Exam Code: ITIL 4 Practitioner Deployment Management
Exam Name: ITIL 4 Practitioner Deployment Management
Certification Provider: ITIL
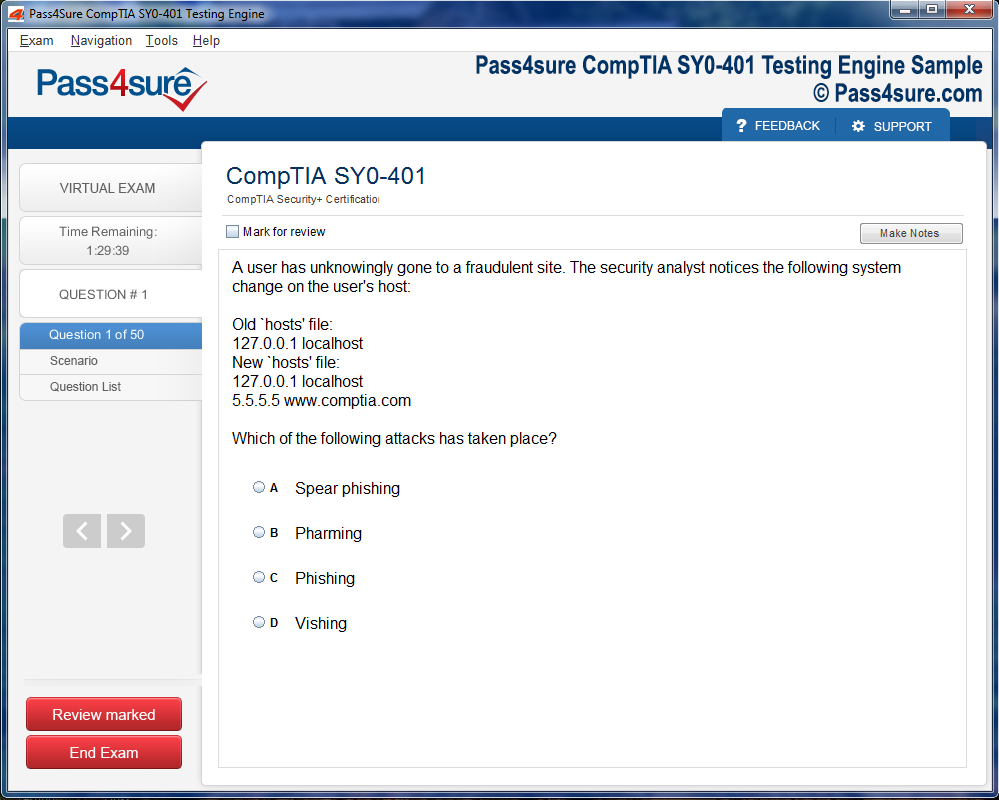
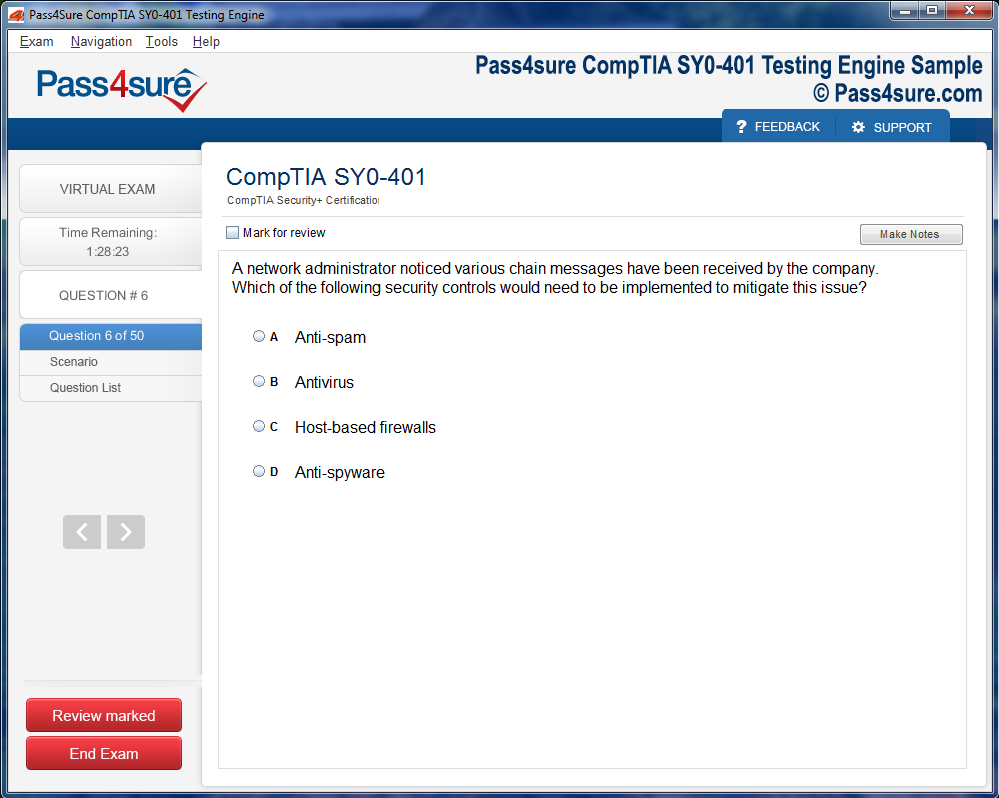
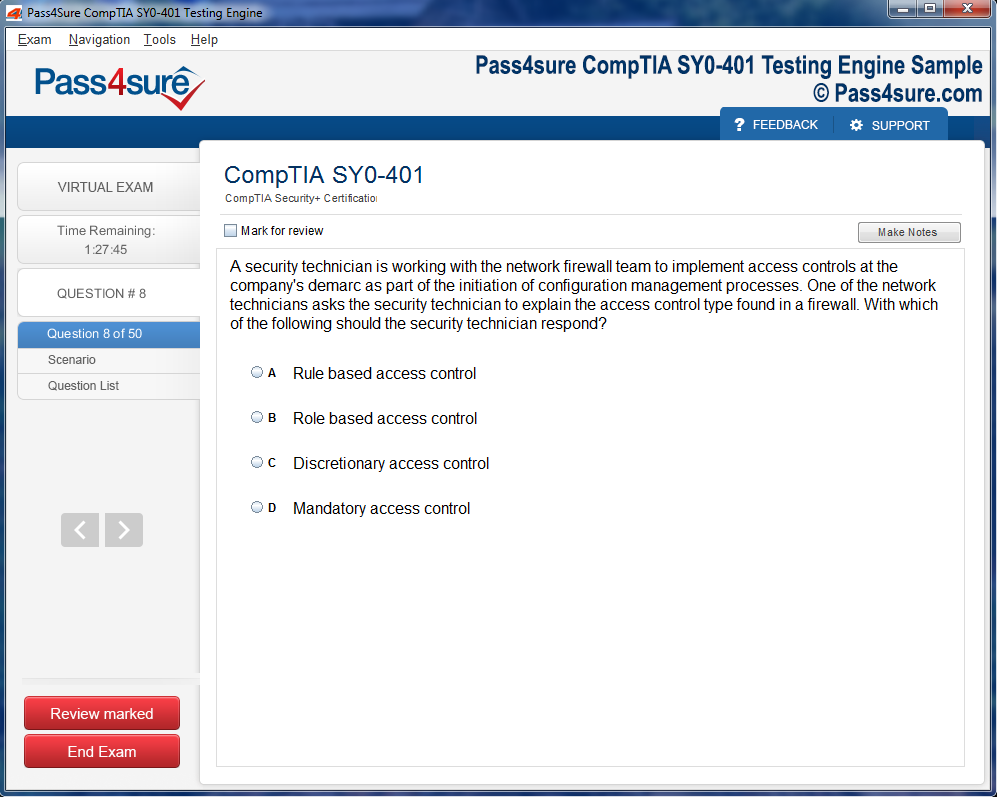
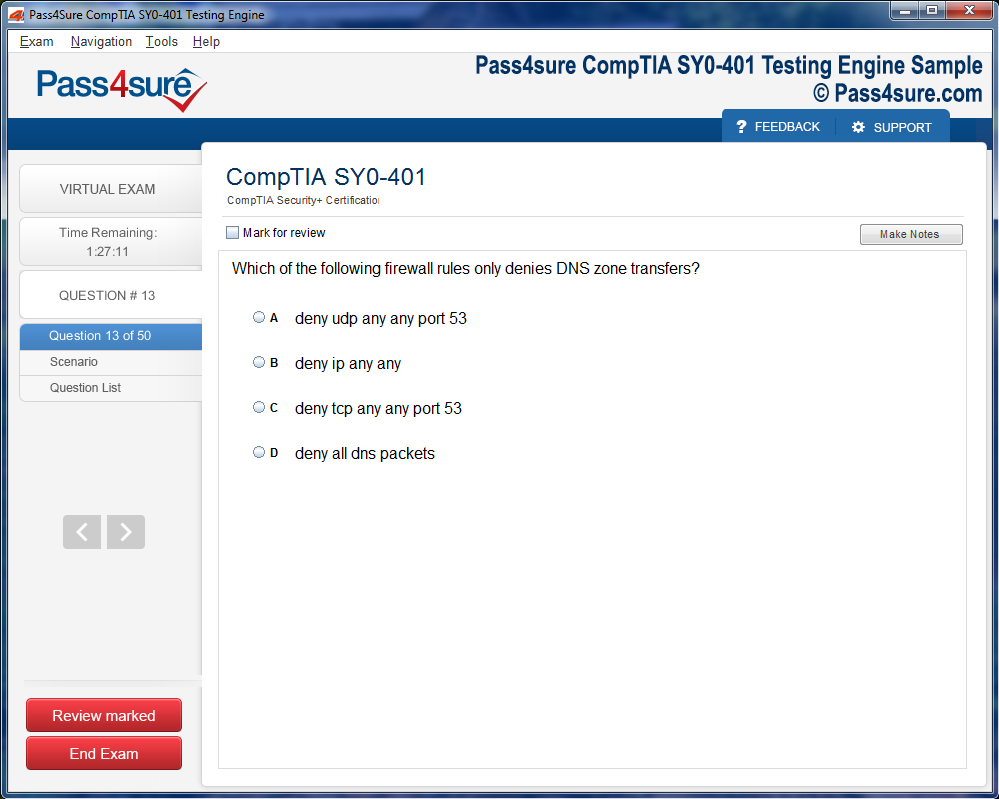
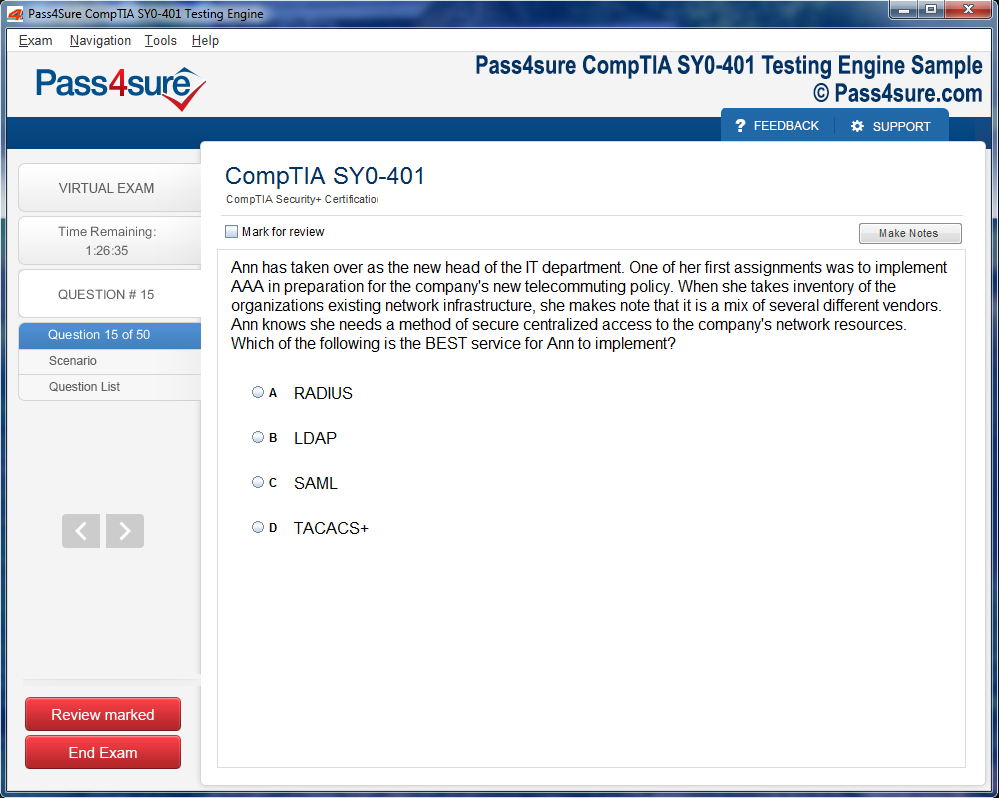
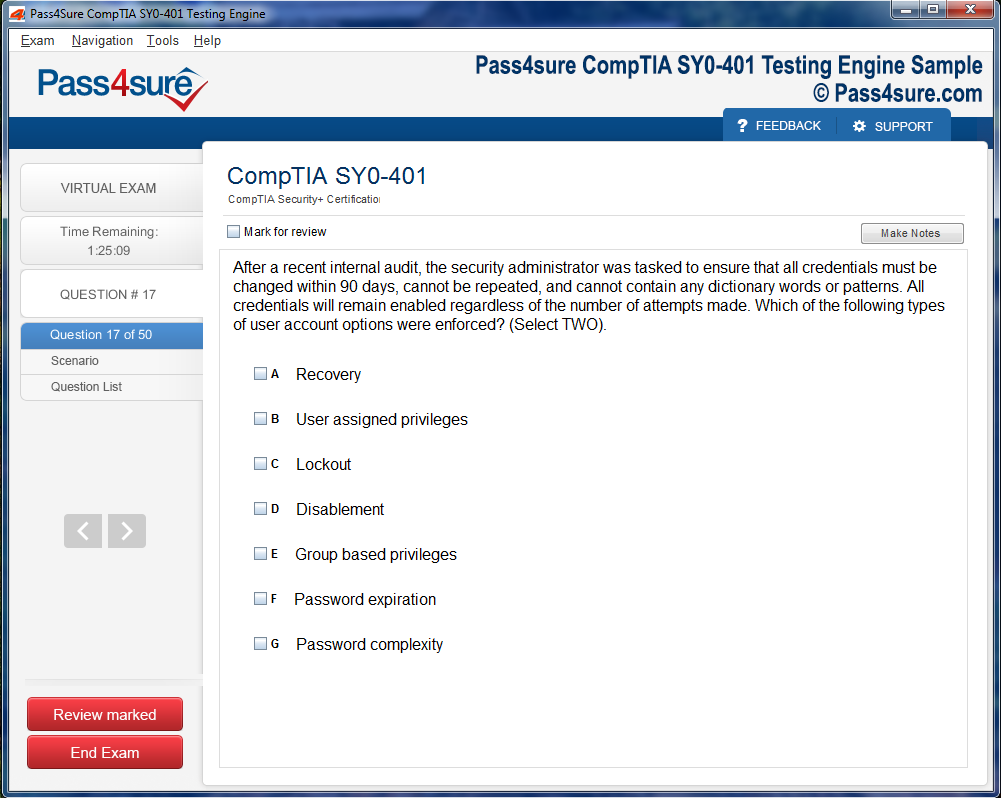
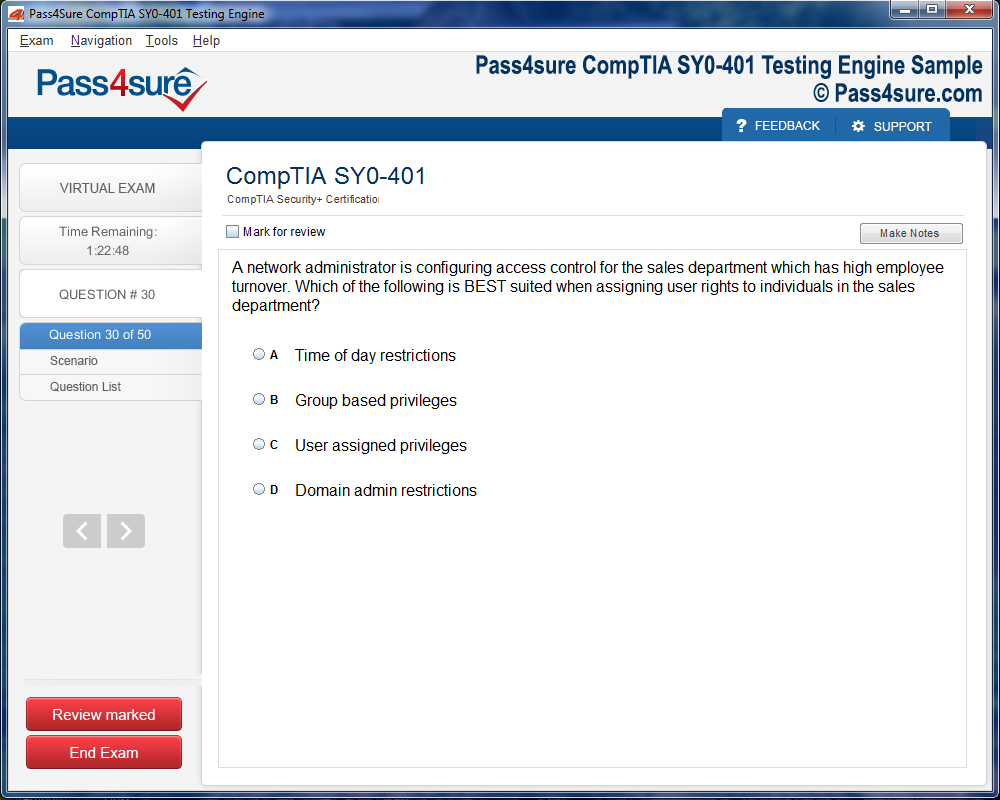
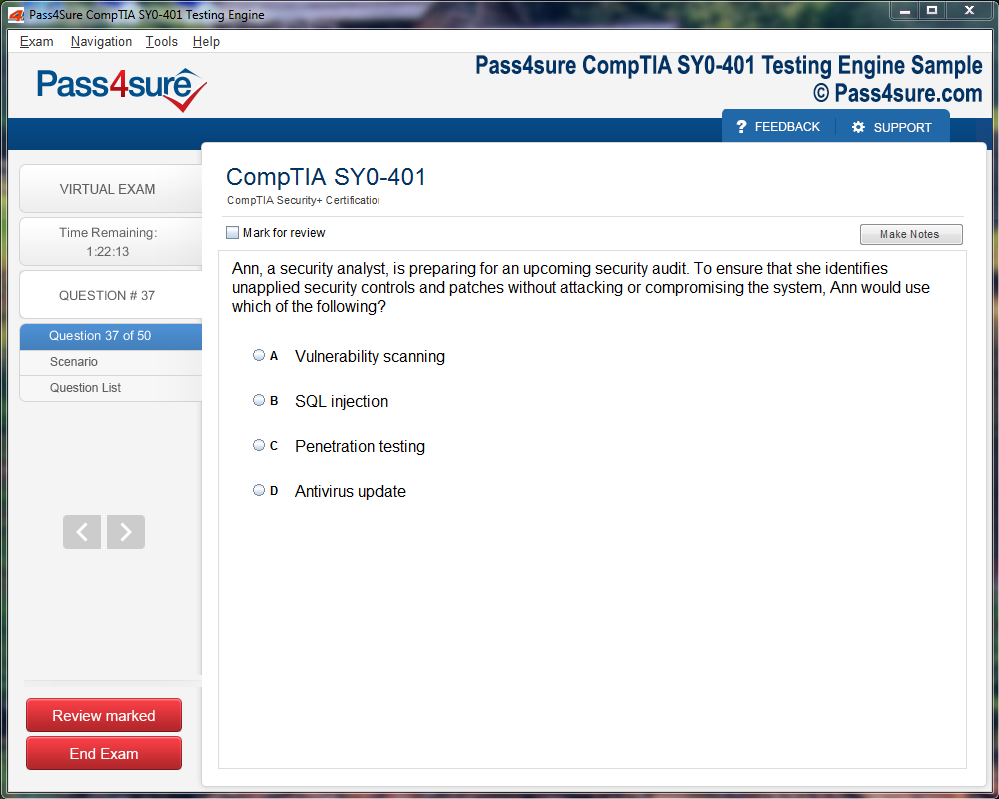
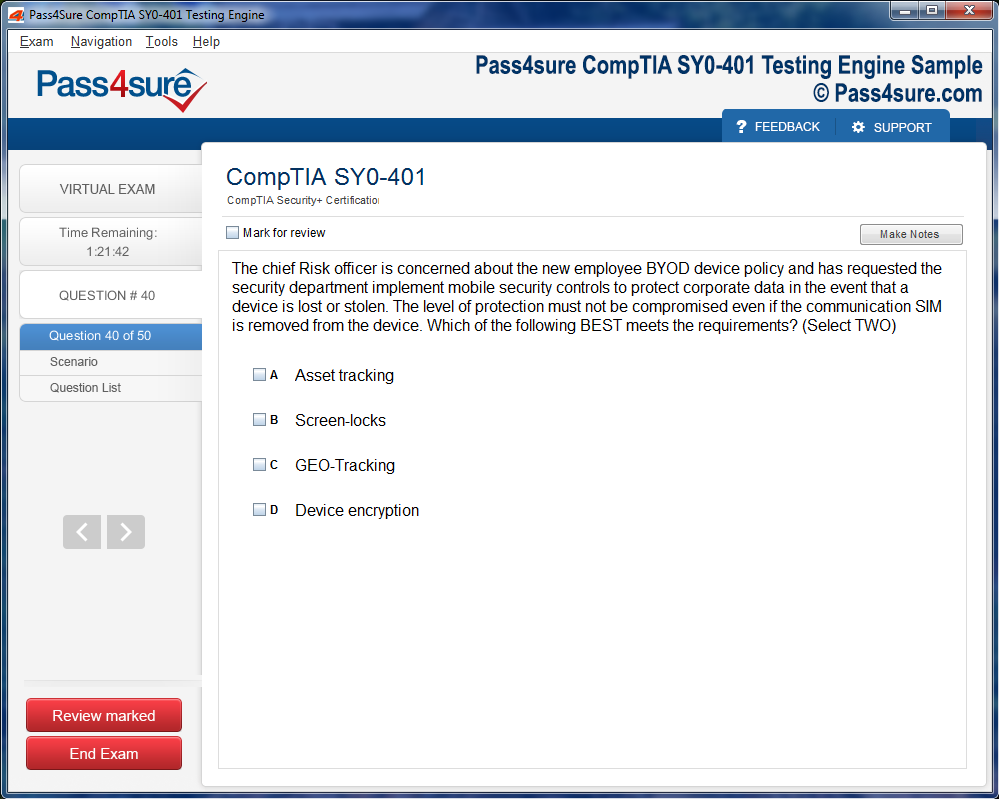
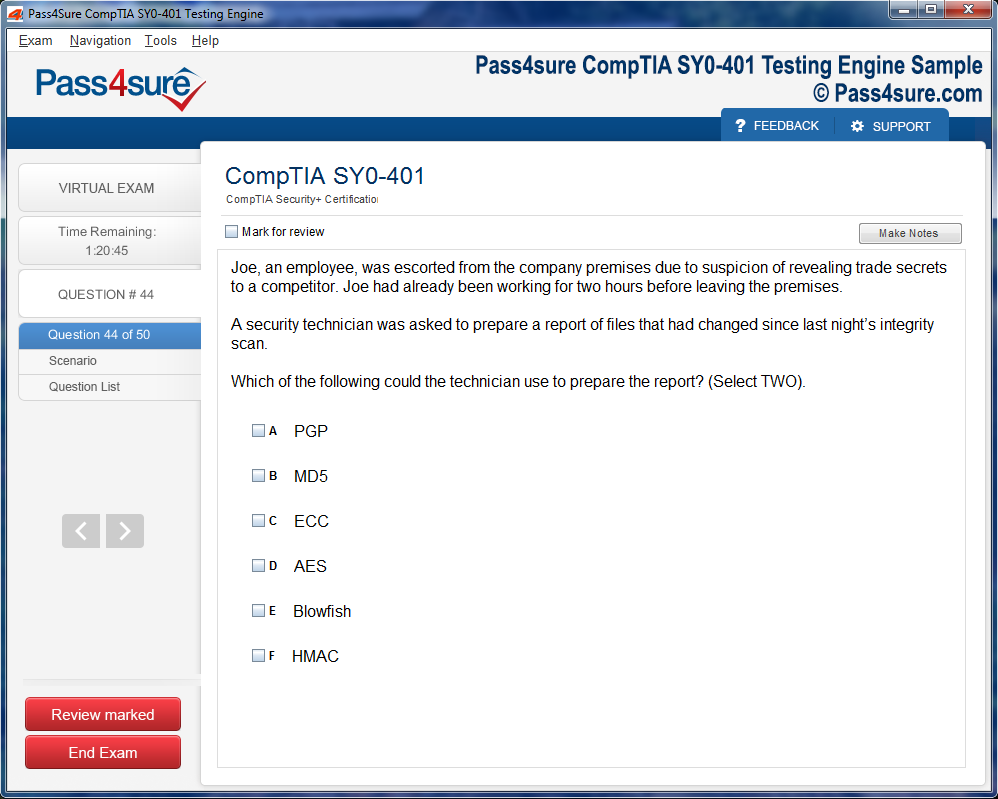
Product Screenshots
Frequently Asked Questions
How does your testing engine works?
Once download and installed on your PC, you can practise test questions, review your questions & answers using two different options 'practice exam' and 'virtual exam'. Virtual Exam - test yourself with exam questions with a time limit, as if you are taking exams in the Prometric or VUE testing centre. Practice exam - review exam questions one by one, see correct answers and explanations.
How can I get the products after purchase?
All products are available for download immediately from your Member's Area. Once you have made the payment, you will be transferred to Member's Area where you can login and download the products you have purchased to your computer.
How long can I use my product? Will it be valid forever?
Pass4sure products have a validity of 90 days from the date of purchase. This means that any updates to the products, including but not limited to new questions, or updates and changes by our editing team, will be automatically downloaded on to computer to make sure that you get latest exam prep materials during those 90 days.
Can I renew my product if when it's expired?
Yes, when the 90 days of your product validity are over, you have the option of renewing your expired products with a 30% discount. This can be done in your Member's Area.
Please note that you will not be able to use the product after it has expired if you don't renew it.
How often are the questions updated?
We always try to provide the latest pool of questions, Updates in the questions depend on the changes in actual pool of questions by different vendors. As soon as we know about the change in the exam question pool we try our best to update the products as fast as possible.
How many computers I can download Pass4sure software on?
You can download the Pass4sure products on the maximum number of 2 (two) computers or devices. If you need to use the software on more than two machines, you can purchase this option separately. Please email sales@pass4sure.com if you need to use more than 5 (five) computers.
What are the system requirements?
Minimum System Requirements:
- Windows XP or newer operating system
- Java Version 8 or newer
- 1+ GHz processor
- 1 GB Ram
- 50 MB available hard disk typically (products may vary)
What operating systems are supported by your Testing Engine software?
Our testing engine is supported by Windows. Andriod and IOS software is currently under development.
Essential Tips for ITIL 4 Practitioner Deployment Management
Deployment management under ITIL 4 transcends mere procedural mechanics; it embodies a philosophical paradigm that privileges anticipation, responsiveness, and systemic foresight. At its core lies the axiom of value co-creation, which implores professionals to discern not only the tangible deliverables of software deployment but also the intangible consequences upon organizational culture, customer perception, and operational fluidity. By internalizing these precepts, deployment architects cultivate a mindset attuned to the dynamism of contemporary IT ecosystems, navigating volatility with perspicacious acuity.
Syncretic Collaboration Across Domains
Effective deployment management necessitates a syncretic approach to interdepartmental synergy. Development, operations, and service management teams must coalesce around a unified schema of communication, transparency, and mutual accountability. ITIL 4 Practitioner emphasizes that such cross-functional collaboration is not perfunctory; it is strategic, engendering an environment where latent conflicts are preempted, knowledge silos dissolve, and collective intelligence elevates decision-making. By leveraging collaborative rituals—ranging from automated release pipelines to structured retrospectives—organizations achieve orchestration that is simultaneously robust and pliant.
Automation as an Operative Catalyst
In the crucible of deployment, automation functions as an operative catalyst, transmuting repetitive toil into precision-engineered processes. Provisioning environments, orchestrating configurations, and executing iterative testing sequences are no longer bottlenecks but accelerants of velocity and fidelity. ITIL 4 Practitioner advocates the judicious integration of intelligent automation tools, emphasizing the dual imperative of efficiency and vigilance. Beyond mere mechanization, automation also fosters traceability, enabling stakeholders to dissect and comprehend every procedural vector, thereby reinforcing accountability and continuous improvement.
Metrics, Measurement, and Epistemic Insights
Deployment efficacy is inherently contingent upon epistemic clarity, the capacity to derive insight from empirical observation. ITIL 4 Practitioner prescribes the rigorous application of metrics and KPIs, which illuminate both successes and latent deficiencies. These measures extend beyond conventional performance indicators to include anomaly detection, deployment cadence, rollback frequency, and post-release user sentiment. By synthesizing quantitative and qualitative intelligence, organizations cultivate a feedback loop that perpetuates refinement, mitigates recurrent errors, and enhances predictive foresight.
Risk Assessment and Contingency Cognizance
Prudential risk management constitutes a linchpin of deployment integrity. ITIL 4 Practitioner advocates anticipatory assessment of vulnerabilities, encompassing both technical fragilities and organizational susceptibilities. Contingency cognizance—predefined rollback procedures, failover architectures, and incident response playbooks—ensures that potential disruptions are contained with minimal operational perturbation. This preemptive disposition engenders confidence among stakeholders, fortifies resilience, and transforms deployment from a perilous undertaking into a calculated, reliable conduit for value delivery.
Deployment Orchestration in Agile Environments
Modern enterprises frequently operate within agile frameworks, necessitating a nuanced orchestration of deployment sequences. ITIL 4 Practitioner harmonizes with agile principles, advocating incremental, iterative releases that maximize adaptability while minimizing systemic shock. In such environments, deployment orchestration entails meticulous coordination of sprints, feature toggles, and continuous integration pipelines. The ability to reconcile agile velocity with ITIL’s structured guidance exemplifies the practitioner’s dexterity, ensuring that iterative innovation does not compromise stability or service continuity.
Cognitive Load and Change Perception
Beyond procedural considerations, deployment management intersects with cognitive and perceptual dimensions. Stakeholders, whether internal users or external clients, experience deployments not merely as events but as perceptual constructs shaped by clarity, timing, and perceived impact. ITIL 4 Practitioner underscores the necessity of managing cognitive load, providing transparent communication, staged rollouts, and contextual education. Such attentiveness to perception not only mitigates resistance but cultivates an organizational ethos wherein change is apprehended as progressive enhancement rather than disruptive intrusion.
The Intricacies of Deployment Management in ITIL 4
Deployment management is not merely a procedural task; it is a sophisticated orchestration of interdependent activities aimed at harmonizing technological change with organizational objectives. At its nucleus lies a confluence of structured methodology, strategic foresight, and iterative enhancement, ensuring that service evolution does not compromise operational stability. Within ITIL 4 Practitioner, deployment management is conceptualized as a conduit for value realization, linking tangible outcomes with the abstract imperatives of the Service Value System.
The Service Value System (SVS) itself is a latticework of governance, practices, and continual improvement paradigms. Deployment management thrives within this lattice, coordinating multifarious activities to ensure that every introduced change contributes positively to the organizational ecosystem. Unlike archaic methods, which often regard deployments as isolated tasks, ITIL 4 envisions deployment as a systemic operation, interconnected with change enablement, risk mitigation, and stakeholder engagement.
Collaborative Dynamics and Visibility
A linchpin of deployment excellence is the cultivation of collaborative dynamics. Teams are encouraged to operate within a framework of transparent communication, wherein every nuance of the deployment lifecycle is documented and disseminated. This transparency is not ornamental; it is operationally critical. Clear deployment logs, real-time status updates, and stakeholder notifications function as navigational beacons in a complex landscape of interdependent systems.
Visibility, therefore, is not merely the act of sharing information but the strategic alignment of knowledge across functional silos. When teams collectively perceive potential bottlenecks or vulnerabilities, they can preemptively institute mitigations. The resultant ecosystem is resilient, adaptive, and coherent, ensuring that deployments advance the business agenda without inadvertent disruptions.
Structured Change Enablement
Each deployment encapsulates an element of transformation, whether it is the introduction of novel functionality, the fortification of security protocols, or infrastructure augmentation. ITIL 4 Practitioner accentuates structured change enablement as a mechanism for safeguarding stability. Through rigorous assessment, meticulous approval workflows, and controlled execution, organizations reduce the probability of deployment failures. This structured approach is both prophylactic and prescriptive, combining preventive measures with adaptive strategies to accommodate emergent conditions.
By embedding change within a formalized governance framework, organizations cultivate stakeholder trust and service reliability. Each successful deployment reinforces the credibility of IT operations, transforming procedural rigor into a competitive advantage.
Automation as a Catalyst
Automation emerges as a pivotal enabler in contemporary deployment practices. By mechanizing repetitive or error-prone tasks, ITIL 4 practitioners amplify velocity and reliability while simultaneously minimizing human-induced variability. Automation extends beyond mere scripting; it encompasses orchestrated pipelines that unify development, testing, and production environments, ensuring consistency across heterogeneous landscapes.
Standardization via automation curtails configuration drift, a notorious source of unexpected failures. It empowers teams to replicate success across multiple environments, enhancing predictability and reducing cognitive overhead. The strategic infusion of automation transforms deployment management from a labor-intensive endeavor into a streamlined, precision-driven operation.
Quantitative Measurement and Iterative Feedback
Deployment management under ITIL 4 is profoundly empirical. By defining and monitoring key performance indicators—such as deployment frequency, success ratios, lead time, and post-deployment incident rates—organizations acquire actionable insights into operational efficacy. Metrics are not mere numeric abstractions; they form the substrate for iterative refinement, enabling continuous process enhancement.
Feedback loops are integral to this empirical paradigm. Monitoring systems, incident reports, and post-deployment analyses collectively inform successive iterations, fostering a culture of perpetual learning. This cyclical approach ensures that deployments progressively embody efficiency, stability, and alignment with organizational imperatives.
Risk Awareness and Proactive Mitigation
Deployments are inherently fraught with risk, encompassing potential service interruptions, data inconsistencies, and customer impact. ITIL 4 Practitioner advocates a proactive stance toward risk management, emphasizing early identification, comprehensive assessment, and robust contingency planning. Risk awareness is not a passive acknowledgment; it is an anticipatory discipline that calibrates deployment velocity against operational resilience.
Proactive mitigation strategies may include phased rollouts, canary deployments, and automated rollback mechanisms. These techniques reconcile the dual imperatives of speed and stability, ensuring that each deployment maximizes value without compromising continuity.
Continual Improvement and Evolution
Perhaps the most profound principle permeating ITIL 4 deployment management is continual improvement. Post-deployment reflection is not perfunctory; it is a rigorous analytical exercise. Teams systematically document lessons learned, dissect process bottlenecks, and refine operational protocols. This commitment to iterative enhancement ensures that deployment capabilities evolve in sophistication, agility, and resilience.
Continual improvement also fosters organizational memory, preserving insights from past experiences while embedding them into future practices. The resultant operational intelligence enhances service quality, accelerates innovation adoption, and fortifies the organization against systemic perturbations.
Strategic Contemplation of Deployment Trajectories
Embarking upon a deployment necessitates meticulous contemplation of its trajectory, a cognitive orchestration that transcends mere procedural adherence. It is within this crucible of planning that the sinews of success are forged. Forethought, when applied with judicious rigor, transforms uncertainty into a navigable lattice of actionable insights. By delineating the architecture of anticipated outcomes, teams cultivate a clairvoyant perspective, enabling preemptive identification of potential obfuscations that may compromise continuity. The cognitive scaffolding established at this stage serves as a prelude to operational precision, reducing perturbations in service continuity and accelerating the realization of business exigencies.
Delineating Scope and Operational Imperatives
The nucleus of preparatory rigor lies in the elucidation of scope and operational imperatives. Teams must dissect the metamorphosis intended within the system, articulating the rationale and alignment with overarching strategic initiatives. Such articulation fosters a shared cognitive schema among stakeholders, delineating both tangible and intangible metrics of success. By forging clarity in objectives, organizations mitigate the peril of misaligned expectations and cultivate a substrate upon which robust risk analysis and resource orchestration can flourish.
Environmental Harmonization and Consistency
Equally paramount is the harmonization of digital ecosystems across developmental strata. Incongruities between development, staging, and production environments manifest as latent vulnerabilities, capable of derailing even the most meticulously plotted deployments. Automation becomes the sentinel against such discrepancies, facilitating consistent replication of configuration states and environmental attributes. The resultant homogeneity serves as a prophylactic against erratic behaviors, ensuring that the transition from controlled testing to production is seamless and predictable.
Dependency Cartography and Integrative Cohesion
Deployment endeavors are rarely monolithic; they are intricate tapestries woven from interdependent modules, services, and processes. Mapping these dependencies is an intellectual cartography that illuminates potential friction points and integration bottlenecks. Documenting these interrelations is not merely bureaucratic; it constitutes an operational compendium that expedites troubleshooting and post-deployment audits. Such foresight engenders integrative cohesion, wherein the confluence of disparate components coalesces into a harmonious operational symphony.
Stakeholder Synergy and Transparent Communication
The orchestration of a successful deployment is contingent upon the cultivation of stakeholder synergy. The multifarious impact of changes necessitates proactive discourse encompassing operations, security, support, and business units. Articulating deployment timelines, elucidating anticipated ramifications, and clarifying rollback contingencies fosters a climate of trust and preparedness. Transparent communication functions as both lubricant and stabilizer, reducing cognitive dissonance and engendering collective readiness to navigate emergent anomalies.
Automation as Catalytic Mechanism
In the alchemy of deployment, automation is the catalytic agent that transmutes labor-intensive procedures into efficient, reliable sequences. By identifying repetitive and predictable operations—ranging from regression testing to configuration orchestration—teams liberate human capital for strategic endeavors while enhancing operational velocity. Strategic automation, when applied judiciously, minimizes fallibility, accelerates cycles, and fortifies system resilience. It is the invisible architect of operational cadence, orchestrating complexity with an unerring precision that manual execution seldom achieves.
Preemptive Risk Cognition and Contingency Architecture
A sophisticated deployment strategy is inseparable from the anticipation of potential perturbations. Preemptive risk cognition involves a meticulous survey of plausible failure vectors and the development of resilient contingency architectures. By codifying rollback protocols and defining alternative procedural pathways, organizations construct a buffer against systemic dislocations. This preemptive rigor transforms reactive firefighting into anticipatory intervention, mitigating downtime and preserving operational integrity.
Confluence of Planning and Operational Excellence
The synthesis of these preparatory endeavors crystallizes into a paradigm of operational excellence. Deployment management, when approached through the prism of strategic foresight and structured orchestration, transcends transactional execution and emerges as a value-centric discipline. The judicious application of planning principles ensures that every deployment is not a gambit but a calculated maneuver, designed to reinforce service reliability, fortify stakeholder confidence, and amplify organizational agility.
Orchestrating Deployments with Meticulous Precision
Deployment orchestration is the fulcrum of operational success, demanding a symphony of interdependent activities that coalesce seamlessly. The nuance lies not merely in sequential task execution but in harmonizing disparate elements—code artifacts, infrastructure alterations, configuration adjustments, and end-user touchpoints. A meticulously orchestrated deployment mitigates unforeseen perturbations and circumvents chaotic service interruptions.
Dependencies must be elucidated with perspicacity, ensuring that database migrations, configuration rollouts, and service restarts interlace with precision. Each interconnection constitutes a potential vector of disruption; therefore, visualizing the end-to-end deployment flow with granular clarity empowers teams to preempt misalignments. The orchestration mechanism functions as a temporal conductor, delineating the cadence of activities and dictating the precise juncture of intervention for each subsystem.
Automation as the Quintessence of Deployment Fidelity
Manual intervention, though sometimes inevitable, is inherently susceptible to capricious human error. Automation transmutes deployment from a stochastic endeavor into a deterministic process. Scripts meticulously crafted for code integration, environment provisioning, and rollback execution alleviate cognitive overhead while amplifying repeatability.
Continuous integration and continuous delivery pipelines epitomize this paradigm. By embedding automated verification, regression testing, and deployment triggers, CI/CD pipelines furnish instantaneous feedback loops. The automation not only accelerates throughput but fosters a provenance trail, rendering every deployment traceable and auditable. This traceability fortifies organizational confidence, transforming tentative experimental releases into robust, repeatable processes.
Vigilant Observation During Deployment
Monitoring is not merely a safeguard; it is a real-time diagnostic lens that unveils latent anomalies before they metastasize into systemic failures. Observational acuity encompasses the monitoring of application response latency, server resource consumption, and error frequency. Beyond these conventional metrics, user experience telemetry offers insight into perceptible degradation, enabling preemptive remediation.
Alerting mechanisms, when coupled with automated remediation protocols, diminish the window of vulnerability. Anomaly detection frameworks, enriched with adaptive thresholds, discern subtle deviations from normalcy. This vigilance ensures that the deployment environment remains resilient, responsive, and aligned with service level expectations.
Incident Governance and Dynamic Coordination
Even the most assiduously orchestrated deployment may encounter unanticipated contingencies. Centralized incident governance, epitomized by a deployment control board, provides a fulcrum for rapid, coordinated decision-making. Such a hub facilitates real-time escalation, resource reallocation, and stakeholder engagement.
Dynamic coordination also extends to inter-team synchronization. Development, operations, and business units must converse continuously, transcending siloed communication structures. The deployment becomes a living entity, adaptable to emergent variables while retaining procedural integrity.
Strategizing Rollbacks for Contingency Resilience
A rollback is not a mere afterthought but a critical element of deployment strategy. Predefined rollback schemas, meticulously documented and rehearsed, ensure that service continuity is preserved in the face of anomalies. These strategies delineate the precise steps to revert changes across multiple layers—database, middleware, application, and user interfaces—without engendering further disruption.
In essence, a robust rollback plan embodies anticipatory prudence. By codifying potential failure scenarios and their corresponding remediation pathways, teams reduce cognitive load during crises and bolster organizational confidence in the deployment lifecycle.
Communicative Transparency as an Operational Imperative
Communication, often underestimated, constitutes the connective tissue that binds the deployment apparatus. Stakeholders, from executives to end-users, require transparent, timely updates regarding progress, impediments, and mitigative actions. This communicative clarity mitigates uncertainty, fosters trust, and aligns cross-functional teams toward the shared objective of successful deployment.
Structured communication channels—ranging from automated status dashboards to interactive incident briefings—ensure that information is not merely disseminated but internalized. The interplay between real-time updates and anticipatory alerts cultivates a proactive environment, minimizing reactive firefighting.
Integration of Orchestration, Automation, and Monitoring
The zenith of deployment efficacy emerges when orchestration, automation, and monitoring converge into a synergistic ecosystem. Orchestration dictates the rhythm, automation executes with precision, and monitoring provides diagnostic insight. Together, these pillars coalesce into a controlled, predictable deployment continuum.
This holistic integration also enhances organizational agility. Teams can deploy iteratively, adapt to changing requirements, and scale processes with minimal friction. The deployment ceases to be a disruptive, high-stakes event; it becomes a regularized, value-generating activity with inherent resilience.
Post-Deployment Review: A Crucible for Insight
The deployment of a system or service does not signify the terminus of effort; rather, it inaugurates an indispensable crucible of analysis and reflection. Post-deployment review constitutes the bedrock of understanding whether the implemented changes fulfill intended objectives. Metrics such as deployment success rate, mean time to recovery, and service-level adherence provide numerical barometers of achievement, yet they are merely the superficial veneer of a deeper evaluative process. The alchemy of review lies in discerning latent patterns, emergent inefficiencies, and unforeseen anomalies, which collectively illuminate pathways for refinement.
Incipient Issues and Root Cause Exegesis
In the aftermath of deployment, incidents often surface with unanticipated ferocity. Each perturbation, however minor, warrants meticulous scrutiny. Root cause exegesis extends beyond mere troubleshooting; it necessitates a forensic interrogation of processes, dependencies, and systemic interactions. By identifying the fulcrum of disruption, organizations can institute prophylactic measures that forestall recurrence. This procedural perspicacity aligns with the ethos of continual improvement, fostering a culture of preemptive vigilance rather than reactive remediation.
Stakeholder Perspicuity and Qualitative Appraisal
Metrics alone cannot encapsulate the entirety of deployment impact. Stakeholders—spanning end-users, business units, and support cadres—offer a reservoir of qualitative insight. Eliciting this perspicuity requires structured interviews, surveys, and feedback loops, enabling organizations to apprehend subtleties imperceptible to quantitative assessment. Anecdotal evidence, when triangulated with operational data, unveils nuanced inefficiencies and latent opportunities for enhancement, enriching the strategic intelligence of the organization.
Process Codification and Knowledge Osmosis
The post-deployment phase is fertile terrain for process codification. Lessons harvested from the deployment lifecycle should be transcribed into comprehensive guides, runbooks, and best practice compendiums. Such codification engenders knowledge osmosis across teams, mitigating the risks of experiential attrition. Documented processes transform ephemeral insights into durable intellectual assets, ensuring that future initiatives are scaffolded upon accumulated wisdom rather than ad hoc improvisation.
Iterative Refinement and Evolutionary Loops
Deployments are not static monuments but dynamic constructs necessitating iterative refinement. Continuous improvement loops act as accelerants for this evolution, synthesizing monitoring data, stakeholder feedback, and emergent methodologies into actionable enhancements. This cyclical approach cultivates a resilient deployment architecture, incrementally bolstering efficiency, reducing operational risk, and amplifying service quality. Each iteration functions as a microcosm of experiential learning, progressively honing organizational capability.
Analytics-Driven Vigilance
Post-deployment monitoring constitutes an analytical vigil that perpetuates improvement. Telemetry, logs, and performance metrics provide granular visibility into system behavior under real-world conditions. Advanced analytical techniques, including anomaly detection and predictive modeling, enable preemptive identification of performance degradation. By operationalizing data into prescriptive insights, organizations transcend reactive paradigms, transforming surveillance into strategic foresight.
Feedback Integration and Adaptive Strategies
The quintessence of post-deployment review lies in the agile integration of feedback into adaptive strategies. Observations from users, combined with analytical data, catalyze tactical recalibrations. This adaptive stance ensures that the deployment remains congruent with evolving organizational exigencies and emergent technological landscapes. The dynamic interplay between feedback assimilation and strategy refinement engenders a virtuous cycle of perpetual optimization.
Knowledge Dissemination and Cultural Amplification
Recognizing and disseminating knowledge derived from deployment experiences reinforces organizational culture. Celebrating triumphs, documenting failures, and sharing nuanced insights cultivate an ethos of transparency and engagement. Knowledge dissemination engenders collective competency, fortifying the enterprise against complexity and volatility. Such cultural amplification ensures that the organizational intellect continuously accrues, fortifying readiness for subsequent deployment challenges.
Synergistic Alignment of Metrics and Experience
The most efficacious post-deployment reviews marry quantitative metrics with qualitative experience. While KPIs, service-level achievements, and defect indices quantify operational success, narrative accounts from teams elucidate contextual subtleties. This synergistic alignment produces a holistic understanding of deployment efficacy, informing strategic planning, resource allocation, and future process optimization.
Embedding Continuous Improvement into Operational DNA
The culmination of post-deployment reflection is the institutionalization of continuous improvement. By embedding iterative refinement into operational DNA, organizations transcend episodic enhancements, cultivating a culture of perpetual learning. Deployments evolve from mere procedural obligations into strategic touchstones that shape organizational capability, resilience, and adaptability. Each deployment becomes an inflection point, providing fertile ground for empirical learning and enduring process enrichment.
The Paradigm of Predictive Deployment Analytics
In the labyrinthine landscape of modern IT operations, predictive deployment analytics emerges as a lodestar. Harnessing historical deployment datasets through sophisticated AI algorithms, organizations can anticipate latent bottlenecks, forecast temporal deviations, and meticulously allocate ephemeral resources. The predictive lens illuminates hidden correlations between deployment frequency, rollback incidents, and operational anomalies, enabling preemptive mitigation strategies. By transcending reactive paradigms, predictive deployment empowers managers to sculpt decision architectures that minimize entropy and enhance systemic resilience.
Value Stream Cartography and Operational Cognition
Strategic optimization of deployment necessitates a cartographic approach to value streams. Mapping the trajectory from conceptual ideation to production instantiation elucidates concealed redundancies, obfuscatory handoffs, and latent inefficiencies. This operational cognition enables organizations to pinpoint process inflection points and design interventions with surgical precision. By integrating ITIL 4 Practitioner principles, the cartographic exercise becomes a conduit for aligning technical flows with macroeconomic imperatives, thus maximizing both efficiency and organizational consonance.
Containerization and Microservices Synergy
The ascendance of cloud-native architectures has catalyzed the proliferation of containerized deployments. Microservices, encapsulated within lightweight containers, offer unparalleled modularity, decoupling, and horizontal scalability. Orchestration platforms such as Kubernetes facilitate synchronous choreography of interdependent services while preserving systemic coherence. By embedding ITIL 4 frameworks within this architecture, organizations can harness technological elasticity without compromising governance, ensuring both agility and operational fidelity.
Hyperautomation and CI/CD Confluence
Hyperautomation, synergized with continuous integration and continuous deployment pipelines, redefines the temporal metrics of delivery. Automated regression suites, unit testing, and deployment scaffolds accelerate time-to-value while mitigating human-induced variance. Strategic calibration ensures that automation augments, rather than supplants, human oversight, preserving decision-making granularity in anomalous conditions. The fusion of these methodologies engenders a cadence of deployments that is both rapid and predictably robust, aligning operational tempo with strategic imperatives.
Cultural Transmutation and Cross-Functional Synergy
Beyond technical dexterity, deployment efficacy is profoundly influenced by organizational culture. High-functioning deployment teams cultivate transparency, shared accountability, and cross-pollination of expertise across functional silos. ITIL 4 Practitioner underscores the indispensability of a learning-oriented ecosystem where failure is dissected, knowledge codified, and adaptability valorized. The resultant cultural transmutation not only accelerates operational responsiveness but embeds a collective intelligence that perpetuates continuous refinement and resilience.
Strategic Confluence with Enterprise Objectives
Deployment management ascends to strategic relevance when entwined with overarching enterprise objectives. By harmonizing release cadence with regulatory mandates, customer exigencies, and market oscillations, organizations ensure that each deployment functions as a vector of tangible value creation. Strategic confluence mandates rigorous alignment of technical decisions with corporate trajectories, converting deployments from isolated operational acts into orchestrated enablers of innovation and market differentiation.
Dynamic Orchestration and Risk Prognostication
Dynamic orchestration of deployment pipelines, informed by real-time telemetry and heuristic risk models, provides a proactive bulwark against operational perturbations. Predictive algorithms assess resource contention, potential conflicts, and throughput anomalies, enabling anticipatory adjustments to deployment scheduling and resource provisioning. This iterative prognostication cultivates an adaptive deployment ecosystem where uncertainty is systematically mitigated, and organizational resilience is continuously reinforced.
Cognitive Automation and Intelligent Feedback Loops
Intelligent feedback loops, integrated within automated deployment frameworks, engender a self-correcting operational milieu. Continuous monitoring of post-deployment metrics, error incidence, and user experience indicators informs iterative refinements. Cognitive automation synthesizes these insights, adjusting deployment heuristics in near-real-time, thereby fostering an environment where operational knowledge is dynamically codified and leveraged to preempt systemic degradation.
Orchestral Integration of Multi-Environment Deployments
Managing deployments across heterogeneous environments necessitates an orchestral approach. Coordinated synchronization of staging, pre-production, and production environments mitigates version drift, dependency conflicts, and configuration anomalies. ITIL 4 principles facilitate governance, ensuring that multi-environment orchestration maintains fidelity to organizational standards while accommodating the dynamism of emergent technologies.
Resilient Architecture and Contingency Engineering
Resiliency in deployment architecture is predicated upon anticipatory contingency engineering. Redundant topologies, failover mechanisms, and rollback contingencies provide a safeguard against systemic failures. By embedding resiliency into the architectural design, organizations transform deployment strategies from reactive firefighting into proactive fortification, ensuring operational continuity even amidst stochastic disruptions.
Strategic Deployment Planning and Temporal Orchestration
Deployment is not an ad hoc operation; it is a temporally orchestrated enterprise demanding foresight and meticulous sequencing. Strategic deployment planning under ITIL 4 Practitioner emphasizes aligning release windows with business imperatives, resource availability, and potential systemic stress points. This temporal orchestration ensures that deployments capitalize on periods of minimal operational friction while anticipating peak load challenges. By integrating predictive analytics and historical data, deployment architects can model the optimal cadence, reducing both latency and the likelihood of cascading failures.
Environment Sanctity and Configuration Fidelity
The sanctity of deployment environments is paramount. ITIL 4 Practitioner asserts that a deviation in configuration integrity or environmental parity between development, staging, and production can precipitate cascading disruptions. Ensuring configuration fidelity entails rigorous version control, automated provisioning, and environment-as-code paradigms. These practices transform mutable environments into reproducible, auditable constructs that significantly mitigate the risk of unforeseen anomalies and reinforce organizational confidence in each release.
Orchestration of Multi-Component Releases
Modern IT ecosystems are often polyglot, comprising multiple interdependent services and microcomponents. Orchestrating such multi-component releases requires a systems-thinking perspective. ITIL 4 Practitioner promotes the decomposition of releases into modular units, each with defined dependencies, rollback strategies, and monitoring thresholds. By treating deployments as an ecosystem rather than isolated events, organizations achieve resilience, enabling individual components to evolve independently without jeopardizing overall service integrity.
Continuous Improvement Through Post-Deployment Reflection
Deployment is a locus of learning, not merely execution. Post-deployment reflection, a core tenet of ITIL 4 Practitioner, facilitates continuous improvement by capturing anomalies, identifying process bottlenecks, and codifying best practices. These reflections extend beyond technical parameters to encompass cross-team communication, stakeholder engagement, and user experience outcomes. Through systematic retrospection, deployment management transforms into a living discipline, continuously adapting to technological innovations and organizational evolution.
Stakeholder Integration and Sociotechnical Synergy
Deployments do not occur in a vacuum; they intersect with the sociotechnical matrix of the organization. ITIL 4 Practitioner emphasizes stakeholder integration, ensuring that business units, end-users, and operational teams participate in both planning and assessment. This sociotechnical synergy fosters alignment between IT outcomes and organizational objectives, reducing friction, preempting resistance, and facilitating adoption. The result is a deployment culture where changes are co-created, anticipated, and collectively owned.
Risk Stratification and Probabilistic Contingency
Advanced deployment management requires nuanced risk stratification, extending beyond deterministic analyses to probabilistic modeling. ITIL 4 Practitioner encourages the assessment of risk likelihood and impact, informed by historical incident data, system interdependencies, and external factors such as regulatory changes or market volatility. Probabilistic contingency planning ensures that fallback mechanisms are proportionate to potential disruption, creating a tiered response capability that enhances resilience while avoiding over-engineered or underprepared interventions.
Automation Maturity and Toolchain Harmonization
The sophistication of deployment management is inseparable from the maturity of automation and the cohesiveness of the toolchain. ITIL 4 Practitioner advocates for a holistic approach, where orchestration tools, CI/CD pipelines, configuration management systems, and observability platforms operate in concert. Harmonized toolchains reduce cognitive load, minimize manual error, and enable near-real-time visibility into deployment status. The emphasis is not merely on automation for expedience but on creating a self-correcting ecosystem where insights from each deployment inform the next.
Observability and Feedback Loops
Observability transcends traditional monitoring by emphasizing proactive insight into system behavior under real-world conditions. ITIL 4 Practitioner integrates observability into deployment management, ensuring that logs, metrics, traces, and user feedback converge into actionable intelligence. These feedback loops allow practitioners to detect anomalies early, refine deployment strategies, and anticipate emergent system behaviors. The net effect is a deployment practice that is anticipatory rather than reactive, fostering a culture of continuous vigilance and adaptive learning.
Cultural Embedding of Deployment Practices
Sustainable deployment management is as much cultural as it is technical. ITIL 4 Practitioner underscores the necessity of embedding deployment practices into the organizational ethos. This involves inculcating principles of transparency, shared accountability, and iterative learning into team norms. Cultural embedding ensures that process adherence is voluntary, habitual, and contextually appropriate, mitigating the risk of procedural drift and reinforcing the perception of deployment as an enabler rather than a constraint.
Change Saturation and Cognitive Economy
A critical consideration often overlooked in deployment strategy is change saturation—the threshold beyond which the organization’s capacity to absorb change diminishes. ITIL 4 Practitioner emphasizes managing cognitive economy, balancing the frequency and magnitude of deployments against the organization’s bandwidth for adaptation. Techniques such as phased rollouts, feature flagging, and staggered adoption are employed to maintain equilibrium, ensuring that innovation is delivered without overwhelming human or technical resources.
Knowledge Management and Epistemic Continuity
Knowledge is the substrate upon which deployment resilience is constructed. ITIL 4 Practitioner integrates robust knowledge management, ensuring that insights, procedural nuances, and incident learnings are systematically captured, indexed, and disseminated. Epistemic continuity preserves institutional memory, enabling successive deployment cycles to benefit from cumulative experience. This practice mitigates the risk of repeating errors, accelerates onboarding, and fosters a culture where learning is codified and operationalized.
Incident Preparedness and Adaptive Recovery
No deployment strategy is immune to unforeseen contingencies; thus, adaptive recovery planning is indispensable. ITIL 4 Practitioner emphasizes the articulation of incident preparedness protocols, including automated rollback, hotfix deployment, and cross-team escalation channels. Adaptive recovery frameworks are designed to be elastic, accommodating both minor perturbations and critical failures. By rehearsing and refining these protocols, organizations transform reactive firefighting into a systematic capability, enhancing confidence and operational stability.
Compliance Alignment and Regulatory Consonance
Deployments are subject to an increasingly intricate lattice of regulatory and compliance mandates. ITIL 4 Practitioner mandates that deployment processes are consonant with legal frameworks, cybersecurity standards, and organizational policies. Integrating compliance considerations into deployment planning precludes regulatory infractions, mitigates reputational risk, and ensures that innovation operates within sanctioned boundaries. This alignment is achieved through automated auditing, version-controlled documentation, and role-based access management, creating a defensible operational posture.
Cognitive Friction and Adoption Velocity
The efficacy of deployment is intimately tied to adoption velocity—the speed at which end-users integrate and leverage new capabilities. ITIL 4 Practitioner addresses cognitive friction, which impedes adoption, by instituting transparent communication, contextual training, and user-centric interface design. Reducing friction enhances both perceived and actual value, ensuring that deployments catalyze operational effectiveness rather than provoke resistance. This human-centered approach underscores the interdependence of technical execution and behavioral dynamics.
Cross-Pollination of Best Practices
Deployment management thrives when best practices are cross-pollinated across teams, domains, and even industries. ITIL 4 Practitioner encourages practitioners to synthesize insights from diverse contexts, creating hybridized approaches that are innovative yet grounded. This cross-pollination fosters resilience, reduces redundancy, and promotes a culture of adaptive experimentation, where novel methodologies can be tested safely within controlled parameters before broader implementation.
Strategic Communication and Narrative Framing
The perception of deployment success is contingent not solely on operational metrics but also on narrative framing. ITIL 4 Practitioner emphasizes strategic communication, ensuring that stakeholders perceive deployments as deliberate, value-adding initiatives. This involves articulating objectives, anticipated impacts, and success criteria clearly and persuasively. Narrative framing mitigates uncertainty, galvanizes support, and reinforces the perception of IT as a proactive driver of organizational capability rather than a reactive service provider.
The Philosophical Underpinnings of Deployment Management
Deployment management in ITIL 4 transcends the mere technical execution of changes; it is an intricate philosophical exercise in orchestrating organizational flux. Each deployment is a microcosm of systemic equilibrium, demanding an appreciation of interdependencies, latent constraints, and emergent behaviors. Practitioners are encouraged to perceive deployments as semiotic artifacts—each action, log, and rollback conveys information that shapes the organizational consciousness.
This cognitive lens transforms deployment from a transactional activity into a reflective practice. By contemplating the ripple effects of each deployment, organizations can preempt unintended consequences, optimize resource allocation, and harmonize IT initiatives with strategic imperatives. The deployment process thus becomes a dialectical interplay between precision engineering and adaptive cognition.
Contextual Awareness in Deployment Strategies
Contextual awareness is an often-overlooked axis of deployment excellence. ITIL 4 Practitioner emphasizes that deployments must be contextually congruent, taking into account environmental variability, user behavior, and infrastructural topology. Deployments in isolated test environments may function flawlessly but encounter chaos when transposed into heterogeneous production landscapes.
Environmental profiling—an analytical process of mapping dependencies, system interactions, and usage patterns—is essential. Context-aware deployments consider temporal factors, such as peak usage intervals, seasonality of traffic, and organizational readiness. By embedding contextual intelligence, organizations reduce the incidence of latent failures, enhance user satisfaction, and fortify the alignment between technological evolution and business exigencies.
The Semantics of Deployment Logs and Documentation
Documentation in deployment management is often underestimated, yet it is a vessel of operational semiotics. Deployment logs, meticulously maintained, provide a historical ledger that enables forensic analysis, predictive modeling, and knowledge transfer. Every log entry, timestamp, and annotation constitutes a fragment of organizational memory, revealing patterns, recurring anomalies, and latent systemic vulnerabilities.
High-fidelity documentation transforms mundane procedural records into strategic instruments. For example, correlating log data with incident occurrences can illuminate subtle causative relationships, enabling preemptive corrective action. Similarly, rich documentation facilitates cross-team collaboration, knowledge sharing, and onboarding, fostering a resilient and self-sustaining deployment ecosystem.
Orchestration and the Symphony of Automation
Automation is not merely a tactical convenience; it is a transformative force in deployment orchestration. Orchestrated automation pipelines unify disparate processes—build, test, deploy, monitor—into a coherent, symphonic sequence. Each stage of the pipeline is choreographed with precision, ensuring that transitions are seamless, dependencies are respected, and anomalies are immediately flagged.
Advanced automation leverages declarative configurations, infrastructure as code, and intelligent rollback mechanisms. Declarative frameworks abstract procedural complexity, allowing practitioners to describe the desired state rather than procedural minutiae. Infrastructure as code codifies environmental configurations, ensuring reproducibility, eliminating configuration drift, and embedding consistency across heterogeneous environments. Intelligent rollback mechanisms detect deviations from expected behavior and initiate corrective interventions autonomously, preserving stability and service continuity.
Metrics as Strategic Instruments
While metrics are often viewed as operational indicators, ITIL 4 Practitioner frames them as strategic instruments for organizational insight. Deployment frequency, lead time, mean time to recovery, and change failure rate provide quantitative lenses to assess efficacy. However, the true value of metrics emerges when they are integrated into a broader feedback ecosystem.
Causal analysis transforms raw data into actionable intelligence. For instance, a trend of increasing lead time may reveal hidden bottlenecks in pre-deployment testing or approval workflows. Conversely, a declining change failure rate may indicate maturation of automation pipelines or enhanced stakeholder alignment. By contextualizing metrics within organizational objectives, deployment management evolves from reactive troubleshooting to anticipatory governance.
Risk Taxonomy and Hierarchical Mitigation
Effective deployment management requires an intricate taxonomy of risks. ITIL 4 Practitioner encourages the decomposition of risks into hierarchical strata—operational, infrastructural, security, and business continuity. Each stratum demands distinct mitigation strategies, tailored to severity, likelihood, and organizational impact.
Operational risks, such as misconfigurations or human errors, are mitigated through automation, peer review, and procedural audits. Infrastructural risks, including hardware failures or dependency inconsistencies, require redundancy planning, failover mechanisms, and continuous monitoring. Security risks—ranging from patch vulnerabilities to unauthorized access—necessitate rigorous validation, encryption, and compliance adherence. Business continuity risks, encompassing service outages or reputational damage, are addressed through contingency planning, phased rollouts, and resilient communication protocols.
This multi-layered approach fosters a comprehensive understanding of potential vulnerabilities, ensuring that deployments advance with calculated confidence rather than precarious haste.
Stakeholder Cognition and Expectation Management
Deployment management is intrinsically social as well as technical. Stakeholder cognition—the collective understanding of deployment scope, risk, and impact—plays a pivotal role in operational success. ITIL 4 Practitioner underscores the necessity of proactive expectation management. Transparent communication, pre-deployment briefings, and post-deployment debriefs cultivate trust, reduce resistance, and align divergent perspectives.
Misalignment between operational teams and stakeholders can precipitate cascading disruptions. Conversely, well-informed stakeholders act as collaborative agents, providing contextual insights, identifying potential pain points, and endorsing strategic trade-offs. By integrating stakeholder cognition into deployment workflows, organizations achieve symbiosis between technical execution and organizational comprehension.
Cognitive Load and Decision Optimization
The orchestration of deployments entails navigating high-dimensional decision spaces. Practitioners must balance competing priorities: speed versus stability, standardization versus customization, automation versus human oversight. Cognitive load management emerges as a crucial principle, ensuring that decision-makers retain clarity and operational acuity under complex conditions.
Techniques to reduce cognitive load include decision matrices, automated alerting, simulation environments, and modularized processes. By structuring choices, filtering extraneous information, and providing real-time feedback, organizations enhance decision quality and reduce the likelihood of error. Cognitive optimization thus functions as a silent enabler of deployment resilience.
Emergent Behavior and Adaptive Strategies
Deployments in complex IT ecosystems often induce emergent behavior—unanticipated interactions and outcomes arising from system interdependencies. ITIL 4 Practitioner advocates for adaptive strategies capable of responding to emergent phenomena. These strategies include incremental rollouts, feature toggles, canary releases, and adaptive monitoring frameworks.
Incremental rollouts limit exposure to novel changes, allowing early detection of adverse effects. Feature toggles provide dynamic control over functionality, enabling swift retraction without full rollback. Canary releases expose subsets of users to new changes, gathering empirical feedback before widespread deployment. Adaptive monitoring continuously analyzes system performance, triggering automated interventions when anomalies arise.
This adaptive stance transforms uncertainty from a threat into an informational asset, enabling organizations to refine deployments dynamically and harness emergent insights for continuous improvement.
Orchestrated Observability and Telemetry Intelligence
In contemporary deployment ecosystems, orchestrated observability functions as the nervous system of operational integrity. By integrating comprehensive telemetry pipelines, organizations capture high-fidelity signals encompassing performance metrics, latency anomalies, and resource utilization. These telemetry signals are not merely diagnostic; when coupled with AI-driven analytical engines, they metamorphose into prescriptive insights that anticipate potential degradations. Observability enables real-time situational awareness, empowering teams to dynamically recalibrate deployments and preempt cascading failures before systemic instability emerges.
Algorithmic Load Balancing and Capacity Forecasting
Deployment efficacy is intimately tethered to algorithmic load balancing and capacity foresight. Sophisticated queuing models and predictive allocation algorithms ensure that workloads are dynamically distributed across infrastructure nodes, mitigating contention and bottlenecks. Capacity forecasting, leveraging historical demand curves and stochastic simulations, anticipates peak load periods, thereby optimizing scaling policies. The integration of these mechanisms within ITIL-aligned deployment protocols ensures that resource elasticity aligns with both technical constraints and business exigencies.
DevSecOps Infusion and Security Posture Harmonization
Security, traditionally treated as an adjunct to deployment, now assumes a proactive, embedded role within DevSecOps paradigms. By interweaving security controls into the deployment pipeline, organizations ensure continuous compliance, threat detection, and vulnerability remediation. Static analysis, container image scanning, and runtime behavioral monitoring converge to establish a hardened security posture. The harmonization of deployment speed with risk mitigation epitomizes strategic sophistication, ensuring that acceleration does not compromise the sanctity of organizational data and operational trust.
Multi-Cloud Orchestration and Interoperability Challenges
The proliferation of multi-cloud architectures introduces unprecedented flexibility but concomitant interoperability challenges. Managing deployments across diverse cloud providers requires meticulous standardization of API interactions, network topologies, and configuration schemas. Advanced orchestration tools facilitate seamless cross-cloud deployments, enabling elastic resource utilization while mitigating vendor lock-in. Strategic alignment with ITIL 4 Practitioner guidance ensures that cloud diversification amplifies value streams without generating operational opacity or compliance drift.
Autonomous Rollback Mechanisms and Anomaly Containment
Rollback capabilities, once rudimentary, have evolved into autonomous, intelligence-driven mechanisms capable of real-time anomaly containment. By continuously monitoring post-deployment behavior against historical baselines, these systems identify deviations and initiate corrective actions autonomously. The resultant agility not only minimizes downtime but embeds a layer of operational self-healing within deployment pipelines, reducing the cognitive load on human operators and enhancing overall systemic resilience.
Choreographed Feature Flag Management
Feature flags have emerged as pivotal instruments in orchestrating controlled, incremental releases. Choreographed management of feature toggles allows teams to decouple code deployment from feature activation, facilitating canary releases, A/B testing, and progressive rollout strategies. This granular control mitigates exposure to systemic risk, enabling rapid experimentation while preserving service continuity. When codified within ITIL-aligned practices, feature flag orchestration transforms experimental agility into strategic operational advantage.
Continuous Learning and Deployment Intelligence
Deployment management thrives within an ecosystem of continuous learning. By integrating post-mortem analysis, incident retrospectives, and performance analytics, organizations cultivate a repository of deployment intelligence. This knowledge, codified into playbooks, adaptive heuristics, and automated pipelines, forms a feedback loop that incrementally elevates deployment efficacy. The iterative nature of this learning process fosters resilience, operational predictability, and strategic adaptability, transforming deployment management into a continuously self-optimizing discipline.
Micro-Orchestration for Heterogeneous Workloads
Modern enterprise applications often span heterogeneous workloads encompassing batch processing, real-time streaming, and stateful microservices. Micro-orchestration techniques, leveraging container schedulers and lightweight service meshes, facilitate fine-grained coordination of these disparate workloads. By dynamically tuning resource allocation, dependency resolution, and failure recovery, organizations achieve optimal throughput while maintaining architectural coherence. ITIL 4 Practitioner principles provide governance scaffolding, ensuring that micro-orchestration enhances operational efficiency without undermining compliance or stability.
Predictive Resource Contention and Proactive Scaling
Resource contention remains a perennial impediment to seamless deployments. Predictive modeling, grounded in historical utilization patterns and probabilistic simulations, anticipates contention hotspots and informs proactive scaling strategies. Dynamic provisioning of compute, storage, and network resources minimizes the latency and throughput variability that often plague high-velocity deployments. This anticipatory approach transforms reactive firefighting into strategic capacity orchestration, aligning operational performance with business-critical SLAs.
Intelligent Dependency Mapping and Decoupling
Complex deployments often involve intricate dependency graphs, encompassing microservices, shared libraries, and external APIs. Intelligent dependency mapping, leveraging graph analytics and service topology models, identifies critical coupling points, cyclic dependencies, and latent failure propagation paths. Decoupling strategies, informed by this intelligence, enable modular deployments with minimized inter-service friction. Such sophistication ensures that deployment cadence remains unimpeded by architectural entanglement while maintaining holistic system integrity.
Adaptive Configuration Management
Configuration drift remains an insidious source of deployment instability. Adaptive configuration management frameworks, employing declarative schemas and policy-driven automation, enforce consistency across environments. Real-time validation, drift detection, and automated remediation safeguard deployment fidelity while enabling rapid iteration. Integrating these practices with ITIL 4 guidance ensures that flexibility in deployment does not compromise governance, compliance, or systemic stability.
Cognitive Observers for Incident Mitigation
Cognitive observers, powered by machine learning, analyze continuous streams of operational data to identify subtle signals of impending failure. These systems correlate anomalies across metrics, logs, and traces, generating actionable insights for preemptive intervention. By embedding cognitive observers into deployment workflows, organizations achieve an anticipatory operational posture, where incidents are mitigated before they escalate, enhancing both reliability and customer trust.
Evolutionary Deployment Pipelines
Deployment pipelines are evolving from linear, rigid sequences into evolutionary constructs capable of adaptive reconfiguration. Dynamic branching, parallelized testing, and context-aware routing enable pipelines to respond to environmental conditions, workload variations, and emergent risks. This evolutionary design philosophy ensures that pipelines remain robust under fluctuating operational conditions, continuously optimizing throughput, quality, and risk management in alignment with strategic objectives.
Cross-Domain Collaboration Ecosystems
Deployment efficacy extends beyond technical prowess to the orchestration of cross-domain collaboration ecosystems. Integrating development, operations, security, and business stakeholders fosters a holistic understanding of deployment impact, risk, and value creation. Transparent communication channels, shared dashboards, and collaborative incident review practices cultivate a culture of collective responsibility. ITIL 4 Practitioner emphasizes that such ecosystems not only accelerate deployment cycles but embed strategic alignment and adaptive learning within organizational DNA.
Deployment Retrospective as an Illuminative Lens
Post-deployment retrospectives act as an illuminative lens, revealing the intricacies of operational orchestration. Far from perfunctory, these retrospectives scrutinize procedural efficacy, alignment with strategic objectives, and latent vulnerabilities. By dissecting deviations between planned outcomes and actual performance, teams gain unprecedented clarity into the nuances of deployment mechanics. This analytical lens fosters a discerning mindset, promoting vigilance and preemptive intervention in future endeavors.
Operational Contingency Analysis
An often-overlooked facet of post-deployment scrutiny is operational contingency analysis. This process involves mapping potential failure modes against realized outcomes, evaluating the efficacy of fallback mechanisms, and identifying gaps in resilience strategies. Such analytical rigor transforms reactive troubleshooting into proactive fortification, ensuring that subsequent deployments are better insulated against disruption. Contingency analysis integrates seamlessly with broader risk management frameworks, enhancing both tactical and strategic preparedness.
Cognitive Insights from User Behavior
User interactions post-deployment provide a rich substrate for cognitive insights. Behavioral analytics, session tracking, and engagement patterns reveal not only functional acceptance but also perceptual interpretations of service changes. By decoding these behavioral signals, organizations can calibrate deployments to maximize user satisfaction, minimize friction, and anticipate latent dissatisfaction before it crystallizes into operational incidents. Cognitive insights thus augment the post-deployment intelligence ecosystem, bridging the gap between technical efficacy and human experience.
Cross-Functional Synergies and Collaborative Debriefing
Deployments are rarely siloed phenomena; they involve multiple functional domains including development, operations, security, and business analysis. Collaborative debriefing sessions facilitate the crystallization of cross-functional synergies, allowing disparate teams to coalesce around shared lessons. Such debriefings catalyze collective cognition, enabling holistic process optimization that transcends the capabilities of any single function. Through structured dialogue and knowledge integration, organizations cultivate a symbiotic environment conducive to sustained operational excellence.
Process Resilience and Redundancy Engineering
A cardinal principle emerging from post-deployment analysis is the engineering of process resilience through redundancy. By identifying failure-prone junctures and embedding redundant safeguards, organizations create self-reinforcing operational architectures. Redundancy engineering mitigates the impact of unforeseen perturbations, ensuring continuity of service even under duress. This approach not only fortifies deployment reliability but also instills confidence among stakeholders, as service stability becomes demonstrably robust.
Emergent Pattern Recognition in Deployment Metrics
Advanced post-deployment analytics often reveal emergent patterns that are invisible to superficial monitoring. Temporal trends in incident occurrence, performance degradation clusters, and interdependent service anomalies provide a roadmap for targeted improvement. Pattern recognition, when integrated with predictive modeling, transforms reactive operations into anticipatory management. This foresight empowers teams to address potential disruptions before they manifest, creating a proactive deployment culture that is both agile and resilient.
Feedback Loops as Catalysts for Innovation
Structured feedback loops act as catalysts for innovative refinement. By continuously harvesting insights from users, technical teams, and business stakeholders, organizations can generate iterative enhancements that extend beyond mere corrective action. These loops cultivate an environment where experimentation, adaptation, and learning coalesce, converting post-deployment observations into actionable innovations. Feedback loops thus become engines of ingenuity, perpetually invigorating deployment practices with novel approaches and solutions.
Cognitive Load Management for Deployment Teams
The complexity of modern deployments imposes significant cognitive load on operational teams. Post-deployment review should therefore incorporate assessments of cognitive strain, task saturation, and decision fatigue. By understanding these human factors, organizations can redesign workflows, automate repetitive processes, and optimize task allocation to alleviate operational stress. This attention to human-centric dynamics not only enhances team performance but also reduces the risk of error, elevating overall deployment quality.
Strategic Realignment Through Deployment Insights
Insights derived from post-deployment activities often inform broader strategic realignment. Patterns of inefficiency, emergent user requirements, and systemic vulnerabilities can precipitate adjustments in long-term planning, technology roadmaps, and resource allocation. By leveraging deployment intelligence in strategic deliberations, organizations convert operational learnings into enterprise-wide value, ensuring that tactical experiences reinforce overarching objectives.
Scenario Simulation and Predictive Modeling
Predictive modeling and scenario simulation are invaluable adjuncts to post-deployment evaluation. By extrapolating from real-world data, organizations can simulate potential contingencies, stress-test new features, and anticipate emergent risks. This modeling not only informs immediate remediation but also enhances strategic foresight, enabling the organization to preemptively optimize future deployments. In essence, simulation transforms retrospective learning into proactive strategic advantage.
Knowledge Capitalization Through Structured Documentation
Structured documentation is the vessel through which post-deployment knowledge becomes enduring organizational capital. Comprehensive runbooks, decision logs, and process blueprints capture the tacit intelligence of deployment experiences. This codification ensures that expertise is not ephemeral but transmutable across teams and temporal boundaries. The cumulative effect is a knowledge-rich ecosystem where each deployment incrementally strengthens organizational capability.
Metrics Fusion: Integrating Quantitative and Qualitative Insights
The integration of quantitative and qualitative insights is pivotal to a comprehensive post-deployment review. While numerical KPIs quantify operational performance, qualitative observations provide context, nuance, and interpretive depth. Metrics fusion creates a multidimensional understanding of deployment outcomes, enabling decision-makers to identify subtle inefficiencies, emerging opportunities, and latent risks that would otherwise remain obscured.
Cultural Reinforcement Through Recognition and Knowledge Sharing
Post-deployment review is also a cultural instrument. Celebrating successes, acknowledging challenges, and disseminating insights engender a culture of continuous learning. Knowledge sharing not only democratizes expertise but also fosters accountability, collaboration, and engagement. When teams witness the tangible impact of their contributions, morale and performance are simultaneously elevated, reinforcing a virtuous cycle of improvement.
Adaptive Governance and Policy Refinement
Deployment experiences often expose areas where governance frameworks require adaptation. Policies regarding access control, change management, and operational thresholds can be recalibrated to reflect empirical insights. Adaptive governance ensures that organizational regulations remain aligned with evolving operational realities, maintaining both compliance and efficiency. By iteratively refining policies, organizations transform post-deployment review into a mechanism for systemic agility.
Incident Taxonomy and Root Cause Taxonomy Development
Post-deployment review provides the raw material for developing comprehensive incident and root cause taxonomies. By categorizing incidents according to causality, severity, and recurrence, organizations can identify systemic weaknesses and recurring vulnerabilities. This taxonomy facilitates trend analysis, prioritization of corrective action, and refinement of preventive strategies, establishing a rigorous framework for long-term resilience.
Operational Symbiosis: Aligning Teams, Tools, and Processes
The post-deployment phase offers a unique opportunity to harmonize teams, tools, and processes into operational symbiosis. By analyzing interactions between disparate system components and cross-functional teams, organizations can identify bottlenecks, streamline workflows, and optimize resource allocation. Operational symbiosis enhances efficiency, reduces friction, and fosters a coherent ecosystem where all elements function synergistically.
Conclusion
Mastering deployment management through ITIL 4 Practitioner is more than a technical necessity—it is a strategic advantage. Across planning, execution, monitoring, and post-deployment improvement, the principles of collaboration, automation, risk awareness, and continual learning guide organizations toward predictable, value-driven outcomes. By embracing these practices, teams reduce errors, accelerate release cycles, and enhance overall service quality while maintaining alignment with business objectives.
The journey does not end with a single deployment; it continues through reflection, feedback, and iterative improvement. Organizations that embed ITIL 4 Practitioner principles cultivate resilience, agility, and a culture of excellence, transforming deployment management into a source of competitive advantage. Ultimately, the combination of structured processes, modern tools, and a proactive mindset ensures that every deployment delivers meaningful value, strengthens stakeholder trust, and supports the ongoing evolution of digital services.
Top ITIL Exams
- ITILFND V4 - ITIL 4 Foundation
- ITIL 4 Specialist Create Deliver and Support - ITIL 4 Specialist Create, Deliver and Support
- ITILFND V5 - ITIL Foundation (Version 5)
- ITIL4 Specialist - Monitor and Support and Fulfil - ITIL4 Specialist: Monitor, Support and Fulfil
- ITIL 4 Specialist High-Velocity IT - ITIL 4 Specialist High-Velocity IT
- ITIL 4 Leader Digital and IT Strategy - ITIL 4 Leader Digital and IT Strategy
- ITIL 4 Specialist Collaborate Assure and Improve - ITIL 4 Specialist: Collaborate, Assure and Improve
- ITIL4 Practitioner Monitoring and Event Management - ITIL4 Practitioner Monitoring and Event Management