Exam Code: CISSP-ISSEP
Exam Name: Information Systems Security Engineering Professional
Certification Provider: ISC
Corresponding Certifications: CISSP Concentrations, CISSP-ISSEP
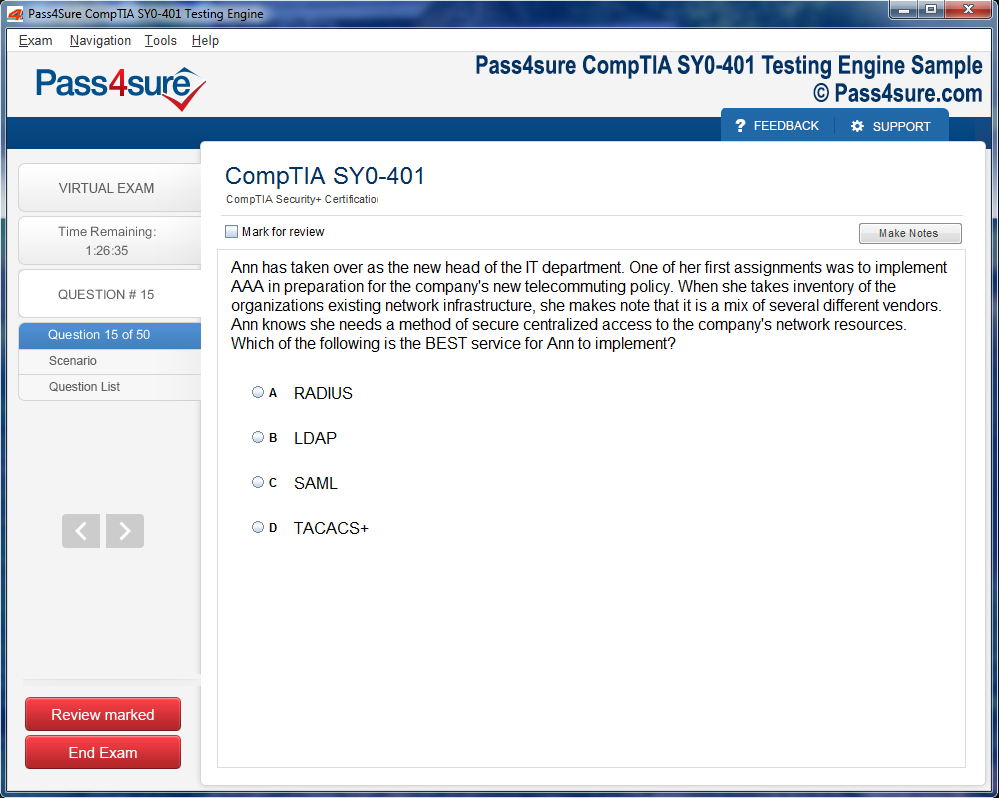
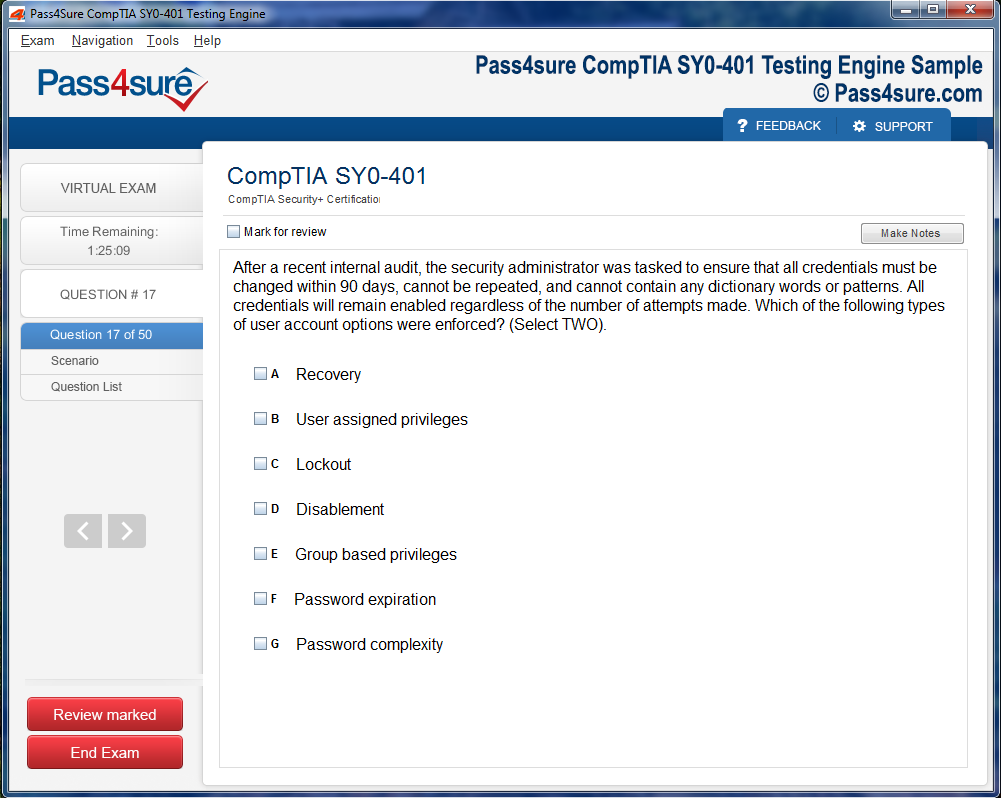
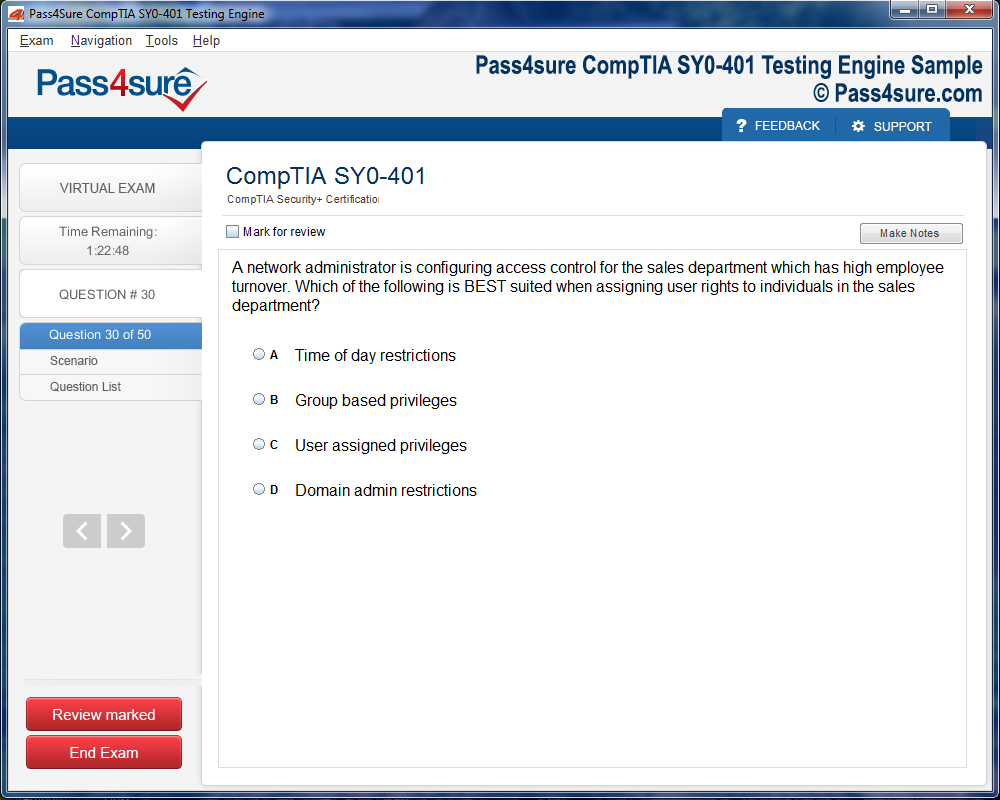
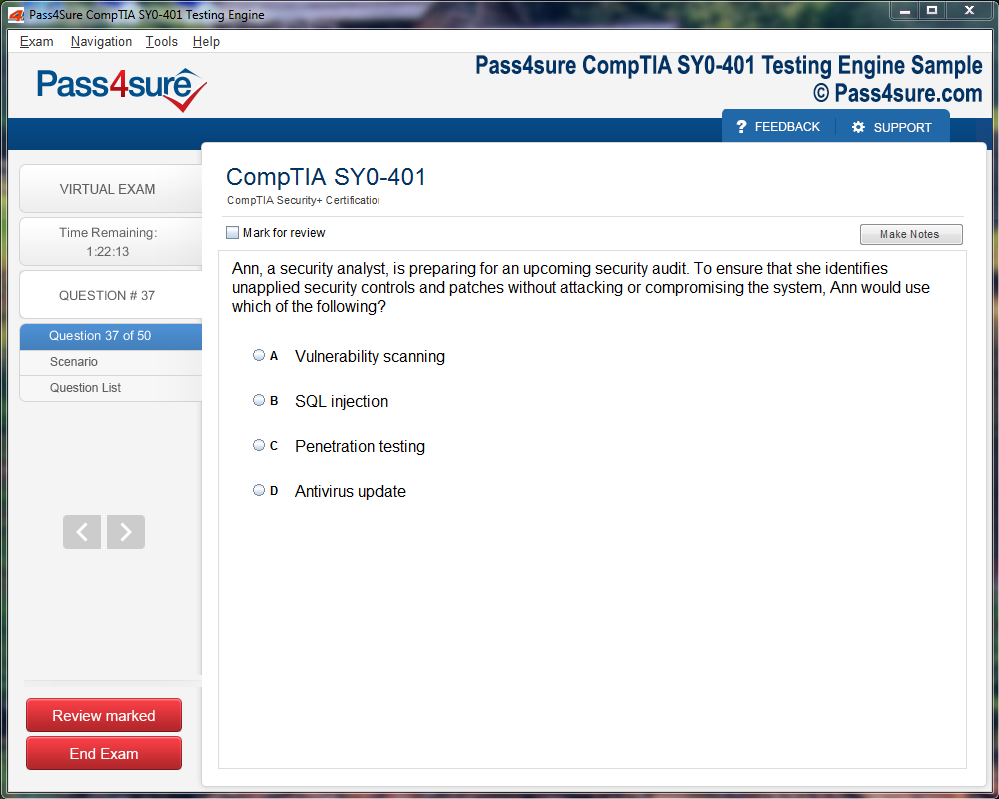
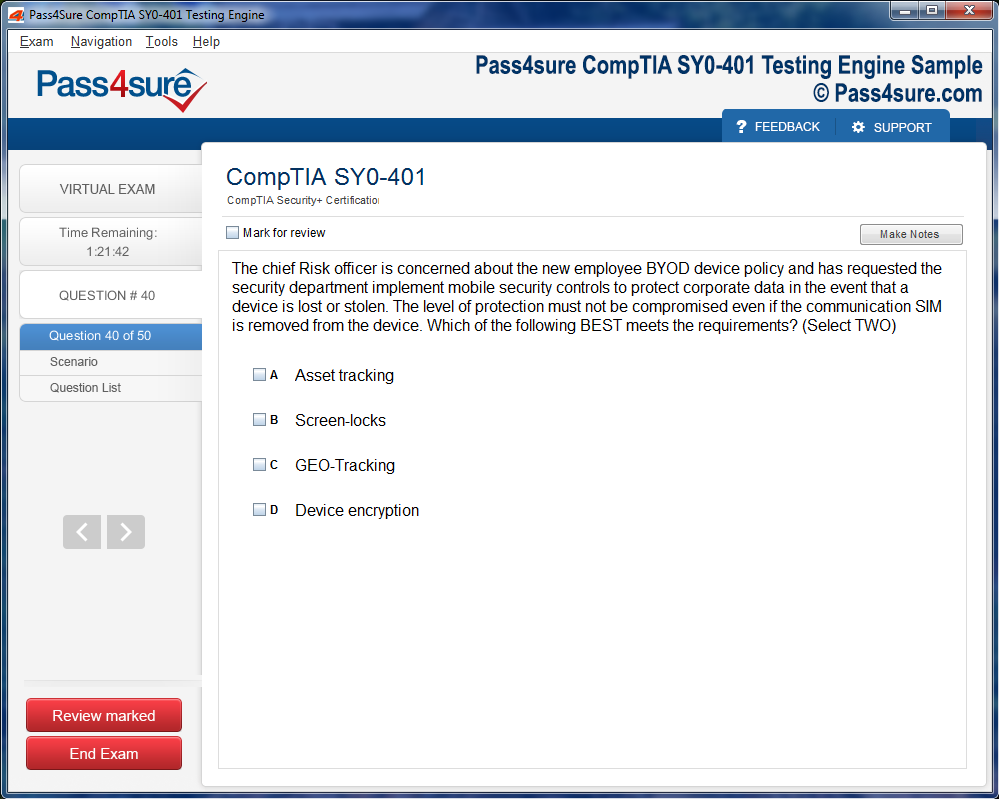
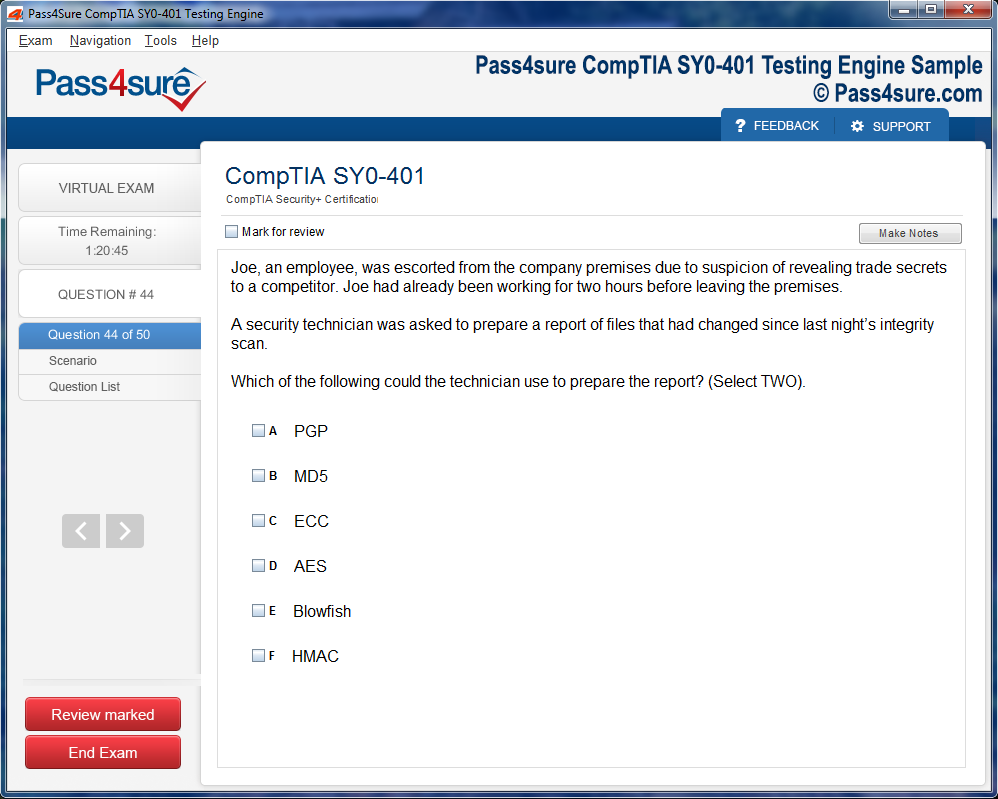
Product Screenshots
Product Reviews
Something that is really amazing
"It is only Pass4sure that tries to provide you something that is really amazing for training of CISSP-ISSEP exam. Due to Pass4sure I improved my skills for CISSP Concentrations CISSP-ISSEP exam and got highest scores in the ISC CISSP-ISSEP exam.
Brenan"
Great service
"Firstly I would like to say thanks to Pass4sure for a great service! Secondly I want to let you know all that I passed my CISSP-ISSEP exam recently. After reading Pass4sure material I felt so prepared and confident for ISC CISSP-ISSEP exam. I could not have done it without Pass4sure’s proper guide and help. Thanks a lot for making the CISSP Concentrations CISSP-ISSEP exam strangely easier for me.
Stephen Chuck"
Really appreciable
"I really appreciate Pass4sure effort for students. I used Pass4sure material for my CISSP-ISSEP exam and passed it on first attempt. Thank you so much for coming up with this ISC CISSP-ISSEP exam ingenious material which is guaranteed to help applicant to pass the CISSP Concentrations CISSP-ISSEP exam for sure.
Charlie Brown"
i loved the exam prep course pack age system
"I just wanted to say I went to the training class for pass 4 sure for the prep of the exam, CISSP-ISSEP exam on the 17th and I really enjoyed it. pass 4 sure was were very informative and made the ISC CISSP-ISSEP exam test a lot easier for me. I will definitely recommend pass 4 sure to any one who wants to obtain there notary commission. Again thank you. I went to the training class for pass 4 sure for the prep of the exam, ISC CISSP-ISSEP exam on the 17th and I really enjoyed it. pass 4 sure was were very informative and made the CISSP Concentrations CISSP-ISSEP exam test a lot easier for me. I will definitely recommend pass 4 sure to any one who wants to obtain there notary commission. Again thank you.
Samantha"
Pass4usre Offers Free Environment
"The best thing of Pass4sure ISC CISSP-ISSEP test papers is that it gives a freely environment for the sake of preparing CISSP-ISSEP exam. You can use your all abilities in a very comfortable way and can do a satisfied preparation of CISSP Concentrations CISSP-ISSEP exam through Pass4sure test papers.
Turner"
It Is Truly Worth The Time And Effort
"I had a swell experience undergoing preparation and training using the Pass4sure CISSP-ISSEP preparatory resources. I enjoyed the learning and the structure of the tests. I liked that the materials included step-by-step exercise and tutorials. It gives a very good grounding for the subject content of the ISC CISSP-ISSEP exam, but allows you to learn it at your own pace and at times that suits busy people well. This course produced real learning. All in all, I found the training to be more than worth my time and worth the cost. The result was that I shone in my CISSP Concentrations CISSP-ISSEP exam and got the certification!
Matthew A Robbins"
Feeling lucky
"Your CISSP-ISSEP exam material helped me a lot. Material was really great and organized. I took ISC CISSP-ISSEP exam and passed. I am feeling so lucky. I will highly recommend Pass4sure CISSP Concentrations CISSP-ISSEP exam material to all others. Thank you Pass4sure.
Vince"
Do Wonderful Performance With Pass4sure
"If your CISSP-ISSEP exam is creating problem in your life then wait and listen! Give Pass4sure ISC CISSP-ISSEP exam preparatory guide a chance and then see the miracle which will lead you towards a very successful and satisfied result. Start your preparations for CISSP Concentrations CISSP-ISSEP exam and do a wonderful performance by getting highest grades.
Tillie"
Complete Details And Solid Concepts
"The CISSP-ISSEP exam went pretty well for me; I passed with outstanding results and got my certification within a month’s time. I owe it all to you Pass4sure! The only reason that I did so well, is because I received top-notch help from your ISC CISSP-ISSEP exam preparatory materials. Every exam feature was explained in full detail and I was able to build a very solid foundation for my concepts. Even though I only spent a week using the model tests and exercises, I found myself capable of attempting the CISSP Concentrations CISSP-ISSEP exam pretty easily. I believe that my score could have been much higher had I spent a little more time on the drill exercises. None the less I am quite happy with my result and I owe it all to you!
Steven N Hopkins"
Success Will Be Yours If You Use Pass4sure
"Passing CISSP-ISSEP exam is not a big deal if you are preparing yourself from the best quality preparatory tool. Pass4sure ISC CISSP-ISSEP exam preparatory material is the most wanted pathway nowadays. You just have to prepare your CISSP Concentrations CISSP-ISSEP exam from Pass4sure exam preparatory material and success will surely be yours.
Tarrant"
Frequently Asked Questions
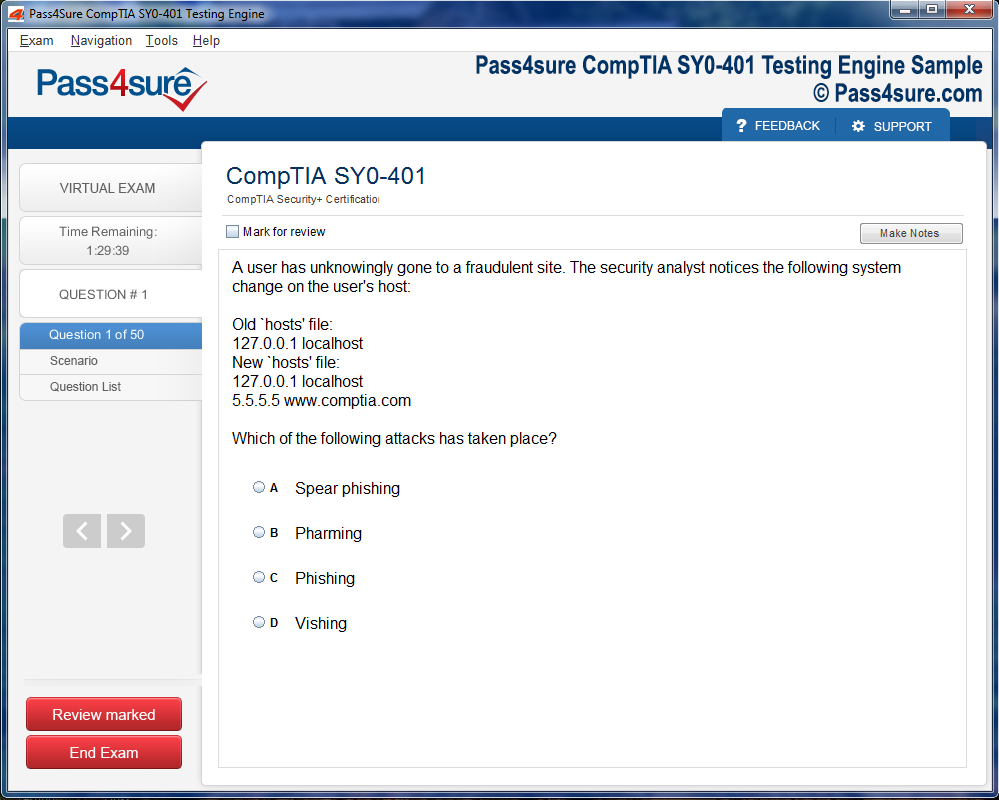
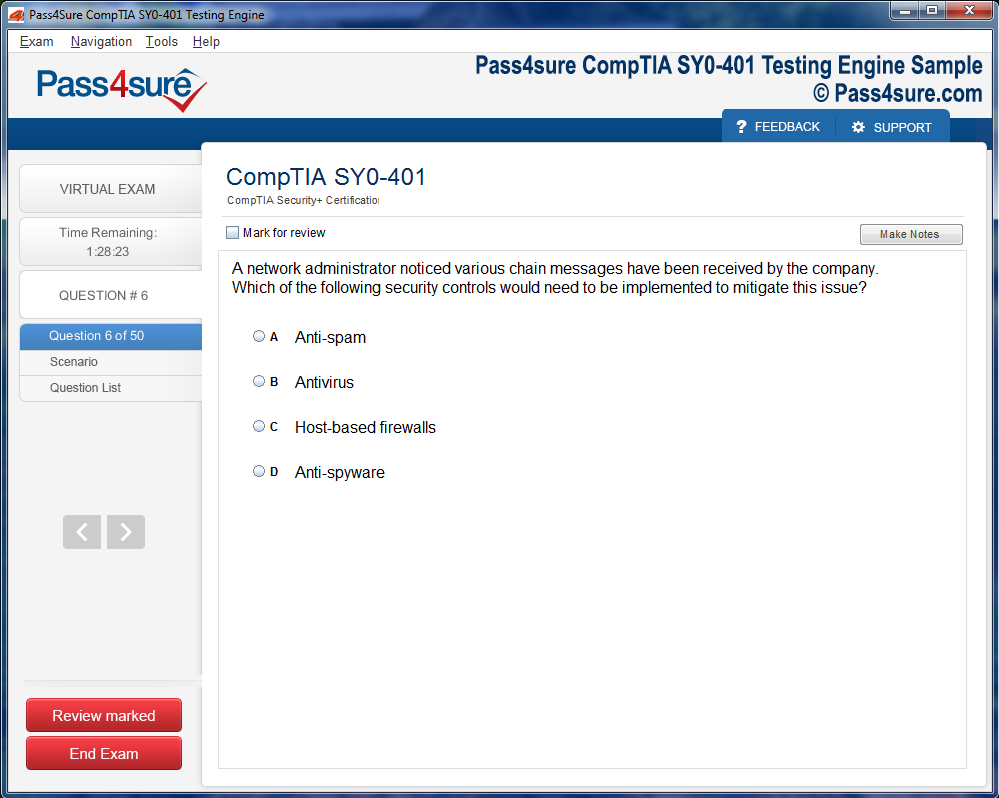
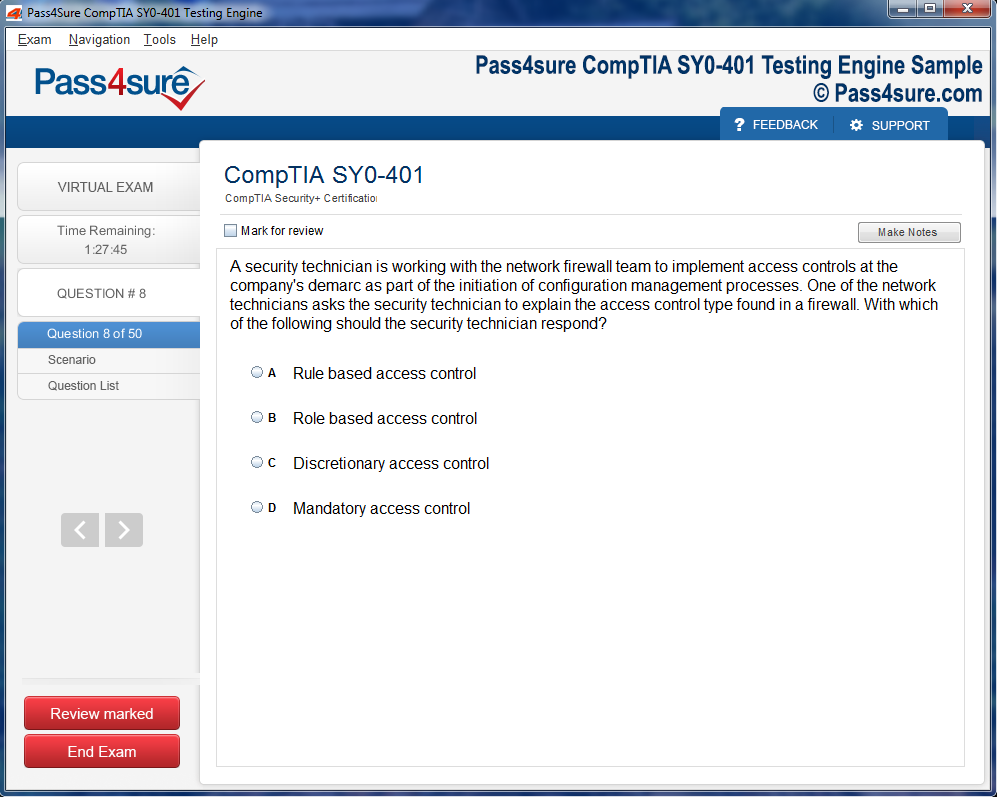
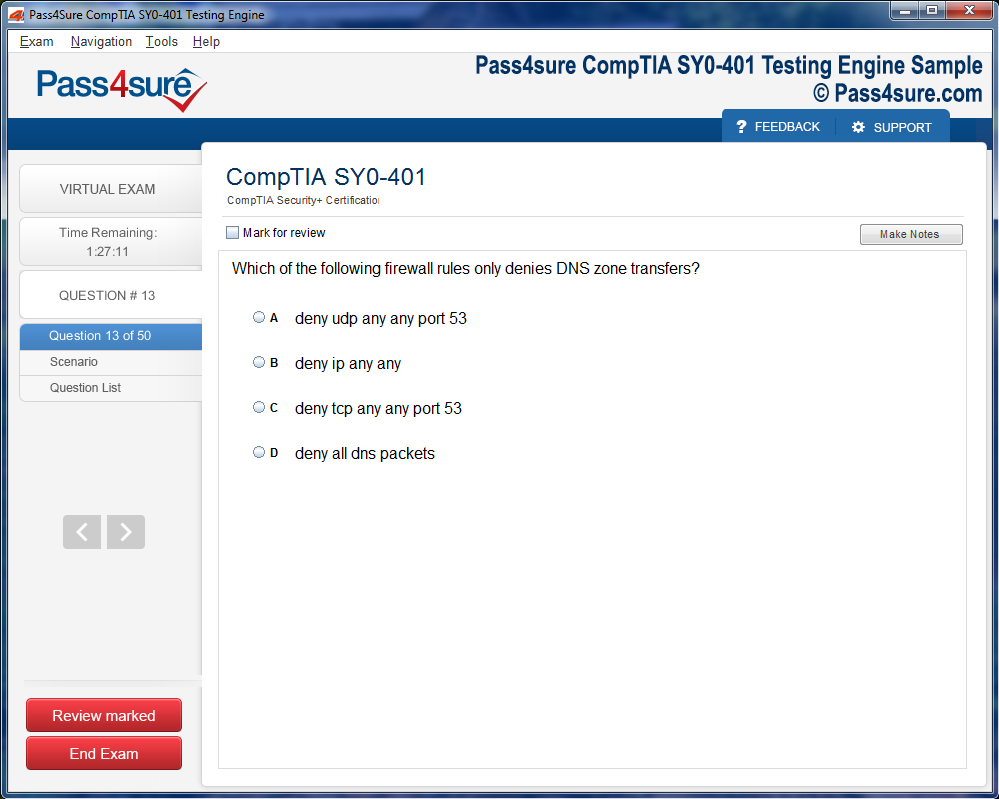
How does your testing engine works?
Once download and installed on your PC, you can practise test questions, review your questions & answers using two different options 'practice exam' and 'virtual exam'. Virtual Exam - test yourself with exam questions with a time limit, as if you are taking exams in the Prometric or VUE testing centre. Practice exam - review exam questions one by one, see correct answers and explanations.
How can I get the products after purchase?
All products are available for download immediately from your Member's Area. Once you have made the payment, you will be transferred to Member's Area where you can login and download the products you have purchased to your computer.
How long can I use my product? Will it be valid forever?
Pass4sure products have a validity of 90 days from the date of purchase. This means that any updates to the products, including but not limited to new questions, or updates and changes by our editing team, will be automatically downloaded on to computer to make sure that you get latest exam prep materials during those 90 days.
Can I renew my product if when it's expired?
Yes, when the 90 days of your product validity are over, you have the option of renewing your expired products with a 30% discount. This can be done in your Member's Area.
Please note that you will not be able to use the product after it has expired if you don't renew it.
How often are the questions updated?
We always try to provide the latest pool of questions, Updates in the questions depend on the changes in actual pool of questions by different vendors. As soon as we know about the change in the exam question pool we try our best to update the products as fast as possible.
How many computers I can download Pass4sure software on?
You can download the Pass4sure products on the maximum number of 2 (two) computers or devices. If you need to use the software on more than two machines, you can purchase this option separately. Please email sales@pass4sure.com if you need to use more than 5 (five) computers.
What are the system requirements?
Minimum System Requirements:
- Windows XP or newer operating system
- Java Version 8 or newer
- 1+ GHz processor
- 1 GB Ram
- 50 MB available hard disk typically (products may vary)
What operating systems are supported by your Testing Engine software?
Our testing engine is supported by Windows. Andriod and IOS software is currently under development.
Proven Tips to Pass the CISSP-ISSEP Certification Exam
In the digital era, organizations rely heavily on secure and resilient information systems to sustain their operations, protect their assets, and maintain trust with stakeholders. As technology grows in complexity, so too do the threats that seek to exploit weaknesses in these systems. From stealthy intrusions to large-scale attacks capable of crippling entire infrastructures, modern challenges demand professionals who can design systems that are not only functional but also inherently secure. The CISSP-ISSEP certification serves as a distinguished credential for individuals seeking to prove their mastery in systems security engineering. It represents a unique combination of knowledge, applied expertise, and forward-looking skills that enable professionals to safeguard critical assets across industries.
The certification is a concentration under the broader Certified Information Systems Security Professional credential. Unlike the foundational CISSP, which spans the entire cybersecurity spectrum, the ISSEP narrows its focus to security engineering, ensuring that every system component is scrutinized for vulnerabilities and reinforced with robust safeguards. This concentration allows professionals to blend engineering precision with security principles, ensuring that defenses are incorporated into a system’s very architecture.
Developed in close collaboration with standards rooted in defense and government practices, the ISSEP bridges theoretical knowledge and practical implementation. It empowers professionals to build solutions that endure in real-world conditions, where systems must remain resilient against persistent and evolving adversaries. By validating advanced competencies, the ISSEP equips professionals with recognition that extends across global industries, providing credibility and trust in their ability to design fortified systems.
Origins and Foundations of Security Engineering Expertise
The foundation of the CISSP-ISSEP certification lies in a legacy of collaboration between industry and government. When the certification was crafted, it drew heavily upon the rigorous standards applied in mission-critical defense projects. The need for disciplined engineering processes was clear: information systems were no longer optional tools but vital assets upon which entire missions and organizations depended.
Security engineering, as a discipline, emerged from the recognition that traditional cybersecurity measures often acted as afterthoughts. Systems would be designed for performance, efficiency, or usability, and only afterward would organizations attempt to patch vulnerabilities or insert protective measures. This reactive approach proved insufficient against increasingly complex threats. The ISSEP reversed this mindset by embedding security into every layer of design and development, creating systems where resilience was part of the blueprint rather than a supplemental feature.
Through structured processes, risk-driven methodologies, and standards-based practices, ISSEP professionals are trained to examine systems holistically. Every phase, from initial requirements gathering to final decommissioning, carries the imprint of security considerations. This structured approach ensures that systems not only meet performance goals but also maintain integrity, confidentiality, and availability under stress.
Relevance in Modern Cybersecurity Environments
The demand for ISSEP-certified professionals has grown alongside the expanding threat landscape. Organizations across sectors have realized that a failure in security engineering can result in catastrophic consequences. Breaches today extend beyond data theft; they can disrupt healthcare systems, financial institutions, power grids, transportation networks, and critical defense operations. A single vulnerability in design can cascade into national security crises or global financial instability.
The ISSEP credential underscores the ability of professionals to anticipate and mitigate such risks. Unlike certifications that emphasize detection and response, ISSEP emphasizes resilience. Professionals holding this certification demonstrate the foresight to consider security in every design decision. They create systems that do not rely solely on reactive controls but instead possess defenses that are integral to their structure.
This relevance extends far beyond defense or government sectors. Enterprises across the globe face increasing scrutiny from regulators, stakeholders, and customers regarding their security postures. From protecting intellectual property in technology companies to safeguarding patient information in healthcare, the ISSEP provides a framework to ensure security is engineered from inception.
The Six Domains of Mastery
The CISSP-ISSEP certification is structured around six key domains that together encompass the full breadth of systems security engineering. Each domain is designed to build competencies that are essential for creating secure systems in diverse contexts.
The first domain, Systems Security Engineering Foundations, establishes the core principles, models, and standards. It provides the philosophical and methodological base upon which all secure systems are constructed. This domain ensures that candidates understand both the theoretical and practical underpinnings of their work.
The second domain, Risk Management, emphasizes identifying vulnerabilities, assessing probabilities, and evaluating potential impacts. ISSEP professionals are trained to integrate risk considerations into every decision, ensuring that mitigation strategies are balanced against mission and organizational goals.
The third domain, Security Planning and Design, is where abstract principles are transformed into concrete architectures. This domain ensures that security is not isolated but woven into the design fabric, producing systems that operate with built-in resilience.
The fourth domain, Systems Implementation, Verification, and Validation, focuses on proving that designs meet requirements. Through rigorous testing, validation, and assurance, this stage confirms that systems are prepared to function securely in real-world scenarios.
The fifth domain, Secure Operations, Change Management, and Disposal, recognizes that security is a lifecycle responsibility. Systems evolve, technologies shift, and operational environments change. ISSEP professionals ensure that security persists through maintenance, upgrades, and even the final disposal of systems.
The sixth domain, Technical Management, brings leadership into focus. Beyond technical mastery, professionals are expected to guide teams, manage projects, and coordinate across disciplines. This domain elevates the ISSEP credential by recognizing that effective engineering requires both technical and managerial expertise.
Together, these domains ensure that candidates are not narrowly specialized but instead carry holistic expertise that spans every stage of system development and operation.
The Professional Journey Toward ISSEP
Attaining the CISSP-ISSEP credential is not the first step in a career but rather an advanced milestone. It requires candidates to hold the foundational CISSP certification, ensuring that they already possess a wide-ranging knowledge of information security. Furthermore, professionals must demonstrate significant experience in engineering practices, reflecting their ability to apply knowledge in complex real-world environments.
The pathway to ISSEP reflects the certification’s role as a specialization. It is designed for those who aspire to deepen their expertise and distinguish themselves in roles where system design and security engineering are paramount. Senior engineers, architects, analysts, and assurance officers find in the ISSEP an avenue to refine their skills and gain formal recognition of their advanced capabilities.
The exam itself demands more than rote memorization. Candidates face scenario-based challenges that require analytical thinking, applied knowledge, and practical decision-making. This ensures that certified individuals are not only well-versed in theories but also adept at applying them under the pressures and ambiguities of professional practice.
For many, preparing for the ISSEP represents a transformative phase. It compels candidates to study not only the mechanics of security engineering but also the broader implications of their designs. They come to appreciate the balance between innovation and protection, between operational goals and security imperatives. This reflective journey enhances both their technical abilities and their professional maturity.
Organizational Benefits of ISSEP Expertise
Organizations that employ ISSEP-certified professionals benefit from more than individual expertise; they gain a strategic advantage in resilience and trust. Secure systems reduce the likelihood of costly breaches, regulatory penalties, and reputational damage. They also create confidence among clients, partners, and regulators who view robust engineering as a sign of organizational reliability.
The certification encourages a culture of proactive defense, shifting mindsets from patching vulnerabilities after they appear to anticipating and preventing them during the design phase. This approach minimizes operational disruptions and ensures that systems can support missions and business objectives without compromise.
From an economic perspective, the value is equally clear. The costs of responding to a breach—legal settlements, remediation expenses, lost productivity—often far outweigh the investments required to design systems securely. ISSEP professionals help organizations avoid these expenses by embedding resilience into the very foundations of their systems.
The global demand for skilled security engineers has also created intense competition for talent. Organizations that can boast ISSEP-certified staff gain not only enhanced technical capabilities but also a reputation that aids in recruiting, retaining, and reassuring stakeholders. This recognition becomes a differentiating factor in industries where trust and resilience are non-negotiable.
The Broader Impact of ISSEP on the Cybersecurity Landscape
The influence of ISSEP-certified professionals extends beyond their immediate organizations. By advancing the discipline of security engineering, they contribute to raising the overall standards of the cybersecurity field. Their expertise shapes projects that underpin critical infrastructure, defense readiness, economic stability, and global connectivity.
As the digital ecosystem becomes increasingly interconnected, vulnerabilities in one sector can ripple across entire industries. ISSEP professionals, by ensuring that systems are robust at their core, help stabilize this interconnected landscape. Their contributions reduce systemic risks, fostering resilience not only within individual organizations but across the digital environment as a whole.
This broader impact is particularly vital in an era where digital trust is both fragile and indispensable. Citizens, consumers, and businesses alike depend on systems functioning securely without interruption. By applying their specialized expertise, ISSEP professionals uphold this trust, ensuring that technology continues to serve as an enabler rather than a source of vulnerability.
Systems Security Engineering Foundations
The CISSP-ISSEP exam begins with the foundation of systems security engineering, a domain that sets the intellectual and professional stage for all the others. At its core, this domain emphasizes the integration of security into the engineering process, treating it not as an afterthought but as an intrinsic quality woven into every stage of development. The life-cycle approach dominates here, teaching candidates that a system cannot be trusted unless its architecture reflects security from conception through decommissioning.
Security design principles provide the intellectual compass for this work. Concepts such as least privilege, defense in depth, and separation of duties serve as guardrails that prevent design flaws from creating catastrophic vulnerabilities later in implementation. Systems thinking is also central to this foundation. Instead of analyzing isolated parts, candidates must learn to consider the interdependence of subsystems, their relationships, and the emergent properties that may amplify risk.
The principle of trustworthiness is not abstract; it becomes measurable when applied through frameworks like ISO/IEC standards. These frameworks guide the engineering community in defining and validating security requirements. By anchoring systems design to widely accepted standards, professionals build solutions that meet regulatory expectations while resisting the constantly evolving threat landscape.
In practical application, these principles manifest in projects that demand airtight security from the earliest sketches. Consider the design of a satellite communication platform for defense operations. Rather than waiting until the final stages to embed encryption, engineers must architect protocols that protect integrity, confidentiality, and availability before a single line of code is written. This proactive embedding of security transforms the final product into something resilient rather than reactive.
The foundation domain carries significant weight in the exam because it reflects professional philosophy as much as technical mastery. It encourages candidates to adopt a mindset in which engineering excellence and security are indistinguishable from each other. Without this foundation, the subsequent domains lose their coherence, for every other practice in security engineering rests upon the steady ground of these principles.
Risk Management
Risk management, though smaller in exam weight, carries immense operational significance. Security engineers must accept that risk cannot be eliminated; instead, it must be identified, evaluated, mitigated, and monitored. This process is dynamic, requiring vigilance as technologies change, adversaries evolve, and organizational priorities shift.
Threat modeling sits at the heart of this domain. Engineers map potential adversaries, their capabilities, and the pathways through which they could exploit vulnerabilities. This proactive activity ensures that defenses are not built only after a breach but before an incident occurs. Risk assessment methodologies provide the structured techniques for scoring and prioritizing these risks, balancing them against cost and system performance requirements.
Safeguards represent the tangible outputs of risk management. Encryption, access controls, intrusion detection systems, and multi-factor authentication are not merely tools; they are expressions of a deliberate decision to minimize impact without compromising functionality. Yet, safeguards are never static. Continuous monitoring ensures that they remain effective as adversaries innovate new methods of attack.
Consider the implementation of a nationwide electronic health record system. The risks to patient confidentiality are immense, as attackers may seek to exploit personal data for profit or malicious influence. Through risk assessment, engineers identify weaknesses in data storage, transmission, and access. Through safeguards like strong encryption, role-based access, and multifactor authentication, these risks are reduced to an acceptable level. Regular audits and penetration testing maintain the system’s defensive posture against emerging threats.
This domain also tests the professional’s ability to weigh competing priorities. For example, adding extensive security checks may slow system performance. Conversely, prioritizing speed at the expense of safeguards invites disaster. The art of risk management lies in striking a balance where usability, cost, and security coexist in harmony.
Security Planning and Design
This domain commands the greatest share of the exam, reflecting its centrality in security engineering practice. Security planning and design shape the architecture that ensures systems achieve their intended functions without succumbing to internal or external threats.
At the center of this domain is a secure architecture. Defense-in-depth, segmentation, redundancy, and least privilege are not merely buzzwords but essential architectural layers. Each element addresses a different aspect of resilience. Defense-in-depth ensures that breaching one barrier does not mean total compromise. Segmentation limits the spread of attacks by isolating components. Redundancy guarantees continuity even if parts of the system fail. Least privilege minimizes damage by restricting users and processes to only what is necessary.
Planning also involves translating requirements into enforceable policies. Compliance obligations are not optional. Security engineers must anticipate and embed regulatory expectations into system design, ensuring that platforms satisfy both organizational goals and external oversight.
Practical illustrations clarify the scope of this domain. Imagine constructing a digital payments infrastructure. Security planning dictates that not only must transactions be efficient and user-friendly, but they must also resist fraud, protect cardholder information, and comply with payment security regulations. Engineers must align architecture with security policies, weaving authentication, encryption, logging, and fraud detection into every layer of the platform.
This domain also emphasizes adaptability. Threats evolve, and designs must anticipate long-term resilience. Engineers must create architectures flexible enough to accommodate patches, upgrades, and technological advancements without compromising security. This foresight transforms planning into a strategic act rather than a reactive necessity.
The heavy exam weighting of this domain underscores its importance in real-world applications. Security planning and design embody the transition from theoretical principles into tangible architecture that can withstand real adversarial pressures.
Systems Implementation, Verification, and Validation
Once planning is complete, the next logical step is to bring designs into reality. This domain ensures that professionals understand the structured process of implementation, where secure concepts become operational systems. Verification and validation represent the final assurances that design intent aligns with performance outcomes.
System integration is often complex, as different subsystems, applications, and hardware components converge. Security engineers must oversee this integration carefully, ensuring that interfaces do not create vulnerabilities. Implementation also demands strict adherence to secure coding practices, configuration management, and controlled deployment processes.
Verification answers the question of whether the system was built correctly. Validation addresses whether the correct system was built. Together, they form a dual assurance that protects both the engineering process and its final product. Testing methods range from static code analysis to dynamic penetration testing, each designed to uncover flaws before adversaries can exploit them.
Consider the deployment of a new identity management system for a multinational corporation. Implementation requires careful coordination across diverse networks, user groups, and regional regulations. Verification involves testing whether access controls correctly restrict unauthorized individuals. Validation ensures the system functions seamlessly across global operations, supporting business needs while maintaining strong security.
Without rigorous verification and validation, even the most elegantly designed system can harbor hidden flaws. This domain teaches professionals the discipline of structured testing, reducing reliance on assumptions and ensuring that systems meet their security and operational requirements in practice.
Secure Operations, Change Management, and Disposal
After implementation, systems enter the longest phase of their life cycle: operations. This domain prepares professionals to maintain, monitor, and eventually retire systems in a manner that preserves security throughout their existence.
Secure operations involve constant vigilance. Monitoring tools detect anomalies, patch management closes vulnerabilities, and incident response plans ensure quick recovery from breaches. Engineers must maintain operational resilience without compromising performance or user experience.
Change management introduces another layer of complexity. Every update, patch, or modification must be carefully reviewed, tested, and documented. Even seemingly minor changes can create unforeseen weaknesses. Structured change management processes ensure that updates strengthen systems rather than degrade them.
Disposal, often overlooked, is equally important. Retiring outdated systems without secure data destruction creates serious risks. Sensitive information may linger on decommissioned hardware, vulnerable to exploitation. Engineers must ensure complete sanitization, whether through overwriting, degaussing, or physical destruction.
Consider the example of a financial institution retiring old servers. Secure disposal demands more than reformatting drives. Engineers must guarantee that no data remains recoverable, often resorting to physical destruction to ensure irretrievability. In this way, disposal becomes the final safeguard in the system’s life cycle, protecting sensitive data even after active use ends.
This domain reminds professionals that security is a continuous commitment, not a one-time effort. Operations demand persistence, and disposal requires closure that is as deliberate and disciplined as the initial design.
Technical Management
Technical management runs across all domains, acting as the binding force that ensures coherence between people, processes, and technology. This domain highlights the leadership and organizational skills that transform technical knowledge into practical results.
Effective management requires clear communication, resource allocation, and coordination across diverse teams. Security engineering often unfolds within multinational environments, where cultural, linguistic, and regulatory differences add complexity. The ability to harmonize these elements defines successful technical management.
Project management also plays a critical role. Timelines must be realistic, budgets must be maintained, and quality must not be sacrificed. Technical managers balance these competing demands while ensuring that security remains central.
Consider leading a global project to develop secure communication platforms for military alliances. The manager must coordinate specialists across continents, synchronize efforts despite time zone differences, and maintain cohesion under tight deadlines. Success depends as much on leadership and communication as on technical skill.
Technical management also emphasizes professional responsibility. Leaders must inspire trust, maintain transparency, and foster a culture of accountability. Without these qualities, even the most technically sound project risks collapse due to misalignment or poor coordination.
This domain reinforces the idea that security engineering is not a solitary endeavor. It is a collective enterprise that requires structured management to ensure success across complex, high-stakes projects.
Integration of Domains into Professional Practice
The six domains of the CISSP-ISSEP exam are not isolated silos but interwoven threads that form the fabric of secure systems engineering. Mastery comes not from memorizing each domain in isolation but from understanding their interplay in real-world practice.
Security foundations provide the philosophical grounding, risk management balances priorities, planning and design create the architecture, implementation validates its function, operations sustain resilience, and technical management harmonizes the entire process. Together, they reflect the complete life cycle of secure systems, from conception to disposal.
Professionals who internalize these domains embody the discipline of security engineering at its highest level. They approach systems not as temporary constructs but as enduring structures designed to resist the ingenuity of adversaries across decades. They balance technical precision with managerial foresight, building systems that serve organizational missions while safeguarding critical assets.
The CISSP-ISSEP exam evaluates more than technical knowledge. It measures maturity, foresight, and the ability to apply structured principles in unpredictable environments. By mastering its domains, candidates not only prepare for certification but also cultivate the skills essential for defending the complex technological ecosystems on which modern society depends.
Building the Foundation of a Study Journey
Preparing for the CISSP-ISSEP examination is not just about memorization; it is a process of reshaping the way one perceives information security systems. Many aspirants often assume preparation to be similar to earlier certification journeys, but the ISSEP path differs because it requires mastery of applied knowledge. A strong foundation starts with acknowledging that the exam measures not only understanding of theories but also the ability to integrate them into practical architectures. Before diving into books or practice questions, a candidate should reflect upon the experiences already gained in professional life, because those lived experiences become the lens through which study content will be understood.
The first step in this journey is creating an inner commitment to persistence. Unlike short-term learning, mastering ISSEP concepts demands daily reinforcement of technical frameworks, design principles, and system lifecycle processes. A realistic timeline should stretch across several months, where each week is dedicated to a manageable portion of the vast syllabus. This slow but consistent exposure keeps the mind from becoming overwhelmed while ensuring deeper absorption. A candidate who patiently invests time into understanding a single principle in depth will find greater strength in applying it later than one who rushes through entire domains with superficial awareness.
Motivation is also anchored in purpose. When individuals connect their preparation to career aspirations, the effort becomes more meaningful. Someone aspiring to contribute to critical infrastructure defense or national security, for example, will recognize how mastering secure system design is not just about passing an exam but about building resilience for institutions that rely on information systems. With this mindset, study sessions transform from chores into purposeful practice, strengthening resolve for the months ahead.
Designing a Personalized Study Framework
The most productive preparation always begins with structure. A study framework that maps the domains of the exam into smaller, digestible clusters provides clarity and direction. The ISSEP content encompasses diverse areas such as security planning, system development, technical management, and certification processes. Approaching this vast terrain without organization leads to confusion. Instead, candidates should create a roadmap that defines not only what to study but also when to review and reinforce previous learning.
Consistency proves more effective than bursts of intense cramming. A candidate devoting two hours each evening to structured study will, over several months, surpass the progress of someone who attempts to cover entire sections in sporadic weekend marathons. This gradual rhythm mimics the way knowledge embeds itself into long-term memory, making recall far more reliable under the pressure of exam conditions. Allocating time in proportion to the weight of each domain also ensures balance. A domain that carries greater significance in the examination should naturally command more study sessions.
Calendars and trackers are useful companions in this phase. By visualizing the progress week after week, one avoids drifting aimlessly. Setting milestones, such as completing a domain within a specified timeframe or mastering a complex framework within two weeks, creates an environment of steady advancement. Reviewing these goals not only reveals achievements but also highlights areas where additional reinforcement is needed. This combination of foresight and adaptability crafts a study framework that is resilient to distractions and sustainable across the months of preparation.
Immersing in Comprehensive Study Resources
Study materials form the backbone of preparation. Candidates must ensure that their chosen resources are reliable, clear, and sufficiently detailed to cover the depth of concepts expected in the exam. A strong strategy blends multiple forms of content rather than depending on a single book or guide. Text-based resources explain the frameworks in structured language, while digital lectures and recorded sessions bring the content alive with illustrations and spoken clarity. The act of hearing complex ideas explained aloud often stimulates fresh connections that reading alone cannot achieve.
Interactive tools also reinforce retention. Flashcards, whether physical or digital, sharpen recall by challenging the learner to retrieve knowledge actively. This constant retrieval builds memory resilience, which becomes vital in the examination hall when questions appear under strict time constraints. Mobile applications can provide practice questions during moments of idle time, turning even short commutes into productive micro-sessions of study.
Another underrated resource is the study of real-world case studies. By analyzing examples of security projects, whether they involve the development of large-scale systems or the protection of sensitive information, candidates gain contextual understanding. These case studies act as bridges between theory and practice, showing how the abstract principles of secure design materialize in actual environments. With this insight, a candidate is better prepared to answer scenario-driven questions that form the essence of the exam.
Integrating Hands-On Practical Experience
The essence of ISSEP mastery lies in practical application. While reading theory develops awareness, experience in applying those principles cements understanding. Candidates benefit greatly from constructing their own laboratory environments. These virtual labs need not be extravagant; with modest computing resources, one can simulate secure networks, configure system architectures, and conduct controlled risk assessments. The act of performing tasks like system hardening, encryption deployment, or access control implementation transforms passive knowledge into active competence.
Simulated attacks within these labs also sharpen problem-solving abilities. By intentionally creating vulnerabilities and then defending against them, learners see firsthand how theoretical frameworks withstand pressure. This experimentation fosters creativity and resilience, qualities that prove invaluable not just for the exam but for professional responsibilities beyond it.
Engaging in collaborative projects, whether with colleagues or peers also preparing for the exam, adds another dimension to practical learning. Discussing design approaches, debating system trade-offs, and collectively resolving technical dilemmas mirrors the collaborative environment of real-world security engineering. Each such engagement deepens not only technical understanding but also communication skills, which are essential for professionals tasked with aligning security measures to organizational goals.
Hands-on practice further strengthens memory through physical involvement. Concepts that are acted upon, rather than merely read, tend to linger longer in the human mind. This blend of tactile and intellectual engagement produces confidence that endures throughout the exam process.
Mastering the Art of Practice Assessments
Practice tests stand as one of the most powerful tools in the preparation journey. They serve as mirrors, reflecting both the strengths already gained and the weaknesses that require additional effort. A candidate who regularly engages with practice assessments develops familiarity with the rhythm, tone, and complexity of exam-style questions. This familiarity diminishes anxiety because the environment no longer feels alien when sitting for the actual examination.
Full-length practice sessions train stamina. The CISSP-ISSEP exam is not a short engagement; it demands focus across many hours. By simulating this length in advance, candidates prepare their minds to sustain concentration without faltering midway. Shorter sets of questions, on the other hand, allow targeted drilling of specific domains where a candidate feels uncertain. The blend of these two approaches balances both endurance and precision.
The reflective process following each practice test is perhaps even more important than the test itself. When reviewing incorrect answers, the candidate should not merely note the right choice but should investigate the reasoning that led to the mistake. Was it a misunderstanding of the concept, a misreading of the question, or simply a lapse in recall? Identifying the root cause transforms each error into a valuable lesson, ensuring that the same trap is not encountered again.
Repeated exposure to timed questions also cultivates time management. Some questions will inevitably be complex and time-consuming, while others may be straightforward. Learning to navigate these variations ensures that no single difficult item consumes disproportionate time, leaving sufficient opportunity to address the remainder of the test.
Sustaining Motivation and Managing Stress
The long preparation journey brings inevitable periods of fatigue. Sustaining momentum requires deliberate attention to balance. Study sessions should be intense but not endless; intervals of rest allow the mind to recharge. Exercise, nutrition, and sufficient sleep act as silent partners in the preparation process, contributing as much to performance as the hours spent with study materials. A candidate who neglects these essentials may find mental sharpness dulled when it is needed most.
Engagement with others also fortifies motivation. Study groups, whether physical or online, provide a network of accountability and encouragement. Discussing difficult topics with peers reveals new perspectives and reduces feelings of isolation. Celebrating milestones within these groups, such as completing a domain or achieving progress on a practice exam, sustains enthusiasm for the larger goal.
Stress management techniques such as controlled breathing, meditation, or short breaks during study sessions also play a vital role. The brain processes information more efficiently when not burdened by anxiety. A calm mind can navigate complex questions more effectively than one clouded by worry. Candidates should remember that preparation is a marathon, not a sprint, and maintaining equilibrium ensures that energy remains steady until exam day.
Small victories along the way deserve acknowledgment. Completing a challenging reading, mastering a difficult concept, or scoring higher than before on a practice test provides encouragement that fuels continued effort. These celebrations of progress remind candidates that success is being built steadily, day by day.
Reaching Exam-Day Readiness
As the exam approaches, the final stage of preparation involves shifting from learning new material to reinforcing confidence in what has already been mastered. The days leading up to the examination should be spent reviewing summaries, key frameworks, and difficult concepts rather than overwhelming the mind with entirely new topics. Light, consistent revision during this stage is more effective than exhaustive late-night sessions.
Exam-day readiness also extends to practical arrangements. Arriving early, ensuring sufficient rest the night before, and preparing identification documents in advance reduce unnecessary stress. Managing time within the exam itself becomes crucial. Tackling the easier questions first builds momentum and secures early marks, leaving more time for reflection on the challenging scenarios that follow.
A composed mindset on exam day is the culmination of all the months of preparation. Trust in the effort invested, recall the practical applications mastered, and approach each question as an opportunity to apply that knowledge. Instead of perceiving the exam as an intimidating obstacle, it should be approached as the natural extension of the skills developed throughout the preparation journey.
Government and Defense Applications of CISSP-ISSEP
The discipline of security engineering within the sphere of government and defense demands unwavering precision. Every architectural element designed under this umbrella must withstand the scrutiny of national adversaries, espionage attempts, and persistent cyber threats. The CISSP-ISSEP certification proves invaluable here, as it equips professionals with the ability to align theoretical frameworks with real-world, mission-critical demands. An ISSEP-certified professional is expected to design with foresight, ensuring that both offensive and defensive postures are anticipated.
Consider the role of a defense engineer tasked with constructing a secure communication channel for military field operations. This task extends far beyond simply deploying encryption protocols. The design incorporates redundancy to ensure communication persists under duress, integrity checks to prevent tampering, and authentication layers that eliminate the risk of impersonation. Each node in the system becomes an integral guardian of classified intelligence. The ISSEP engineer sees not just the immediate technical challenge, but the broader operational context in which soldiers depend on the unwavering availability of secure connections.
Defense organizations also benefit when ISSEP-trained minds create blueprints for long-term infrastructure. A weapons control network, for instance, cannot tolerate downtime or compromise. With ISSEP principles applied, every line of code and every architectural choice embodies resilience, compartmentalization, and verifiability. Nation-state adversaries often attempt to exploit the smallest oversight, and thus, the ISSEP-certified expert thrives in crafting solutions that withstand the subtlest intrusion attempts. These designs embrace both layered security and adaptive countermeasures, which evolve as threats mature.
The nature of government projects also means that legacy systems must be integrated with emerging innovations. This challenge requires a balance of modernization and continuity. The ISSEP framework prepares professionals to secure decades-old infrastructure while enabling new technologies to coexist safely. In environments where outdated hardware may still control critical resources, the ISSEP-certified engineer provides the bridge between necessity and progress, ensuring that even the most fragile systems are not left vulnerable.
Healthcare Applications of CISSP-ISSEP
Healthcare represents one of the most delicate landscapes for information security. Patient trust, regulatory mandates, and the sanctity of life itself converge in this environment, creating a domain where compromise is unthinkable. The ISSEP-certified professional steps into this world with a mindset that extends far beyond compliance, focusing instead on creating architectures that truly respect the sensitivity of human data.
Electronic health records are a prime example of where secure design principles transform the healthcare ecosystem. An ISSEP-trained specialist might design an architecture where data flows seamlessly between hospitals, clinics, and remote caregivers, while simultaneously guaranteeing confidentiality. This balance requires meticulous application of authentication layers, encrypted storage systems, and finely tuned access privileges. Medical staff need immediate availability, yet malicious actors must never breach the gates. The ISSEP engineer orchestrates this balance with surgical precision.
Beyond records, modern healthcare increasingly relies on telemedicine, wearable devices, and cloud-based diagnostics. Each of these innovations expands the attack surface. A poorly designed telemedicine application could inadvertently expose live consultation sessions or patient images. By embedding ISSEP principles during design, these platforms safeguard privacy without obstructing care. Encryption extends not just to stored data but also to real-time interactions. Audit mechanisms ensure that anomalies are quickly identified, while redundancy guarantees that medical professionals remain connected during emergencies.
The stakes rise further when medical devices themselves—such as pacemakers, insulin pumps, or robotic surgery instruments—connect to digital networks. Compromise in such cases translates directly into physical harm. ISSEP professionals account for these realities by designing embedded controls that operate securely even under the harshest conditions. They ensure that critical commands cannot be overridden, that firmware updates are authenticated, and that external signals cannot manipulate device behavior. In this manner, the ISSEP-certified expert acts as a silent protector of patient well-being.
Financial Sector Applications of CISSP-ISSEP
Financial institutions have always attracted adversaries, yet the digital era has magnified both the sophistication and scale of attacks. Banks, investment firms, and payment platforms are no longer just custodians of money but also stewards of identities, credit histories, and financial reputations. The ISSEP framework prepares security architects to build fortresses where every transaction, from micro-payments to multi-billion-dollar transfers, is shielded by intricate, adaptive defenses.
Imagine a bank preparing to launch a new mobile payment ecosystem. Without a secure foundation, such a platform becomes a magnet for fraudsters, data thieves, and disruptive adversaries. An ISSEP-certified professional crafts the design with multiple protective layers. Transaction monitoring systems watch continuously for anomalies, such as location mismatches or spending behaviors outside expected patterns. Secure APIs form the backbone of integration, ensuring that no rogue process can inject malicious instructions. Encryption safeguards not only user credentials but also every exchange along the payment chain.
Fraud prevention systems designed under ISSEP principles do not merely react; they anticipate. By embedding advanced anomaly detection mechanisms, the system evolves with adversary tactics. Attackers attempting to exploit timing windows, duplicate transactions, or hidden backdoors find themselves consistently repelled by a design that foresees their maneuvers. This foresight is the essence of ISSEP thinking—designing for tomorrow’s threats, not only today’s.
Furthermore, global financial regulations demand compliance at the highest level. From cross-border transfers to anti-money-laundering frameworks, the ISSEP-certified engineer ensures that compliance does not hinder efficiency. Secure workflows are constructed to meet audit requirements automatically, reducing manual oversight while ensuring transparent accountability. In this way, financial institutions thrive by balancing speed, trust, and security simultaneously.
Even investment firms and insurance companies gain protection when ISSEP professionals design systems that defend client portfolios and sensitive actuarial data. By embedding confidentiality and availability into their frameworks, these organizations maintain customer confidence, safeguard reputations, and ensure uninterrupted service despite relentless cyber pressure.
Critical Infrastructure Applications of CISSP-ISSEP
Critical infrastructure embodies the backbone of modern civilization. Power grids, water systems, transportation networks, and communication lines all rely on digital command structures that must never be compromised. The ISSEP-certified professional steps into this environment with an appreciation for its unparalleled significance. A single breach could ripple across cities, states, or even nations.
Take the example of a power grid operator collaborating with an ISSEP-trained engineer. The primary task is securing supervisory control and data acquisition (SCADA) systems. Unlike typical IT infrastructures, SCADA systems control turbines, substations, and power lines in real time. A single malicious instruction could lead to cascading failures. To counteract such threats, the ISSEP engineer introduces layered isolation techniques, ensuring that external networks cannot directly manipulate core controls.
Redundancy is another critical element. By designing resilient architectures, the ISSEP-certified professional ensures that even if one node falters, alternative systems maintain the flow of energy or water. Integrity checks embedded throughout the system confirm that every command is legitimate, every packet authentic, and every transaction accounted for. Adversaries attempting to inject falsified data or disrupt flows encounter barriers meticulously planned long before they strike.
Transportation systems, from rail networks to aviation communication, also benefit from ISSEP-driven design. An attack on these networks could paralyze entire economies. Engineers trained in ISSEP embed mechanisms that preserve operational continuity while isolating anomalies. Safety, availability, and resilience become inseparable goals, ensuring that commuters, goods, and services continue to move without disruption.
What makes critical infrastructure particularly challenging is the long lifespan of its components. Systems designed decades ago must still function, even as digital threats evolve exponentially. The ISSEP-certified engineer bridges this gap, embedding modern safeguards into legacy frameworks. They create hybrid designs where old and new coexist securely, ensuring that society’s most vital services never fall prey to evolving adversaries.
Corporate Applications of CISSP-ISSEP
The corporate world thrives on innovation, competition, and data-driven strategies. Within this arena, information is both an asset and a vulnerability. Intellectual property, customer information, and operational secrets form the lifeblood of enterprises, making them prime targets for industrial espionage and cyber sabotage. ISSEP-certified professionals transform this environment by weaving security into every thread of corporate architecture.
When a global technology company deploys a new cloud platform, the risks are as vast as the opportunities. ISSEP engineers approach the design by embedding secure coding practices at the very inception. Threat modeling exercises identify possible attack vectors long before malicious actors attempt exploitation. Compliance with international data protection laws is not an afterthought but a central pillar of the design. The result is a platform that enables innovation without sacrificing trust.
Corporate mergers and acquisitions also reveal the necessity of ISSEP principles. When two organizations combine, their disparate systems must merge seamlessly. This process often exposes hidden vulnerabilities, legacy flaws, and conflicting architectures. An ISSEP-certified expert orchestrates the integration with security at the forefront, ensuring that the newly formed entity does not inherit dangerous weaknesses.
Beyond the technical, corporate governance benefits as well. ISSEP professionals contribute frameworks where accountability and transparency dominate. Access controls are designed so that employees gain only the privileges necessary for their roles. Audit mechanisms provide executives with real-time insight into system behavior, ensuring informed decision-making. By embedding security into the governance model itself, corporations achieve resilience not only technologically but culturally.
Even startups, though smaller in scale, gain an immense advantage when security engineering becomes foundational. Early investment in ISSEP-driven design spares organizations from costly breaches, regulatory fines, and reputational damage later. By cultivating secure practices from the outset, corporations position themselves for sustainable growth in an environment where digital threats evolve faster than markets themselves.
Engineering Security for Emerging Technologies
The rapid acceleration of technological progress demands that security never lag. Artificial intelligence, quantum computing, and the Internet of Things are reshaping industries at breathtaking speed. Each innovation, however, introduces new vulnerabilities. The ISSEP framework prepares professionals not just to react, but to anticipate.
In artificial intelligence, security concerns extend beyond algorithms to the integrity of training data. A poisoned dataset could lead to corrupted models that misinterpret reality. ISSEP-certified engineers design data pipelines where authenticity is verified at every stage. Audit trails ensure that manipulation attempts are swiftly detected, while cryptographic signatures guarantee dataset integrity.
The Internet of Things expands the attack surface exponentially. Millions of interconnected sensors, appliances, and devices interact daily, often without sufficient safeguards. ISSEP-trained professionals create architectures where every device participates in a secure ecosystem. Authentication mechanisms ensure that rogue devices cannot infiltrate the network, while segmentation limits the spread of compromise if one node is breached.
Quantum computing presents both opportunity and peril. While its power promises revolutionary breakthroughs, it simultaneously threatens to dismantle traditional encryption. ISSEP-certified specialists prepare by embedding post-quantum cryptographic frameworks into modern designs. This foresight ensures that infrastructures today remain resilient against the breakthroughs of tomorrow.
In every emerging technology, the ISSEP mindset views innovation not merely as functionality, but as responsibility. By embedding trust into the foundation of new systems, these professionals guarantee that progress remains sustainable, safe, and universally beneficial.
Long-Term Industry Impacts of ISSEP Expertise
The presence of ISSEP-certified professionals across industries creates ripples that extend far beyond individual projects. Their influence reshapes organizational priorities, elevating security from a technical detail to a strategic imperative. Organizations led by ISSEP frameworks enjoy heightened resilience, stronger reputations, and greater public trust.
Within governments, these professionals safeguard sovereignty by ensuring that national defense structures cannot be dismantled by cyber adversaries. In healthcare, they protect the dignity of patients by keeping their most intimate details inviolable. Financial systems thrive under their guardianship, maintaining the confidence of global economies. Infrastructure remains steady, corporate innovation flourishes, and emerging technologies progress without reckless risk.
Over time, industries guided by ISSEP thinking cultivate cultures where security is not viewed as a barrier but as an enabler. Engineers, executives, and policymakers alike adopt principles that prioritize trust, integrity, and resilience. The ripple effect strengthens societies as a whole, ensuring that as digital dependency deepens, the foundation upon which it rests remains unshakable.
The Expansive Landscape of Information Security Engineering
The world of digital infrastructure grows denser each passing year, with systems woven deeply into every layer of human activity. From energy grids and healthcare facilities to financial institutions and governmental frameworks, every sector leans upon secure information systems. Within this landscape, trust and resilience become paramount. The CISSP-ISSEP certification anchors itself precisely in this domain, granting professionals the mastery to architect, safeguard, and sustain secure environments. Unlike ordinary qualifications, this credential symbolizes a higher degree of immersion into the craft of information security engineering, embedding advanced comprehension of security policies, architectural methodologies, and risk management principles.
While countless certifications exist across the cyber industry, CISSP-ISSEP inhabits a distinguished realm because it goes far beyond validating theoretical knowledge. It carves a pathway toward an immersive understanding of system security life cycles, engineering models, and strategic frameworks that support resilient infrastructures. This creates professionals capable of transforming complex challenges into structured solutions that not only prevent breaches but also build systems designed with long-lasting fortitude.
Earning this credential is not a superficial accomplishment. It is a voyage through rigorous preparation, mental discipline, and deep technical exploration. Those who achieve it emerge not only with sharpened capabilities but with a professional identity that commands respect and recognition. Over time, the influence of such expertise manifests across career trajectories, organizational landscapes, and even within the broader evolution of cybersecurity as a discipline.
Cultivating Advanced Proficiency Through the Certification
Professionals embarking on the CISSP-ISSEP journey cultivate an expanded horizon of technical and strategic skills. The program immerses candidates in frameworks that stretch across the entirety of the system development life cycle. By examining the earliest stages of system design and extending through deployment, operations, and eventual decommissioning, the certification ensures that professionals acquire a panoramic comprehension of security integration.
This level of mastery equips individuals to contribute value regardless of the organizational sector. Energy firms implementing secure grid controls, healthcare institutions managing sensitive patient data, or aerospace agencies designing mission-critical communication systems all require professionals who can implement robust security engineering. The versatility of these acquired skills allows the certified engineer to transcend boundaries and adapt seamlessly across diverse environments.
Another defining feature of this training is its emphasis on aligning security decisions with organizational missions and objectives. Instead of viewing cybersecurity as an isolated technical endeavor, the certification teaches practitioners to contextualize solutions in ways that advance enterprise goals. This union of technical expertise with business alignment elevates the certified individual into a role that extends beyond engineering and ventures into organizational strategy.
Over the long arc of a career, this heightened proficiency proves invaluable. Professionals discover themselves consistently entrusted with responsibilities that carry weight, because their insights interlace both engineering precision and strategic foresight. The capacity to safeguard technology while aligning it with organizational aspirations is what differentiates the ordinary from the extraordinary within this discipline.
Rising Toward Leadership and Professional Advancement
Career progression in the modern era of cybersecurity depends upon more than simply accumulating years of service. Advancement requires demonstrable expertise, trusted competence, and visible dedication to the craft. The CISSP-ISSEP credential catalyzes professionals to rise from mid-level engineering posts to strategic leadership designations.
Titles such as senior systems engineer, enterprise security architect, and chief information security officer do not simply signify status; they signify command over vast domains of responsibility. These positions demand vision, the ability to navigate complexity, and the confidence to make decisions where both technological precision and organizational futures intersect. Employers naturally gravitate toward professionals who hold such a credential, because it signals readiness to assume these pivotal roles.
Moreover, advancement is not limited to hierarchical promotion. The certification often transforms professional influence, granting individuals greater authority in shaping projects, influencing policy development, and guiding multi-disciplinary teams. Whether leading the construction of a secure military communication network or steering the integration of security architecture into a corporate infrastructure, the certified professional enjoys opportunities to direct initiatives of great consequence.
The long-term effect becomes visible through recognition, promotions, and the steady growth of responsibilities. Such advancement is not simply personal gain; it reflects an ongoing trust placed by employers who recognize the rare synthesis of technical mastery and strategic judgment within the certified engineer.
Recognition Across the Global Professional Stage
In an interconnected world, the reputation of a certification depends upon its ability to transcend borders. The CISSP-ISSEP has earned respect across continents, making it a credential that resonates with employers from diverse industries and cultures. Recognition extends beyond the immediate community of information security specialists and reaches decision-makers who govern hiring strategies, project funding, and leadership appointments.
When such a certification appears on a resume, it acts as a signal. Employers do not merely see evidence of technical knowledge; they recognize proof of rigorous preparation, resilience in mastering complex domains, and commitment to professional excellence. This recognition becomes especially crucial in an era when the cybersecurity profession is crowded with a multitude of qualifications of varying credibility.
The global acknowledgment of the CISSP-ISSEP certification empowers professionals to pursue opportunities in regions far from their homeland. A security engineer in Europe may seamlessly transition into a role in Asia, North America, or the Middle East because the credential speaks a universal language of trust and expertise. Over the long arc of a career, this global reputation expands not only professional mobility but also cultural horizons, opening doors to cross-border projects and multinational collaborations.
This recognition also places certified professionals within the higher echelons of trust. Employers, clients, and partners regard them as dependable custodians of complex infrastructures, granting access to projects where failure is not an option. Such trust reinforces the enduring value of the certification, ensuring that its benefits multiply with time.
Gaining a Competitive Edge in the Evolving Job Market
The contemporary job market within cybersecurity is both fertile and fiercely competitive. Opportunities abound, yet employers face the challenge of differentiating between candidates who appear similar on the surface. Within this context, possessing the CISSP-ISSEP credential provides an undeniable advantage. It distinguishes professionals not only by their knowledge but also by their proven dedication to continuous development.
Employers searching for candidates often prioritize those who embody both competence and commitment. The CISSP-ISSEP holder stands apart because their certification indicates months or even years of disciplined preparation, examination of complex frameworks, and demonstrated expertise in security engineering. This separates them from the growing sea of applicants whose qualifications may be limited to entry-level or narrowly focused domains.
Over the span of a career, this competitive edge translates into recurring benefits. Certified professionals encounter fewer obstacles when pursuing roles, negotiate stronger compensation packages, and enjoy greater stability during economic fluctuations. Their rare combination of skill and credibility ensures that they remain valuable even when industries experience contraction or reorganization.
Furthermore, the competitive distinction is not static. It grows deeper with each year, as certified professionals accumulate not only the prestige of the credential but also real-world experiences where their skills produce visible impact. The longer their careers extend, the more their combination of certification and applied achievement strengthens their position against competition.
Expanding Professional Networks and Collaborative Horizons
A subtle yet powerful dimension of the CISSP-ISSEP certification lies in the community it cultivates. Achieving the credential grants access to a fellowship of professionals who share the same dedication, standards, and expertise. This network stretches across industries and nations, offering avenues for collaboration, mentorship, and the exchange of insights.
Networking within this elite circle transcends mere professional acquaintanceship. It becomes an ecosystem of growth, where individuals learn from one another, discover new perspectives, and forge connections that evolve into long-term collaborations. Certified professionals often find themselves invited into special initiatives, research projects, or leadership forums precisely because of the trust inspired by their shared ccrecredentialspractical terms, this network amplifies career possibilities. A professional seeking a new role may find opportunities shared within this community before they appear publicly. Similarly, those aiming to develop specialized knowledge or explore new domains can rely on peers for guidance and mentorship. Such a network is not bound by geography; it functions as a global collective bound by shared achievement and commitment.
The enduring impact of this network grows with time. As careers progress, individuals within the community ascend into higher positions, thereby extending the influence and opportunities available to fellow members. What begins as a certification transforms into a lifelong membership within a global fellowship of trust, expertise, and collaboration.
Remaining Agile in the Face of Evolving Threats
Cybersecurity exists in a realm where constancy is rare. Threats evolve daily, adversaries refine their methods, and technologies emerge with staggering speed. Within this turbulent environment, professionals must remain agile to preserve the integrity of systems. The CISSP-ISSEP certification equips its holders with frameworks and mindsets that emphasize adaptability, foresight, and resilience.
The certification trains individuals not to merely react to threats but to anticipate them. By embedding security at the architectural level of system design, certified professionals construct infrastructures that are not easily undone by adversarial ingenuity. They also understand how to integrate compliance with regulatory requirements and adapt swiftly as new standards arise across industries and governments.
This capacity to remain ahead of adversaries proves essential across the duration of a career. Whereas unprepared professionals risk obsolescence as technology advances, certified engineers maintain relevance by virtue of their training. Their expertise in life-cycle security ensures that as systems evolve, they evolve alongside them, preventing their knowledge from becoming outdated.
The long-term benefit of this adaptability is profound. It secures the employability of certified professionals, sustains their credibility, and ensures they remain at the forefront of the profession. More than mere technical mastery, it cultivates a professional identity that thrives amidst change rather than succumbs to it.
Conclusion
The journey toward earning the CISSP-ISSEP certification is not just about passing an exam. It is about embracing the discipline of information systems security engineering and mastering the skills required to build resilient, trustworthy systems in a world filled with evolving cyber threats.
We began by understanding the foundations of the certification, exploring how it builds upon the CISSP credential and deepens expertise in engineering secure systems. The breakdown of the six domains revealed the balance between theory and application, from systems security engineering foundations to secure operations and change management. Preparation strategies highlighted the importance of structured study, hands-on experience, and practice exams to succeed in this rigorous assessment.
Beyond the exam itself, we examined how CISSP-ISSEP knowledge translates into practical impact across industries such as healthcare, defense, finance, and critical infrastructure. In every scenario, the principles of secure design, risk management, and system life-cycle integration proved invaluable. Finally, we explored the long-term benefits, showing how this credential leads to career advancement, industry recognition, global opportunities, and an enduring competitive edge.
The CISSP-ISSEP certification is more than a credential—it is a statement of commitment, expertise, and leadership. It empowers professionals to not only design systems that function but also safeguard them against the threats of today and tomorrow. For organizations, employing ISSEP-certified practitioners ensures that security is woven into the very fabric of their operations. For individuals, it represents both mastery and opportunity in one of the most critical fields of our time.
The path is demanding, but the reward is a transformation: from being a capable professional to becoming a trusted architect of secure systems that stand resilient in a rapidly changing digital world.
Top ISC Exams
- CISSP - Certified Information Systems Security Professional
- CCSP - Certified Cloud Security Professional (CCSP)
- SSCP - System Security Certified Practitioner (SSCP)
- CISSP-ISSAP - Information Systems Security Architecture Professional
- CISSP-ISSEP - Information Systems Security Engineering Professional
- CSSLP - Certified Secure Software Lifecycle Professional
- CISSP-ISSMP - Information Systems Security Management Professional
- CAP - Certified Authorization Professional