Product Screenshots
Product Reviews
I love pass4sure
"I love pass4sure GASF GASF learning tools, as they made me a qualified expert. I was very confused about my GASF GASF qualification but I got a lot confidence when I started taking help from Pass4sure materials. I just simply love their Certification GASF GASF exam study manual, which is so magnificently developed that it improves the understanding of a candidate. During my period of interaction, I found these tools very useful and quite interesting, as they teach everything very well.
Ricky Ambrose"
Pass4sure - my first choice for professional certification
"Pass4sure is my first choice to attain a professional certification. I have used these exam preparatory solutions before and they provided me a great deal of knowledge. Not only that, I also passed my GASF GASF exam with the help of Pass4sure study materials. With my wonderful experience, Pass4sure study tools are on the top of my priority list. Pass4sure GIAC GASF materials were amazing, as they made my certification exam go easy. I recommended the same to my several friends and all of them are now a certified Certification GASF GASF professional. Thanks Pass4sure for learning my trust and helping me pass.
Melissa Abey"
Pass4sure is a helpful source to pass an exam
"I passed GASF exam on 5/6/2011. Pass4sure GIAC GASF exam kit was a very helpful resource to me while I prepared for my GASF exam. I was particularly benefitted by the contents pass4sure provided. Because I have to spend a lot of time in commuting to the office every day, pass4sure saved me a lot of time on preparing for the exam. I found pass4sure study guide very useful because it always points out where the key point is in each knowledge area. This saves me a lot of time from trying to identify the most important parts in the subject.
Thanks to all the pass4sure developers!
Frank L."
Love Pass4sure
"I love Pass4sure because when I studies for GASF GASF exam using the products provided, I realized that it was made just for me. The questions and answers for GIAC GASF exam are compiled by experts and are very similar to the actual ones on the exam. I had the option of buying hard copies to make things even easier. I could easily download the test engine on my PC. Plus I passed Certification GASF GASF exam with an incredible score! This is Charlotte Briggs."
Pass4sure - an easy way to learn
"Pass4sure GASF exam material is easy to learn and it is so detailed that it helped me pass my certification in the first attempt. Before pass4sure, I never imagined that passing GASF certification will be too easy and then things got clearer, as I used Pass4sure. My first experience with pass4sure was very commendable, as these helping materials explained each concept to me very well and in detail. Therefore, when the questions related to those concepts appeared in my exam, I had no problem in addressing them and I readily answered to all the problems. I am much grateful to pass4sure team, which made a qualified expert. Thank you.
Alberta Scott"
Frequently Asked Questions
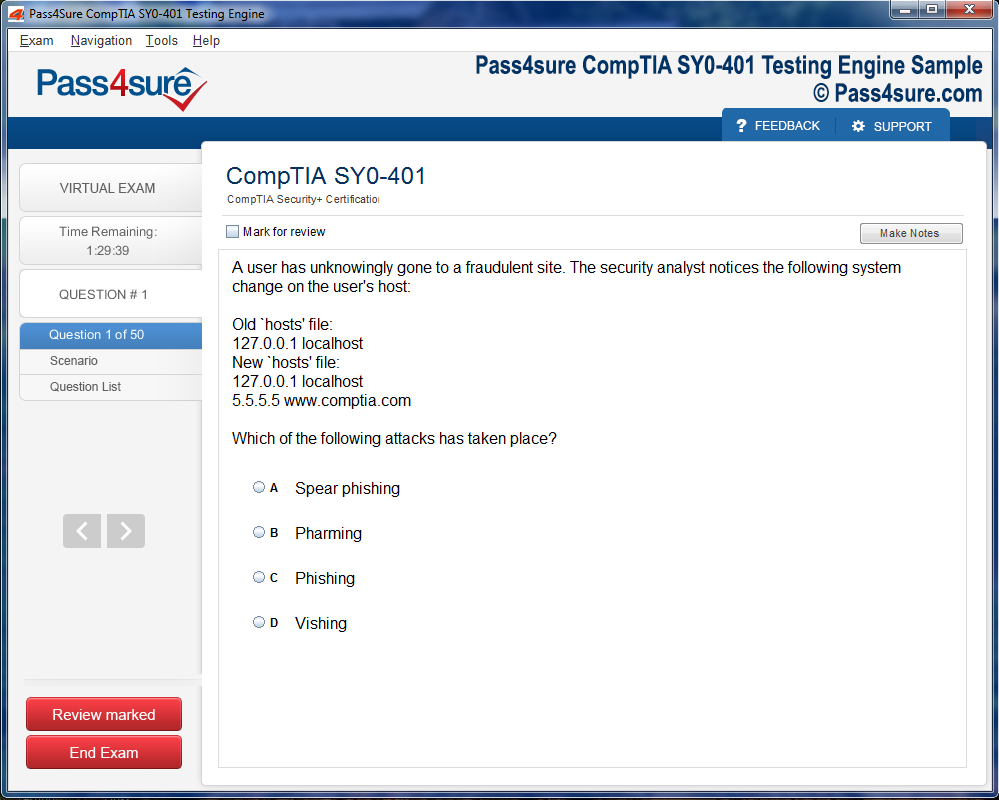
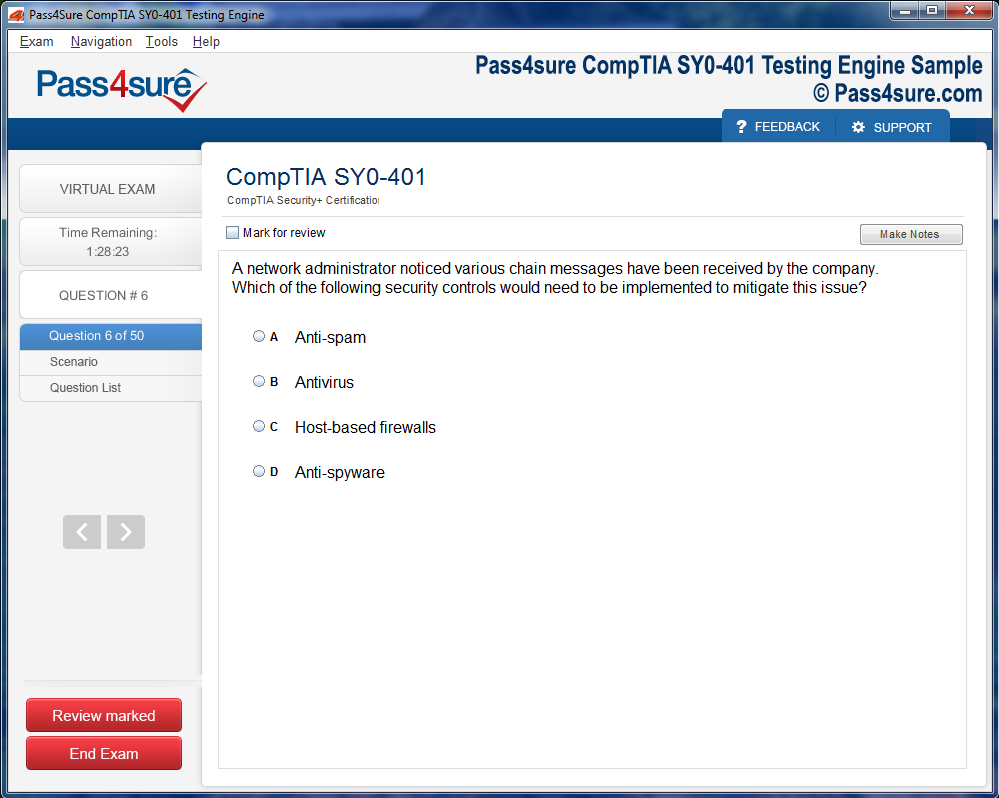
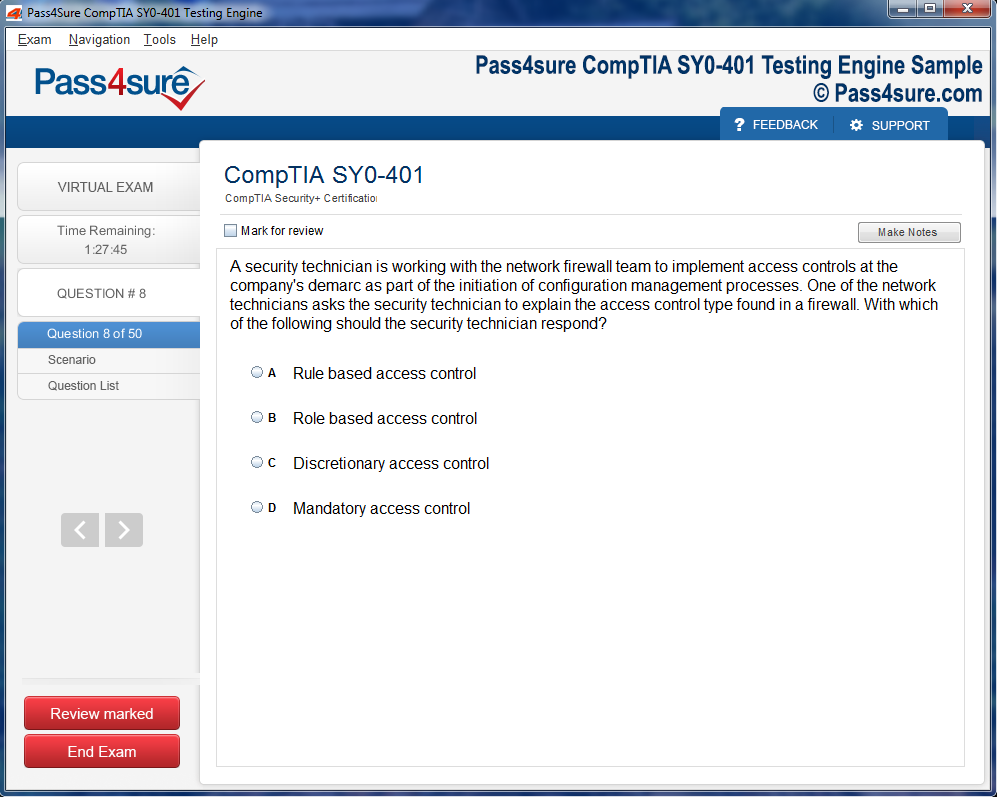
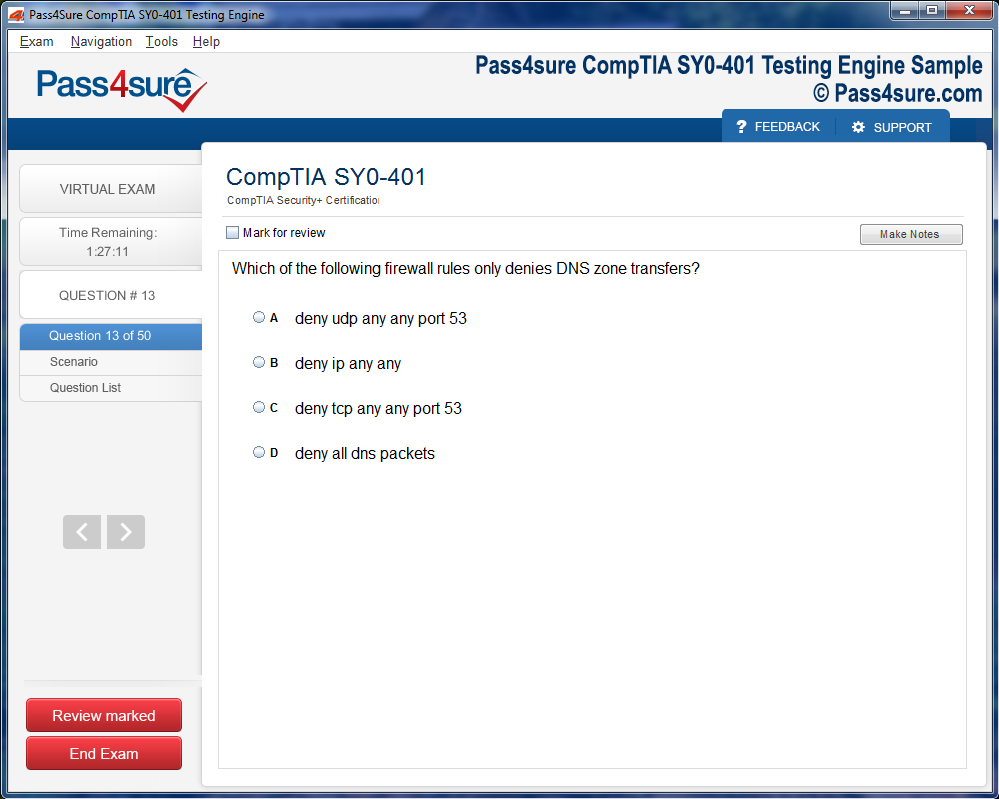
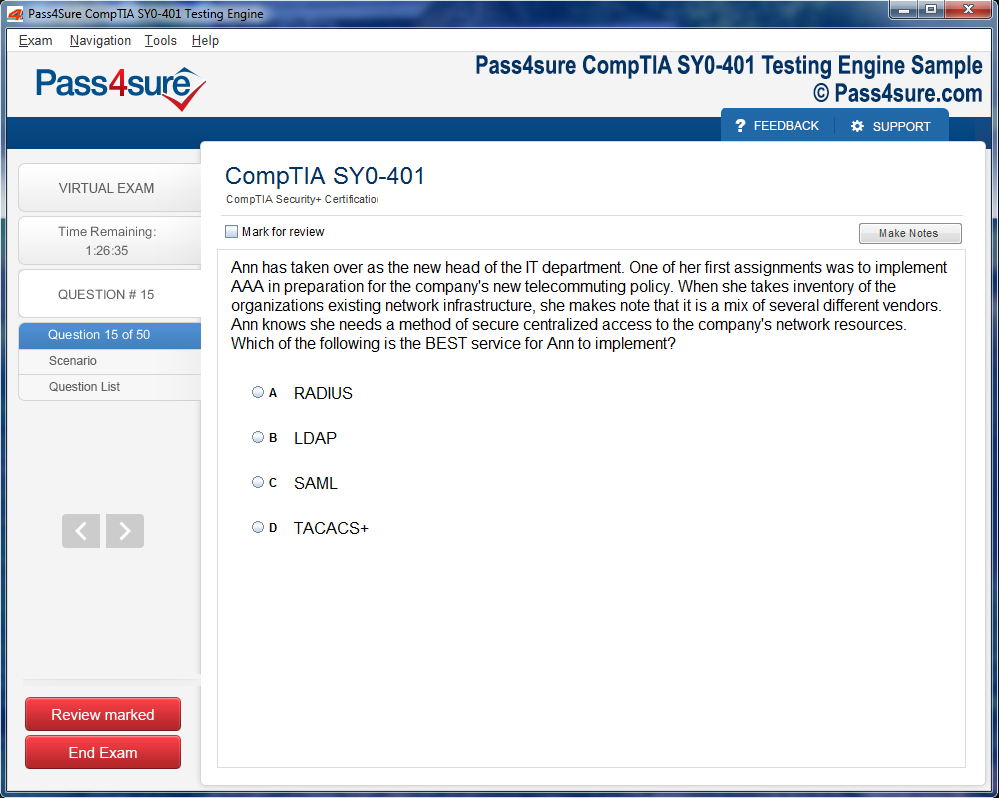
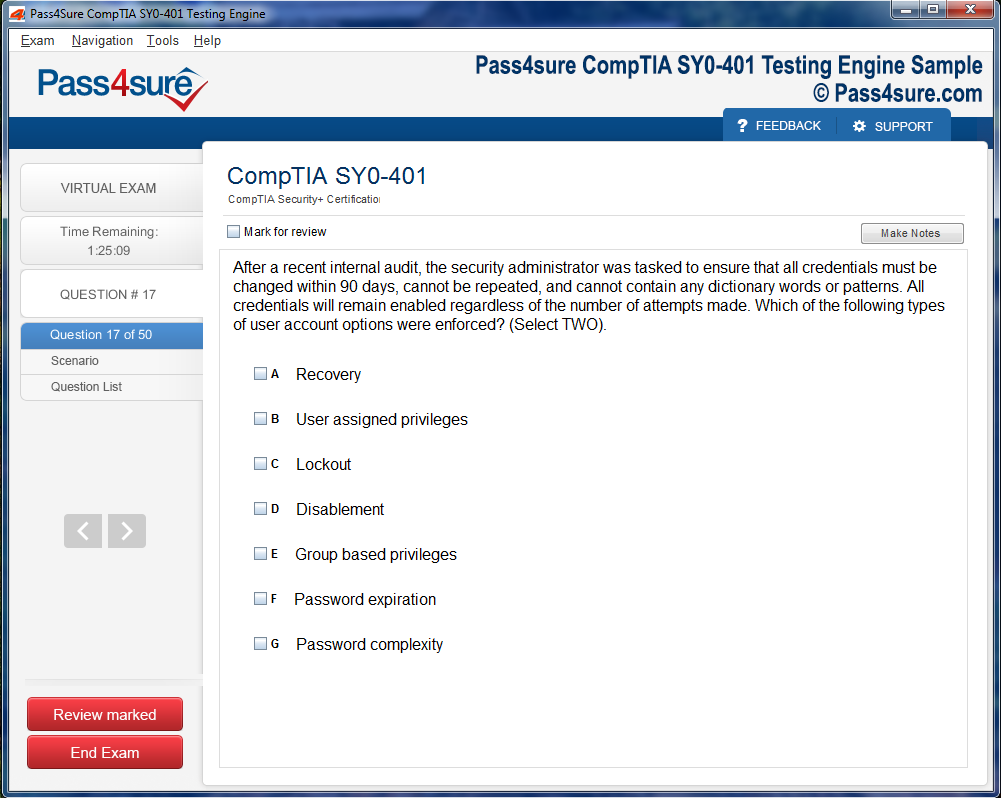
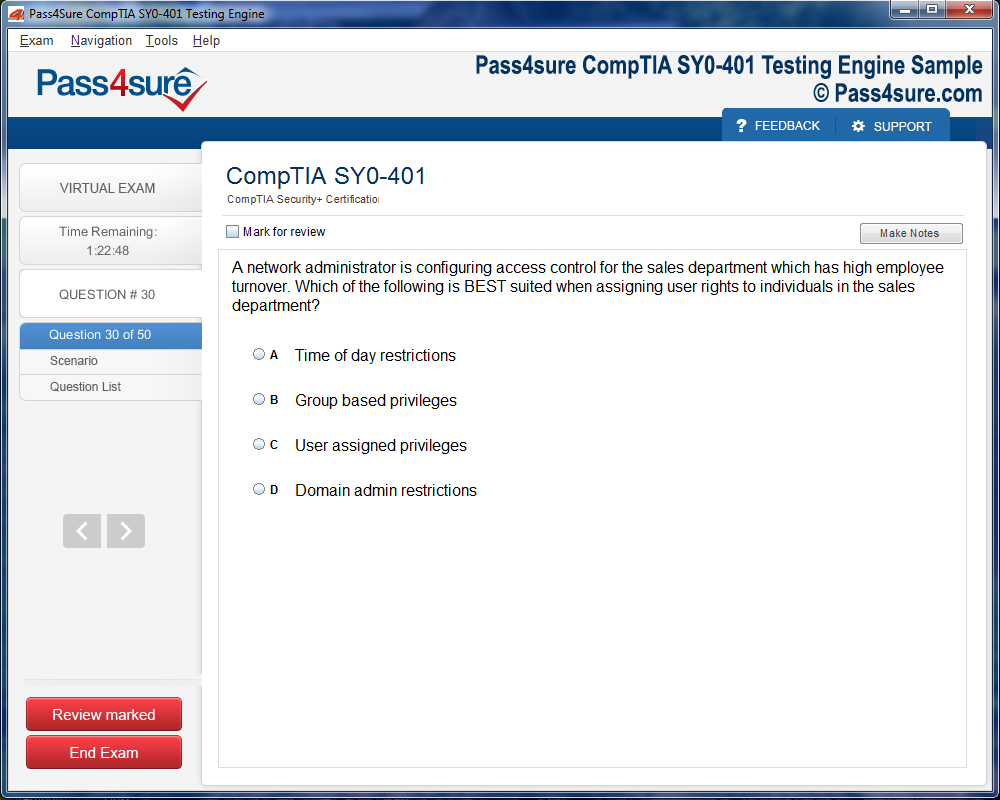
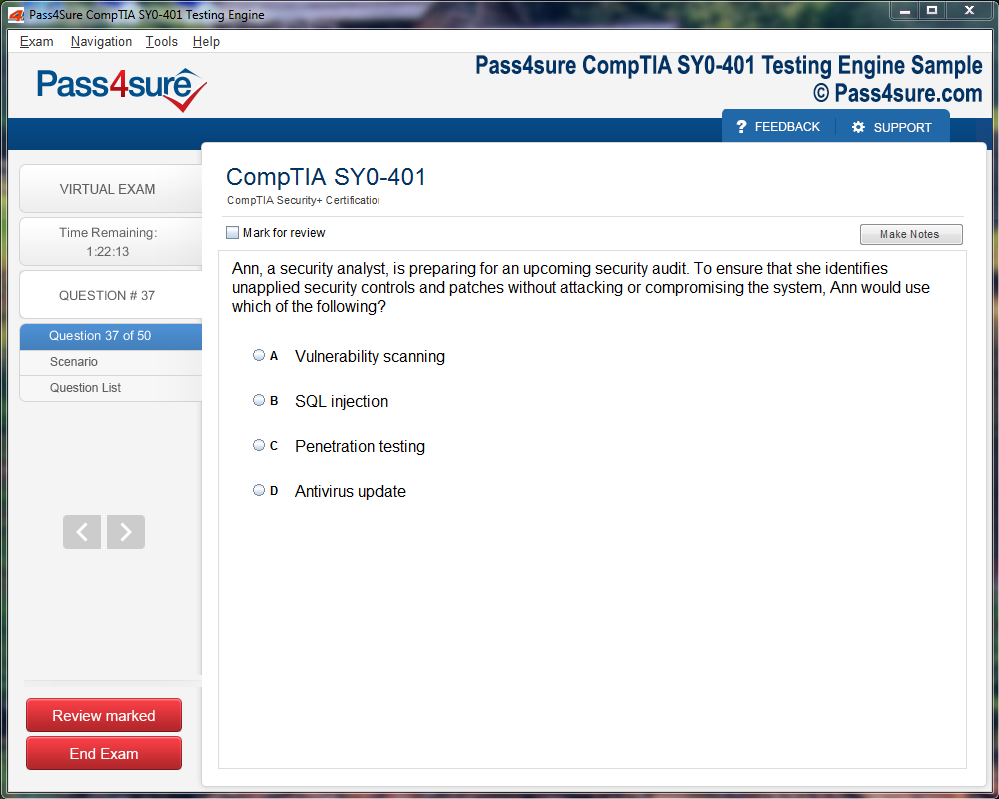
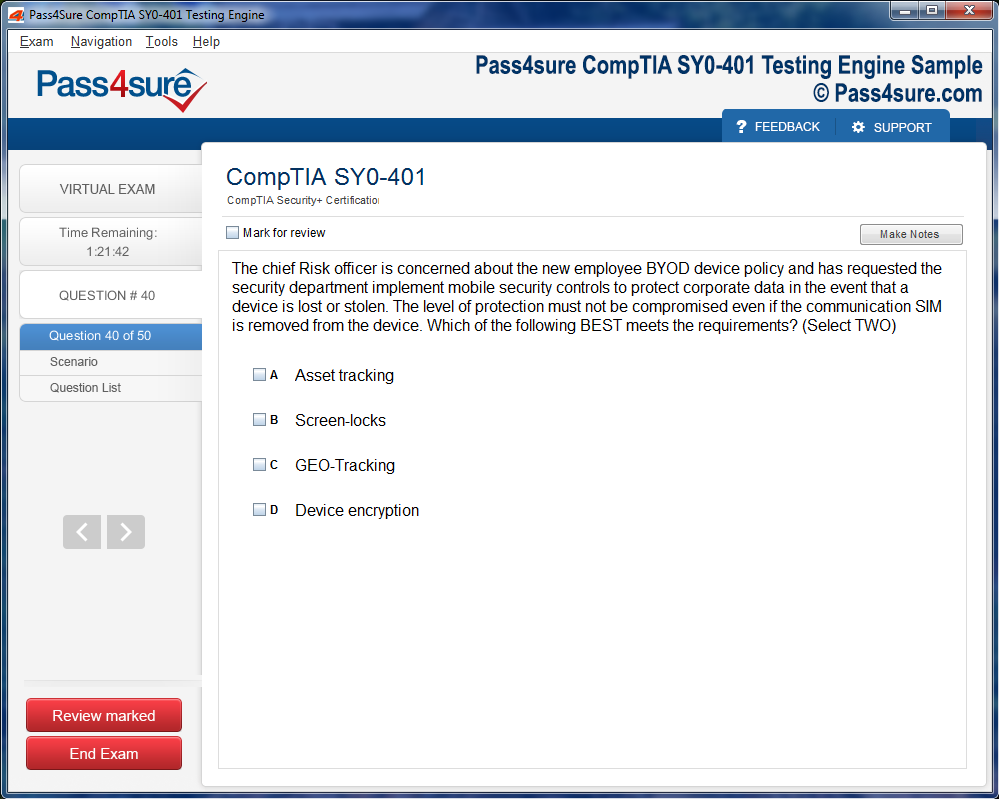
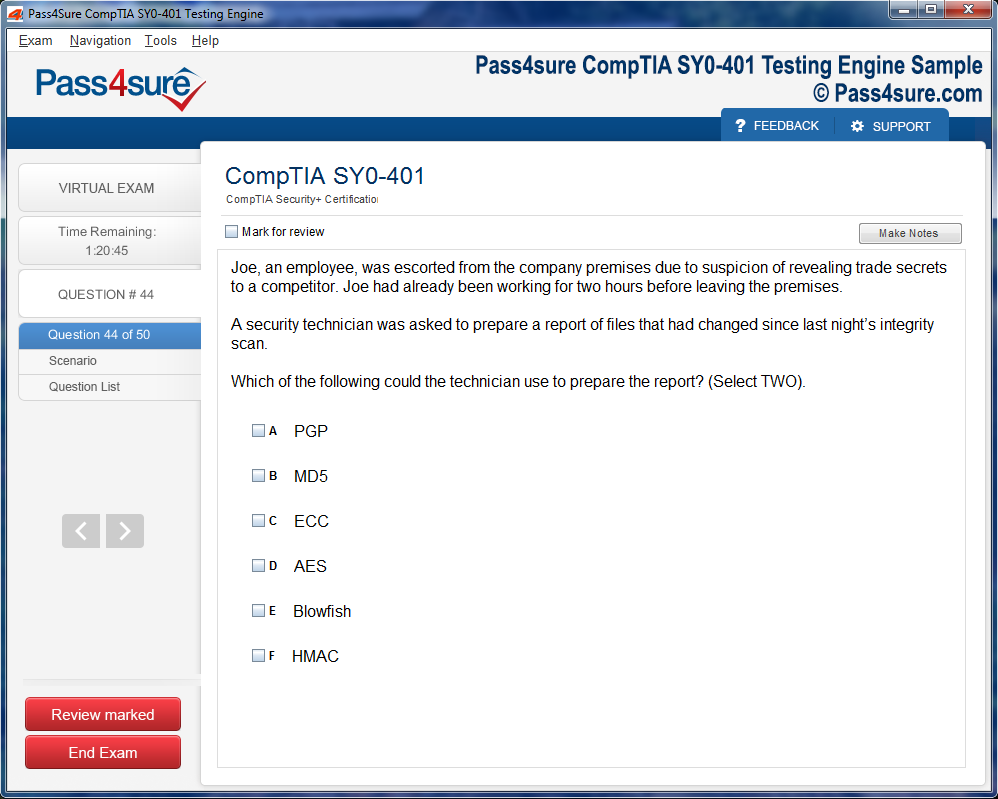
How does your testing engine works?
Once download and installed on your PC, you can practise test questions, review your questions & answers using two different options 'practice exam' and 'virtual exam'. Virtual Exam - test yourself with exam questions with a time limit, as if you are taking exams in the Prometric or VUE testing centre. Practice exam - review exam questions one by one, see correct answers and explanations.
How can I get the products after purchase?
All products are available for download immediately from your Member's Area. Once you have made the payment, you will be transferred to Member's Area where you can login and download the products you have purchased to your computer.
How long can I use my product? Will it be valid forever?
Pass4sure products have a validity of 90 days from the date of purchase. This means that any updates to the products, including but not limited to new questions, or updates and changes by our editing team, will be automatically downloaded on to computer to make sure that you get latest exam prep materials during those 90 days.
Can I renew my product if when it's expired?
Yes, when the 90 days of your product validity are over, you have the option of renewing your expired products with a 30% discount. This can be done in your Member's Area.
Please note that you will not be able to use the product after it has expired if you don't renew it.
How often are the questions updated?
We always try to provide the latest pool of questions, Updates in the questions depend on the changes in actual pool of questions by different vendors. As soon as we know about the change in the exam question pool we try our best to update the products as fast as possible.
How many computers I can download Pass4sure software on?
You can download the Pass4sure products on the maximum number of 2 (two) computers or devices. If you need to use the software on more than two machines, you can purchase this option separately. Please email sales@pass4sure.com if you need to use more than 5 (five) computers.
What are the system requirements?
Minimum System Requirements:
- Windows XP or newer operating system
- Java Version 8 or newer
- 1+ GHz processor
- 1 GB Ram
- 50 MB available hard disk typically (products may vary)
What operating systems are supported by your Testing Engine software?
Our testing engine is supported by Windows. Andriod and IOS software is currently under development.
Certified in GIAC Advanced Smartphone Forensics (GASF)
In an era where digital pervasiveness is nearly axiomatic, the discipline of smartphone forensics has transcended traditional paradigms. Mobile devices no longer merely serve as conduits for communication; they are repositories of behavioral minutiae, repositories of ephemeral and persistent data, and integral nodes in sprawling digital ecologies. Experts in GASF Advanced Smartphone Forensics occupy a vantage point that requires both meticulous technical prowess and a prescient awareness of the ontological shifts in data landscapes. The professional is compelled to synthesize granular investigative techniques with macroscopic foresight, mapping not only what exists within a device but also the invisible vectors by which digital traces propagate across virtual and corporeal spaces.
Artificial Intelligence as a Cognitive Amplifier in Forensic Inquiry
The integration of artificial intelligence and machine learning within smartphone forensics signifies a paradigm shift akin to the advent of microscopic analysis in biological sciences. AI algorithms, particularly those employing deep learning architectures, function as cognitive amplifiers—detecting patterns, anomalies, and correlations that would elude conventional human inspection. These methodologies facilitate predictive analyses, enabling practitioners to anticipate potential data obfuscation strategies employed by adversaries. Yet, despite the algorithmic sophistication, human discernment remains indispensable. Contextual interpretation, ethical reasoning, and strategic judgment are dimensions of inquiry that cannot be wholly codified into computational paradigms. In this interplay, AI becomes a symbiotic instrument rather than a replacement, augmenting human acumen and extending the analytical bandwidth of the forensic professional.
Cryptographic Obstacles and the Art of Subtle Data Extraction
The proliferation of encrypted communication channels, ephemeral messaging, and sophisticated anonymization protocols constitutes a formidable labyrinth for contemporary forensic investigators. Platforms offering end-to-end encryption obscure evidentiary content, while ephemeral messaging erases transactional traces with temporal precision. Navigating this cryptographic terrain necessitates not only technical dexterity but also judicious adherence to legal and ethical frameworks. Forensic specialists employ a repertoire of strategies—from memory forensics and volatile data capture to metadata reconstruction—to circumvent obfuscation while maintaining procedural integrity. This delicate balancing act underscores a nuanced epistemology of forensic inquiry: knowledge is sought without transgressing the normative boundaries of privacy and legality, rendering the investigation both rigorous and morally tenable.
Ecosystemic Cognition: Smartphones Within Interconnected Digital Networks
The ontological scope of smartphone forensics extends far beyond individual devices. Modern investigative praxis must consider smartphones as nodes within intricate ecosystems encompassing IoT devices, wearable technology, vehicular telemetry, and smart home infrastructures. The interconnectivity of these devices engenders a lattice of digital imprints that can elucidate behavioral patterns with unprecedented granularity. Certified professionals develop methodologies to traverse these interconnected systems, reconstructing holistic narratives from ostensibly disparate datasets. The capacity to synthesize multisystem data not only enhances evidentiary completeness but also cultivates an anticipatory understanding of digital interactions—a predictive acuity that is increasingly essential in high-stakes investigations.
Cyber Threat Topography and the Imperative of Forensic Vigilance
Emergent cyber threats, including polymorphic malware, ransomware, and clandestine remote manipulations, redefine the operational imperatives of smartphone forensics. The professional must maintain both a defensive and investigative posture, cognizant of the tactics, techniques, and procedures employed by adversaries seeking to subvert data integrity. Understanding the lifecycle of malicious interventions—from injection vectors to persistence mechanisms—enables the forensic expert to reconstruct events with forensic precision. This awareness is not solely reactive; it informs proactive strategies, anticipating adversarial maneuvers and fortifying investigative methodologies against unforeseen contingencies.
Pedagogical Continuity and the Culture of Lifelong Forensic Mastery
Professional development in smartphone forensics is an iterative continuum rather than a terminal accomplishment. Certification in GASF Advanced Smartphone Forensics represents a formalized recognition of expertise, yet the rapidity of technological evolution demands relentless intellectual engagement. Practitioners immerse themselves in symposia, workshops, and scholarly discourse, integrating empirical research with emergent practice. Collaboration with interdisciplinary cohorts—spanning cybersecurity, legal adjudication, behavioral analysis, and digital anthropology—enriches both methodological rigor and ethical comprehension. This culture of lifelong learning ensures that expertise is not static but dynamically recalibrated to the ever-changing topography of digital threats and opportunities.
Interdisciplinary Synergy in Investigative Endeavors
Modern investigative landscapes increasingly necessitate interdisciplinary cooperation. Forensic specialists contribute a distinct epistemic perspective to teams composed of cyber threat analysts, legal professionals, and behavioral scientists. Their role is to articulate the evidentiary significance of mobile-derived data, contextualize its implications within broader investigative frameworks, and anticipate methodological pitfalls. This integrative model not only enhances evidentiary fidelity but also ensures procedural coherence across the investigative continuum. The capacity to navigate interdisciplinary dialogues with clarity and authority underscores a critical competency in advanced forensic practice.
Ethical Stewardship and the Custodianship of Digital Truth
As forensic methodologies grow in sophistication, the ethical responsibilities of practitioners become proportionally magnified. Professionals must negotiate the tensions between evidentiary acquisition, privacy preservation, and legal compliance. Ethical stewardship entails rigorous documentation, judicious interpretation, and an unwavering commitment to procedural transparency. The forensic expert is not merely a technician but a custodian of digital truth, entrusted to illuminate hidden realities without succumbing to investigative hubris or methodological compromise. This moral dimension is inseparable from technical proficiency, shaping the contours of professional identity and public trust.
Adaptive Methodologies in the Face of Technological Flux
The velocity of technological innovation mandates a corresponding agility in forensic methodology. Emerging device architectures, novel data storage paradigms, and adaptive security protocols require professionals to continuously recalibrate investigative strategies. Flexibility, creativity, and anticipatory reasoning become operative imperatives, enabling practitioners to respond effectively to unforeseen challenges. By integrating adaptive techniques with foundational principles of data integrity and analytical rigor, forensic specialists maintain investigational efficacy even amidst systemic disruption.
AI-Enhanced Behavioral Reconstruction and Predictive Forensics
Beyond pattern recognition, AI facilitates advanced behavioral reconstruction, enabling the forensic professional to infer digital behavioral trajectories with heightened precision. Predictive forensics leverages historical datasets, temporal sequencing, and anomaly detection to forecast potential adversarial actions or reconstruct complex event chains. This confluence of algorithmic sophistication and forensic reasoning transforms investigation from a purely retrospective endeavor into a dynamic anticipatory practice. Certified experts exploit these capabilities to derive actionable insights, guiding investigative decisions with both evidentiary and strategic acuity.
Cloud Constellations and Data Stratification
The migration of data into cloud infrastructures introduces both opportunity and complexity for smartphone forensics. Multi-tiered storage, cross-platform synchronization, and ephemeral caches create stratified data environments that require nuanced extraction techniques. Professionals must navigate authentication barriers, jurisdictional constraints, and data integrity challenges, constructing coherent narratives from fragmented repositories. Mastery of cloud forensics entails both technical dexterity and an awareness of legal topography, ensuring that reconstructed datasets retain both evidentiary weight and procedural legitimacy.
Malware Epistemology and Forensic Countermeasures
Sophisticated malware represents a deliberate epistemic obfuscation, designed to distort, delete, or exfiltrate sensitive information. Understanding malware requires forensic professionals to adopt a dual lens: technical deconstruction and behavioral anticipation. Reverse engineering, sandbox analysis, and memory forensics illuminate the mechanisms by which malicious code interacts with device architecture. This knowledge allows investigators to anticipate adversarial strategies, implement mitigation protocols, and reconstruct compromised datasets with methodical precision. Malware epistemology is thus both an investigative and defensive discipline, requiring continuous adaptation to evolving threat vectors.
Data Provenance and the Semiotics of Digital Evidence
Every digital artifact carries with it a provenance, a traceable lineage that encodes the circumstances of its creation, modification, and transmission. Advanced forensic analysis extends beyond content extraction to semiotic interpretation—deciphering the latent meanings embedded within timestamps, metadata, and network interactions. Certified professionals cultivate an interpretive acumen that transforms raw data into narrative intelligence, reconstructing sequences of action, intent, and consequence. This semiotic dimension imbues forensic practice with both depth and nuance, enhancing the evidentiary value of seemingly mundane digital traces.
Cross-Platform Integrative Analysis
As smartphones become nodes within broader technological constellations, cross-platform forensic integration is increasingly indispensable. Synchronization between mobile devices, wearables, cloud services, and IoT ecosystems demands methodological coherence and analytical precision. Certified experts develop integrative frameworks that consolidate heterogeneous datasets, identify interdependencies, and elucidate behavioral continuity. This multidimensional perspective transforms fragmented digital landscapes into comprehensive, interpretable narratives, enabling investigators to understand both micro-level interactions and macro-level patterns.
Modern smartphones are labyrinthine constructs of hardware and software, where circuits and code intermingle in astonishing intricacy. Beneath the polished interface lies a concatenation of microprocessors, coprocessors, memory caches, and sensor arrays, all orchestrating data acquisition and storage. Understanding these hidden strata is pivotal for a forensic specialist. Each component—be it the system-on-chip, NAND flash memory, or baseband processor—serves as a potential repository for digital traces. The analyst must cultivate an intimate familiarity with these elements to decipher not only the presence of data but also its provenance and integrity.
Embedded ecosystems present additional complexity. Operating systems mediate interactions among applications, sensors, and peripheral hardware. Variations in kernel architecture, sandboxing protocols, and inter-process communications create idiosyncratic storage patterns that challenge standardized extraction methodologies. A profound grasp of these subtleties enables forensic professionals to navigate devices with surgical precision, retrieving information without compromising evidentiary validity.
The Labyrinth of Encrypted Data
Encryption is no longer an optional feature; it is a pervasive safeguard that fortifies the sanctity of mobile data. Full-disk encryption, secure enclaves, and hardware-backed key storage have transformed smartphones into fortified citadels. Forensic analysts confront these protections with a blend of ingenuity and technical acumen. Successful decryption or bypass demands a rigorous understanding of cryptographic frameworks, key management strategies, and potential vulnerabilities.
This arena is not merely a contest of software but also a confrontation with physics and timing. Differential analysis, voltage probing, and side-channel assessments may be employed in high-stakes investigations. Each method must be executed with meticulous care, as even minor procedural errors can render data irretrievable or inadmissible in judicial proceedings. Mastery of encrypted landscapes is a defining trait of the certified professional, distinguishing mere operators from true digital archeologists.
Navigating Cloud Interstices and Remote Repositories
The paradigm of data residence has shifted. Increasingly, digital traces escape the confines of local storage, migrating to cloud platforms in fragmented, encrypted forms. Forensic practitioners must engage with these interstices, orchestrating access to remote repositories while adhering to legal and ethical strictures. Techniques include lawful subpoena acquisition, API-based extraction, and analysis of synchronization logs that may expose deleted or modified content.
The challenge lies not solely in retrieval but in reconstructing coherent narratives from dispersed fragments. Cloud services often introduce temporal discrepancies, redundant storage, and obfuscation layers, demanding analytic strategies that balance thoroughness with efficiency. A certified analyst must cultivate patience, dexterity, and a methodical approach to reconstructing events from these digital palimpsests.
Forensic Methodologies: From Acquisition to Interpretation
Acquisition is the fulcrum upon which all subsequent analysis pivots. Methods vary from physical extraction of raw memory blocks to logical acquisition of file systems and application data. Each method carries trade-offs in completeness, invasiveness, and forensic integrity. Decision-making here requires both experience and foresight, as the wrong choice may foreclose opportunities to recover crucial evidence.
Interpretation transforms raw data into intelligible narratives. Analysts cross-reference communication logs, GPS traces, and metadata to elucidate behavioral patterns. Temporal correlation is a powerful tool: aligning timestamps across applications can reveal previously hidden interactions or coordinated activity. The narrative is seldom linear; instead, it resembles a multidimensional tapestry where minor threads may illuminate major developments.
Investigative Creativity and Analytical Dexterity
Forensics is as much an art as it is a science. Beyond technical proficiency, investigators must cultivate creativity to hypothesize hidden behaviors, anticipate obfuscation tactics, and discern subtle anomalies. A deleted message may signal concealment, yet its implications are only decipherable through careful contextual analysis.
Pattern recognition, anomaly detection, and inferential reasoning coalesce in this cognitive exercise. Analysts often construct digital heuristics, anticipating the methods by which data might have been modified, masked, or destroyed. This mental agility is what separates routine examination from groundbreaking discovery.
Multi-Device Correlation and Cross-Platform Synthesis
Modern investigations rarely involve isolated devices. Smartphones are nodes within expansive digital networks, interacting with tablets, laptops, IoT devices, and cloud repositories. Extracting a single device’s data offers only a partial narrative. Certified analysts synthesize findings across multiple sources, identifying correlations, conflicts, and patterns that might otherwise remain invisible.
This cross-platform synthesis is particularly critical in complex investigations such as cyberstalking, financial fraud, or intellectual property misappropriation. By integrating diverse datasets, analysts generate comprehensive insights, reconstructing activity timelines and revealing inter-device dependencies that illuminate the broader scope of an event.
Adapting to Emerging Technologies
The landscape of smartphone forensics is in perpetual flux. Artificial intelligence, machine learning, and edge computing redefine both the types of data collected and the techniques necessary for extraction. Predictive algorithms can detect subtle behavioral deviations, while machine learning models can classify vast quantities of unstructured data with unprecedented speed.
Simultaneously, the proliferation of IoT devices introduces new evidence vectors. Wearables, smart home hubs, and connected automobiles often synchronize with smartphones, generating logs and metadata that are invaluable in investigations. Certified professionals must remain vigilant, continuously updating their knowledge to navigate this dynamic ecosystem effectively.
Legal and Ethical Imperatives
Legal compliance is the bedrock of admissible evidence. Forensic analysts operate under stringent frameworks, balancing investigative diligence with civil liberties and ethical standards. Unauthorized access, improper chain-of-custody handling, or procedural lapses can invalidate findings or expose the analyst to legal jeopardy.
Certified professionals internalize these imperatives, integrating procedural rigor into every stage of investigation. Documentation, evidence handling, and transparent methodology ensure both credibility in court and integrity in practice. Ethical foresight complements technical mastery, forming the dual pillars of responsible forensic expertise.
Tools and Techniques in Advanced Smartphone Forensics
Delving into the realm of smartphone forensics necessitates a meticulous blend of technical acumen, investigative methodology, and the strategic deployment of sophisticated instruments. In the domain of GASF Advanced Smartphone Forensics, practitioners recognize that understanding the conceptual scaffolding of data recovery constitutes merely a fraction of the challenge; the remaining rigor lies in the precise orchestration of extraction techniques and analytical methodologies. Contemporary mobile devices have metamorphosed into labyrinthine ecosystems, incorporating multiple storage strata, encrypted partitions, and perpetually evolving operating systems. Forensic specialists must navigate these complexities while upholding the sanctity of data integrity and evidentiary admissibility.
The foundational step in any forensic inquiry entails an intimate comprehension of the hardware and software topography. Modern smartphones present heterogeneous storage matrices—internal flash memory, removable SD modules, SIM cards, and cloud synchronization repositories. Each vector mandates discrete extraction strategies, each fraught with potential pitfalls. Certified professionals systematically interrogate these components, employing a combination of patience, forensic discipline, and technical sagacity to ensure that evidence is harvested without compromise. This procedural rigor extends to understanding chipset architectures, file system hierarchies, and the idiosyncrasies of various mobile operating systems.
Physical extraction instruments constitute the backbone of advanced forensic praxis. These devices facilitate direct engagement with hardware, retrieving raw binary data otherwise obscured from conventional access. Unlike logical extractions, which interface with the device’s operating system and are confined to user-visible content, physical methods penetrate deeper strata, uncovering deleted artifacts, latent partitions, and vestiges of system logs. Skilled practitioners discern the precise applicability of physical versus logical extractions, calibrating their approach in alignment with investigative imperatives. The nuanced understanding of these modalities allows professionals to recover data that might otherwise be irrevocably lost, preserving its authenticity for legal scrutiny.
Logical extraction tools operate in tandem with physical methodologies, granting access to user-facing data such as messaging archives, call logs, contacts, and application-specific repositories. While logical extractions do not typically expose deleted files, they provide immediate visibility into the user’s recent behavioral footprint. By integrating both extraction paradigms, forensic experts can construct a panoramic reconstruction of device activity, elucidating both explicit actions and subtle, concealed behaviors. This dual-pronged strategy ensures a holistic evidentiary capture that balances thoroughness with operational efficiency.
Navigating Encryption and Security Obstacles
A defining challenge in modern smartphone forensics is circumventing encryption and access controls. Contemporary devices deploy formidable security mechanisms, including biometric authentication, full-disk encryption, and ephemeral application-level protections. Certified GASF professionals possess both the technical acumen and legal discernment to navigate these obstructions. Techniques may involve the deployment of specialized decryption software, forensic-grade hardware interfaces, or memory acquisition strategies designed to preserve data fidelity. Each intervention is calculated to avoid corruption or contamination of evidence, ensuring legal defensibility in subsequent proceedings.
Proficiency in decryption techniques also entails an appreciation for cryptographic principles. Understanding block ciphers, key management schemas, and hash validation is integral to discerning when and how data can be extracted. Forensic specialists leverage this knowledge to target partitions, reconstruct fragmented file structures, and trace residual artifacts across encrypted environments. The interplay between cryptanalysis and practical extraction embodies the intellectual rigor that distinguishes advanced smartphone forensics from rudimentary data recovery operations.
Analytical Methodologies and Data Interpretation
Extraction represents only the preliminary phase; the true forensic endeavor lies in sophisticated data interpretation. Once acquired, data must be parsed, contextualized, and correlated to reveal meaningful narratives. Analysts examine temporal sequences, reconstruct deleted communications, and identify recurring motifs within user activity. Advanced parsing algorithms facilitate rapid sifting through voluminous datasets, highlighting anomalies, behavioral patterns, and investigative touchpoints of significance. Certified professionals synthesize these findings with investigative reasoning, producing insights that transcend mere digital footprints to inform legal, operational, and strategic decision-making.
Temporal correlation is particularly crucial. By aligning timestamps from disparate applications—messaging platforms, location trackers, and system logs—investigators reconstruct chronological narratives that illuminate cause-and-effect relationships. Even minor discrepancies in temporal metadata can indicate tampering, deliberate obfuscation, or evidence of sophisticated evasion techniques. Recognizing such subtleties requires both technical acumen and experiential intuition, cultivated through rigorous certification and field practice.
Network and Communication Analysis
Smartphones operate as conduits for constant digital interaction. Data flows incessantly between local storage, cloud environments, and external servers. Network analysis thus emerges as a critical facet of forensic inquiry. Practitioners examine Wi-Fi access points, cellular triangulations, and metadata streams to elucidate the trajectory of information. This forensic lens can reveal the provenance of malicious activity, map inter-party communications, and validate the chronological integrity of events. Understanding these digital pathways requires an integration of network engineering, security principles, and investigative strategy.
Metadata analysis augments traditional network scrutiny. File creation and modification timestamps, message headers, geolocation markers, and device identifiers collectively provide a mosaic of user behavior. Forensic specialists interpret these signals to infer intent, trace manipulative actions, or detect patterns indicative of illicit activity. In increasingly complex threat landscapes, such network-oriented analysis serves as a pivotal adjunct to hardware and software extraction techniques.
Integration of Artificial Intelligence in Forensics
Emergent technologies are redefining the scope of smartphone forensics. Artificial intelligence and machine learning are being harnessed to detect patterns that evade human cognition. Algorithms can sift through tens of thousands of messages, images, and application interactions to surface correlations, anomalies, and predictive indicators. Yet, algorithmic insights alone are insufficient; certified forensic practitioners combine computational outputs with domain expertise to derive actionable intelligence.
Machine learning applications extend to anomaly detection, sentiment analysis, and behavioral profiling. By identifying deviations from baseline activity, AI-driven tools can flag suspicious patterns, optimize investigative focus, and accelerate the analytical workflow. Forensic experts exercise critical judgment in interpreting these outputs, ensuring that algorithmic suggestions are contextualized within a broader evidentiary framework.
Documentation and Forensic Reporting
The culmination of forensic operations is the generation of comprehensive reports. Accurate documentation, meticulous chain-of-custody records, and clear presentation are imperative to sustaining evidentiary credibility. Certified GASF professionals recognize that a recovered dataset holds value only insofar as it can withstand legal scrutiny. Every extraction, analysis, and interpretative decision is recorded with precision, forming an immutable record of procedural integrity.
Reporting encompasses not only the raw data but also the interpretive narrative that conveys investigative findings. This narrative must balance technical specificity with accessibility, translating complex forensic operations into intelligible insights for legal and operational stakeholders. The ability to convey nuanced conclusions with clarity is a hallmark of advanced forensic proficiency.
Continuous Innovation in Mobile Forensics
The mobile landscape evolves with relentless velocity. Encrypted communication protocols, ephemeral data storage, and sophisticated application-level protections continuously challenge forensic methodologies. Certified experts respond with iterative learning, experimenting with novel tools, refining techniques, and staying abreast of technological innovations. The discipline demands both analytical rigor and creative problem-solving, integrating scientific methodology with adaptive ingenuity.
Understanding application-specific data management is central to this innovation. Each platform—be it messaging, financial, or social media—manages data differently. Recognizing storage idiosyncrasies, identifying tampering indicators, and correlating activity across multiple devices enables investigators to reconstruct complex behavioral patterns. The forensic professional operates at the nexus of technology, analysis, and investigative intuition, transforming raw digital residues into coherent, actionable intelligence.
Cognitive Cartography of Digital Interactions
In the labyrinthine expanse of modern smartphones, each datum is a node in an intricate cognitive network. Interpreting these nodes demands more than algorithmic parsing—it necessitates cognitive cartography, a deliberate mapping of behavioral trajectories. Certified experts trace the ebb and flow of social interactions, charting the subtle undulations in communicative frequency, emotive intensity, and latent intent. Each call log, text message, and ephemeral notification functions as a digital breadcrumb, collectively forming an elusive narrative of human conduct.
Appnoetic Patterns and Microhabits
Application usage reveals microcosms of habitual behavior. The seemingly innocuous act of toggling between apps can uncover profound insights into temporal preferences, proclivities, and covert agendas. Forensic specialists delve into metadata, analyzing cached files, session durations, and interaction hierarchies to reconstruct appnoetic patterns—those unconscious routines that dictate digital life. Through meticulous cross-referencing with cloud backups and auxiliary devices, these professionals illuminate otherwise opaque behavioral tendencies.
Geospatial Semantics and Locational Inference
Location-based data serves as a cartographic compass for investigative reasoning. GPS trajectories, Wi-Fi triangulations, and geotagged multimedia afford a semiotic lexicon for spatial interpretation. Professionals trained in advanced smartphone forensics leverage these datasets to extrapolate habitual zones, corroborate temporal alibis, and detect anomalous movement clusters. Even obliterated locational logs often harbor residual vectors, enabling reconstruction of clandestine journeys and clandestine rendezvous.
Residual Data Resuscitation
Digital deletion is seldom absolute. Smartphones employ overwriting mechanisms that leave vestigial data remnants, which can be resurrected through specialized analytical techniques. Forensic practitioners engage in residual data resuscitation, extracting the ephemeral echoes of prior activity. This meticulous process transforms apparent voids into fertile investigative terrain, revealing suppressed communications, obscured transactions, and hidden intent with remarkable fidelity.
Chronometric Dissection of Events
Temporal analysis serves as a keystone in behavioral reconstruction. By dissecting timestamps embedded in communications, application interactions, and system logs, analysts create an intricate chronometric lattice of events. This temporal dissection allows investigators to sequence occurrences with precision, align them with external testimonies, and challenge incongruent narratives. The interplay of time and action offers a lens through which causality and motive become discernible.
Interdevice Network Synthesis
Behavioral insight often extends beyond singular devices, encompassing interconnected networks of communication. Analysts examine interdevice relationships to detect hierarchies, affiliations, and collaborative schemata. Communication topologies reveal hidden conduits of information, exposing subtle linkages and subversive coordination. In multi-suspect investigations, this network synthesis is instrumental in identifying pivotal actors and understanding collective operational dynamics.
Psycholinguistic Deconvolution
Digital communication is rife with psycholinguistic subtleties. Variations in syntax, emotive markers, and lexical idiosyncrasies serve as indicators of psychological states and intentional obfuscation. Forensic experts apply psycholinguistic deconvolution to detect deception, assess stress indicators, and evaluate interpersonal dynamics. This fusion of linguistic acumen and technical analysis allows the transformation of raw data into nuanced narratives of cognition and intent.
Algorithmic Augmentation and Cognitive Symbiosis
Artificial intelligence and machine learning algorithms have become indispensable adjuncts in behavioral interpretation. These systems can flag anomalies, recognize patterns imperceptible to human cognition, and highlight probabilistic correlations. Yet, the role of the certified professional remains central, integrating algorithmic outputs with contextual reasoning to preserve analytical rigor. The symbiosis of human insight and computational prowess amplifies the granularity and reliability of forensic assessments.
Ethical Cartography and Data Stewardship
Interpretive analysis carries profound ethical responsibilities. Certified practitioners navigate a delicate balance between investigative utility and personal privacy, adhering to stringent legal and ethical frameworks. Confidentiality, consent, and proportionality govern every analytic endeavor, ensuring that data is leveraged judiciously and that evidentiary integrity remains unassailable. Ethical stewardship is not ancillary but foundational to the credibility and admissibility of forensic findings.
Semiotic Reconstruction of Concealed Behaviors
Behavioral analysis often involves semiotic reconstruction—the decoding of symbols, codes, and clandestine digital traces. Hidden applications, encrypted messages, and obfuscated storage schemes are interpreted through a semiotic lens, revealing patterns of evasion or clandestine communication. By mapping these signals against temporal and locational data, forensic professionals reconstruct behavioral schemas that would otherwise remain inscrutable.
Cross-Domain Correlation and Contextual Amplification
Effective interpretation transcends the confines of the device itself. By correlating smartphone data with external systems—such as cloud archives, social media footprints, and IoT devices—analysts achieve contextual amplification. This multidomain approach transforms isolated data points into comprehensive behavioral mosaics, providing a richer, more holistic understanding of user activity, motivations, and operational patterns.
Cloud Integration and Cross-Device Synchronization
Modern smartphones rarely function in isolation; they exist as nodes within an intricate digital lattice. The ceaseless interaction with cloud repositories, wearable apparatuses, and interconnected peripherals forms a complex ecosystem whose nuances are pivotal for forensic examination. Practitioners credentialed in GASF Advanced Smartphone Forensics recognize that data often transcends the device, inhabiting synchronized caches, cloud repositories, and auxiliary instruments such as smartwatches or ambient home assistants.
Cloud repositories encapsulate staggering volumes of user-generated information: correspondence, multimedia archives, application telemetry, and behavioral logs. Disregarding cloud-stored data risks constructing a fragmented narrative. Forensic experts employ meticulous extraction methodologies, navigating authentication protocols, encryption schemas, and legal mandates to retrieve synchronized information without compromising evidentiary integrity.
Cross-device synchronization compounds investigative intricacy. Smartphones may replicate information across tablets, laptops, or automotive infotainment nodes, generating redundant or mirrored datasets. Professionals adept in advanced smartphone forensics must discern synchronization vectors, juxtapose data across devices, and reconstruct coherent chronologies. This acumen is indispensable when analyzing multi-suspect networks or extensive digital infrastructures.
Encrypted storage amplifies forensic challenges. Many service providers implement end-to-end encryption, tokenized authentication, or ephemeral session keys. Certified practitioners leverage specialized tools to traverse these cryptographic barriers, remaining scrupulously within lawful parameters. Their proficiency ensures that recovered data is both exhaustive and admissible in judicial proceedings.
Analytical focus on metadata unveils behavioral subtleties. Temporal markers, device signatures, geolocation coordinates, and access logs illuminate patterns of use, deviations from normative activity, and attempts at obfuscation. Even a deleted communication or a seemingly innocuous file may persist in cloud archives or secondary devices, offering forensic breadcrumbs crucial for investigation fidelity.
The advent of AI-augmented synchronization and predictive cloud caching introduces both novel evidentiary avenues and intricate analytical dilemmas. Professionals maintain a continuous learning ethos, adapting to emergent technologies to unearth latent data and contextualize it within the investigative tableau.
Encrypted Ecosystems and Forensic Methodologies
Encryption has evolved beyond mere data concealment, functioning as a ubiquitous layer of digital opacity. Smartphones, cloud services, and synchronized devices increasingly rely on sophisticated cryptographic architectures. Forensic specialists navigate these labyrinthine systems using algorithmic acumen, heuristic analysis, and protocol-level interrogation. The objective is to extract verifiable evidence without perturbing the cryptographic equilibrium, ensuring the chain of custody remains unimpeachable.
Advanced forensic workflows encompass both static and dynamic analysis. Static techniques interrogate dormant data structures, examining cached files, backups, and residual system artifacts. Dynamic approaches, conversely, observe device behavior in real time, monitoring synchronization events, network transactions, and application interactions. Mastery of these dual paradigms allows experts to reconcile disparate datasets, corroborate user actions, and expose inconsistencies or tampering.
Moreover, understanding proprietary synchronization protocols is paramount. Vendors often implement opaque data schemas, unique timestamp conventions, and selective replication strategies. Experts trained in GASF-level methodologies can reverse-engineer these structures, decode inter-device communication, and reconstruct comprehensive activity matrices. This proficiency transforms opaque digital signals into legible forensic narratives.
Behavioral Insights through Cross-Device Correlation
Correlating activity across devices yields profound behavioral insights. Patterns of habitual interaction, anomalous deviations, and attempted data obfuscation become detectable when viewed holistically. Cross-referencing geolocation data, timestamp sequences, and communication threads can reveal the rhythm of daily activity, the orchestration of multi-device tasks, and even clandestine manipulations designed to elude scrutiny.
For instance, a deleted message on a primary smartphone may persist within a cloud snapshot or a wearable device, creating a forensic footprint that illuminates intent and chronology. Similarly, duplicative storage across vehicles or smart home devices can provide unexpected vantage points, enriching investigative granularity. Professionals attuned to these inter-device echoes can transform ostensibly mundane datasets into high-resolution reconstructions of user behavior.
Emerging Challenges in Multi-Platform Forensics
The rapid proliferation of cross-platform ecosystems presents unique investigative dilemmas. AI-driven synchronization, ephemeral cloud sessions, and predictive caching mechanisms blur traditional data boundaries. Professionals must adapt by employing adaptive forensic techniques, integrating machine learning insights, and continuously updating protocol knowledge.
The convergence of disparate devices, operating systems, and cloud environments necessitates a holistic analytical lens. Investigators must reconcile heterogeneous datasets, normalize divergent timestamp formats, and interpret cryptographically obfuscated content. This sophisticated approach ensures that forensic reconstruction is both accurate and defensible, reflecting the intricacies of modern digital behavior.
Technological Convergence and Forensic Innovation
The landscape of smartphone forensics is increasingly shaped by technological convergence, where disparate modalities of data coalesce into complex information ecosystems. Contemporary smartphones are no longer mere communication tools; they are repositories of sensor data, biometric identifiers, geolocation logs, and encrypted messaging networks. Certified professionals leverage sophisticated methodologies that encompass multifactorial analysis, merging hardware inspection with software deconstruction to unearth obfuscated digital footprints.
The proliferation of integrated applications, from augmented reality platforms to decentralized finance wallets, introduces intricate challenges. Each application may harbor proprietary encryption, nonstandard file structures, and ephemeral data retention policies. Experts in GASF Advanced Smartphone Forensics cultivate the acumen to decode these labyrinthine architectures, applying algorithmic heuristics, memory forensics, and cryptanalytic techniques that transcend traditional investigative paradigms.
Cognitive Profiling Through Digital Artifacts
An emergent frontier within advanced smartphone forensics is cognitive profiling through digital artifacts. Analysts reconstruct behavioral patterns, social networks, and decision-making tendencies from metadata, communication histories, and app interaction logs. This form of digital psychometry enables investigators to hypothesize intentions, detect anomalies, and anticipate potential threats.
Certified practitioners maintain methodological rigor, ensuring that such profiling is grounded in verifiable data rather than conjectural inference. Temporal sequencing, anomaly detection, and cross-correlation algorithms are applied to delineate credible behavioral narratives. By synthesizing these insights, forensic experts enhance investigative acuity, providing law enforcement and judicial entities with actionable intelligence derived from ephemeral digital traces.
Cryptographic Challenges and Data Resilience
As encryption protocols evolve, so too does the sophistication of forensic countermeasures. Modern smartphones deploy end-to-end encryption, hardware-backed key storage, and secure enclave technologies that fortify user data against unauthorized access. Certified experts confront these barriers with a repertoire of cryptanalytic strategies, memory-resident extraction techniques, and differential power analysis, all executed within the confines of legal authorization.
Data resilience—the inherent durability and recoverability of digital evidence—remains a central concern. Fragmented storage, wear-leveling mechanisms in flash memory, and intentional obfuscation require meticulous extraction methodologies. Professionals trained in GASF Advanced Smartphone Forensics employ multi-layered validation, cross-platform verification, and forensic imaging to ensure that recovered data maintains evidentiary integrity and withstands adversarial scrutiny.
Ethical Dilemmas in Persistent Surveillance
The omnipresence of smartphones introduces ethical dilemmas in persistent surveillance and investigative reach. Professionals must navigate the tension between public safety imperatives and individual privacy rights, avoiding unauthorized intrusion while ensuring investigative thoroughness. Ethical praxis dictates that each access point, from cloud repositories to local device caches, is approached with procedural transparency and proportionality.
Decision-making frameworks are informed by both codified standards and situational exigencies. Analysts weigh the significance of data against potential collateral exposure, employing privacy-preserving extraction methods, anonymization protocols, and selective data retention strategies. This ethical vigilance fosters trustworthiness in forensic findings and fortifies the legitimacy of judicial proceedings.
Cross-Border Forensics and Jurisdictional Nuances
Smartphone data often traverses geopolitical boundaries, entangling investigators in complex jurisdictional matrices. Cross-border forensics necessitates familiarity with international data protection statutes, mutual legal assistance treaties, and cybercrime conventions. Certified professionals adeptly navigate these regulatory frameworks, ensuring that evidence collection, analysis, and transfer comply with multilateral obligations.
In practice, this involves meticulous documentation of chain-of-custody, encryption handling, and procedural compliance. Any lapse may render evidence inadmissible or expose the investigative entity to legal liability. The capacity to operate within these legal liminalities distinguishes seasoned forensic practitioners, allowing them to reconcile technological capabilities with intricate regulatory landscapes.
Visual Analytics and Evidence Narratives
Transforming voluminous data into digestible insights is pivotal in courtroom settings. Forensic experts employ visual analytics to construct chronological narratives, correlation maps, and interaction graphs that illuminate complex digital relationships. These visualizations bridge the cognitive gap between technical analysis and human comprehension, enabling jurors and legal professionals to apprehend sophisticated findings intuitively.
The practice involves not only technical precision but also aesthetic discernment. Timeline visualizations, geospatial plotting, and interaction heatmaps are rendered with clarity, emphasizing causality, frequency, and contextual relevance. Certified professionals in GASF Advanced Smartphone Forensics excel in crafting these narrative artifacts, ensuring that evidence is both compelling and comprehensible without compromising accuracy or integrity.
Continuous Learning and Threat Anticipation
The dynamism of digital ecosystems demands perpetual professional evolution. Emerging threats, including AI-driven malware, cross-platform exploits, and quantum-resilient encryption, compel forensic practitioners to engage in continuous learning and scenario modeling. Certification programs reinforce this ethos, promoting mastery of cutting-edge tools, experimental techniques, and anticipatory threat frameworks.
Through ongoing professional development, analysts refine their technical dexterity while integrating ethical and legal considerations into every investigative maneuver. This proactive stance ensures that forensic interventions remain anticipatory rather than reactive, positioning certified experts at the forefront of both technological innovation and evidentiary reliability.
Multimodal Data Synthesis and Interpretive Precision
Smartphones generate multimodal datasets encompassing text, audio, video, sensor telemetry, and application logs. Integrating these heterogeneous streams demands interpretive precision and methodological coherence. Professionals synthesize diverse data types, aligning temporal, spatial, and contextual vectors to reconstruct events with granular fidelity.
This synthesis is further complicated by data incompleteness, fragmentation, and intentional obfuscation. Certified forensic analysts deploy pattern recognition algorithms, anomaly detection frameworks, and cross-modal correlation techniques to bridge these gaps. The resultant reconstructions not only facilitate investigative clarity but also reinforce evidentiary credibility in high-stakes legal environments.
Ephemeral Data and the Imperative of Temporal Awareness
The fleeting nature of digital footprints introduces a temporal dimension to forensic inquiry that demands heightened vigilance. Ephemeral messages, self-erasing media, and transient session data create a landscape in which evidence may vanish within moments. Certified professionals cultivate a temporal sensitivity, orchestrating data capture and analysis with a precision that accounts for both immediate retrieval and longitudinal reconstruction. The mastery of temporal awareness encompasses the ability to anticipate volatility, synchronize multi-source datasets, and reconstruct ephemeral interactions into coherent investigative narratives. In doing so, forensic experts convert impermanence into actionable insight, revealing behavioral patterns that might otherwise dissolve into digital oblivion.
Advanced Memory Forensics and Volatile Artifact Analysis
Memory forensics, particularly the examination of volatile data residing in RAM, constitutes a pivotal dimension of modern smartphone investigations. Volatile artifacts capture ephemeral operational states, revealing active processes, decrypted data, and transient communications that do not persist on disk. Certified professionals employ specialized tools and techniques to extract, analyze, and interpret these artifacts without perturbing their integrity. The subtleties of memory analysis—ranging from stack inspection to heap reconstruction—demand both technical dexterity and interpretive insight. By elucidating the ephemeral states of devices, memory forensics transforms invisible operational nuances into tangible investigative evidence.
Behavioral Biometrics and Contextual Signature Analysis
Beyond raw data retrieval, smartphone forensics increasingly engages with behavioral biometrics, exploiting unique patterns of device interaction, typing cadence, swipe gestures, and habitual app usage. These behavioral signatures function as quasi-biometric identifiers, providing probabilistic correlations between users and device activity. Certified professionals leverage machine learning and statistical modeling to quantify and validate these correlations, creating evidentiary linkages that complement traditional forensic artifacts. The integration of behavioral biometrics into investigative praxis exemplifies the convergence of human-centered analysis with algorithmic sophistication, expanding the interpretive horizon of digital investigations.
Jurisdictional Complexity and Cross-Border Forensic Strategy
The proliferation of cloud services and globalized digital infrastructures introduces intricate jurisdictional considerations for forensic investigations. Data stored across international boundaries is subject to divergent regulatory frameworks, privacy statutes, and procedural requirements. Certified professionals navigate this complexity by integrating legal acumen with technical methodology, ensuring that evidence collection, transfer, and analysis comply with applicable legal standards. Strategic planning encompasses cross-border data access protocols, mutual legal assistance treaties, and encryption compliance, ensuring that investigative rigor is matched by procedural legitimacy. Mastery of jurisdictional complexity positions professionals to operate effectively in the transnational landscape of digital evidence.
Forensic Artifact Reconstruction in Fragmented Environments
Smartphone data often exists in fragmented or partially corrupted states, whether due to device failure, malware interference, or deliberate obfuscation. Forensic reconstruction requires sophisticated techniques to reassemble incomplete datasets, infer missing information, and validate reconstructed sequences. Certified professionals employ methodologies including differential analysis, heuristic reconstruction, and error-correcting algorithms to bridge gaps in evidence. This capacity to recover intelligible narratives from incomplete or degraded artifacts underscores the analytic ingenuity required in contemporary forensic practice, transforming apparent loss into investigable insight.
IoT Integration and Multinode Forensic Mapping
The expansion of Internet of Things (IoT) devices has created a dense network of interconnected nodes, each generating traces of user behavior. Smartphones often function as hubs within these networks, mediating interactions with smart appliances, wearable sensors, and connected vehicles. Certified forensic professionals must map these multinode ecosystems, correlating events across disparate devices to reconstruct comprehensive activity timelines. Techniques such as cross-device event correlation, temporal alignment, and inter-system provenance tracing enable the forensic investigator to synthesize a coherent narrative from diverse digital sources. This multidimensional approach exemplifies the evolution of forensic inquiry from device-centric to ecosystem-centric analysis.
Proactive Threat Anticipation and Cyber-Resilience
Advanced smartphone forensics extends beyond reactive investigation into proactive threat anticipation. Certified professionals develop cyber-resilient methodologies, anticipating malware evolution, adversarial encryption strategies, and obfuscation techniques. Threat modeling, intrusion simulation, and predictive analysis allow practitioners to foresee potential compromise vectors, preemptively safeguarding data integrity. By integrating anticipatory cognition with methodical forensic rigor, investigators position themselves not merely as responders to digital incidents but as strategic architects of investigative resilience.
Cognitive Load Management in Forensic Analysis
The complexity of contemporary smartphone forensics imposes significant cognitive demands on practitioners. Managing vast datasets, integrating cross-platform evidence, and interpreting algorithmically derived insights necessitates sophisticated cognitive load management strategies. Certified experts employ structured analytical frameworks, hierarchical prioritization of investigative tasks, and automated triage systems to optimize mental bandwidth. By mitigating cognitive overload, forensic professionals enhance both analytical accuracy and procedural efficiency, ensuring that intricate investigations are navigated with precision and insight.
Ethical Implications of Predictive and Algorithmic Forensics
The increasing reliance on AI and predictive methodologies introduces profound ethical considerations. Algorithmically derived inferences, behavioral reconstructions, and probabilistic correlations carry inherent uncertainties and biases. Certified professionals are tasked with scrutinizing algorithmic outputs, validating predictive conclusions, and ensuring transparency in evidentiary interpretation. Ethical forensics requires the reconciliation of technological capability with moral responsibility, guarding against the potential misuse of algorithmic authority and preserving the integrity of investigative outcomes. This ethical vigilance is a cornerstone of professional practice, reinforcing trustworthiness in an era of computational sophistication.
Epistemic Rigor and Forensic Methodology
Forensic inquiry is predicated upon epistemic rigor—the systematic pursuit of knowledge through disciplined observation, validation, and reasoning. Certified smartphone forensic experts cultivate methodological exactitude, meticulously documenting evidence provenance, analytic processes, and interpretive decisions. This epistemic rigor ensures that investigative conclusions are defensible, reproducible, and analytically sound. By embedding rigor into every phase of investigation—from data acquisition to interpretive synthesis—professionals safeguard the reliability and credibility of forensic outcomes in both legal and operational contexts.
Cross-Disciplinary Synergy in Investigative Ecosystems
Effective smartphone forensics increasingly relies upon cross-disciplinary collaboration. Investigations frequently involve law enforcement personnel, cybersecurity analysts, legal counsel, and behavioral scientists. Certified experts articulate technical findings, interpret complex datasets, and provide domain-specific insight, enabling cohesive and informed decision-making across investigative teams. Cross-disciplinary synergy enhances evidentiary comprehensiveness, operational coherence, and strategic foresight, reflecting a modern investigative ethos in which collaborative intelligence supersedes siloed expertise.
Forensic Tool Evolution and Technical Acumen
The rapid evolution of forensic tools—from hardware-based extraction devices to cloud-integrated analytical platforms—requires continuous technical refinement. Certified professionals maintain familiarity with emergent toolsets, evaluating their capabilities, limitations, and operational integrity. Mastery encompasses not only tool proficiency but also adaptive problem-solving, enabling investigators to tailor methodologies to unique investigative contexts. The interplay between technical acumen and methodological flexibility ensures that forensic outcomes remain robust amidst the continual transformation of technological landscapes.
Digital Provenance and Contextualized Evidence Interpretation
The evidentiary value of digital artifacts is contingent upon their provenance and contextual interpretation. Metadata, temporal sequencing, network interactions, and device-specific characteristics collectively inform the reconstruction of events. Certified professionals apply analytic frameworks that situate raw data within broader operational, behavioral, and environmental contexts. This contextualization elevates mere digital traces into intelligible narratives, enabling nuanced understanding of user intent, operational causality, and interaction dynamics. Evidence interpretation thus transcends mechanical extraction, embodying a sophisticated synthesis of technical, behavioral, and contextual intelligence.
Adaptive Algorithms and Predictive Forensics
Advanced smartphone forensics increasingly relies on adaptive algorithms to anticipate patterns of behavior and reconstruct complex digital interactions. Predictive forensics, a nascent yet rapidly evolving discipline, combines historical datasets, machine learning models, and anomaly detection to forecast probable user actions or system events. Certified practitioners deploy these algorithms judiciously, ensuring that computational predictions complement empirical evidence rather than supplant it.
These adaptive systems excel in environments characterized by data volatility, such as cloud-based applications or ephemeral messaging platforms. By analyzing recurrent behavioral signatures, temporal sequences, and inter-device interactions, forensic analysts can identify discrepancies indicative of tampering, deception, or unauthorized access. This proactive approach extends investigative reach beyond reactive recovery, offering strategic insights that bolster both operational efficacy and evidentiary robustness.
Memory Forensics and Ephemeral Data Recovery
Ephemeral data, residing in volatile memory, constitutes a critical yet often overlooked component of digital investigations. RAM snapshots, temporary caches, and transient process logs frequently contain information that is irretrievable from persistent storage. Certified professionals employ memory forensics techniques, including live acquisition, process enumeration, and heap analysis, to capture these fleeting artifacts.
The process requires meticulous precision; even minor missteps during acquisition can corrupt memory states or introduce inconsistencies. Through careful segmentation, timestamp synchronization, and hash validation, forensic analysts reconstruct volatile datasets to reveal patterns of application usage, encryption key residency, and inter-process communication. This layer of investigative insight is indispensable when addressing complex cases involving sophisticated adversaries or real-time operational obfuscation.
Biometric Data and Identity Validation
Modern smartphones incorporate biometric authentication mechanisms, such as fingerprint sensors, facial recognition, and voice verification. These systems introduce both opportunities and challenges for forensic practitioners. While biometric logs can corroborate user presence and device interaction, they also raise profound ethical and privacy concerns. Certified analysts navigate this terrain with stringent adherence to legal frameworks and procedural safeguards.
Extraction of biometric metadata often necessitates collaboration with device manufacturers, specialized hardware interfaces, or sanctioned software toolkits. Professionals validate the provenance and integrity of these artifacts to ensure that identity assertions are admissible in court. The interplay between biometrics, cryptographic authentication, and system logs enables nuanced reconstructions of user behavior, adding layers of evidentiary depth to complex investigations.
Cloud Ecosystems and Distributed Evidence
Cloud storage and distributed computing platforms have fundamentally transformed smartphone forensics. Data frequently resides in decentralized repositories, spanning multiple jurisdictions and governed by diverse regulatory frameworks. Certified professionals employ distributed forensic methodologies, encompassing API extraction, server-side logging, and cross-platform reconciliation, to capture comprehensive datasets.
The challenges of cloud forensics are multifaceted. Data consistency, replication latency, and synchronization anomalies can introduce ambiguity if not carefully managed. Experts implement meticulous verification protocols, including cryptographic hash comparisons, integrity checks, and audit trail validation, to ensure that cloud-derived evidence maintains legal admissibility. This approach reinforces investigative credibility, enabling digital artifacts to withstand scrutiny in complex litigation or cybercrime proceedings.
Encrypted Messaging and De-obfuscation Techniques
Encrypted messaging applications constitute a formidable frontier in smartphone forensics. End-to-end encryption, ephemeral message deletion, and obfuscation layers pose significant hurdles to data extraction and interpretation. Certified analysts employ sophisticated de-obfuscation techniques, including cryptanalysis, key escrow retrieval, and temporal correlation, to reconstruct message content and interaction timelines.
Analytical rigor is paramount; improper handling can not only compromise evidence but also contravene statutory mandates. By integrating metadata analysis with content reconstruction, forensic experts elucidate communication networks, detect coordinated activity, and infer behavioral intent. These techniques provide actionable intelligence that extends beyond surface-level content, revealing the structural dynamics of digital interactions and enhancing investigative depth.
Sensor Fusion and Contextual Reconstruction
Smartphones are embedded with a plethora of sensors, ranging from accelerometers and gyroscopes to ambient light and proximity detectors. Certified forensic professionals exploit this sensor data through fusion techniques, combining disparate streams to reconstruct user movement, environmental context, and device orientation.
Sensor fusion enables the creation of high-fidelity reconstructions, such as tracking a device’s trajectory during a critical event or corroborating eyewitness accounts with sensor-derived timelines. By applying statistical models, anomaly detection, and cross-sensor validation, analysts extract meaningful patterns from seemingly innocuous data. This multidimensional approach exemplifies the convergence of technical ingenuity and investigative rigor, yielding insights inaccessible through conventional forensic modalities.
Advanced File Carving and Data Recovery
File carving, the extraction of fragmented or partially deleted files, remains a cornerstone of smartphone forensics. Advanced techniques leverage signature-based detection, content-aware heuristics, and pattern recognition to reconstruct files from unallocated memory or damaged storage sectors. Certified professionals refine these methods through iterative validation and cross-referencing, ensuring that recovered artifacts are authentic and legally defensible.
Complications arise when data is encrypted, compressed, or intentionally obfuscated. Analysts must apply reverse-engineering methodologies, entropy analysis, and algorithmic reconstruction to retrieve intelligible information. By combining these strategies with metadata preservation, forensic experts deliver evidence that retains contextual integrity while illuminating previously inaccessible digital footprints.
Legal Admissibility and Evidentiary Standards
The ultimate utility of forensic findings hinges upon legal admissibility. Certified professionals meticulously document procedural steps, maintain immutable evidence trails, and adhere to recognized forensic standards. This ensures that recovered data withstands scrutiny under cross-examination, evidentiary challenges, and appellate review.
Understanding jurisdiction-specific rules, such as chain-of-custody requirements, statutory privacy thresholds, and procedural mandates, is integral. Analysts reconcile investigative imperatives with these legal frameworks, balancing operational efficacy against procedural compliance. The result is evidence that is not only technically sound but also judiciously contextualized for legal proceedings, reinforcing the credibility and reliability of investigative outputs.
Mobile Threat Intelligence and Proactive Defense
The integration of mobile threat intelligence into forensic practice exemplifies proactive digital defense. By analyzing malware signatures, intrusion vectors, and exploit patterns, certified professionals anticipate potential compromises and mitigate future risks. Threat intelligence frameworks incorporate cross-device correlation, behavioral anomaly detection, and predictive modeling to identify emerging vulnerabilities.
This intelligence-driven approach extends beyond reactive incident response, informing strategic investigations, corporate security postures, and law enforcement operations. Certified analysts translate technical findings into actionable insights, enabling stakeholders to fortify systems while preserving evidentiary integrity. The symbiosis of forensic investigation and threat intelligence enhances operational resilience and situational awareness in an ever-evolving digital landscape.
Cross-Platform Correlation and Multi-Device Analysis
Modern investigations frequently involve multiple devices within a single ecosystem. Smartphones, tablets, laptops, and IoT peripherals may collectively contain critical evidence. Certified forensic professionals perform cross-platform correlation, aligning temporal, spatial, and content-based data across devices to construct coherent narratives.
This analytical endeavor requires sophisticated toolchains capable of normalizing disparate file formats, synchronizing timestamps, and identifying inter-device interactions. By triangulating evidence, analysts uncover relational dynamics, detect coordinated activity, and validate behavioral hypotheses. Cross-platform forensic synthesis exemplifies the fusion of technical proficiency, analytical acumen, and methodical rigor, delivering insights unattainable through single-device examination.
Ethical Oversight and Professional Accountability
Ethical oversight remains a cornerstone of advanced smartphone forensics. Certified professionals are accountable not only to legal standards but also to societal expectations regarding privacy, proportionality, and data stewardship. Decisions regarding data access, retention, and dissemination are governed by stringent ethical frameworks, ensuring that investigative outcomes respect fundamental rights while achieving investigative objectives.
Accountability mechanisms, including peer review, audit trails, and professional certification protocols, reinforce adherence to ethical standards. This ensures that forensic interventions are transparent, reproducible, and defensible, safeguarding both the credibility of the practitioner and the integrity of the investigative process. Ethical vigilance thus underpins the legitimacy and trustworthiness of contemporary smartphone forensic practice.
Dynamic Forensic Toolchains and Automation
Certified experts leverage dynamic forensic toolchains, integrating automated processes with manual verification to enhance efficiency, accuracy, and reproducibility. Automation facilitates the rapid processing of voluminous datasets, while human oversight ensures contextual interpretation and methodological validation.
Toolchains encompass data acquisition, hashing, pattern recognition, anomaly detection, and reporting modules. By tailoring these toolchains to specific investigative contexts, analysts achieve a balance between computational speed and forensic precision. This integration exemplifies the evolution of digital forensics from labor-intensive practice to a hybridized paradigm of human insight augmented by automated intelligence.
Societal Implications and Public Trust
Smartphone forensics extends beyond individual investigations, influencing societal perceptions of privacy, security, and justice. Certified professionals operate at the intersection of technological capability and social accountability, shaping public trust through transparent, ethical, and legally compliant practice.
The responsible application of forensic methodologies contributes to societal stability by ensuring that digital investigations are conducted with precision, fairness, and respect for individual rights. Analysts’ adherence to professional and legal standards reinforces confidence in judicial outcomes, demonstrating that technological sophistication can coexist with ethical stewardship and societal responsibility.
Cloud Ecosystems as Forensic Reservoirs
The modern cloud ecosystem functions as an expansive reservoir of digital residue. Beyond mere storage, it encapsulates user behavior, systemic interactions, and application telemetry, forming an intricate mosaic of activity. Forensic professionals must approach cloud analysis with methodological rigor, recognizing that data may be transient, replicated, or obfuscated across multi-tiered architectures.
Temporal artifacts within cloud services often hold untapped investigative potential. Version histories, incremental backups, and synchronized snapshots can reveal the evolution of user interactions, demonstrating not only what occurred but also how behavior adapted over time. Such longitudinal analysis affords a granular understanding of user intent, the orchestration of complex actions, and potential attempts to conceal activity.
Cloud metadata, often underappreciated, serves as a linchpin for reconstructing forensic narratives. Access logs, IP correlations, and device identifiers allow the establishment of precise activity timelines. These artifacts can also illuminate anomalous behavior indicative of compromise, collusion, or unauthorized access. Professionals trained in advanced smartphone forensics leverage this metadata to transform raw digital traces into actionable intelligence, providing both evidentiary clarity and investigative depth.
Synchronization Nodes and Interdevice Forensics
Synchronization nodes represent the critical junctures where device ecosystems intersect. These nodes—ranging from smartphones to wearables, IoT devices, and vehicle infotainment systems—act as conduits for the replication of user data. Understanding their operational logic is essential for comprehensive forensic examination.
Professionals often encounter scenarios where activity appears fragmented across multiple endpoints. A file created on a smartphone may propagate to a tablet, mirror on a cloud repository, and persist as a cached element within a vehicle’s infotainment system. Identifying these conduits and tracing data flow across nodes allows investigators to reconstruct complete behavioral arcs, exposing latent connections that may otherwise remain hidden.
Device-to-device synchronization often employs proprietary protocols, varying dramatically across vendors. Reverse-engineering these protocols is crucial for interpreting timestamp sequences, understanding delta changes, and resolving conflicts in replicated datasets. Practitioners must combine technical dexterity with methodical analysis, correlating multi-source data to establish coherent timelines and behavioral linkages.
Cryptography and Forensic Adjudication
Encryption functions as both a protective mechanism and a forensic obstacle. End-to-end cryptography, ephemeral session keys, and zero-knowledge storage architectures complicate evidence acquisition. Certified forensic professionals must navigate these challenges while maintaining legal and ethical compliance.
Cryptographic analysis often begins with identifying the type and scope of encryption. Symmetric, asymmetric, and hybrid schemas may co-exist within a single ecosystem. Recognizing their operational characteristics allows professionals to deploy targeted strategies—ranging from token extraction and key escrow methodologies to protocol-level interrogation—ensuring data integrity while retrieving actionable evidence.
Beyond technical proficiency, cryptographic forensics demands acute interpretive judgment. Understanding how encryption interacts with synchronization, caching, and cloud replication is critical. A seemingly inaccessible message may exist redundantly across secondary devices or cloud snapshots, revealing content and timing without violating cryptographic protections. This duality underscores the necessity of cross-disciplinary expertise, blending cryptography, system architecture, and investigative methodology.
Behavioral Profiling through Multi-Device Analysis
Inter-device analysis enables behavioral profiling at an unprecedented granularity. By aggregating activity from smartphones, tablets, smartwatches, and cloud repositories, forensic experts can generate high-fidelity behavioral maps. These maps illuminate patterns of habitual activity, deviations from normative routines, and deliberate obfuscation attempts.
Behavioral anomalies often emerge when data from disparate nodes is juxtaposed. A deleted text may persist in cloud backup logs; a location ping may reveal clandestine movement; and application telemetry may expose interactions otherwise hidden on primary devices. Professionals must integrate these insights to distinguish between benign anomalies and deliberate attempts to manipulate evidence.
Predictive modeling further enhances behavioral profiling. Advanced forensic workflows increasingly incorporate algorithmic analysis to identify patterns indicative of premeditated action, habitual concealment, or multi-device coordination. Such predictive capabilities provide both investigative foresight and corroborative support, enabling experts to anticipate behavior and reconstruct nuanced digital narratives.
Emerging Paradigms in Digital Interconnectivity
The advent of AI-assisted synchronization and predictive caching introduces novel paradigms in device interconnectivity. These mechanisms autonomously replicate, archive, and optimize data flows across heterogeneous ecosystems, creating new avenues and challenges for forensic investigation.
Forensic practitioners must understand the operational logic behind these systems. AI-driven replication may prioritize relevance, frequency, or predictive user intent, producing data patterns that deviate from traditional chronological order. Interpreting such patterns requires a fusion of algorithmic literacy, forensic acumen, and investigative intuition, ensuring that recovered evidence retains evidentiary veracity while illuminating user behavior.
Cross-platform ecosystems further complicate analysis. Devices running divergent operating systems, leveraging unique storage architectures, or employing vendor-specific synchronization protocols generate heterogeneous datasets. Experts must reconcile temporal discrepancies, normalize metadata, and decode cryptographically protected content to form coherent investigative narratives.
Metadata as Forensic Keystone
Metadata functions as the forensic keystone in cloud-integrated investigations. Time stamps, device identifiers, geolocation coordinates, and access logs collectively provide a multidimensional perspective on user activity. Each metadata element contributes to reconstructing chronology, verifying authenticity, and detecting anomalous behavior.
Temporal metadata, in particular, is invaluable. Incremental changes, session durations, and replicated timestamps reveal the cadence of user activity. Geospatial metadata uncovers movement patterns and locational consistencies, often exposing undisclosed device usage or multi-location interaction. Access logs can identify unauthorized entry, atypical device engagement, or synchronization anomalies, highlighting potential attempts at concealment.
The forensic value of metadata is amplified when correlated across nodes. An ostensibly deleted communication may persist within cloud logs; a synchronization anomaly may reveal simultaneous activity on multiple devices. By integrating these insights, experts construct a layered understanding of user behavior, transforming ephemeral digital traces into tangible evidence.
Legal and Procedural Considerations in Cloud Forensics
Navigating the legal framework is integral to cloud and cross-device forensic investigation. Professionals must operate within statutory boundaries, balancing investigative efficacy with ethical and procedural compliance.
Accessing cloud-stored data typically necessitates formal authorization. Legal requisites, ranging from search warrants to consent agreements, ensure that evidence acquisition aligns with jurisdictional mandates. Professionals must also maintain chain-of-custody protocols, meticulously documenting extraction processes to guarantee admissibility.
Moreover, the ethical dimension of cloud forensics cannot be overstated. Investigators encounter sensitive information that extends beyond the primary scope of inquiry. Responsible handling, secure storage, and judicious analysis safeguard both the integrity of the investigation and the privacy rights of individuals.
Cross-jurisdictional investigations present additional complexity. Data may reside on servers spanning multiple legal territories, each with distinct regulations and compliance requirements. Professionals must navigate this labyrinth, coordinating with legal authorities and leveraging international forensic standards to ensure lawful and effective data acquisition.
Reconciling Volatile and Persistent Data
Smartphone ecosystems generate both volatile and persistent data, each offering distinct forensic insights. Volatile data, residing in active memory or ephemeral caches, reflects immediate interactions and system states. Persistent data, encompassing stored files, cloud backups, and archival snapshots, documents enduring activity and historical behavior.
Reconciling these two dimensions is critical for investigative completeness. Volatile data can elucidate recent actions, reveal temporary system anomalies, and expose in-progress obfuscation. Persistent data provides contextual continuity, illustrating patterns of behavior, data propagation, and synchronization over extended periods. Integrating these perspectives enables professionals to reconstruct precise, multi-layered narratives of user activity.
Advanced forensic techniques often involve live acquisition and dynamic analysis. Monitoring network interactions, observing synchronization events, and capturing real-time system behavior provide insights inaccessible through static examination alone. This holistic approach ensures that both transient and enduring data are captured, correlated, and interpreted with methodological rigor.
Multilayered Behavioral Stratigraphy
Human activity on smartphones manifests in stratified layers, each revealing a distinct dimension of behavior. From overt communications to subtle micro-interactions, each layer constitutes a behavioral stratum, demanding careful excavation. Analysts employ multilayered behavioral stratigraphy, segmenting data into chronological, functional, and contextual strata. This process elucidates the interdependencies of routines, exposing recurrent motifs, latent patterns, and anomalies that may otherwise elude detection. Stratigraphy extends beyond single applications, capturing the interplay between messaging platforms, productivity tools, and entertainment environments, revealing the digital psyche in its totality.
Ephemeral Communication Dynamics
The proliferation of ephemeral communication—self-deleting messages, vanishing media, and transient notifications—introduces an additional analytical complexity. While designed to evade permanence, ephemeral content leaves traces within system caches, memory residues, and cloud snapshots. Certified forensic practitioners exploit these residual signals to reconstruct fleeting interactions, decipher temporal relevance, and infer intentional concealment. The subtlety of these interactions often unveils behavioral nuances, including urgency, secrecy, or premeditation, that conventional data might fail to capture.
Encrypted Interactions and Ciphered Networks
Encryption serves as a formidable barrier in digital forensics, yet it also offers indirect behavioral insights. Even when content remains inaccessible, metadata surrounding encrypted communications—timestamps, frequencies, and peer associations—can be analytically informative. Forensic experts map these ciphered networks to reveal operational topologies, habitual correspondences, and hidden affiliations. Understanding these interactions requires a dual lens of cryptographic comprehension and behavioral acumen, as patterns in encrypted communication often betray intent, coordination, or clandestine planning.
Anomalistic Pattern Recognition
Human behavior is seldom linear; deviations and irregularities are often the most telling. Anomalistic pattern recognition identifies outliers in usage, interaction, and locational behavior. Certified analysts detect atypical login times, unusual message volumes, or erratic application usage that may indicate concealment, coercion, or deviance. This methodology leverages both algorithmic detection and contextual interpretation, ensuring that anomalies are not merely statistical artifacts but actionable behavioral indicators.
Temporal Synesthesia and Chronological Synthesis
Temporal synesthesia is the perceptual blending of chronological data streams, enabling analysts to perceive sequences not merely as linear events but as overlapping, interdependent phenomena. By synthesizing timestamps from calls, messages, system events, and application interactions, professionals reconstruct complex temporal tapestries. These tapestries reveal simultaneities, causal linkages, and orchestrated behaviors that illuminate the rhythm and cadence of human digital life. Chronological synthesis transforms isolated timestamps into a narrative continuum, essential for both investigative clarity and judicial validation.
Locational Resonance Mapping
Beyond basic geospatial plotting, locational resonance mapping interprets behavioral significance in physical spaces. Analysts examine frequency, duration, and contextual activity at specific locations to assess habitual zones, risk loci, and recurrent convergence points. Patterns emerge that correlate with social interactions, professional routines, or clandestine rendezvous. Even when data has been partially erased, residual locational signals—such as cell tower pings or Wi-Fi associations—allow reconstruction of these resonances, providing insight into habitual behaviors and potential investigatory relevance.
Psychosocial Network Analytics
Devices rarely operate in isolation; they are nodes within broader psychosocial networks. Advanced forensic analysis leverages psychosocial network analytics to identify hierarchies, influence vectors, and relational dynamics. Patterns of communication intensity, reciprocity, and clustering reveal social roles, collaborative tendencies, and latent affiliations. When combined with behavioral stratigraphy and locational mapping, network analytics enables a multidimensional understanding of human interactions, exposing both overt and covert relational architectures.
Residual Forensic Ecology
Smartphones exist within a residual forensic ecology—a dynamic environment in which deleted files, overwritten caches, and system artifacts coexist. Analysts navigate this ecology with precision, employing sophisticated extraction methodologies to recover, validate, and interpret these vestiges. Each recovered fragment contributes to the reconstruction of prior behaviors, revealing hidden activities, temporal sequences, and interaction patterns. This ecological perspective emphasizes the continuity of digital traces, demonstrating that even erased data persists within complex system interdependencies.
Algorithmic Behavior Synthesis
While machine learning algorithms assist in detecting patterns, human experts engage in algorithmic behavior synthesis, integrating computational outputs with contextual insight. Algorithms may flag unusual activity, yet human judgment contextualizes anomalies within social, psychological, and situational frameworks. This synthesis ensures that interpretations are nuanced, defensible, and actionable. Behavioral synthesis transforms discrete data signals into cohesive narratives, bridging the technical precision of computation with the interpretive depth of human analysis.
Digital Semiotics and Behavioral Iconography
Every interaction on a smartphone conveys semiotic meaning. Emojis, abbreviations, hashtags, and app-specific behaviors constitute a complex iconography of intent and affect. Forensic specialists decode this digital semiotics to interpret emotion, intention, and relational context. Behavioral iconography extends beyond textual analysis to encompass gestures, interface interactions, and device usage modalities, offering a holistic understanding of user conduct. Through this lens, even the minutiae of digital expression becomes analytically significant, revealing dimensions of human behavior often invisible to surface-level inspection.
Multidimensional Contextual Integration
The most compelling behavioral insights arise when data is analyzed across multiple dimensions simultaneously. Temporal, locational, network, and semiotic dimensions intersect, producing a rich, multidimensional contextual fabric. Analysts integrate these layers to uncover correlations, causality, and behavioral motifs. By synthesizing cross-domain information, professionals reconstruct comprehensive behavioral profiles, transforming raw digital artifacts into coherent, meaningful, and actionable intelligence.
Predictive Behavioral Modelling
With sufficient data, analysts can construct predictive behavioral models, extrapolating future actions, tendencies, or interactions. These models, grounded in historical usage, temporal patterns, and network dynamics, enable proactive investigation, risk assessment, and strategic intervention. Predictive modeling blends statistical rigor, machine learning, and expert judgment, providing a forward-looking dimension to smartphone forensic analysis. Such models illuminate not only what occurred but what is likely to transpire, offering investigators a nuanced anticipatory capability.
Cognitive Dissonance and Behavioral Incongruities
Behavioral incongruities often reveal cognitive dissonance—instances where digital actions conflict with stated intentions, social norms, or prior behaviors. Analysts identify these dissonances through cross-referencing communications, locational data, and app usage. Such inconsistencies may indicate deception, hidden motives, or attempts at obfuscation. Understanding cognitive dissonance requires both analytical precision and psychological insight, as the subtleties of human inconsistency are as informative as overt patterns of behavior.
Ethical Semiotics of Interpretation
Interpreting human behavior through digital traces entails profound ethical responsibility. Analysts navigate the semiotics of digital life with care, balancing investigative necessity with respect for privacy, consent, and proportionality. Every interpretive act is contextualized within legal, ethical, and professional frameworks, ensuring that insights are not only accurate but morally defensible. Ethical semiotics emphasizes the interpretive act itself as a moral undertaking, reinforcing the importance of principled analysis in complex digital landscapes.
Conclusion
Advanced smartphone forensics represents a unique intersection of technology, investigation, and human behavior. Professionals certified in GASF Advanced Smartphone Forensics stand at the forefront of this field, equipped not only with the technical expertise to extract and analyze data but also with the ethical and legal knowledge to ensure that investigations are conducted responsibly and effectively.
Throughout this series, we explored the foundations of mobile device architecture, the tools and techniques used for data extraction, the nuances of behavioral analysis, and the critical role of cloud integration and cross-device synchronization. We examined the ethical and legal frameworks that govern forensic work and looked ahead to emerging trends and challenges that will shape the discipline in the years to come.
The journey of a certified forensic professional is both rigorous and rewarding. Each device presents a unique puzzle, each dataset reveals new insights, and each case offers opportunities to combine technical acumen with investigative creativity. The ability to reconstruct hidden activities, recover erased information, and interpret complex behavioral patterns underscores the value of advanced training and certification.
As technology evolves, the role of the forensic expert becomes ever more essential. Smartphones and connected devices increasingly mediate daily life, storing vast troves of personal and professional information. Certified experts must remain vigilant, adaptable, and committed to continuous learning, ensuring that their skills evolve alongside technological advancements.
In essence, advanced smartphone forensics is more than a technical discipline—it is a gateway to understanding the digital imprints of human activity. Professionals who embrace this field with dedication and integrity not only uncover evidence but also contribute to justice, accountability, and the responsible use of technology in an increasingly connected world. The knowledge, tools, and ethical grounding gained through certification empower experts to meet the challenges of today and tomorrow, making a meaningful impact in the realm of digital investigation.