Exam Code: SEC504
Exam Name: Hacker Tools, Techniques, Exploits and Incident Handling
Certification Provider: SANS
Corresponding Certification: Hacker Tools, Techniques, Exploits and Incident Handling
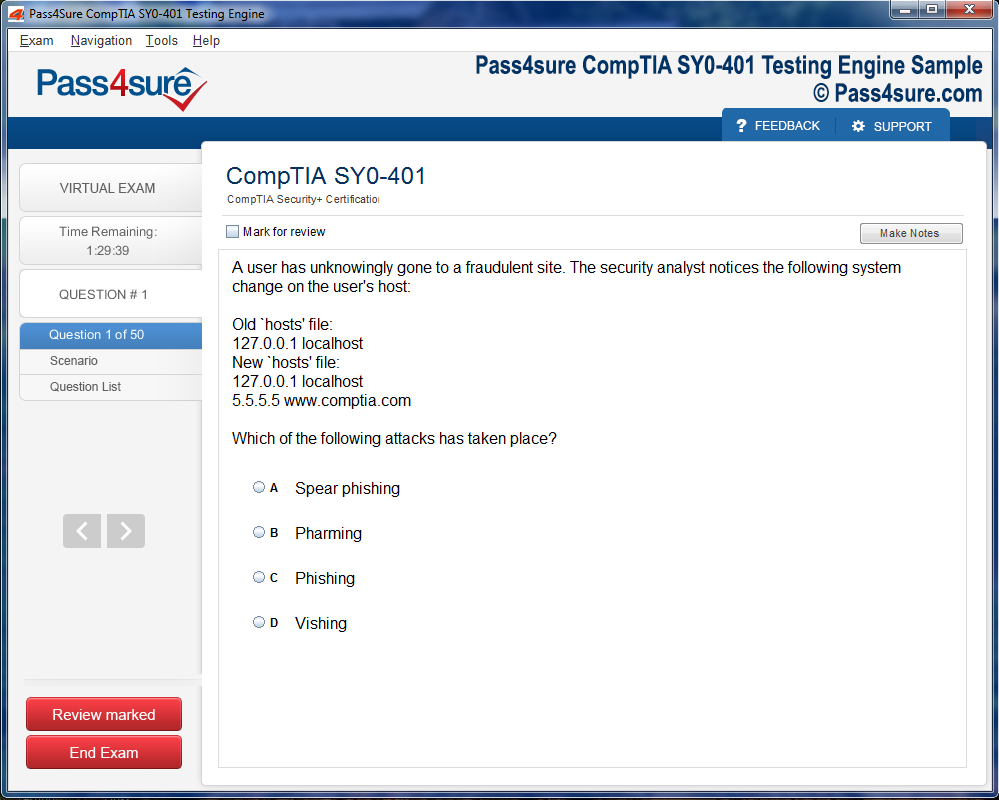
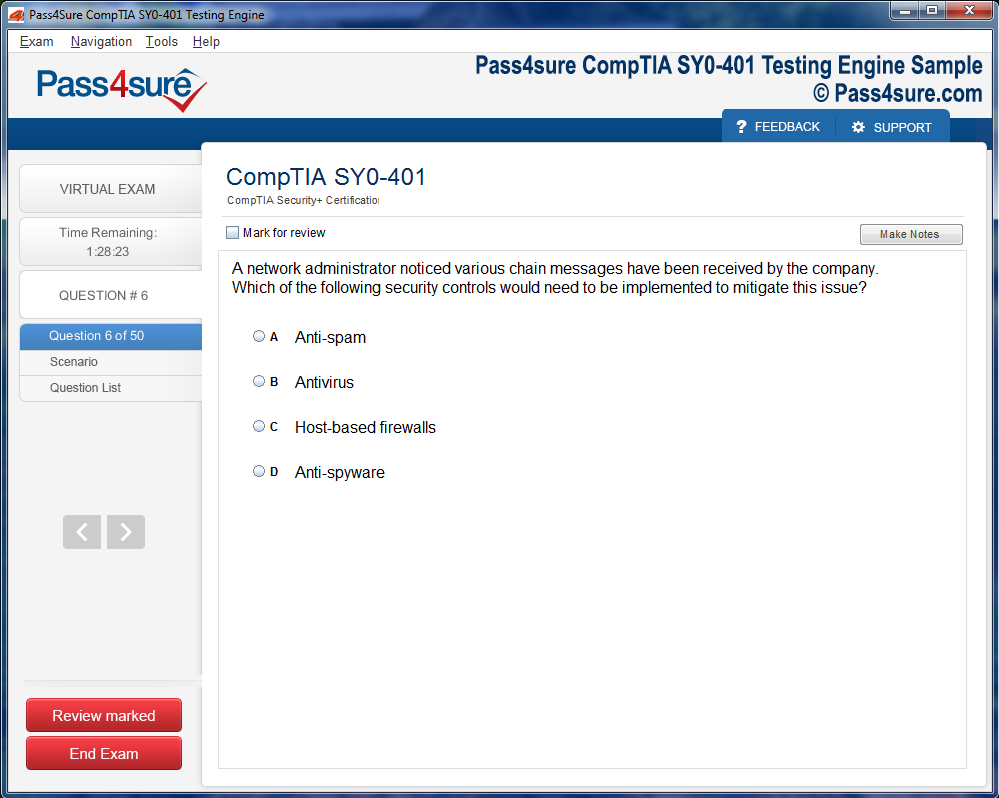
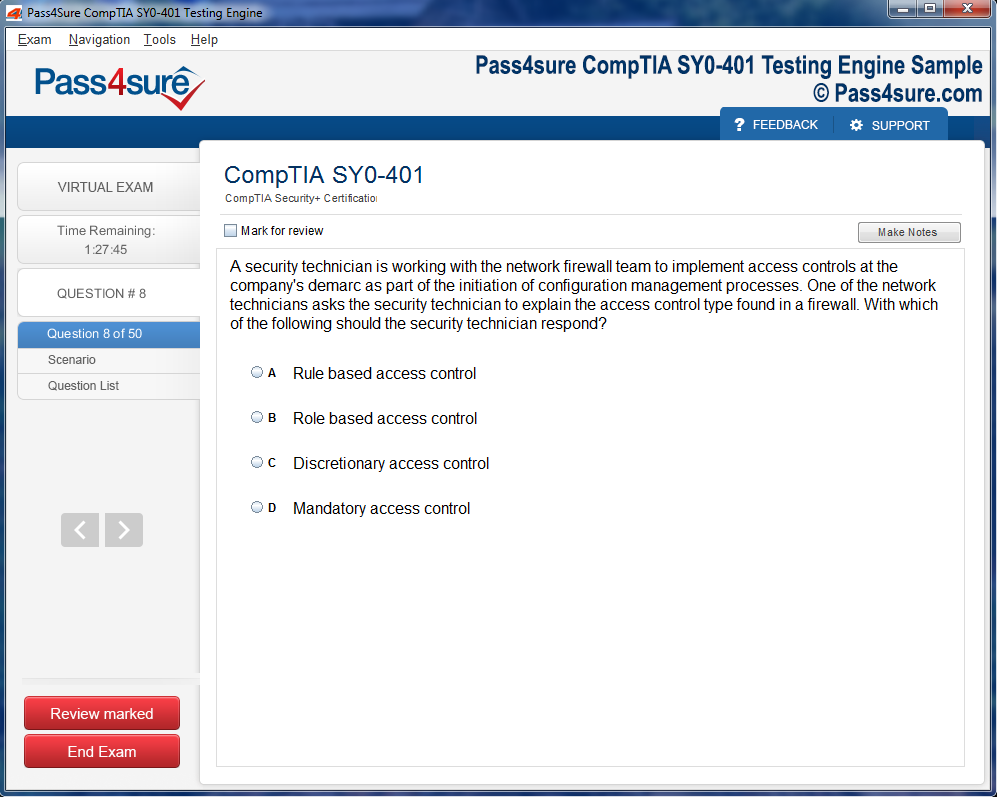
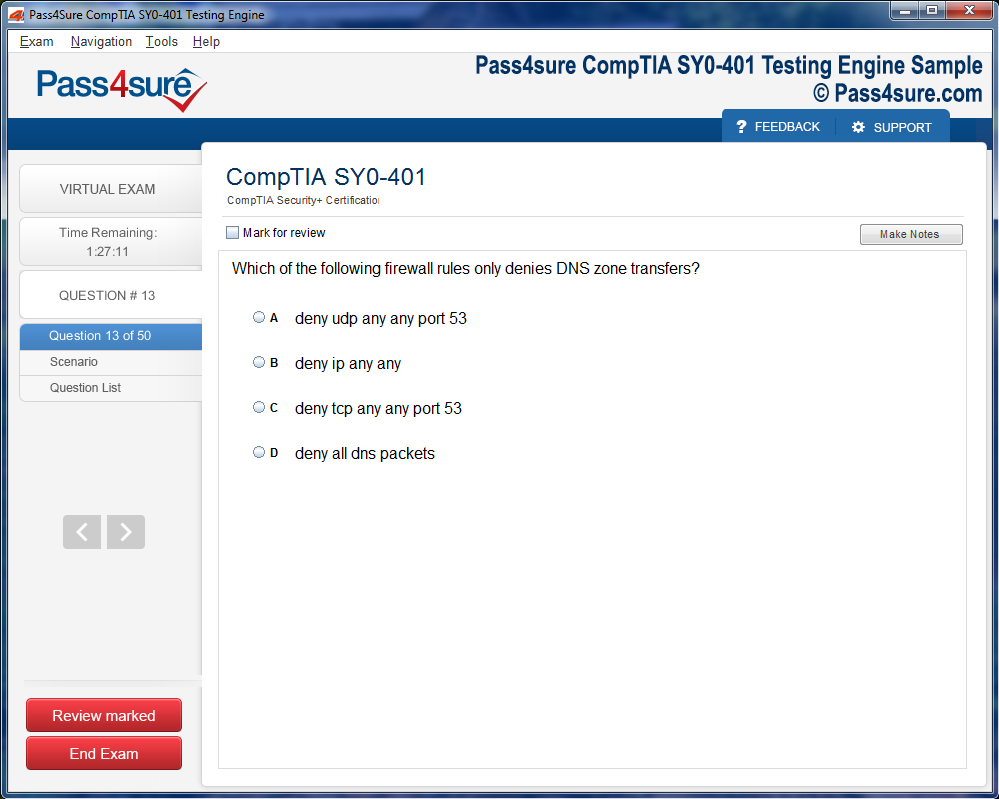
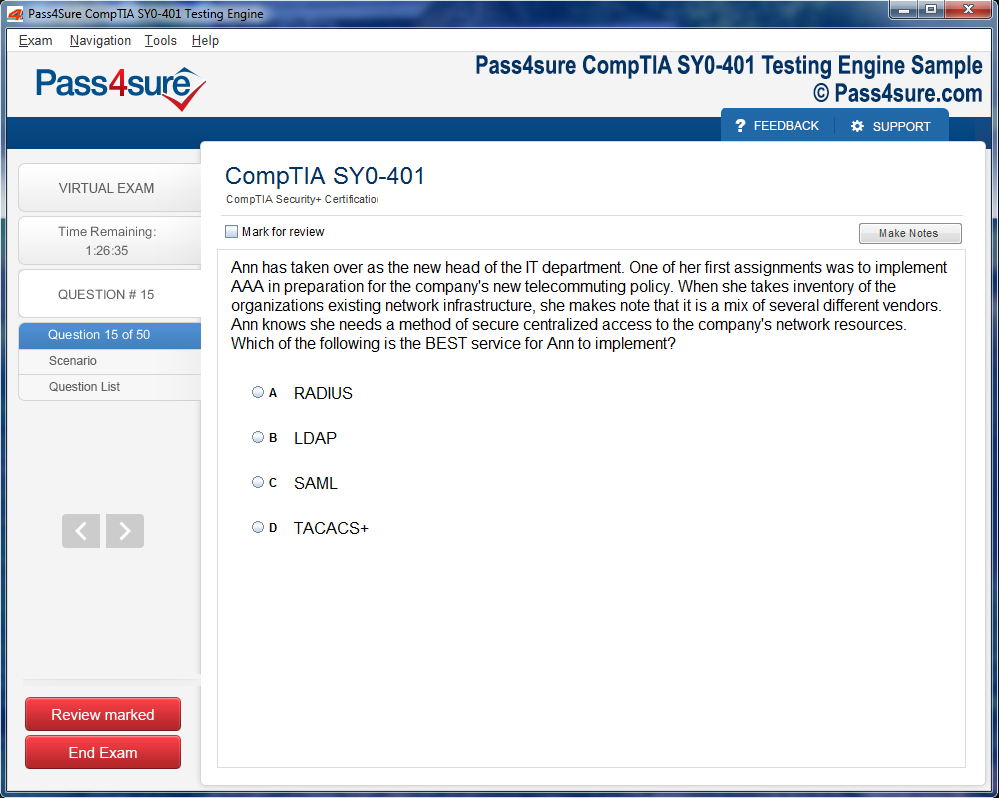
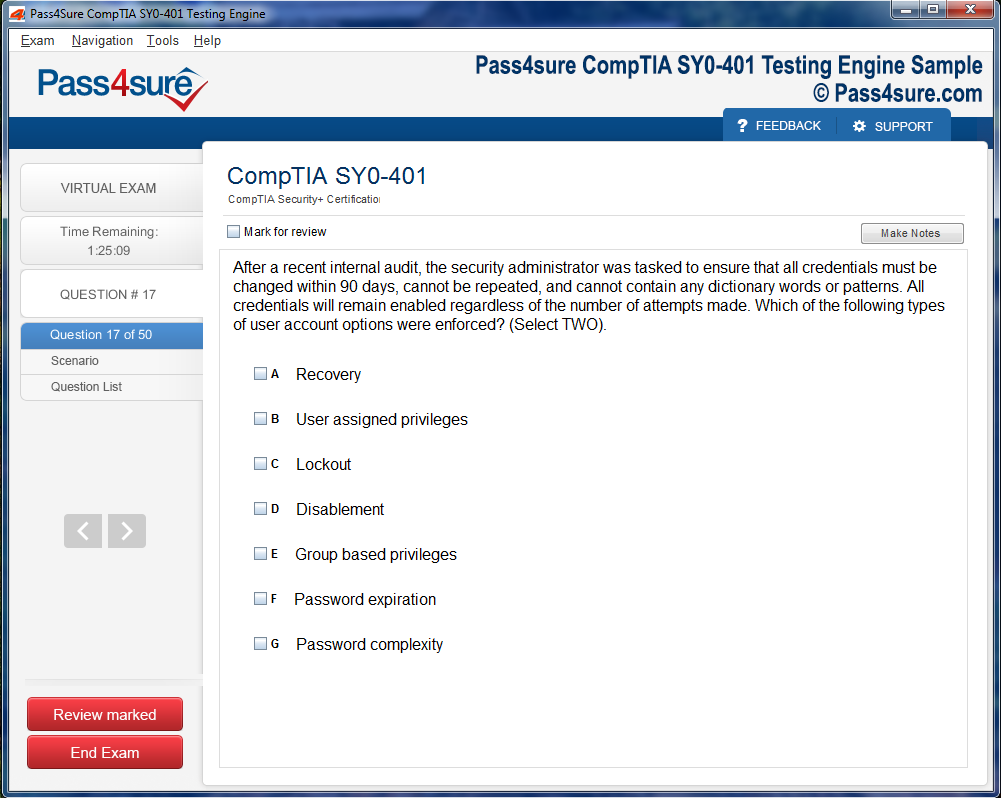
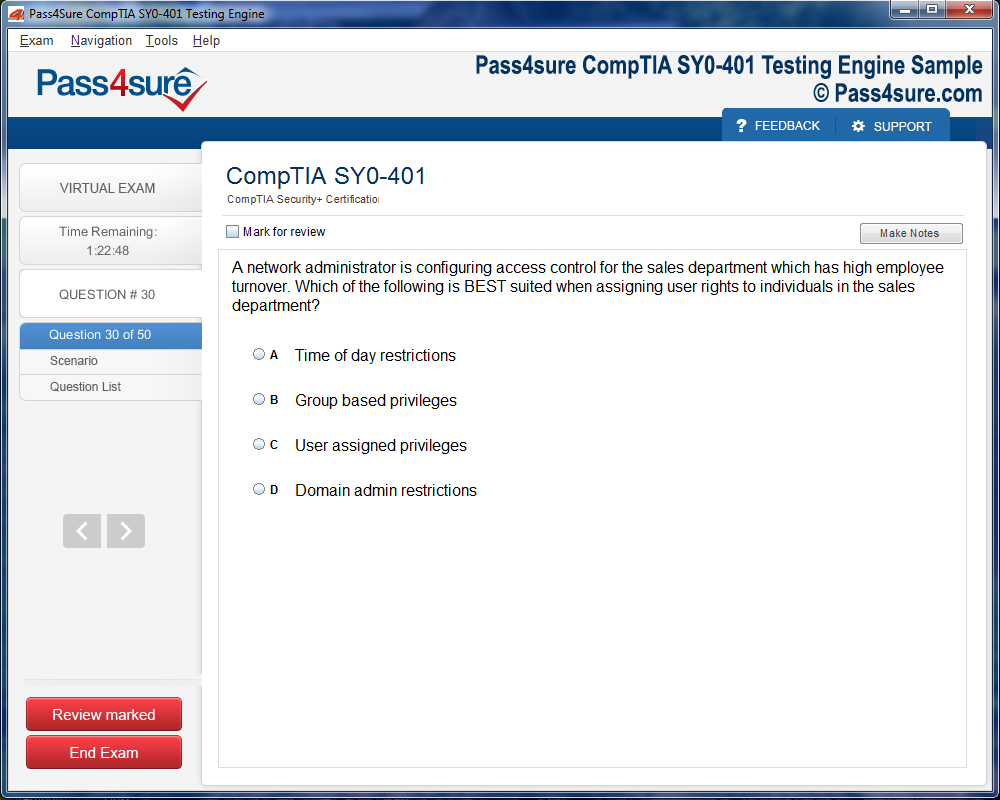
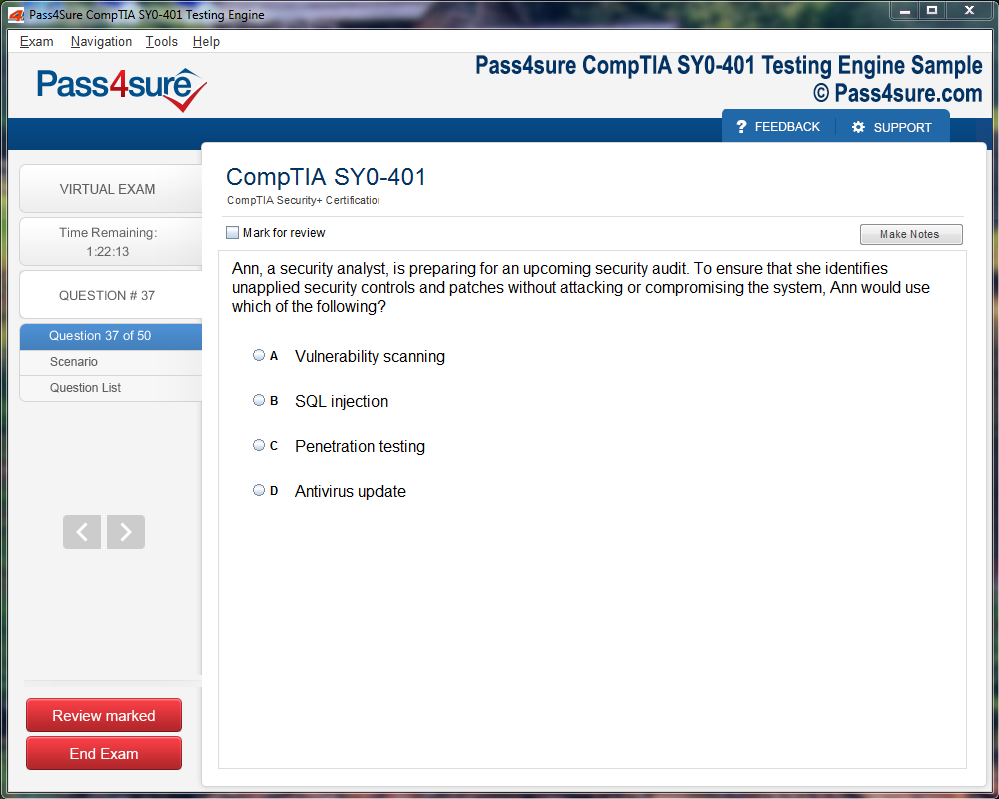
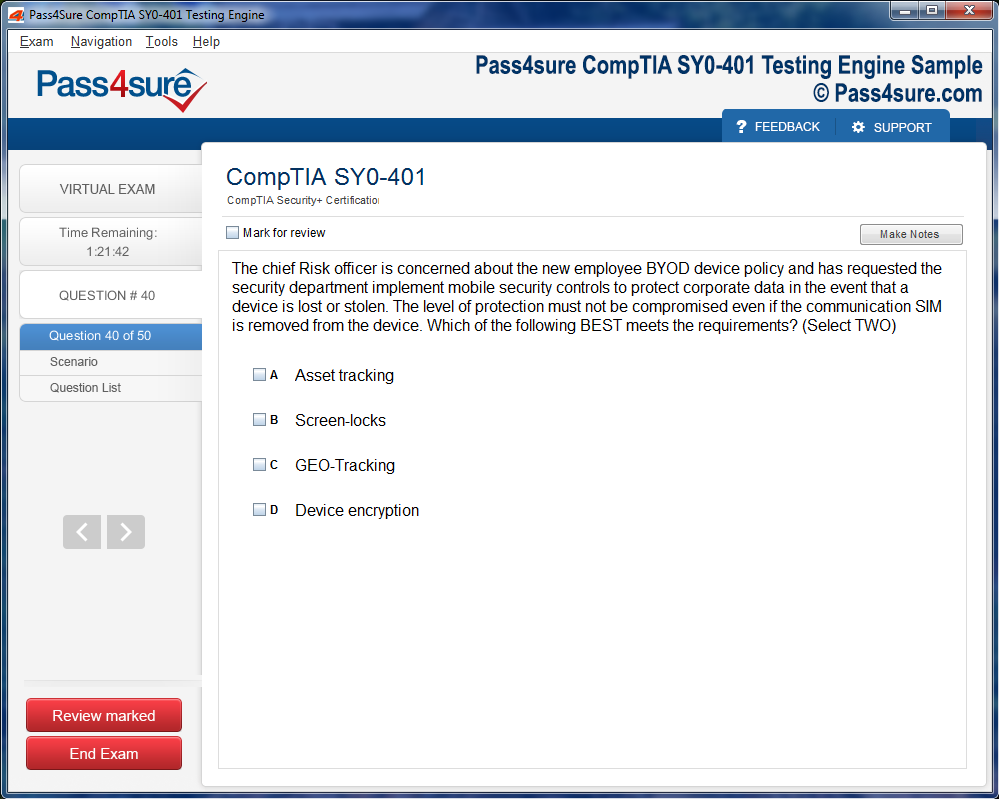
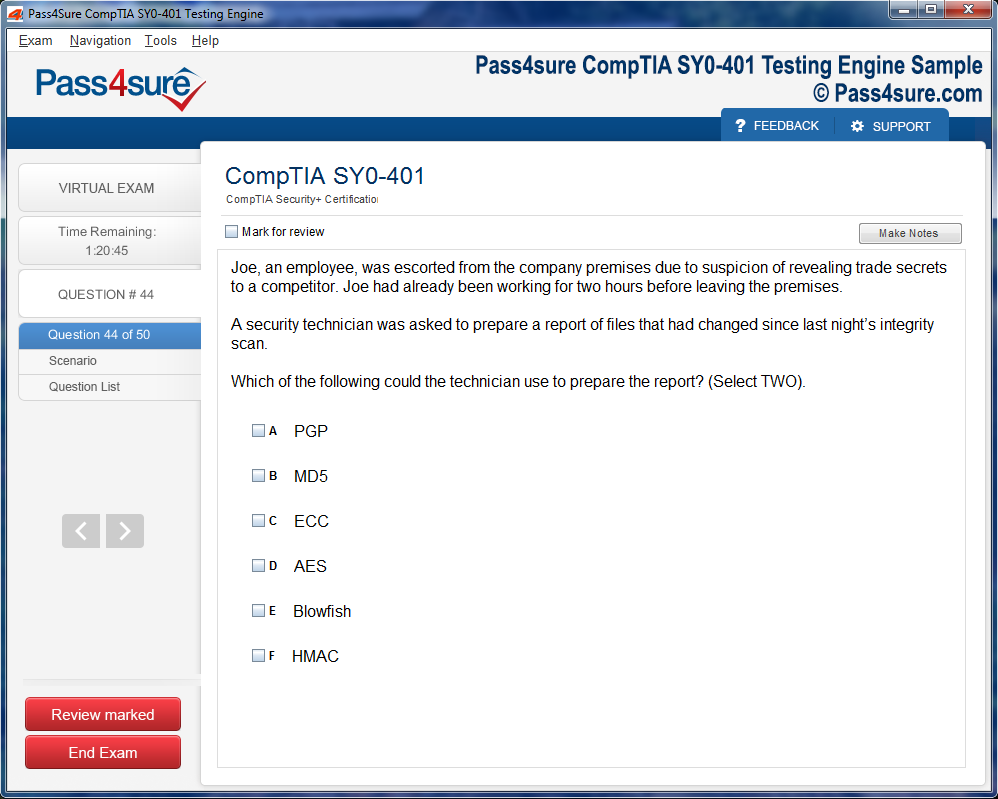
Product Screenshots
Frequently Asked Questions
How does your testing engine works?
Once download and installed on your PC, you can practise test questions, review your questions & answers using two different options 'practice exam' and 'virtual exam'. Virtual Exam - test yourself with exam questions with a time limit, as if you are taking exams in the Prometric or VUE testing centre. Practice exam - review exam questions one by one, see correct answers and explanations.
How can I get the products after purchase?
All products are available for download immediately from your Member's Area. Once you have made the payment, you will be transferred to Member's Area where you can login and download the products you have purchased to your computer.
How long can I use my product? Will it be valid forever?
Pass4sure products have a validity of 90 days from the date of purchase. This means that any updates to the products, including but not limited to new questions, or updates and changes by our editing team, will be automatically downloaded on to computer to make sure that you get latest exam prep materials during those 90 days.
Can I renew my product if when it's expired?
Yes, when the 90 days of your product validity are over, you have the option of renewing your expired products with a 30% discount. This can be done in your Member's Area.
Please note that you will not be able to use the product after it has expired if you don't renew it.
How often are the questions updated?
We always try to provide the latest pool of questions, Updates in the questions depend on the changes in actual pool of questions by different vendors. As soon as we know about the change in the exam question pool we try our best to update the products as fast as possible.
How many computers I can download Pass4sure software on?
You can download the Pass4sure products on the maximum number of 2 (two) computers or devices. If you need to use the software on more than two machines, you can purchase this option separately. Please email sales@pass4sure.com if you need to use more than 5 (five) computers.
What are the system requirements?
Minimum System Requirements:
- Windows XP or newer operating system
- Java Version 8 or newer
- 1+ GHz processor
- 1 GB Ram
- 50 MB available hard disk typically (products may vary)
What operating systems are supported by your Testing Engine software?
Our testing engine is supported by Windows. Andriod and IOS software is currently under development.
Key Facts About SANS SEC504 Every Security Professional Should Know
The SANS SEC504 certification establishes a comprehensive framework for incident handling that security professionals worldwide rely upon. This credential focuses on the systematic approach to detecting, responding to, and recovering from security incidents that threaten organizational assets. The methodology taught through this program emphasizes the importance of preparation, identification, containment, eradication, and recovery phases that form the backbone of effective security operations. Organizations investing in SEC504-certified professionals gain team members who can navigate complex security challenges with confidence and precision.
The structured approach to incident response creates consistency across security teams and enables faster resolution of critical threats. Security professionals who master these methodologies often find themselves better equipped to handle emerging threats and sophisticated attack vectors. The certification content covers real-world scenarios that mirror actual incidents organizations face daily, making the knowledge immediately applicable in production environments. For those seeking to broaden their expertise across multiple domains, exploring resources like a complete guide to MuleSoft developer integration can complement security knowledge with integration skills that enhance overall technical capabilities.
Network Traffic Analysis Capabilities Matter Most
Understanding network traffic patterns represents one of the most valuable skills developed through SANS SEC504 training. Security professionals learn to identify malicious activity hidden within legitimate network communications by analyzing packet captures and flow data. This capability enables defenders to detect advanced persistent threats that evade traditional security controls and operate stealthily within enterprise networks. The ability to read and interpret network protocols gives security analysts a decisive advantage when investigating suspicious activity.
Network analysis skills translate directly into improved threat detection and faster incident response times across organizations of all sizes. The certification program teaches participants how to use industry-standard tools for capturing and analyzing network traffic effectively. These skills become particularly crucial when investigating data exfiltration attempts, command and control communications, and lateral movement activities. Professionals looking to maintain productivity with familiar tools might appreciate insights on how to keep using classic Outlook while managing security-related communications and incident notifications efficiently.
Forensic Techniques Enable Comprehensive Incident Investigation
Digital forensics forms a critical component of the SEC504 curriculum, teaching professionals how to collect and preserve evidence during security incidents. The forensic methodologies covered in this certification ensure that investigators maintain the integrity of evidence while conducting thorough examinations of compromised systems. Participants learn both volatile and non-volatile data collection techniques that preserve critical artifacts before they disappear. This knowledge proves essential when incidents require legal action or detailed post-mortem analysis.
The forensic skills acquired through SEC504 training enable security teams to reconstruct attack timelines and identify the full scope of compromises. Investigators learn to analyze file systems, memory dumps, and system logs to uncover attacker tactics, techniques, and procedures. These capabilities help organizations understand not just what happened, but how attackers achieved their objectives and what vulnerabilities they exploited. Security professionals expanding their knowledge base might find value in reviewing core networking concepts from the 70-741 exam to strengthen their foundational understanding of infrastructure that forensic investigations often examine.
Security Tool Proficiency Accelerates Response Time
Mastery of security tools represents a cornerstone of the SANS SEC504 certification experience. Participants gain hands-on experience with industry-standard software for network monitoring, intrusion detection, malware analysis, and log examination. The certification program emphasizes practical application rather than theoretical knowledge alone, ensuring graduates can immediately contribute to security operations. Tool proficiency reduces the time required to analyze security events and formulate effective response strategies.
Security professionals who develop strong tool skills through SEC504 training become force multipliers within their organizations. The curriculum covers both open-source and commercial security solutions, providing exposure to diverse technology stacks that different organizations employ. This versatility allows certified professionals to adapt quickly to new environments and leverage available resources effectively. For those interested in certification paths that emphasize practical marketing technology skills, the MB-220 guide to Dynamics 365 offers parallel insights into mastering specialized software platforms.
Threat Intelligence Integration Enhances Detection Capabilities
Incorporating threat intelligence into security operations represents a key focus area within the SEC504 certification framework. Security professionals learn how to consume, analyze, and operationalize threat intelligence feeds to improve detection and response capabilities. This knowledge enables teams to proactively hunt for indicators of compromise and anticipate attacker behaviors based on observed trends. Effective threat intelligence integration transforms reactive security postures into proactive defense strategies.
The certification teaches participants how to evaluate threat intelligence sources for relevance and reliability before incorporating them into security workflows. Understanding the threat landscape helps security teams prioritize vulnerabilities and allocate resources to the most critical risks facing their organizations. Analysts learn to correlate internal security events with external threat intelligence to identify sophisticated attacks that might otherwise go unnoticed. Network security specialists considering advanced certifications might explore CCNP Enterprise exam options to complement their incident response skills with deeper networking expertise.
Malware Analysis Fundamentals Reveal Attack Mechanisms
The SEC504 curriculum provides essential malware analysis skills that help security professionals understand how malicious software operates and spreads. Participants learn both static and dynamic analysis techniques to examine suspicious files and identify malicious behaviors safely. This knowledge enables defenders to develop effective countermeasures and prevent similar attacks from succeeding in the future. Understanding malware mechanics helps security teams communicate threats more effectively to stakeholders and technical teams alike.
Malware analysis capabilities developed through this certification allow professionals to reverse-engineer attack tools and understand attacker motivations. The hands-on labs included in SEC504 training provide safe environments where participants can detonate and observe malware without risking production systems. These practical exercises build confidence and competence in handling unknown threats that traditional security controls fail to detect. Those pursuing broader networking credentials might benefit from comprehensive CCNP certification insights that complement security analysis with infrastructure knowledge.
Log Analysis Skills Uncover Hidden Attack Indicators
Effective log analysis stands as one of the most powerful capabilities developed through SANS SEC504 training. Security professionals learn to extract meaningful security events from vast quantities of log data generated by enterprise systems. The certification teaches participants how to correlate events across multiple log sources to identify patterns that indicate security incidents. This skill becomes increasingly valuable as organizations generate exponentially more log data from cloud services, endpoints, and network devices.
Log analysis expertise enables security teams to detect subtle indicators of compromise that attackers deliberately obscure within normal system activity. The SEC504 program covers log formats from various operating systems, applications, and security devices to ensure broad applicability. Participants learn to automate log collection and analysis processes to scale their capabilities beyond manual review. Security professionals interested in collaboration technologies might explore comprehensive knowledge of collaboration platforms to understand how modern communication tools generate logs that require security monitoring.
Practical Hands-On Experience Distinguishes SEC504 Training
The SANS SEC504 certification emphasizes hands-on learning through extensive lab exercises that simulate real-world security incidents. Participants spend significant time working through practical scenarios rather than passively consuming lecture content. This experiential approach ensures that certified professionals can apply their knowledge immediately when returning to their organizations. The labs cover diverse attack scenarios across different platforms and technologies to build versatile response capabilities.
Hands-on training methodology sets SEC504 apart from purely theoretical certification programs and builds muscle memory for critical response procedures. Participants gain experience making decisions under pressure and prioritizing actions when multiple security events demand attention simultaneously. The practical exercises reinforce concepts introduced in course materials and reveal nuances that only emerge through direct experience. Professionals balancing certification preparation with full-time work responsibilities might appreciate time management strategies for CCIE Service Provider exam preparation that apply equally well to SEC504 study schedules.
Cross-Platform Investigation Competencies Address Modern Environments
Modern security incidents rarely confine themselves to a single operating system or platform, making cross-platform investigation skills essential. The SEC504 certification prepares professionals to investigate security incidents across Windows, Linux, and macOS environments effectively. This versatility proves crucial as organizations increasingly adopt heterogeneous technology stacks that include on-premises systems, cloud infrastructure, and mobile devices. Understanding platform-specific artifacts and behaviors enables more thorough investigations regardless of the affected systems.
Cross-platform competencies allow security professionals to follow attacker trails across different systems as adversaries move laterally through networks. The certification covers platform-specific forensic artifacts, log locations, and analysis techniques that vary between operating systems. Participants learn to adapt their investigation methodologies to the unique characteristics of each platform while maintaining consistent evidence collection standards. Those seeking to enhance their professional communication skills might benefit from insights on the critical role of vocabulary enhancement for articulating technical findings to diverse audiences.
Intrusion Detection System Management Strengthens Network Defense
Understanding intrusion detection and prevention systems forms an integral part of the SANS SEC504 curriculum. Security professionals learn to configure, tune, and optimize these systems to detect malicious activity while minimizing false positives. The certification covers signature-based detection, anomaly detection, and behavioral analysis approaches that modern intrusion detection systems employ. Effective IDS management requires balancing sensitivity with specificity to ensure alerts warrant investigation.
The SEC504 program teaches participants how to develop custom detection rules based on threat intelligence and observed attack patterns. Security analysts learn to interpret IDS alerts within the broader context of network activity and correlate them with other security events. This skill enables teams to distinguish genuine threats from benign anomalies and focus resources on legitimate security incidents. Professionals developing written communication skills for security reporting might explore the ultimate guide to IELTS academic writing for strategies that enhance technical documentation clarity.
Memory Forensics Techniques Capture Volatile Evidence
Memory forensics represents an advanced capability taught through SEC504 training that captures evidence existing only in volatile system memory. Security professionals learn to acquire memory dumps from live systems and analyze them for indicators of compromise that never touch disk storage. This technique proves essential for detecting fileless malware, in-memory-only rootkits, and other sophisticated threats that traditional forensic approaches miss. Memory analysis reveals running processes, network connections, and encryption keys that disappear when systems power down.
The certification program covers specialized tools and techniques for extracting meaningful artifacts from memory dumps across different operating systems. Participants learn to identify malicious code injection, hidden processes, and rootkit behaviors that attackers use to maintain persistence while evading detection. Memory forensics skills enable security teams to uncover the full scope of sophisticated attacks that leave minimal traces in traditional forensic evidence. Those documenting security findings might find value in IELTS writing exam demystification strategies that improve technical report writing.
Command Line Proficiency Enables Efficient Analysis
Mastery of command-line interfaces represents a fundamental skill developed throughout the SEC504 certification program. Security professionals learn to navigate and analyze systems using command-line tools that often provide more powerful capabilities than graphical alternatives. The curriculum emphasizes both Windows PowerShell and Linux shell environments to ensure versatility across platforms. Command-line proficiency dramatically accelerates analysis tasks and enables automation of repetitive investigative procedures.
The certification teaches participants how to use command-line tools for file analysis, network diagnostics, process examination, and log parsing effectively. Security analysts who develop strong command-line skills can perform complex tasks with simple scripts that graphical tools cannot accomplish. This capability becomes particularly valuable when investigating compromised systems remotely or analyzing large datasets that would overwhelm graphical applications. Professionals preparing for comprehensive assessments might benefit from how to prepare for IELTS reading techniques that enhance information processing speed.
Security Event Correlation Connects Disparate Attack Indicators
The ability to correlate security events across multiple data sources represents one of the most valuable analytical skills taught through SEC504. Security professionals learn to identify relationships between seemingly unrelated events that collectively indicate a security incident. This capability requires understanding how attackers chain together multiple actions to achieve their objectives and recognizing the artifacts each action generates. Event correlation transforms isolated data points into coherent attack narratives.
The certification program teaches systematic approaches to event correlation that scale from small incidents to enterprise-wide compromises. Participants learn to use timeline analysis, pattern recognition, and statistical methods to identify significant correlations amid enormous volumes of security data. These skills enable security teams to detect multi-stage attacks that unfold over extended periods and involve multiple systems. Technology enthusiasts exploring various fields might appreciate perspectives on deep learning and image recognition that demonstrate parallel pattern recognition challenges.
Packet Analysis Expertise Reveals Network-Layer Attacks
Deep packet analysis skills developed through SEC504 training enable security professionals to examine network communications at the most granular level. Participants learn to decode network protocols, extract payloads, and identify anomalies that indicate malicious activity or policy violations. This expertise proves essential when investigating sophisticated attacks that leverage legitimate protocols to hide malicious traffic. Packet-level visibility reveals details that flow-based analysis and higher-level monitoring tools miss entirely.
The certification covers packet capture techniques, filtering strategies, and analysis methodologies that maximize efficiency when examining large capture files. Security analysts learn to recognize attack signatures within packet data and extract indicators of compromise for threat intelligence purposes. This skill enables defenders to develop precise detection rules and understand exactly how attackers communicate with compromised systems. Those interested in programming foundations might explore line-by-line file reading in Python for automating packet analysis tasks.
Windows Registry Forensics Uncovers Persistence Mechanisms
Understanding Windows Registry forensics represents a specialized skill that SEC504 participants develop for investigating Windows-based incidents. The Windows Registry contains vast amounts of forensic artifacts that reveal user activity, installed software, system configurations, and attacker persistence mechanisms. Security professionals learn which registry keys attackers commonly manipulate and how to identify suspicious modifications that indicate compromise. Registry analysis often reveals malware persistence mechanisms that allow attackers to maintain access across system reboots.
The certification teaches participants how to extract and analyze registry hives from both live systems and forensic images. Analysts learn to identify timestamps, track configuration changes, and uncover evidence of anti-forensic activities that attackers employ. This knowledge proves essential when investigating Windows environments where attackers frequently leverage the registry for persistence and configuration storage. Programmers might find parallel interests in the comma operator in C as an example of understanding system-level details that affect security.
Security Metrics Development Demonstrates Program Effectiveness
The SEC504 curriculum includes guidance on developing meaningful security metrics that demonstrate the effectiveness of incident response programs. Security professionals learn to measure key performance indicators such as detection time, response time, and containment effectiveness. These metrics help organizations quantify security improvements and justify investments in security personnel and technology. Effective metrics also identify areas where incident response processes need refinement or additional resources.
The certification teaches participants how to collect baseline measurements and track trends over time to identify improvements or degradation in security posture. Analysts learn to present metrics in ways that resonate with both technical and executive audiences, ensuring security programs receive appropriate support. Understanding metrics enables security teams to demonstrate their value and advocate for necessary resources based on quantifiable data. Those interested in broader technological impacts might explore the role of technology in everyday life for context on security's place in digital transformation.
Cloud Incident Response Addresses Modern Infrastructure
As organizations migrate to cloud infrastructure, SEC504 training has evolved to address cloud-specific incident response challenges. Security professionals learn how to investigate incidents in environments where they lack direct access to underlying infrastructure. The certification covers cloud-specific artifacts, logging capabilities, and API-based investigation techniques that differ significantly from traditional on-premises approaches. Understanding cloud shared responsibility models proves essential for determining what evidence organizations can access during investigations.
The program teaches participants how to leverage cloud-native security services and logging capabilities to detect and respond to incidents effectively. Analysts learn to work within the constraints and capabilities that major cloud providers offer while maintaining thorough investigation standards. This knowledge becomes increasingly critical as more organizations adopt cloud-first strategies and hybrid environments. Network engineers might appreciate Kubernetes networking core concepts that relate to cloud infrastructure security.
Scripting Automation Multiplies Analyst Effectiveness
The SEC504 certification emphasizes scripting and automation skills that enable security professionals to work more efficiently at scale. Participants learn to automate repetitive analysis tasks, parse large datasets, and extract indicators of compromise programmatically. These skills prove essential in modern security operations where manual analysis cannot keep pace with the volume of security events. Scripting capabilities allow analysts to focus their expertise on complex investigations rather than routine data processing.
The curriculum introduces scripting concepts across multiple languages including Python, PowerShell, and Bash to ensure versatility across different environments. Security professionals learn to develop custom tools tailored to their specific organizational needs and investigation workflows. Automation skills also enable rapid indicator extraction and threat intelligence sharing across security teams and communities. Linux enthusiasts seeking productivity tools might explore must-have Linux apps for power users that complement security analysis workflows.
Certification Path Planning Aligns With Career Goals
The SANS SEC504 certification fits within broader cybersecurity career paths and often serves as a foundation for more advanced security credentials. Security professionals benefit from understanding how SEC504 knowledge complements other certifications like GCIH, GCFA, and GCIA. Strategic certification planning ensures that professionals develop well-rounded skill sets that match their career objectives. Organizations seeking to build comprehensive security teams often look for professionals who pursue complementary certifications strategically.
The certification provides valuable knowledge regardless of whether participants pursue additional SANS credentials or certifications from other providers. Many security professionals use SEC504 as a springboard to specialized roles in incident response, threat hunting, or security architecture. Understanding the certification landscape helps professionals make informed decisions about time and financial investments in continuing education. Career planners comparing certification options might review choosing between LFCS and RHCSA for insights on certification selection strategies.
Continuous Learning Maintains Skills Relevance
The rapidly evolving threat landscape makes continuous learning essential for security professionals who have earned the SEC504 certification. Attackers constantly develop new techniques, tools, and procedures that require defenders to update their knowledge and skills regularly. The certification provides a strong foundation, but maintaining effectiveness requires ongoing engagement with security communities, threat intelligence sources, and emerging technologies. Security professionals who commit to lifelong learning remain valuable assets to their organizations.
The SEC504 certification establishes learning patterns and analytical approaches that professionals can apply to new security challenges throughout their careers. Certified individuals often find that the investigative methodologies transfer effectively to new platforms and attack vectors as technology evolves. Staying current requires reading security research, participating in capture-the-flag exercises, and experimenting with new tools in lab environments. System administrators expanding their skill sets might appreciate a complete guide to killing processes as an example of mastering fundamental operations that support security work.
Vendor Platform Expertise Expands Employment Opportunities
Security professionals who combine SEC504 incident response skills with specific vendor platform expertise significantly increase their marketability to employers. Organizations running enterprise platforms seek analysts who understand both general security principles and platform-specific security considerations. This combined knowledge enables professionals to investigate incidents more effectively because they understand the underlying systems at a deeper level. Platform expertise also helps security analysts recognize normal versus anomalous behavior within specific technology ecosystems.
The ability to apply incident response methodologies to platforms that organizations heavily invest in creates valuable specialization opportunities. Security professionals who develop expertise in platforms like ServiceNow can leverage their incident response knowledge to improve security operations workflows and automation. This combination of skills positions professionals as bridge builders who can translate between security requirements and platform capabilities. Those interested in expanding platform knowledge might explore ServiceNow certification resources that complement security operations expertise.
Human Resources Security Compliance Requires Incident Response Knowledge
The intersection of human resources and security creates unique compliance challenges that benefit from SEC504-level incident response expertise. Organizations must respond to security incidents involving employee data breaches, insider threats, and policy violations while maintaining legal and regulatory compliance. Security professionals who understand both incident response and HR compliance requirements can navigate these sensitive situations more effectively. This knowledge proves particularly valuable when investigating incidents that may result in disciplinary action or legal proceedings.
HR security incidents often require careful evidence handling and chain of custody procedures that align closely with digital forensics training from SEC504. Professionals who can investigate these incidents while protecting employee privacy and meeting legal requirements provide significant value to organizations. The growing importance of data privacy regulations makes this skill combination increasingly relevant across industries. HR professionals seeking security-related credentials might explore SHRM certification options that address security and compliance intersections.
Content Management Platform Security Demands Specialized Response Skills
Organizations relying on content management systems face unique security challenges that require specialized incident response approaches. Security professionals must understand how these platforms store, manage, and deliver content to investigate incidents effectively. Compromised content management systems can result in defaced websites, stolen customer data, and malicious content distribution that damages organizational reputation. SEC504 skills provide the foundation for investigating these incidents while platform-specific knowledge enables thorough analysis.
Content management platform security incidents often involve web application attacks, database compromises, and privilege escalation that require diverse technical skills. Security analysts who combine SEC504 training with platform expertise can identify attack vectors and implement effective remediation strategies. This specialization becomes particularly valuable as organizations increasingly depend on content management systems for customer engagement and digital presence. Those working with specific platforms might review Sitecore certification materials to deepen platform security knowledge.
Quality Management Methodology Integration Improves Security Operations
Applying quality management methodologies to security operations and incident response processes creates measurable improvements in effectiveness and efficiency. Security professionals trained in both SEC504 and quality management approaches can identify process bottlenecks, reduce response times, and eliminate waste in security workflows. This combination of skills enables data-driven improvements to security programs based on rigorous analysis rather than intuition. Organizations benefit from security teams that apply systematic improvement methodologies to their operations.
Quality management principles help security teams establish baseline performance metrics and track improvements over time using statistical methods. These approaches align well with the analytical mindset that SEC504 develops and create cultures of continuous improvement within security organizations. Professionals who bridge security and quality management often find opportunities to lead security operations improvements and transformation initiatives. Those interested in quality methodologies might explore Six Sigma certification pathways that complement security operations roles.
Collaboration Platform Security Monitoring Requires Specialized Knowledge
Modern organizations depend heavily on collaboration platforms that generate massive amounts of security-relevant data requiring specialized monitoring approaches. Security professionals must understand how these platforms authenticate users, manage permissions, and log activities to detect security incidents effectively. Compromised collaboration platforms can expose sensitive communications, enable lateral movement, and facilitate data exfiltration. SEC504 skills provide the analytical foundation while platform-specific knowledge enables effective threat detection and response.
Collaboration platform security incidents often involve account compromises, insider threats, and social engineering attacks that target trusted communication channels. Security analysts who understand both incident response methodologies and platform-specific indicators can identify threats that less knowledgeable analysts might miss. This expertise becomes increasingly valuable as remote work increases organizational dependence on collaboration technologies. Professionals working with specific platforms might consider Slack certification programs to enhance platform security skills.
Programming Language Security Analysis Enhances Code Review Capabilities
Security professionals who combine SEC504 incident response training with programming language expertise can perform more thorough security code reviews and malware analysis. Understanding how specific programming languages work at a detailed level enables analysts to identify vulnerabilities, logic flaws, and malicious code patterns more effectively. This knowledge proves particularly valuable when investigating incidents involving custom malware or exploits targeting organization-specific applications. The ability to read and understand code enhances overall threat analysis capabilities.
Programming knowledge enables security professionals to develop custom analysis tools and automate incident response tasks more effectively. Analysts who understand language-specific security considerations can provide developers with more actionable feedback during security reviews. This combination of skills positions professionals as valuable contributors to both security operations and secure development initiatives. Those interested in specific programming assessments might explore SOL exam preparation resources that develop foundational programming knowledge.
Medical Field Security Compliance Demands Rigorous Incident Response
Healthcare organizations face stringent regulatory requirements that make effective incident response capabilities essential for compliance and patient safety. Security professionals working in healthcare must investigate incidents involving protected health information while meeting HIPAA requirements and maintaining patient privacy. SEC504 training provides the forensic and analytical skills necessary for thorough investigations while healthcare-specific training addresses regulatory considerations. This combination ensures that incident response activities support both security and compliance objectives.
Healthcare security incidents often involve ransomware attacks, insider threats, and medical device compromises that can directly impact patient care. Security professionals must balance rapid response with careful evidence preservation and regulatory reporting requirements. The stakes in healthcare security make thorough training and proven methodologies particularly important. Healthcare security professionals might explore TEAS exam resources to understand healthcare knowledge foundations that inform security practices.
Academic Assessment Security Requires Specialized Protection Approaches
Educational institutions administering high-stakes assessments face unique security challenges that require specialized incident response capabilities. Security professionals must protect assessment integrity while investigating incidents that could compromise test security or student privacy. Attacks on educational assessment systems can undermine institutional credibility and affect student outcomes across large populations. SEC504 skills enable thorough incident investigation while education-specific knowledge addresses the unique characteristics of academic environments.
Assessment security incidents may involve unauthorized access attempts, answer key theft, or distributed denial of service attacks during testing windows. Security analysts must respond quickly to minimize impact on students while preserving evidence for potential legal proceedings. This specialized application of incident response skills creates unique career opportunities in the education sector. Those working in educational assessment security might review THEA examination materials to understand assessment security contexts.
Healthcare Licensing Examination Security Protects Professional Standards
Organizations administering medical licensing examinations bear significant responsibility for maintaining security and integrity of these high-stakes assessments. Security professionals protecting these systems must investigate incidents that could compromise examination security while maintaining the confidentiality of test content and candidate data. The consequences of security failures in this context extend beyond organizational reputation to potentially affect healthcare quality and patient safety. SEC504-trained professionals provide the investigative rigor necessary for these sensitive environments.
Medical licensing examination security incidents require rapid response and thorough investigation to determine whether test content was compromised. Security teams must work closely with examination boards and regulatory bodies while conducting investigations and implementing remediation measures. This specialized field combines cybersecurity expertise with understanding of medical education and professional licensing requirements. Professionals in this space might explore USMLE preparation resources to understand the examination context they protect.
Workforce Readiness Assessment Security Supports Economic Development
Security professionals protecting workforce readiness assessment systems play important roles in economic development and employment programs. These assessments help individuals demonstrate skills to employers and qualify for training programs, making security and integrity essential for stakeholder trust. Incidents affecting these systems can impact individual employment prospects and undermine confidence in workforce development programs. SEC504 training provides the analytical and forensic skills necessary to investigate incidents thoroughly while minimizing impact on assessment participants.
Workforce assessment security incidents may involve unauthorized access, score manipulation attempts, or service disruptions during testing periods. Security teams must balance rapid restoration of services with thorough investigation to prevent recurrence. This application of incident response skills combines cybersecurity expertise with understanding of workforce development and employment program requirements. Those working in workforce assessment security might consider WorkKeys certification resources to understand the assessment context.
Vendor Risk Management Security Analysis Protects Supply Chains
Organizations increasingly recognize that third-party vendors represent significant security risks requiring specialized monitoring and incident response capabilities. Security professionals must investigate incidents involving vendor systems while maintaining business relationships and meeting contractual obligations. SEC504 skills enable thorough analysis of vendor-related incidents while vendor risk management expertise helps navigate the unique challenges of third-party security. This combination proves essential as organizations depend more heavily on external service providers.
Vendor security incidents often involve compromised credentials, data exposure through third-party platforms, or supply chain attacks targeting multiple organizations simultaneously. Security analysts must coordinate incident response across organizational boundaries while protecting sensitive information about internal security controls. This complex environment requires both technical expertise and strong communication skills. Professionals specializing in vendor risk management might explore CIS-VRM certification options that formalize this expertise.
Cloud Service Administrator Responsibilities Include Security Incident Response
Cloud service administrators increasingly face security incident response responsibilities as organizations migrate critical workloads to cloud platforms. These professionals must understand both cloud platform management and security incident investigation to protect organizational assets effectively. SEC504 training provides essential incident response skills while cloud-specific certifications address platform management and security controls. This combination enables administrators to detect, investigate, and respond to security incidents within their areas of responsibility.
Cloud administrator security incidents often involve misconfigurations, compromised credentials, and unauthorized access attempts that exploit cloud-specific attack vectors. Administrators must leverage platform-native security tools and logging capabilities while applying proven incident response methodologies. The shared responsibility model in cloud environments makes clear understanding of administrative duties and security obligations particularly important. Cloud administrators might consider CSA certification programs that address cloud security responsibilities.
Senior Human Resources Professional Security Awareness Enhances Organizational Defense
Senior HR professionals who understand security incident response can significantly strengthen organizational security postures through informed policy development and employee education. These leaders influence security culture through hiring practices, training programs, and policy enforcement that either support or undermine security objectives. SEC504 knowledge helps HR leaders understand security requirements and communicate effectively with security teams during incident response. This cross-functional expertise proves particularly valuable when addressing insider threats and employee-related security incidents.
HR professionals with security knowledge can develop more effective security awareness training that resonates with employees and produces behavioral changes. They better understand the importance of security considerations in hiring, onboarding, and offboarding processes that represent critical security control points. This perspective helps bridge the gap between security requirements and people management in ways that purely technical approaches cannot achieve. Senior HR professionals might explore SHRM-SCP certification resources that include security and risk management components.
Software Development Security Integration Prevents Incidents Proactively
Software developers who understand security incident response can write more secure code and respond more effectively when security issues arise in production systems. SEC504 training provides developers with insight into how security professionals investigate incidents and what evidence proves most valuable during investigations. This knowledge influences design decisions and coding practices in ways that prevent security incidents and facilitate investigation when incidents occur. Organizations benefit significantly when development teams understand security from both preventive and investigative perspectives.
Developer security knowledge enables more productive collaboration between development and security teams during both normal operations and incident response. Developers who understand attack patterns and investigation techniques can implement logging, monitoring, and defensive controls that support security objectives without compromising functionality. This integration of security and development expertise represents a key component of DevSecOps approaches. Developers interested in security might explore NET Developer certification options that address secure coding practices.
Lean Six Sigma Defense Application Optimizes Security Operations
Applying Lean Six Sigma methodologies to security operations creates data-driven improvements in incident detection and response effectiveness. Security professionals trained in both SEC504 and Lean Six Sigma can identify inefficiencies in security workflows and implement process improvements that reduce waste while maintaining thorough investigation standards. This combination of skills proves particularly valuable in large security operations centers where small process improvements create significant cumulative benefits. Organizations gain more efficient security programs that deliver better results with existing resources.
Lean Six Sigma approaches help security teams establish quantifiable performance metrics and systematically improve incident response times and effectiveness. These methodologies align well with the analytical mindset that SEC504 develops and create cultures of continuous improvement within security organizations. Process optimization enables security teams to handle increasing workloads without proportional staff increases. Security professionals interested in process improvement might consider LDFSS certification programs that formalize Lean Six Sigma expertise.
Lean Six Sigma Black Belt Security Process Mastery Transforms Operations
Security operations leaders who achieve Lean Six Sigma Black Belt certification alongside SEC504 credentials can drive transformative improvements in incident response effectiveness. Black Belt methodology enables comprehensive analysis of security processes and implementation of statistical process control that measurably improves outcomes. This advanced process expertise allows security leaders to redesign workflows, eliminate bottlenecks, and optimize resource allocation across security operations. Organizations benefit from security programs that continuously improve through data-driven decision making.
Black Belt-level process expertise proves particularly valuable when scaling security operations to meet growing organizational needs without proportional budget increases. Security leaders can quantify the impact of process improvements and demonstrate return on investment to executive stakeholders. This combination of technical security knowledge and process optimization skills positions professionals for senior leadership roles. Those pursuing advanced process improvement credentials might explore LSSBB certification pathways that develop Black Belt competencies.
Lean Six Sigma Green Belt Security Application Drives Tactical Improvements
Security analysts who earn Green Belt certification complement their SEC504 incident response skills with process improvement capabilities that enhance daily operations. Green Belt methodology provides structured approaches to identifying and solving security operations problems that impact efficiency and effectiveness. This intermediate level of process expertise enables analysts to lead improvement projects while continuing to perform incident response duties. Organizations benefit from security team members who identify opportunities for improvement and implement solutions systematically.
Green Belt training develops skills in statistical analysis, root cause identification, and solution validation that align naturally with security investigation work. Analysts can apply these methodologies to reduce false positive rates, streamline investigation procedures, and improve collaboration between security and other teams. This combination creates versatile professionals who contribute beyond individual investigations to program-level improvements. Security analysts interested in process improvement might consider LSSGB certification options that formalize Green Belt expertise.
Lean Six Sigma Master Black Belt Security Leadership Enables Enterprise Transformation
Security executives who achieve Master Black Belt certification bring the highest level of process expertise to enterprise security strategy and operations. Master Black Belt capability enables security leaders to mentor others, design comprehensive process improvement programs, and align security operations with organizational objectives through measurable metrics. This advanced expertise proves essential when transforming security programs to meet evolving business needs and threat landscapes. Organizations gain security leadership that speaks the language of business improvement and demonstrates value quantitatively.
Master Black Belt methodology enables security executives to optimize entire security programs rather than individual processes or functions. These leaders can evaluate trade-offs between competing security investments based on rigorous analysis and predictable outcomes. The combination of security expertise and advanced process mastery positions professionals for executive leadership roles that shape organizational strategy. Those pursuing the highest levels of process expertise might explore LSSMBB certification pathways that develop Master Black Belt capabilities.
Lean Six Sigma White Belt Security Awareness Builds Foundation
Security professionals beginning their process improvement journey can leverage White Belt knowledge to understand how systematic improvement methodologies apply to security operations. White Belt provides foundational concepts that help analysts recognize inefficiencies and participate effectively in improvement initiatives. This entry-level process knowledge complements SEC504 training by introducing structured problem-solving approaches that enhance incident response effectiveness. Organizations benefit when entire security teams share common process improvement language and mindsets.
White Belt training helps security professionals understand how their individual contributions fit within larger process improvement initiatives. Analysts learn to document processes, identify waste, and suggest improvements based on data rather than intuition. This foundation supports collaboration with process improvement specialists and participation in cross-functional improvement projects. Security professionals exploring process improvement might start with LSSWB certification resources that introduce foundational concepts.
Lean Six Sigma Yellow Belt Security Participation Supports Team Improvements
Security analysts who earn Yellow Belt certification develop intermediate process improvement skills that enable meaningful participation in security operations enhancement projects. Yellow Belt knowledge provides practical tools for process mapping, data collection, and problem analysis that complement incident response capabilities. This level of process expertise enables analysts to contribute to improvement initiatives while continuing to focus primarily on security investigations. Organizations benefit from security teams where multiple members can identify opportunities and implement tactical improvements.
Yellow Belt training develops skills that help security analysts recognize patterns in security data and propose solutions based on statistical analysis. These capabilities enhance both individual investigation work and contribution to team-level process improvements. The combination creates more versatile professionals who add value beyond responding to individual incidents. Security professionals interested in practical process improvement might explore LSSYB certification programs that develop Yellow Belt competencies.
Six Sigma Black Belt Security Expertise Delivers Strategic Value
Security leaders combining SEC504 incident response knowledge with Six Sigma Black Belt certification can drive significant improvements in security program effectiveness and efficiency. Black Belt methodology provides rigorous analytical frameworks for identifying root causes of security issues and implementing lasting solutions. This expertise enables security leaders to transform reactive incident response into proactive security posture improvements based on incident pattern analysis. Organizations gain security programs that learn from incidents and systematically reduce risk over time.
Black Belt-level expertise proves particularly valuable when justifying security investments to executive leadership through quantifiable business impact. Security leaders can demonstrate return on investment and predicted outcomes using statistical models that business executives understand and trust. This ability to speak the language of business improvement while maintaining deep technical security knowledge positions professionals for executive roles. Those pursuing Black Belt credentials might consider SSBB certification pathways that formalize this expertise.
Six Sigma Green Belt Security Skills Enable Practical Improvements
Security analysts who combine SEC504 training with Six Sigma Green Belt certification gain practical tools for improving security operations efficiency and effectiveness. Green Belt methodology provides structured approaches to analyzing security processes and implementing measurable improvements. This intermediate level of process expertise enables analysts to lead focused improvement projects while maintaining incident response responsibilities. Organizations benefit from security professionals who continuously seek ways to work smarter rather than simply working harder.
Green Belt skills help security analysts identify and eliminate sources of wasted effort in investigation workflows and reduce time spent on low-value activities. These improvements free up capacity for more sophisticated threat hunting and proactive security activities. The combination of investigation skills and process improvement methodology creates professionals who deliver compounding value over time. Security analysts interested in Green Belt certification might explore SSGB programs that develop these capabilities.
Six Sigma White Belt Security Foundation Introduces Process Thinking
Security professionals new to process improvement can build foundations through White Belt training that complements their SEC504 incident response expertise. White Belt knowledge introduces basic concepts of variation, waste identification, and data-driven decision making that apply directly to security operations. This foundational understanding helps analysts participate effectively in improvement initiatives and recognize opportunities for operational enhancement. Organizations benefit when entire security teams share basic process improvement vocabulary and concepts.
White Belt training helps security analysts understand how systematic improvement methodologies can enhance security program effectiveness. Analysts learn to think about their work as processes that can be measured and improved rather than simply responding to incidents reactively. This mindset shift supports long-term career development and organizational security maturity. Security professionals beginning process improvement journeys might start with SSWB resources that introduce foundational concepts.
Six Sigma Yellow Belt Security Application Enables Contribution
Security analysts earning Yellow Belt certification develop intermediate skills that enable meaningful participation in security operations improvement projects. Yellow Belt methodology provides practical tools that complement SEC504 investigation skills and enable analysts to contribute to process enhancements. This level of expertise allows security professionals to identify improvement opportunities and support implementation while maintaining focus on incident response duties. Organizations benefit from security teams where multiple members actively seek and implement incremental improvements.
Yellow Belt training develops analytical and problem-solving skills that enhance both individual investigation effectiveness and team-level process improvements. Analysts learn to use data to identify patterns and validate that proposed solutions actually improve outcomes. This evidence-based approach aligns well with the analytical mindset developed through security investigation work. Security professionals seeking practical process improvement skills might explore SSYB certification options that develop Yellow Belt competencies.
Collaboration Platform Administration Security Requires Specialized Skills
Administrators managing collaboration platforms face significant security responsibilities that require both platform expertise and incident response capabilities. SEC504 training provides essential investigation skills while platform-specific certifications address configuration, monitoring, and security controls. This combination enables administrators to detect security incidents early and respond effectively before significant damage occurs. Organizations depend on administrators who understand both platform capabilities and security principles to maintain secure collaboration environments.
Collaboration platform administrators must balance security requirements with usability to ensure that security controls do not prevent legitimate business activities. This requires deep understanding of how users interact with platforms and what security risks different usage patterns create. Administrators who combine technical platform skills with security investigation capabilities provide significant value to organizations. Those managing specific platforms might pursue Slack Certified Admin credentials that formalize platform expertise.
Content Delivery Platform Security Demands Comprehensive Protection
Security professionals protecting content delivery platforms must understand both application security and network security to investigate incidents effectively. SEC504 training provides analytical and forensic skills while platform-specific knowledge addresses unique security challenges of content delivery systems. This combination proves essential when investigating incidents involving website defacement, malicious content injection, or data breaches through content management vulnerabilities. Organizations rely on security professionals who understand both attack vectors and platform-specific defensive capabilities.
Content delivery platform security incidents often involve multiple attack vectors including web application exploits, database compromises, and social engineering of administrative users. Security analysts must investigate across these domains while maintaining service availability for legitimate users. The complexity of these environments requires both broad security knowledge and deep platform expertise. Professionals working with specific platforms might explore S10-110 certification resources that develop platform security skills.
Advanced Content Platform Security Requires Deep Technical Knowledge
Senior security professionals protecting advanced content platforms need comprehensive skills that span application security, infrastructure security, and incident response. SEC504 provides investigation methodologies while platform-specific advanced certifications address complex security configurations and threat scenarios. This expertise enables security professionals to design defensive architectures and respond to sophisticated attacks targeting content delivery systems. Organizations benefit from security specialists who understand both the business value and security risks of content platforms.
Advanced content platform security requires understanding complex distributed systems, caching mechanisms, and content delivery networks that create unique attack surfaces. Security professionals must investigate incidents that span multiple infrastructure components while maintaining attribution and evidence integrity. This specialized knowledge creates career opportunities for security professionals who develop deep expertise in specific platform families. Those pursuing advanced platform security skills might consider S10-210 certification pathways that address complex scenarios.
Cloud Data Platform Advanced Administration Combines Security and Operations
Advanced administrators managing cloud data platforms require both operational expertise and security investigation capabilities to protect organizational data effectively. SEC504 training provides incident response skills while platform-specific advanced certifications address complex configurations and security controls. This combination enables administrators to detect and respond to security incidents while maintaining the availability and performance that organizations depend upon. Cloud data platforms represent critical infrastructure that requires specialized security knowledge.
Cloud data platform security incidents often involve unauthorized access attempts, data exfiltration, or misconfigurations that expose sensitive information. Advanced administrators must leverage platform-native security capabilities while applying proven investigation methodologies to determine incident scope and impact. This expertise becomes increasingly valuable as organizations migrate critical data workloads to cloud platforms. Administrators pursuing advanced skills might explore SnowPro Advanced Administrator certifications that formalize expertise.
Cloud Architecture Security Design Prevents Incidents Proactively
Cloud architects who understand security incident response can design platforms that both prevent security incidents and facilitate effective investigation when incidents occur. SEC504 knowledge provides architects with insight into what evidence proves valuable during investigations and what security controls prevent common attack vectors. This perspective influences architectural decisions in ways that improve overall security posture. Organizations benefit significantly from architects who design security into cloud platforms rather than adding it as an afterthought.
Security-aware cloud architecture includes comprehensive logging, network segmentation, and access controls that both reduce attack surface and preserve evidence for investigations. Architects who understand incident response requirements can design systems that balance security, performance, and cost effectively. This expertise positions professionals for senior technical roles that shape organizational cloud strategy. Cloud architects might pursue SnowPro Advanced Architect credentials that include security design components.
Cloud Data Engineering Security Integration Protects Information Pipelines
Data engineers who understand security investigation can design data pipelines that protect sensitive information while facilitating business intelligence and analytics. SEC504 training provides engineers with insight into how attackers target data systems and what evidence helps investigators track unauthorized access. This knowledge influences design decisions around encryption, access controls, and audit logging that protect data throughout its lifecycle. Organizations benefit from data engineering teams that integrate security into pipeline design from the beginning.
Secure data engineering requires understanding both technical security controls and compliance requirements that govern data handling in various industries. Engineers who combine SEC504 knowledge with platform expertise can implement solutions that meet both business and security requirements effectively. This capability proves particularly valuable in regulated industries where data protection carries legal and financial consequences. Data engineers might explore SnowPro Advanced Data Engineer certifications that address security considerations.
Conclusion
The SANS SEC504 certification represents far more than a credential on a resume; it establishes foundational incident response capabilities that security professionals build upon throughout their entire careers. The comprehensive coverage of detection methodologies, forensic techniques, malware analysis, and network traffic analysis creates versatile professionals capable of investigating diverse security incidents across multiple platforms and technologies. Organizations investing in SEC504-trained security professionals gain team members who can respond effectively to incidents while continuously improving security operations through learned analytical approaches and systematic thinking.
The certification's emphasis on hands-on learning through practical lab exercises ensures that graduates can immediately apply their knowledge in production environments without extended transition periods. This practical orientation distinguishes SEC504 from purely theoretical programs and builds the confidence necessary for security professionals to make critical decisions under pressure during active incidents. The real-world scenarios covered in training mirror actual incidents that organizations face, making the knowledge directly applicable rather than academic. Security teams incorporating SEC504-certified professionals benefit from standardized investigation approaches and consistent quality in incident response activities.
Beyond individual skill development, SEC504 training creates common language and frameworks that enhance collaboration within security teams and across organizational boundaries. When multiple team members share SEC504 foundations, they can communicate more efficiently during incident response and build upon each other's analyses without extensive explanation. This shared foundation accelerates incident response and reduces the likelihood of miscommunication during high-pressure situations. Organizations where security professionals pursue complementary certifications gain additional benefits as team members bring diverse specialized knowledge while maintaining SEC504 as a common baseline.
The career impact of SEC504 certification extends well beyond incident response specialist roles to influence security architects, cloud engineers, compliance professionals, and technology leaders across industries. The analytical skills and systematic investigation methodologies transfer effectively to security program design, risk assessment, and strategic planning activities that senior security professionals undertake. Professionals who combine SEC504 with specialized certifications in specific technologies, platforms, or methodologies create unique value propositions that distinguish them in competitive job markets. The certification serves as a springboard for career advancement into specialized technical roles or management positions that require both technical depth and broad security knowledge.
Looking forward, the fundamental skills taught through SEC504 remain relevant even as specific technologies and attack techniques evolve. The core principles of systematic investigation, evidence preservation, log analysis, and network traffic examination apply across technology generations and platform changes. Security professionals who master these fundamentals can adapt to new tools, platforms, and attack vectors throughout their careers by applying proven methodologies to novel situations. This adaptability proves essential in cybersecurity where the only constant is change and where yesterday's defensive approaches may prove insufficient for tomorrow's threats.
Organizations evaluating security training investments should recognize that SEC504 certification creates compounding value over time as certified professionals apply their knowledge to improve security processes, mentor colleagues, and influence organizational security culture. The return on investment extends beyond improved incident response capabilities to include better security architecture decisions, more effective security tool deployment, and stronger collaboration between security and other technical teams. Security professionals who pursue SEC504 training position themselves as valuable contributors to organizational security regardless of how their specific roles evolve throughout their careers.