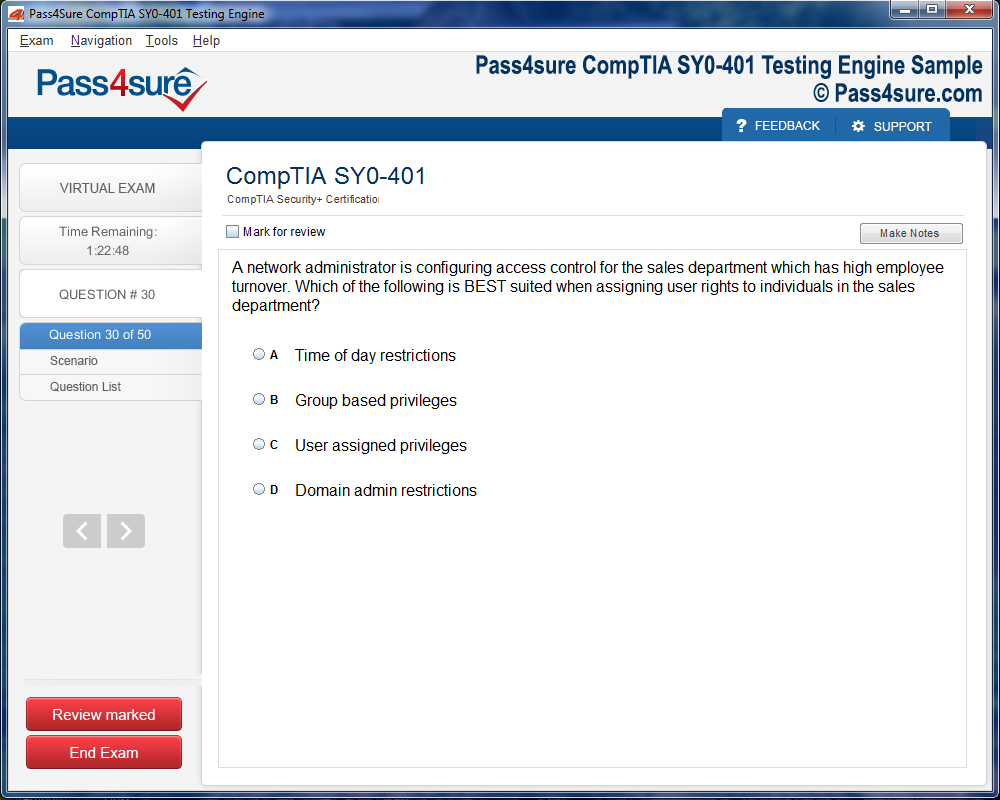
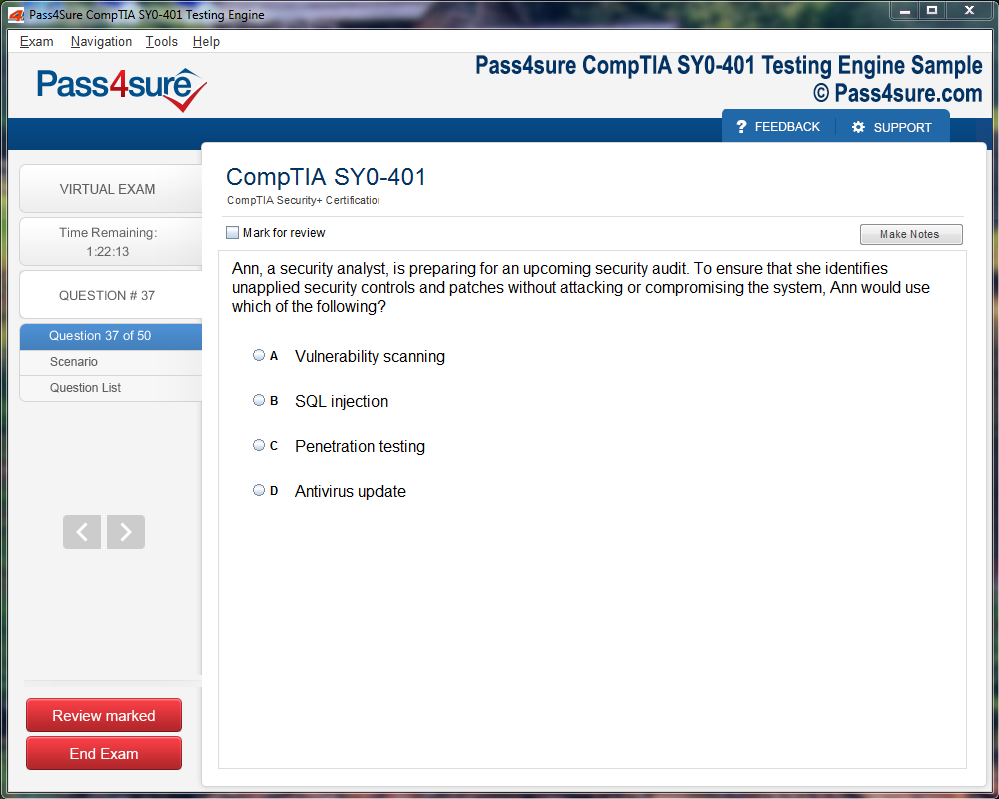
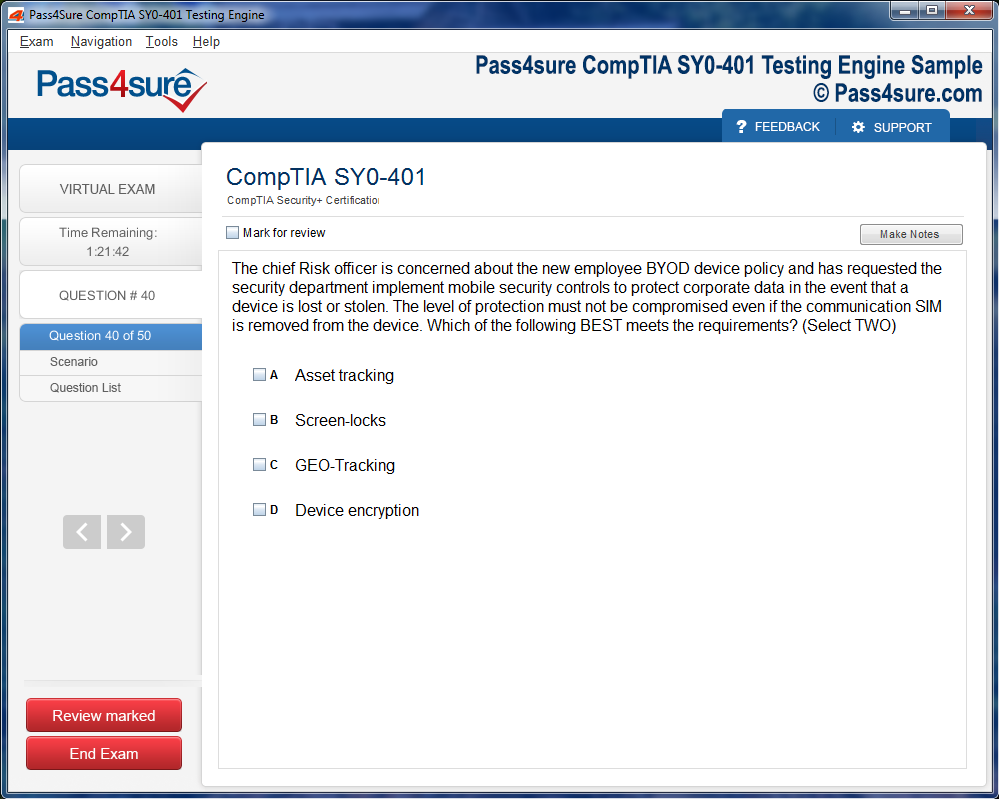
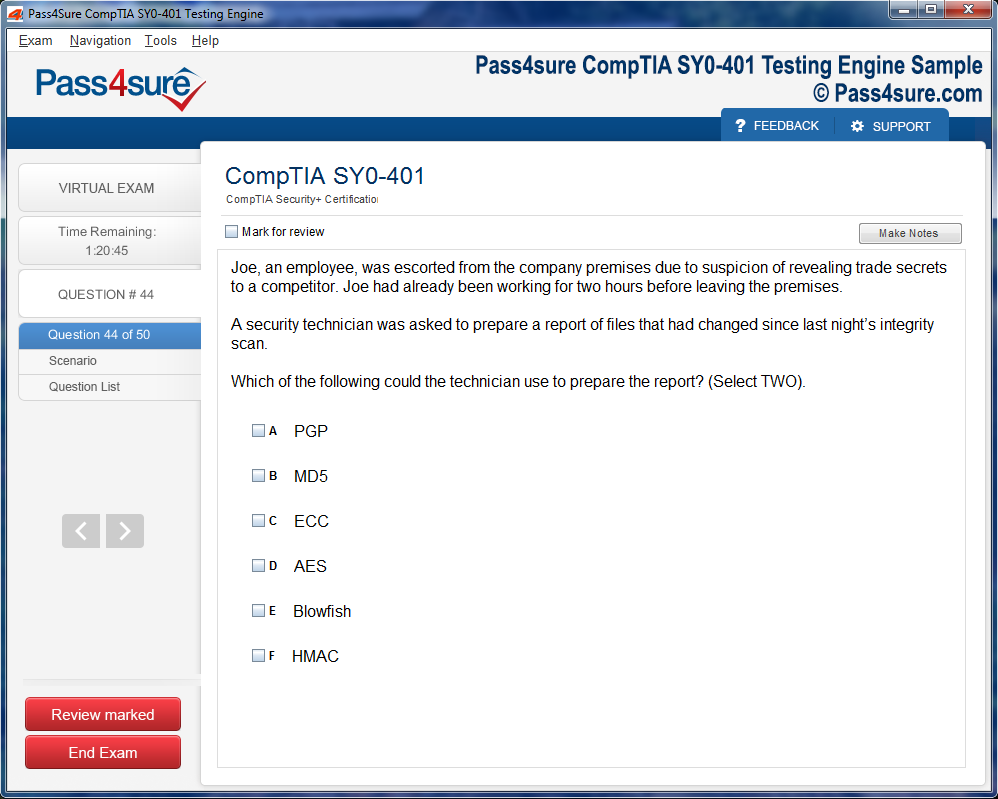
Product Screenshots
Frequently Asked Questions
How does your testing engine works?
Once download and installed on your PC, you can practise test questions, review your questions & answers using two different options 'practice exam' and 'virtual exam'. Virtual Exam - test yourself with exam questions with a time limit, as if you are taking exams in the Prometric or VUE testing centre. Practice exam - review exam questions one by one, see correct answers and explanations.
How can I get the products after purchase?
All products are available for download immediately from your Member's Area. Once you have made the payment, you will be transferred to Member's Area where you can login and download the products you have purchased to your computer.
How long can I use my product? Will it be valid forever?
Pass4sure products have a validity of 90 days from the date of purchase. This means that any updates to the products, including but not limited to new questions, or updates and changes by our editing team, will be automatically downloaded on to computer to make sure that you get latest exam prep materials during those 90 days.
Can I renew my product if when it's expired?
Yes, when the 90 days of your product validity are over, you have the option of renewing your expired products with a 30% discount. This can be done in your Member's Area.
Please note that you will not be able to use the product after it has expired if you don't renew it.
How often are the questions updated?
We always try to provide the latest pool of questions, Updates in the questions depend on the changes in actual pool of questions by different vendors. As soon as we know about the change in the exam question pool we try our best to update the products as fast as possible.
How many computers I can download Pass4sure software on?
You can download the Pass4sure products on the maximum number of 2 (two) computers or devices. If you need to use the software on more than two machines, you can purchase this option separately. Please email sales@pass4sure.com if you need to use more than 5 (five) computers.
What are the system requirements?
Minimum System Requirements:
- Windows XP or newer operating system
- Java Version 8 or newer
- 1+ GHz processor
- 1 GB Ram
- 50 MB available hard disk typically (products may vary)
What operating systems are supported by your Testing Engine software?
Our testing engine is supported by Windows. Andriod and IOS software is currently under development.
HPE6-A79 Exam Complete Study Guide for Aruba Certified Design Expert
The initial phase of preparation involves immersing oneself in the foundational elements of Aruba's mobility solutions. This includes a comprehensive understanding of the ArubaOS architecture, which serves as the backbone for various network functionalities. A solid grasp of this architecture is essential for designing scalable and resilient WLAN solutions.
Equally important is the proficiency in configuring and validating Aruba WLAN solutions. This encompasses tasks such as setting up SSIDs, implementing VLANs, and ensuring seamless client connectivity. Hands-on experience with Aruba's configuration tools and platforms is invaluable during this stage.
Furthermore, delving into the nuances of advanced services and security solutions is crucial. This includes understanding the implementation of features like AirMatch for RF optimization, AppRF for application visibility, and ClearPass for robust network security policies. Mastery of these services ensures the deployment of secure and efficient wireless networks.
A deep familiarity with the dynamic spectrum allocation mechanisms within Aruba's ecosystem also fortifies network stability. Recognizing how access points negotiate channel assignments and transmit power allows for the mitigation of co-channel interference, which is often a silent disruptor of wireless performance. In addition, appreciating the interplay between controller-managed and controller-less deployments enhances an engineer’s flexibility in creating adaptive network topologies.
Foundational knowledge also extends to the methodology of troubleshooting and validation. Utilizing diagnostic tools to examine signal strength, latency, and throughput provides insight into network behavior under varying loads. Practitioners learn to interpret logs, monitor client roaming patterns, and identify anomalous traffic patterns. These preparatory steps lay the groundwork for the advanced configuration stages, ensuring that networks are not only functional but resilient against fluctuations and environmental challenges.
Advanced WLAN Architecture Design
Designing advanced WLAN architectures requires a synthesis of empirical knowledge and strategic foresight. Network architects must anticipate capacity requirements, environmental constraints, and evolving user behaviors. Aruba mobility solutions empower designers to map out extensive topologies that accommodate diverse device ecosystems, from mobile endpoints to IoT devices, without compromising performance.
One of the pivotal aspects of architecture design is RF planning. Conducting comprehensive site surveys to measure signal attenuation, interference sources, and propagation characteristics is indispensable. Using predictive modeling, engineers can simulate RF coverage and identify potential dead zones or areas susceptible to congestion. This proactive approach enables the deployment of access points in positions that maximize signal uniformity and client density support.
Another layer of architectural sophistication involves the deployment of redundancy mechanisms. Aruba’s mesh networking and controller clustering capabilities ensure that single points of failure are minimized. Access points communicate intelligently to maintain connectivity even in the event of hardware disruptions. Such strategies not only enhance network uptime but also provide the scalability required in environments with fluctuating client populations.
Equally vital is the integration of network segmentation and traffic prioritization. Leveraging VLANs, quality of service policies, and application-specific routing allows the network to balance performance with security. By aligning network segments to organizational roles or device types, traffic congestion is reduced, and critical applications receive the bandwidth they necessitate. This holistic approach to architecture guarantees that both routine operations and peak-load scenarios are handled with precision and reliability.
Seamless Client Connectivity
Ensuring seamless client connectivity is central to the efficacy of any wireless network. Aruba mobility solutions focus on creating environments where devices transition effortlessly between access points without drops in performance. Client roaming strategies are underpinned by protocols that optimize handoff decisions based on signal strength, quality, and historical connectivity patterns.
Optimizing client experiences begins with understanding device diversity. Different endpoints exhibit varied RF characteristics and mobility behaviors. By monitoring these patterns, network administrators can fine-tune access point parameters to accommodate heterogeneous devices. This proactive adjustment reduces the likelihood of client disconnections and ensures uniform coverage across large campuses or multifaceted office spaces.
Dynamic bandwidth management further enhances connectivity. Through adaptive allocation algorithms, the network can respond to fluctuating usage patterns in real time. High-density areas, such as conference rooms or auditoriums, benefit from prioritized allocation, while low-density zones maintain sufficient resources for occasional traffic spikes. This fluid allocation is vital for sustaining performance in environments where user presence is unpredictable or mobile applications generate varying traffic loads.
Additionally, Aruba solutions emphasize the importance of visibility and analytics. Real-time dashboards provide insight into client distribution, application usage, and potential interference sources. By leveraging these analytics, administrators can anticipate connectivity issues before they impact users, facilitating preemptive adjustments and minimizing operational disruptions. This intelligent approach to client management transforms wireless networks from reactive systems into predictive, self-optimizing environments.
Optimizing RF Performance
Radio frequency performance is the lifeblood of any wireless network, and optimizing it requires a careful balance of technical understanding and empirical observation. Aruba mobility solutions offer advanced mechanisms to refine RF environments, ensuring consistent coverage and minimal interference.
AirMatch is a critical tool in this optimization process. By analyzing RF metrics and adjusting channel assignments and transmit power dynamically, the system mitigates co-channel interference while enhancing signal uniformity. This automated optimization reduces the need for manual adjustments and allows networks to adapt to environmental changes such as new obstructions or shifting user patterns.
Another aspect of RF optimization involves managing spectrum efficiency. Identifying overlapping channels, detecting rogue access points, and measuring noise floors enables administrators to create interference-resistant networks. Such vigilance ensures that critical applications receive stable and predictable bandwidth even in high-density deployments.
Furthermore, RF performance is closely tied to client experience. Adjusting parameters like minimum RSSI thresholds and load-balancing access points can prevent scenarios where devices cling to distant access points, resulting in slow throughput and packet loss. By understanding the nuanced relationship between client behavior and RF propagation, network operators can fine-tune deployments for both reliability and speed.
Continuous monitoring is also a key component of maintaining optimal RF performance. Alerts triggered by sudden signal degradation or interference spikes allow teams to respond promptly. This proactive approach transforms the network from a static infrastructure into a living ecosystem that adapts in real time to environmental fluctuations and evolving operational demands.
Integrating Security Measures
Security integration in Aruba mobility solutions extends beyond simple access control; it encompasses a multidimensional strategy that safeguards data, devices, and user interactions. ClearPass serves as the cornerstone of this security framework, offering policy-driven access control and authentication across both wired and wireless networks.
Implementing security begins with granular identity management. By defining policies based on user roles, device types, and application access, administrators can enforce rules that dynamically adjust to changing contexts. This adaptive security approach minimizes unauthorized access and ensures that sensitive data remains protected without impeding legitimate traffic.
Equally crucial is endpoint compliance monitoring. Ensuring that devices meet minimum security requirements before granting network access mitigates risks associated with malware, outdated software, or misconfigured systems. Aruba solutions integrate continuous monitoring that can automatically remediate non-compliant devices or quarantine them until appropriate measures are taken.
Network segmentation adds an additional layer of protection. By isolating critical resources, sensitive applications, and guest traffic, the risk of lateral movement in the event of a security breach is minimized. Coupled with encrypted communication and secure authentication protocols, this segmentation fortifies the network against internal and external threats.
Threat intelligence and analytics play a pivotal role in sustaining security efficacy. Real-time logs, anomaly detection, and behavior analysis provide actionable insights that guide network adjustments. By preemptively addressing potential vulnerabilities, administrators can maintain a resilient network posture, balancing security needs with the seamless connectivity and performance expected by users.
Application Visibility and Management
Application visibility is essential in modern network management, particularly as diverse workloads and cloud-based services proliferate. Aruba’s AppRF technology provides granular insight into traffic flows, enabling administrators to understand which applications consume bandwidth and how they affect overall performance.
Understanding application behavior allows networks to prioritize critical operations and maintain responsiveness even under heavy load. For example, voice and video traffic can be allocated higher priority to prevent latency, while less critical background processes are deferred. This strategic allocation ensures consistent user experiences across varied workloads.
Proactive monitoring of application usage patterns also informs capacity planning. By analyzing trends over time, administrators can anticipate spikes in demand, optimize resource allocation, and adjust infrastructure accordingly. This predictive approach reduces bottlenecks, enhances productivity, and prevents disruptions caused by unexpected traffic surges.
Application management extends beyond prioritization. It includes ensuring secure access, mitigating interference with other services, and dynamically adapting to network conditions. By integrating visibility tools with automated optimization mechanisms, Aruba solutions create an intelligent network environment where application performance is continuously monitored and enhanced without manual intervention.
Scaling and Future-Ready Deployments
Preparing networks for future growth is a central consideration in Aruba mobility solutions. Scalable designs accommodate evolving user demands, emerging device types, and technological advancements without requiring extensive overhauls. Anticipating expansion needs ensures continuity in performance and minimizes disruptions during scaling.
One element of future readiness involves modular deployment strategies. By designing networks with flexible access point placements, controller configurations, and cloud-managed services, organizations can incrementally expand capacity. This approach supports gradual growth while maintaining consistent performance and coverage.
Cloud integration enhances scalability by enabling centralized management and seamless updates. Administrators can deploy policy changes, firmware updates, and configuration adjustments across multiple sites simultaneously. This centralization reduces operational complexity and ensures uniformity in network behavior, even in geographically dispersed environments.
Emerging technologies, such as IoT devices and augmented reality applications, also influence scaling strategies. Aruba solutions are designed to handle high-density deployments, diverse protocols, and real-time data streams. By accounting for these future demands during the initial design phase, networks are positioned to accommodate innovation without compromising reliability or security.
Finally, continuous learning and analytics support future-ready deployments. Monitoring trends, evaluating network performance, and integrating predictive tools allow administrators to adapt proactively. This dynamic approach transforms the network into a resilient ecosystem capable of evolving alongside organizational needs, technological advances, and user expectations.
Understanding Advanced WLAN Topologies
Advanced WLAN topologies extend beyond conventional layouts, introducing dynamic interconnections that optimize traffic flow and minimize latency. Unlike simple networks, these designs consider hierarchical structuring, where core, distribution, and access layers collaborate seamlessly. Strategic placement of access points allows for uniform signal propagation while reducing dead zones and congestion points. In complex environments, obstacles like metallic structures, reflective surfaces, and variable occupancy patterns necessitate adaptive topology planning. Employing predictive models based on historical usage patterns enables network architects to anticipate congestion and adjust access point density accordingly. These topologies also leverage mesh configurations, which permit automatic rerouting of data packets when nodes experience failures or unexpected interference. Such adaptability is crucial in scenarios with high device mobility, such as campuses, airports, or industrial sites.
Implementing Layered Security Protocols
Layered security in WLAN design integrates multiple protective mechanisms that function harmoniously to safeguard network integrity. Rather than relying on a single security measure, these networks deploy a combination of encryption protocols, authentication methods, and anomaly detection systems. Advanced encryption standards ensure that data remains confidential during transit, while multifactor authentication validates user identity before granting access. Real-time monitoring tools continuously assess network behavior, detecting unusual traffic patterns or unauthorized devices attempting connections. Segmentation of the network into virtual zones adds another dimension of security, isolating critical systems from general user traffic. This approach not only mitigates the risk of breaches but also contains potential disruptions to a confined segment, preserving the overall functionality of the WLAN. Integrating intrusion prevention systems further strengthens the network, creating a robust environment capable of responding to sophisticated cyber threats.
Optimizing Wireless Spectrum Utilization
Efficient spectrum utilization is pivotal in high-density WLAN deployments, where multiple devices contend for limited radio frequencies. Optimizing spectrum allocation requires careful analysis of channel overlap, interference sources, and environmental factors. Modern WLANs employ dynamic frequency selection, allowing access points to automatically switch to channels with minimal congestion. Load balancing techniques distribute client connections evenly across available frequencies, preventing bottlenecks and maintaining consistent throughput. Environmental sensing tools measure signal attenuation caused by walls, furniture, and human movement, enabling precise calibration of transmission power levels. By harmonizing these parameters, networks achieve maximal data throughput while reducing the probability of packet collisions. Additionally, emerging technologies such as cognitive radios empower devices to adaptively choose spectrum segments based on real-time conditions, further enhancing efficiency and reliability in crowded wireless environments.
Integrating Cloud-Managed Solutions
Cloud-managed WLANs introduce a paradigm shift by centralizing network control through remote platforms. These solutions offer unprecedented visibility into device activity, application performance, and traffic patterns. Centralized dashboards enable network administrators to monitor multiple sites simultaneously, apply firmware updates seamlessly, and enforce consistent security policies across the entire infrastructure. Cloud orchestration also facilitates rapid deployment of new access points, reducing operational overhead and expediting scalability. Analytical tools embedded in cloud platforms provide actionable insights, revealing usage trends, peak demand periods, and potential vulnerabilities. By leveraging automation, networks can self-optimize, adjusting configurations dynamically to meet changing conditions. This integration of cloud intelligence enhances operational efficiency, ensures consistent user experiences, and supports complex architectures with minimal manual intervention.
Implementing High-Availability Mechanisms
High availability in WLAN environments ensures uninterrupted connectivity, even in the event of equipment failures or maintenance activities. Achieving this requires strategic redundancy at multiple levels, including hardware, software, and network paths. Dual controllers, backup access points, and failover links create a resilient infrastructure capable of sustaining operations during adverse conditions. Load balancing between redundant paths prevents overutilization of a single node, minimizing latency and packet loss. Periodic testing of failover mechanisms ensures that they function as intended, providing confidence in the network’s reliability. Advanced monitoring systems detect anomalies before they escalate, triggering automated responses that preserve service continuity. By embedding these high-availability principles into WLAN design, organizations can maintain critical operations, support mission-critical applications, and deliver uninterrupted experiences to end-users in dynamic environments.
Leveraging Advanced Analytics for Performance Tuning
Performance tuning in complex WLANs relies heavily on advanced analytics, which transform raw data into actionable intelligence. Network devices generate extensive logs and metrics, encompassing client behavior, throughput statistics, and interference levels. Analytical platforms aggregate this information, identifying patterns, bottlenecks, and inefficiencies. Predictive algorithms forecast potential issues, enabling proactive adjustments to access point placement, channel allocation, and power levels. Continuous feedback loops refine configurations, adapting to evolving usage patterns and environmental changes. Insights derived from analytics not only enhance throughput and stability but also improve user satisfaction by minimizing latency, packet loss, and connectivity disruptions. Incorporating machine learning techniques allows WLANs to learn from historical trends, making real-time adjustments that optimize performance autonomously. This data-driven approach ensures that complex architectures maintain peak operational efficiency under fluctuating demands.
Coordinating Multi-Site Network Environments
Designing WLANs across multiple locations introduces additional complexity, requiring consistent performance, unified policies, and synchronized monitoring. Centralized management systems provide oversight, enabling administrators to enforce uniform configurations and security measures across geographically dispersed sites. Inter-site traffic routing, bandwidth allocation, and access point calibration must be harmonized to prevent disparities in user experience. Automated tools facilitate configuration replication, ensuring that new installations adhere to established standards without manual intervention. Real-time monitoring across sites identifies localized issues while maintaining a global view of network health. Integrating reporting mechanisms allows stakeholders to track performance metrics, verify compliance with operational standards, and plan upgrades or expansions strategically. Multi-site coordination transforms scattered deployments into cohesive networks, offering seamless connectivity, predictable performance, and simplified administration for expansive organizational footprints.
Advanced Troubleshooting Techniques
Troubleshooting in modern WLAN environments has evolved into a sophisticated art that blends analytical rigor with practical intuition. Mobility experts face networks that are increasingly dynamic, encompassing diverse devices, varied protocols, and intricate security architectures. The ability to dissect connectivity issues and restore seamless performance requires more than basic knowledge; it demands a meticulous approach that unites technological awareness with methodical problem-solving. A successful practitioner must understand both the visible and subtle elements influencing network behavior, ranging from signal propagation anomalies to unexpected protocol interactions.
Effective troubleshooting begins with a disciplined framework. Defining the problem precisely is essential, as vague observations can lead to misdiagnosis and prolonged downtime. Once the issue is articulated, systematic data collection becomes paramount. Diagnostic tools such as performance dashboards, real-time analytics, and client logs offer a window into the network's operational state, revealing patterns invisible to casual observation. Experts often employ a combination of historical trend analysis and instantaneous metrics to isolate root causes, ensuring that the interventions are targeted and impactful rather than superficial.
Understanding the nuances of wireless protocols is integral to high-level troubleshooting. Standards such as 802.11ac and 802.11ax introduce sophisticated mechanisms for channel bonding, beamforming, and interference management. Each feature interacts with others in subtle ways, creating scenarios where a minor configuration mismatch can manifest as degraded performance or intermittent connectivity. Similarly, authentication frameworks like RADIUS and EAP-TLS bring their own complexities, where certificate mismanagement or server misconfiguration can halt access for entire classes of devices. Mastery of these protocols equips mobility professionals to navigate such intricacies with confidence, ensuring that diagnostic efforts are both accurate and comprehensive.
Systematic problem-solving extends beyond identifying the technical cause of a fault. Effective practitioners recognize that the operational context—the broader ecosystem in which the network functions—plays a critical role. For instance, the introduction of new client devices or software updates can trigger latent issues that were previously dormant. By maintaining situational awareness and incorporating proactive monitoring, experts can anticipate potential disruptions before they escalate into significant service degradation. This anticipatory approach distinguishes high-performing network teams from those that merely respond to crises.
Leveraging diagnostic platforms is a cornerstone of sophisticated troubleshooting. Tools designed for centralized management provide not only visibility but also predictive insights that can highlight anomalies before they affect end users. Real-time analytics illuminate traffic flows, signal strengths, and device associations, offering a granular perspective that manual observation cannot match. By interpreting these metrics correctly, mobility specialists can formulate interventions that are precise and minimally disruptive, preserving both performance and user experience. Over time, continuous interaction with these platforms refines intuition and enhances pattern recognition, turning raw data into actionable intelligence.
Troubleshooting in a high-density WLAN scenario introduces additional layers of complexity. As the number of devices and access points multiplies, the potential for interference, channel overlap, and resource contention grows exponentially. Understanding the physics of radio frequency propagation becomes critical, as does the ability to model and predict network behavior under variable load conditions. Techniques such as spectrum analysis and channel planning are employed to mitigate interference, while adaptive mechanisms like dynamic channel selection ensure optimal utilization of available resources. Each intervention must be carefully calibrated, taking into account both immediate performance and long-term network resilience.
Network Performance Optimization
Beyond reactive troubleshooting, mobility experts focus on proactive performance optimization. Network optimization encompasses tuning configurations, balancing load, and anticipating demand patterns to maintain consistent service levels. This process requires a keen understanding of the interplay between access points, client devices, and the applications that consume network resources. Subtle misalignments—such as improper quality of service prioritization or inadequate RF coverage—can cascade into noticeable slowdowns or connectivity interruptions. By addressing these issues preemptively, network teams maintain operational fluidity and reduce the incidence of critical failures.
Traffic analysis forms the backbone of performance optimization. By segmenting data streams, identifying high-consumption endpoints, and monitoring latency fluctuations, specialists gain insights into how the network is utilized. These observations inform strategies for bandwidth allocation, prioritization of critical applications, and adjustments to access point placement. In essence, optimization is a continuous feedback loop where observational data drives configuration refinements, and subsequent results are used to further improve performance. The iterative nature of this process ensures that the network adapts to evolving demands and remains resilient under varied load conditions.
Another crucial aspect of performance enhancement is the calibration of radio frequency environments. High-density deployments, common in enterprise or public spaces, require careful attention to channel overlap, power levels, and antenna orientation. Even minor deviations in RF configuration can amplify interference, leading to reduced throughput and increased packet loss. Mobility experts employ both software-driven tools and empirical measurements to optimize coverage, often combining predictive modeling with real-world verification. The goal is to maintain seamless connectivity across diverse physical spaces while minimizing the potential for signal degradation or dead zones.
Quality of Service (QoS) mechanisms play a pivotal role in network optimization. By categorizing traffic and assigning priority levels, networks can ensure that latency-sensitive applications, such as voice or video, receive preferential treatment. Configuring QoS requires a detailed understanding of application behavior, traffic patterns, and potential bottlenecks. Misconfigured settings can inadvertently throttle critical communications or allow lower-priority traffic to dominate, reducing the overall effectiveness of the network. Effective practitioners not only implement QoS but continually monitor its impact, adjusting thresholds and policies to maintain equilibrium between performance and resource utilization.
Load balancing across multiple access points is another technique to optimize performance. Intelligent assignment of clients to the most appropriate AP prevents congestion and maximizes the use of available bandwidth. This requires real-time awareness of network conditions, device capabilities, and application demands. Sophisticated algorithms, combined with manual oversight, enable mobility teams to distribute traffic efficiently, preventing hotspots and maintaining a uniform quality of service across the network. Such strategies exemplify the blend of technical precision and strategic planning necessary for high-functioning wireless environments.
Security Troubleshooting and Hardening
Security is a fundamental concern in wireless networks, and troubleshooting security-related issues requires both vigilance and expertise. Unauthorized access, rogue devices, and configuration vulnerabilities can compromise the integrity of the entire WLAN infrastructure. Mobility professionals must possess the ability to diagnose security anomalies swiftly, distinguishing between benign operational irregularities and genuine threats. Understanding encryption protocols, authentication mechanisms, and access control policies is essential to mitigate risks without impeding legitimate network usage.
Analyzing authentication failures is a frequent task in security troubleshooting. Misconfigurations in RADIUS servers, certificate errors, or policy mismatches can prevent clients from connecting, creating disruptions that appear as performance issues. By carefully reviewing logs, testing configurations, and validating certificate chains, experts can pinpoint the source of failures and restore secure connectivity. Additionally, maintaining documentation of access policies and configuration baselines facilitates faster resolution of recurring issues and ensures consistent enforcement of security standards.
Wireless intrusion detection and prevention systems serve as critical tools in security monitoring. These systems alert administrators to abnormal behavior, such as unusual association attempts or rogue APs broadcasting within the environment. Troubleshooting alerts requires careful analysis to differentiate between false positives and genuine security incidents. By correlating data across multiple sources—AP logs, client activity, and traffic patterns—mobility teams can make informed decisions that protect the network without unnecessarily restricting legitimate users.
Security hardening complements reactive troubleshooting. By implementing robust encryption, segmenting networks, and enforcing strong authentication policies, organizations reduce the likelihood of security breaches. Mobility specialists work proactively to anticipate vulnerabilities, often simulating attacks or stress-testing the network to uncover potential weaknesses. This proactive stance not only improves overall resilience but also streamlines troubleshooting by minimizing the occurrence of security-related disruptions.
Incident response in wireless environments demands a structured methodology. Once a security anomaly is detected, immediate containment measures, evidence collection, and root cause analysis are essential. Experts employ both technical and procedural interventions to resolve issues while preserving operational continuity. Continuous refinement of incident response procedures ensures that teams remain agile and effective, capable of addressing emerging threats with minimal disruption to service and user experience.
Client Behavior Analysis
Understanding client behavior is a nuanced yet vital aspect of WLAN management. Network issues often manifest in ways that are closely tied to the interactions between devices and access points. Variations in client hardware, operating systems, and application usage create a heterogeneous landscape that can influence performance, connectivity, and security. By studying these behaviors, mobility specialists gain insights into the root causes of issues and can tailor solutions accordingly.
Roaming patterns, for example, significantly affect network stability. As clients move between access points, handoff delays or mismanaged roaming thresholds can produce connectivity interruptions. Analyzing these patterns requires a combination of real-time monitoring and historical data interpretation. Mobility experts adjust parameters such as roaming aggressiveness, signal thresholds, and load balancing strategies to smooth transitions and maintain consistent connectivity, thereby improving the end-user experience.
Client resource consumption also informs troubleshooting and optimization efforts. High-demand applications or background processes can create congestion that manifests as reduced throughput or increased latency. By monitoring these consumption patterns, specialists can implement traffic shaping, prioritize critical applications, or even guide users toward best practices that optimize overall network performance. This insight-driven approach ensures that interventions are precisely aligned with observed client behavior rather than speculative assumptions.
Additionally, compatibility challenges arise as diverse device ecosystems evolve. Older devices may struggle with advanced protocols or security configurations, while newer devices may exploit features that reveal misconfigurations or limitations. By cataloging and analyzing device-specific performance trends, mobility professionals can implement targeted strategies that harmonize network behavior across heterogeneous client populations. This meticulous attention to detail reinforces reliability and minimizes the potential for widespread disruptions.
Systematic Diagnostic Methodologies
A structured diagnostic methodology forms the backbone of advanced troubleshooting. Without a repeatable process, even experienced professionals risk overlooking critical variables or misinterpreting symptoms. The methodology typically involves defining the problem, gathering comprehensive data, performing a detailed analysis, implementing corrective actions, and verifying outcomes. Each step is iterative, feeding insights back into the process to refine both understanding and response.
Data collection encompasses both quantitative metrics and qualitative observations. Real-time performance dashboards, event logs, and spectrum analyses provide measurable indicators of network health. Meanwhile, careful observation of client behavior and environmental factors supplies contextual information that may not appear in numerical reports. By combining these sources, specialists achieve a holistic view of the network, ensuring that interventions address root causes rather than surface manifestations.
Analysis is a critical phase where expertise and experience converge. Correlating disparate data points, identifying anomalies, and testing hypotheses require both technical knowledge and intuitive judgment. Specialists must recognize patterns that may be subtle, such as intermittent interference or sporadic authentication failures, and distinguish them from coincidental fluctuations. This analytical rigor reduces the likelihood of misdiagnosis and ensures that corrective actions are both efficient and effective.
Implementation of solutions demands precision and foresight. Interventions are designed to target identified issues while minimizing disruption to users and operational processes. Once changes are applied, verification processes confirm that the problem is resolved and that no unintended consequences have emerged. This cyclical methodology creates a resilient framework where troubleshooting is not only corrective but also continuously adaptive, enabling networks to maintain high performance even as conditions evolve.
Understanding Network Security Fundamentals
Network security forms the bedrock of any digital infrastructure, acting as a vigilant sentinel against unauthorized access and data breaches. Every organization, regardless of scale, must recognize the intricate dance between accessibility and protection. In the contemporary landscape, networks are no longer isolated; they extend across hybrid cloud architectures, wireless systems, and remote endpoints. This interconnectedness, while enhancing operational agility, exponentially increases susceptibility to cyber threats.
At its core, network security is an intricate amalgamation of protocols, policies, and technologies designed to safeguard digital assets. Firewalls, encryption methods, and secure authentication mechanisms constitute fundamental layers of defense. These components collectively deter malicious actors, ensuring that sensitive information, such as intellectual property or customer data, remains shielded from intrusion. Moreover, security is not static; it evolves continuously to counter sophisticated attack vectors. The advent of ransomware, phishing, and zero-day exploits underscores the necessity for adaptive security frameworks that are responsive to dynamic threats.
Within this framework, visibility into network traffic is indispensable. Administrators must possess the capability to monitor data flows, detect anomalies, and enforce compliance with security policies. Tools that facilitate deep packet inspection, behavioral analytics, and real-time alerts enhance the capacity to preemptively address risks. This proactive posture transforms security from a reactive obligation into a strategic asset, fostering resilience in digital ecosystems.
Implementing Policy Management Solutions
Policy management serves as the strategic compass guiding network security operations. By establishing predefined rules and protocols, organizations can dictate who gains access to which resources and under what conditions. The sophistication of modern policy management platforms allows administrators to orchestrate comprehensive access control across diverse environments, including wired, wireless, and virtual networks.
Centralized policy managers simplify administration by consolidating authentication, authorization, and accounting processes. This consolidation not only streamlines operational workflows but also mitigates human error, a leading cause of security lapses. Through centralized oversight, administrators can implement granular access policies, ensuring that each user or device is granted permissions aligned with their role or purpose. This mitigates the risk of privilege escalation, where a compromised account could inadvertently gain excessive access.
The dynamic nature of policy management extends beyond static rules. Advanced systems incorporate contextual intelligence, evaluating factors such as device type, geolocation, time of access, and behavioral patterns. Such contextual analysis enables adaptive policy enforcement, dynamically adjusting permissions to maintain optimal security postures without impeding legitimate operational activity. Consequently, organizations can achieve a delicate equilibrium between robust security and seamless user experience.
Role-Based Access Control and Dynamic Assignments
Role-based access control, commonly referred to as RBAC, represents a cornerstone of modern security frameworks. Rather than granting blanket access to all resources, RBAC assigns permissions based on predefined roles, aligning access rights with operational responsibilities. This targeted approach not only enhances security but also simplifies compliance reporting, as access patterns are directly traceable to organizational roles.
Dynamic assignments further augment security by allowing networks to respond in real-time to evolving conditions. For instance, when a device connects to the network, policies can automatically assign it to a specific VLAN or access group based on authentication results. This ensures that each endpoint operates within appropriate security boundaries, reducing the likelihood of lateral movement by potential intruders.
In environments where multiple devices, users, and locations intersect, the fusion of RBAC and dynamic assignments becomes indispensable. It offers a scalable solution that adapts to organizational growth, remote work scenarios, and the proliferation of IoT devices. Each network entity is precisely categorized, monitored, and controlled, which translates into both operational efficiency and enhanced security resilience.
Integrating Intrusion Detection and Prevention Systems
Intrusion detection systems (IDS) and intrusion prevention systems (IPS) are critical components in the defensive arsenal of any network. IDS focuses on monitoring network traffic for suspicious patterns, generating alerts when anomalies are detected. In contrast, IPS actively intervenes to neutralize threats, blocking malicious traffic before it can compromise network resources.
The integration of IDS and IPS into the network fabric transforms passive security into a proactive mechanism. It enables organizations to detect early warning signs of cyberattacks, such as unusual login attempts, abnormal traffic spikes, or irregular access patterns. These systems employ sophisticated algorithms, often incorporating machine learning, to distinguish between legitimate anomalies and genuine threats.
Regular tuning and updates of IDS/IPS signatures are crucial to maintain efficacy. Threat landscapes evolve rapidly, and outdated detection mechanisms can fail to identify emerging exploits. By coupling automated threat intelligence with continuous monitoring, organizations can cultivate a resilient defense posture, ensuring that networks remain fortified against both known and unknown adversaries.
Fortifying Networks with Firewall Policies
Firewalls are among the most recognizable pillars of network security, serving as the gatekeepers between internal systems and external networks. By filtering traffic based on predefined rules, firewalls prevent unauthorized access while permitting legitimate communication. Contemporary firewall architectures extend beyond simple packet filtering, incorporating deep inspection capabilities, application-layer controls, and threat intelligence integration.
Configuring robust firewall policies requires a nuanced understanding of network architecture and operational requirements. Policies must be tailored to permit essential services while minimizing exposure to external threats. Overly permissive rules create vulnerabilities, whereas excessively restrictive configurations can impede productivity. Striking the right balance is a nuanced task that demands careful planning and continuous review.
Additionally, next-generation firewalls (NGFW) offer granular visibility into application behavior, user identity, and network interactions. By leveraging NGFW capabilities, organizations can enforce fine-tuned policies that dynamically adjust to evolving threats. This ensures that firewalls remain a living component of the security ecosystem, capable of adapting to new attack vectors while maintaining uninterrupted network functionality.
Securing Guest Access and Remote Connectivity
In modern network environments, accommodating guests and remote users is an operational necessity. However, uncontrolled access can expose networks to significant risk. Secure guest access frameworks allow temporary users to connect without compromising the integrity of core systems. These frameworks typically employ segregated networks, limited permissions, and authentication portals to maintain security boundaries.
Remote connectivity, driven by cloud services and mobile workforces, introduces additional complexity. Secure access solutions, such as virtual private networks (VPNs) or zero-trust architectures, ensure that remote endpoints adhere to organizational security policies. Endpoint verification, encryption, and continuous monitoring are key measures that safeguard remote connections, preventing potential exploitation of network vulnerabilities.
By implementing layered approaches to guest and remote access, organizations can accommodate flexibility without undermining security. These measures cultivate trust, both within the organization and with external collaborators, while reinforcing the principle that security is an integral, non-negotiable aspect of network design.
Continuous Auditing and Policy Refinement
Security and policy frameworks are not static constructs; they require perpetual evaluation and refinement. Continuous auditing identifies gaps, misconfigurations, and deviations from established policies. By routinely assessing network activity, organizations gain insights into emerging vulnerabilities, user behavior, and potential operational inefficiencies.
Policy refinement is an iterative process that responds to audit findings, technological evolution, and regulatory requirements. Adjustments may involve revising access privileges, updating firewall rules, or integrating new security technologies. This dynamic approach ensures that the network maintains resilience in the face of evolving threats and operational demands.
Furthermore, fostering a culture of security awareness among users enhances the effectiveness of technical measures. Training, policy communication, and behavioral reinforcement ensure that personnel act as proactive participants in safeguarding digital assets. When technical frameworks and human vigilance converge, networks achieve a level of protection that is both comprehensive and adaptive.
Understanding the Dynamics of Aruba Network Management
Managing an Aruba network requires more than just basic oversight. It involves a deep comprehension of the interactions between devices, applications, and users. Network administrators must engage in continuous observation to understand patterns, pinpoint anomalies, and optimize connectivity. The intricate web of Aruba components, from access points to controllers, demands meticulous attention to ensure that every element functions harmoniously. This level of management is essential for preventing disruptions, minimizing downtime, and enhancing user experiences. Recognizing the subtle signs of network strain and addressing them early can transform a potentially chaotic environment into a streamlined, efficient digital ecosystem.
Effective network management begins with identifying critical nodes and understanding their role within the infrastructure. Each access point, switch, and controller contributes to the overall performance, and their interdependencies can affect connectivity and speed. By mapping these connections, administrators can anticipate potential points of failure and reinforce them with strategic measures. The proactive approach extends beyond mere observation; it involves establishing a culture of vigilance where every fluctuation, however minor, is recorded, analyzed, and acted upon. This foresight not only reduces operational disruptions but also fosters a resilient network capable of adapting to evolving demands.
Leveraging AirWave for Insightful Analytics
Aruba’s AirWave Network Management platform serves as a central nervous system for monitoring network activities. It provides a panoramic view of network performance, offering granular insights into device behavior, traffic flow, and client interactions. The platform’s ability to visualize complex data allows administrators to detect anomalies that might otherwise remain hidden. Through detailed analytics, one can identify patterns of congestion, recurring faults, and user behavior trends that inform strategic decisions. This intelligence empowers network managers to implement targeted solutions, optimize bandwidth allocation, and enhance overall network efficiency.
AirWave’s analytical capabilities extend beyond static reporting. The platform facilitates predictive analysis by correlating historical data with current performance metrics. This predictive insight enables administrators to anticipate bottlenecks, plan capacity expansion, and deploy preventive measures before problems escalate. Moreover, AirWave’s visualization tools allow for the creation of intuitive dashboards that translate complex technical information into actionable insights. By combining real-time monitoring with historical trends, network managers can achieve a level of oversight that ensures the network remains robust, agile, and responsive to user needs.
Automating Alerts and Response Mechanisms
A critical aspect of managing Aruba networks is the ability to respond swiftly to emerging issues. Automated alerts play a pivotal role in this process, notifying administrators of irregularities in device performance, connectivity disruptions, or unusual traffic spikes. These alerts enable immediate action, preventing minor issues from escalating into significant outages. When combined with automated response mechanisms, such as system adjustments or remedial scripts, network management becomes more efficient, reducing manual intervention while maintaining high reliability.
Automated reporting complements alert systems by providing comprehensive documentation of network activities. These reports serve multiple purposes, including compliance monitoring, performance evaluation, and historical analysis. By reviewing these records, administrators can identify recurring issues, refine operational procedures, and enhance preventive strategies. The synergy of alerts and reporting creates a dynamic monitoring environment, where every event is captured, analyzed, and addressed with minimal delay. This framework ensures that Aruba networks operate seamlessly, with minimal disruption to users and applications.
Establishing Standardized Maintenance Protocols
Standardized maintenance procedures are essential for sustaining the health of Aruba networks. Regular updates, firmware upgrades, and configuration backups form the backbone of a reliable maintenance strategy. By adhering to these practices, administrators ensure that the network remains secure, resilient, and capable of accommodating evolving requirements. Consistency in maintenance routines also reduces the likelihood of human error, enhances operational predictability, and strengthens overall network integrity.
Routine maintenance begins with scheduling periodic inspections of all network components. Access points, switches, and controllers must be checked for firmware updates, security patches, and operational anomalies. Configuration backups should be created and stored securely, providing a safety net in case of system failures or misconfigurations. In addition, documentation of maintenance activities supports accountability and facilitates knowledge transfer within IT teams. The establishment of clear protocols transforms maintenance from a reactive chore into a proactive discipline that safeguards the longevity and performance of Aruba networks.
Optimizing Network Performance Through Continuous Monitoring
Continuous monitoring is the linchpin of optimal network performance. By tracking device health, traffic flows, and application behavior in real time, administrators can quickly identify and rectify issues that may degrade user experiences. Monitoring tools provide insights into network utilization, allowing for strategic load balancing, bandwidth allocation, and performance tuning. This dynamic oversight ensures that the network adapts to changing demands without compromising reliability or speed.
The act of monitoring is not limited to detecting faults; it also involves measuring the effectiveness of interventions. When changes are implemented, such as firmware updates or configuration adjustments, continuous observation validates their impact on overall performance. Trends in network traffic, client connectivity, and application responsiveness can be analyzed to fine-tune settings, optimize resource usage, and enhance user satisfaction. This iterative process creates a feedback loop, where monitoring informs action, action influences performance, and performance guides future decisions. Such vigilance ensures that Aruba networks operate at peak efficiency at all times.
Harnessing Proactive Problem Detection
Proactive problem detection is a cornerstone of effective Aruba network management. By leveraging predictive analytics, anomaly detection, and trend analysis, administrators can identify potential issues before they manifest as critical failures. This foresight minimizes downtime, reduces operational disruptions, and enhances the reliability of network services. Early detection also allows for strategic allocation of resources, ensuring that potential bottlenecks or vulnerabilities are addressed efficiently.
An essential aspect of proactive detection is understanding the patterns of network behavior under normal conditions. By establishing baseline metrics for traffic flow, device performance, and application responsiveness, deviations can be identified with precision. Alerts triggered by these deviations allow administrators to investigate and remediate issues before they impact users. This anticipatory approach transforms network management from a reactive endeavor into a preemptive strategy, fostering a robust and resilient infrastructure that can support complex, high-demand environments.
Strengthening Security and Resilience
Security and resilience are integral components of effective network management. Aruba networks, like all enterprise infrastructures, face ongoing threats that can compromise performance and integrity. By integrating continuous monitoring, automated alerts, and standardized maintenance, administrators create a resilient framework capable of withstanding cyber threats, hardware failures, and operational anomalies. Network security is reinforced through consistent firmware updates, configuration audits, and vigilant observation of traffic patterns, ensuring that vulnerabilities are addressed promptly.
Resilience extends beyond security to encompass redundancy, failover mechanisms, and system reliability. Access points and controllers must be configured to support seamless continuity in case of hardware or software failures. Backup configurations, disaster recovery plans, and regular testing of contingency procedures enhance the network’s ability to maintain uninterrupted service. The combination of proactive monitoring, standardized maintenance, and security vigilance creates a robust, adaptive network infrastructure that supports consistent performance, safeguards sensitive data, and mitigates the risk of operational disruptions.
Understanding the Foundations of Aruba Networks
Mastering the HPE6-A79 exam begins with a thorough comprehension of Aruba Networks’ foundational technologies. The Aruba ecosystem encompasses a wide spectrum of networking solutions designed to optimize connectivity, security, and management. Familiarity with ArubaOS, Aruba switches, and ClearPass solutions forms the bedrock of preparation. These systems are engineered to simplify complex network environments while maintaining robust operational capabilities.
A deep understanding of the core components, including wireless controllers, access points, and security policies, provides essential context for more advanced configurations. Aruba’s architecture emphasizes adaptability and scalability, allowing organizations to respond efficiently to changing network demands. Recognizing these principles helps in contextualizing configuration procedures, troubleshooting steps, and policy implementation. Grasping both the technical specifications and practical applications forms a strong foundation for exam readiness.
The conceptual framework also extends to network topologies and protocol operations. Awareness of Layer 2 and Layer 3 operations, VLAN segmentation, IP addressing schemes, and routing protocols contributes to a holistic understanding. Integrating these concepts with Aruba-specific tools ensures that theoretical knowledge translates seamlessly into practical expertise. This combination of foundational knowledge and contextual application is crucial for performing effectively in simulated and real-world network scenarios.
The Role of Theoretical Knowledge in Exam Preparation
Theoretical mastery serves as the cornerstone of HPE6-A79 exam preparation. While practical experience is indispensable, understanding the principles behind configurations and protocols ensures that candidates can adapt to unfamiliar scenarios. The exam evaluates not just rote memorization but the ability to analyze, reason, and apply concepts.
Delving into official Aruba documentation provides clarity on functionalities, command structures, and configuration nuances. Manuals detailing ArubaOS and ClearPass features offer structured insights that are essential for conceptual understanding. This textual knowledge can be supplemented by white papers, technical guides, and architecture diagrams to reinforce comprehension.
Conceptual learning enhances problem-solving skills by exposing candidates to the rationale behind specific configurations. Recognizing why certain security policies are enforced, or how traffic management strategies affect network performance, enables thoughtful application in practical labs. This theoretical depth prevents superficial understanding and equips candidates to handle complex exam scenarios confidently.
Hands-On Labs and Experiential Learning
Experiential learning forms a pivotal aspect of exam readiness. Engaging in practical labs allows candidates to translate theory into action, reinforcing understanding and building operational confidence. Setting up virtual or physical test environments simulates real-world network conditions, providing a controlled space for experimentation and troubleshooting.
Hands-on practice helps in mastering key Aruba functionalities, such as configuring wireless controllers, setting up user roles, deploying security certificates, and managing access policies. Performing repetitive tasks in a lab environment enhances muscle memory and reduces errors during actual exam execution. Additionally, practicing problem-solving scenarios, such as resolving connectivity issues or implementing access restrictions, cultivates adaptive thinking essential for the exam.
Simulations also provide opportunities to explore less familiar features without fear of repercussions. This freedom to experiment encourages curiosity and promotes deeper comprehension. Candidates can test multiple configurations, observe outcomes, and refine approaches, creating an experiential learning cycle that complements theoretical study.
Utilizing Study Groups and Community Insights
Collaboration and knowledge exchange significantly enrich the preparation journey. Engaging with study groups or online communities exposes candidates to diverse perspectives and problem-solving techniques. These interactions facilitate deeper understanding by highlighting alternative approaches and common pitfalls.
Within such communities, participants often share personal experiences, study strategies, and exam-specific tips. This collective intelligence can illuminate nuances that may not be evident in documentation alone. Discussions may cover configuration intricacies, real-world troubleshooting, and best practices for maintaining network integrity under various conditions.
Moreover, active participation in these communities encourages accountability and sustained motivation. Peer interaction can reinforce study habits, provide encouragement during challenging topics, and enhance retention through dialogue. Leveraging collective knowledge ensures candidates are not navigating preparation in isolation, enriching the learning process with multiple perspectives.
Strategic Practice and Self-Assessment
Regular practice and assessment are critical for gauging readiness. Mock exams and practice questions allow candidates to familiarize themselves with the exam structure, question types, and timing constraints. These exercises reveal knowledge gaps and highlight areas that require deeper review.
Analyzing performance after practice sessions provides actionable insights. Candidates can identify recurring mistakes, refine time management skills, and develop strategies for tackling challenging questions. This iterative approach to self-assessment ensures continuous improvement and builds confidence in handling exam pressure.
Additionally, integrating practice exercises with theoretical review strengthens memory retention. Revisiting concepts that posed challenges during practice solidifies understanding and reduces the likelihood of repeating errors. Over time, this approach creates a robust framework where knowledge, application, and problem-solving coalesce.
Psychological Preparedness and Exam Day Strategy
Cognitive readiness is as crucial as technical mastery. Maintaining composure, focus, and mental clarity directly impacts exam performance. Adequate rest, nutrition, and stress management are essential components of psychological preparedness. Candidates should establish a routine that balances study with relaxation to ensure optimal mental acuity.
On exam day, arriving early and familiarizing oneself with the environment minimizes anxiety. Approaching questions methodically, allocating time wisely, and maintaining a calm mindset are effective strategies for sustained concentration. Recognizing that preparation extends beyond content mastery to include mental and emotional readiness can significantly influence outcomes.
Mindfulness techniques, such as focused breathing or brief mental pauses between sections, help in maintaining clarity and reducing stress. Candidates who integrate psychological preparedness with technical readiness often demonstrate higher accuracy, improved decision-making, and better time management under exam conditions.
Integration of Practical Skills and Theory in Real-World Scenarios
A distinguishing factor in successful exam performance is the ability to integrate practical skills with theoretical understanding. Exam questions often simulate real-world networking scenarios, requiring candidates to apply knowledge dynamically rather than rely solely on memorized facts.
Understanding the interplay between system configuration, network security, and user management enables informed decision-making. Candidates should focus on the functional purpose of each task, such as why certain access policies are enforced or how device authentication protocols impact security. Applying theory in practical scenarios ensures that problem-solving is efficient, accurate, and contextually relevant.
This integrated approach also cultivates long-term expertise beyond the exam. Candidates develop competencies that are directly transferable to professional networking environments, reinforcing both confidence and capability. Real-world integration underscores the value of preparation as a continuous learning process, where theory informs practice and practice reinforces theory.
Conclusion
Achieving the HPE6-A79 certification is a milestone that reflects both deep knowledge and practical mastery of Aruba mobility solutions. It requires dedication to understanding the intricacies of WLAN architecture, advanced troubleshooting, security implementation, and network management. By methodically preparing through hands-on labs, detailed study of official documentation, and engaging with the Aruba community, candidates can build confidence and expertise. This certification not only validates technical skills but also empowers professionals to design and manage robust, efficient, and secure wireless networks. With strategic preparation and continuous learning, success in the HPE6-A79 exam becomes an attainable and rewarding achievement.
Top HP Exams
- HPE7-A01 - HPE Network Campus Access Professional
- HPE0-S59 - HPE Compute Solutions
- HPE6-A86 - HPE Network Switching Associate
- HPE7-A08 - HPE Network Switching Professional
- HPE0-V25 - HPE Hybrid Cloud Solutions
- HPE6-A88 - HPE Networking ClearPass
- HPE0-V27 - HPE Edge-to-Cloud Solutions
- HPE7-A02 - Aruba Certified Network Security Professional
- HPE2-T37 - Using HPE OneView
- HPE7-A11 - HPE Network Campus Access Professional Architect
- HPE7-A03 - Aruba Certified Campus Access Architect
- HPE7-A06 - HPE Aruba Networking Certified Expert - Campus Access Switching
- HPE6-A78 - HPE Network Security Associate
- HPE6-A73 - Aruba Certified Switching Professional
- HPE7-A10 - HPE Network Security Expert
- HPE0-J68 - HPE Storage Solutions
- HPE6-A90 - HPE Networking Central
- HPE6-A84 - Aruba Certified Network Security Expert Written Exam
- HPE6-A85 - HPE Network Campus Access Associate
- HPE7-A07 - HPE Campus Access Mobility Expert