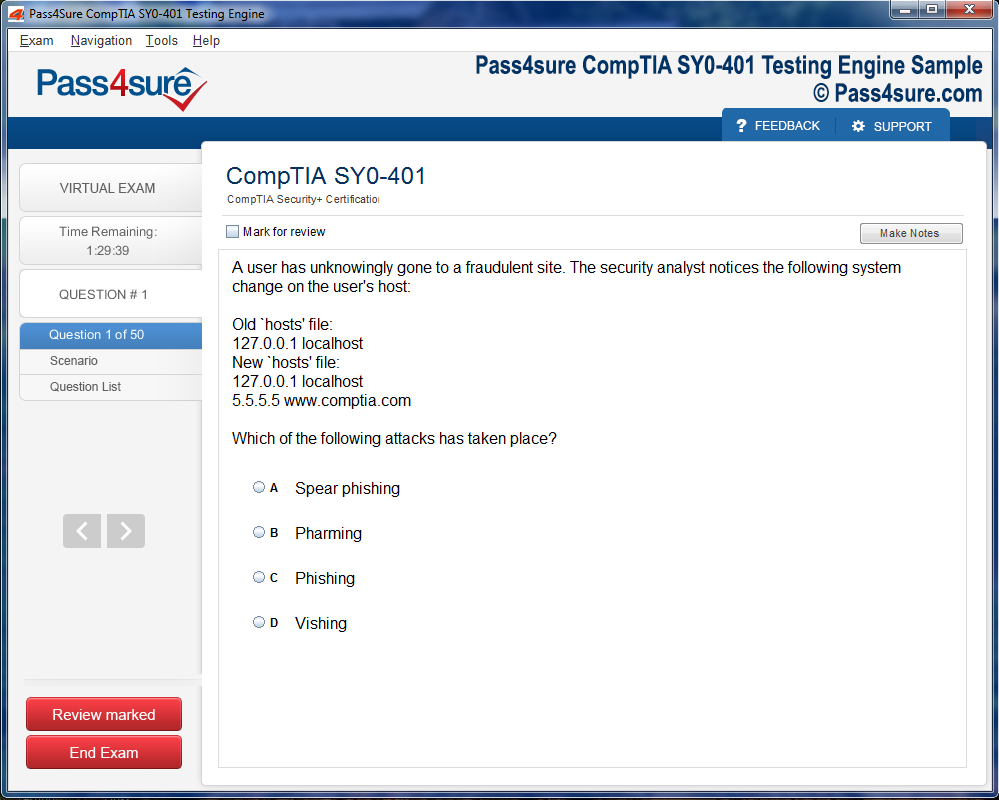
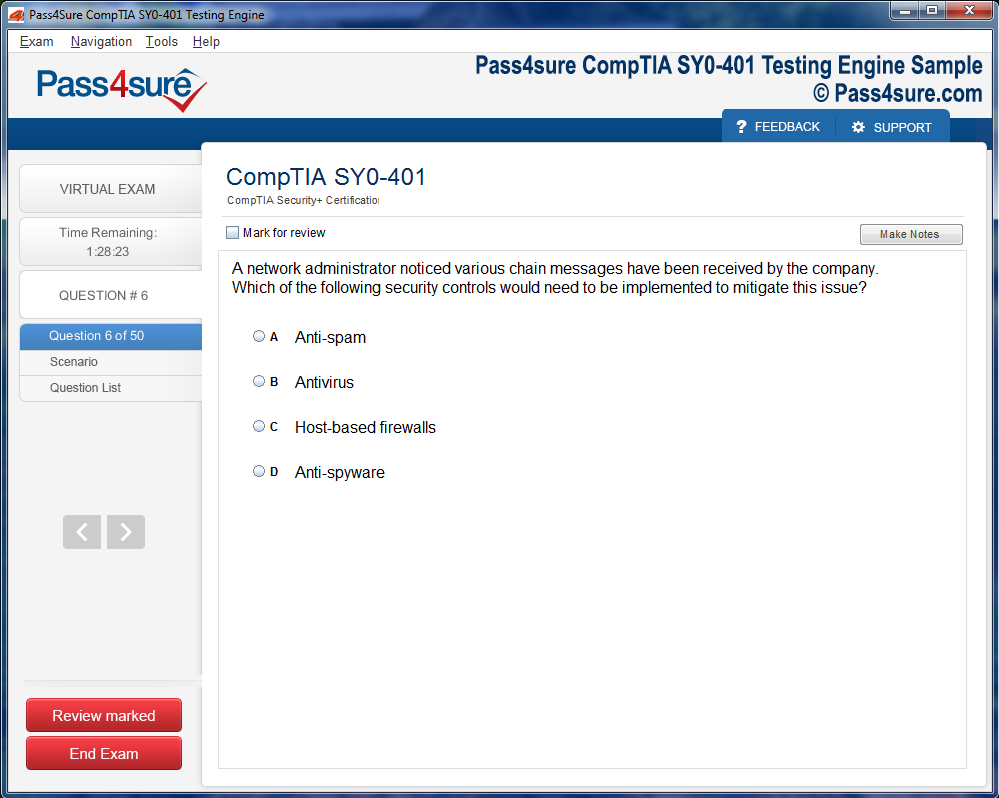
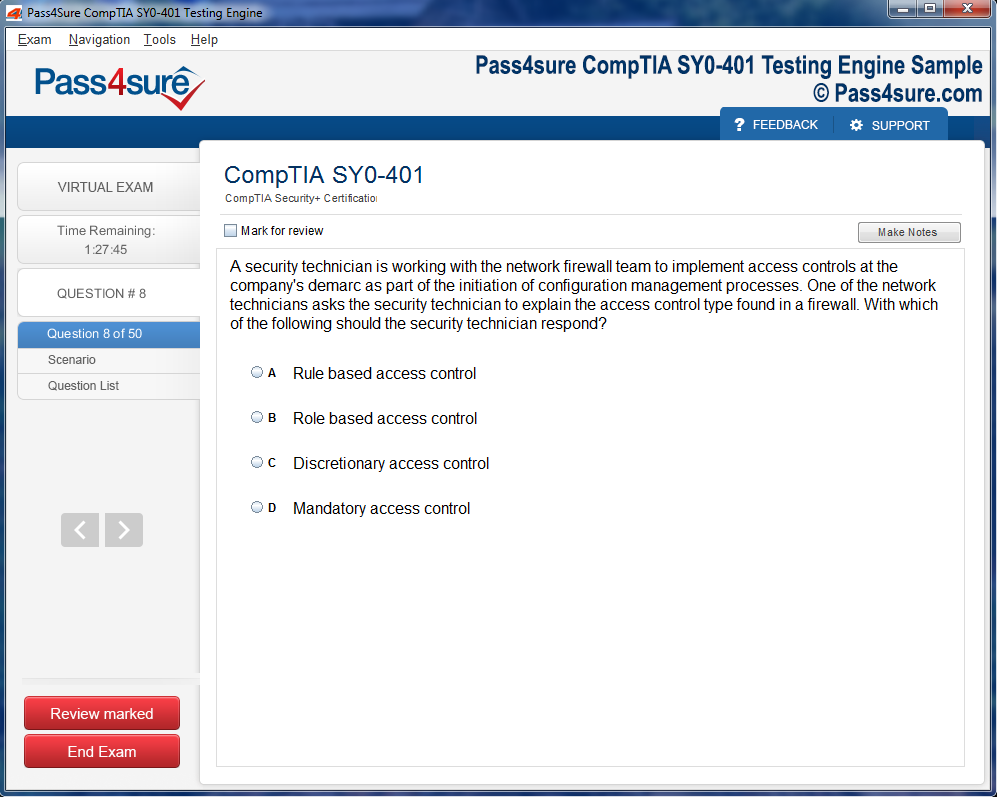
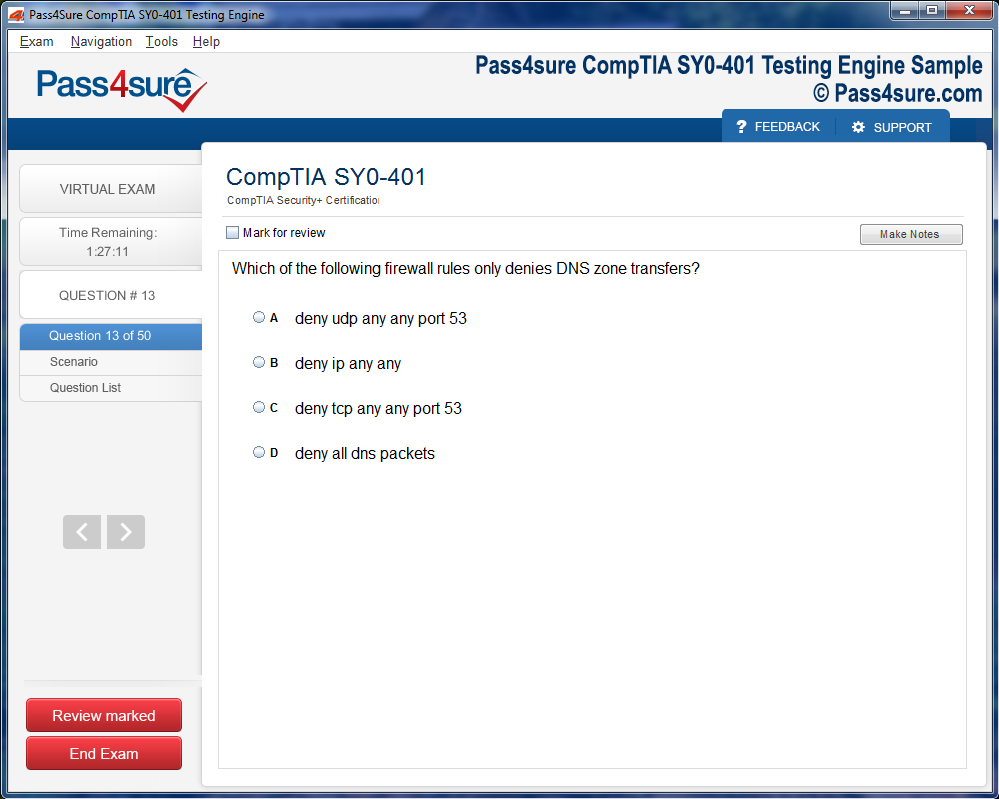
Product Screenshots
Frequently Asked Questions
How does your testing engine works?
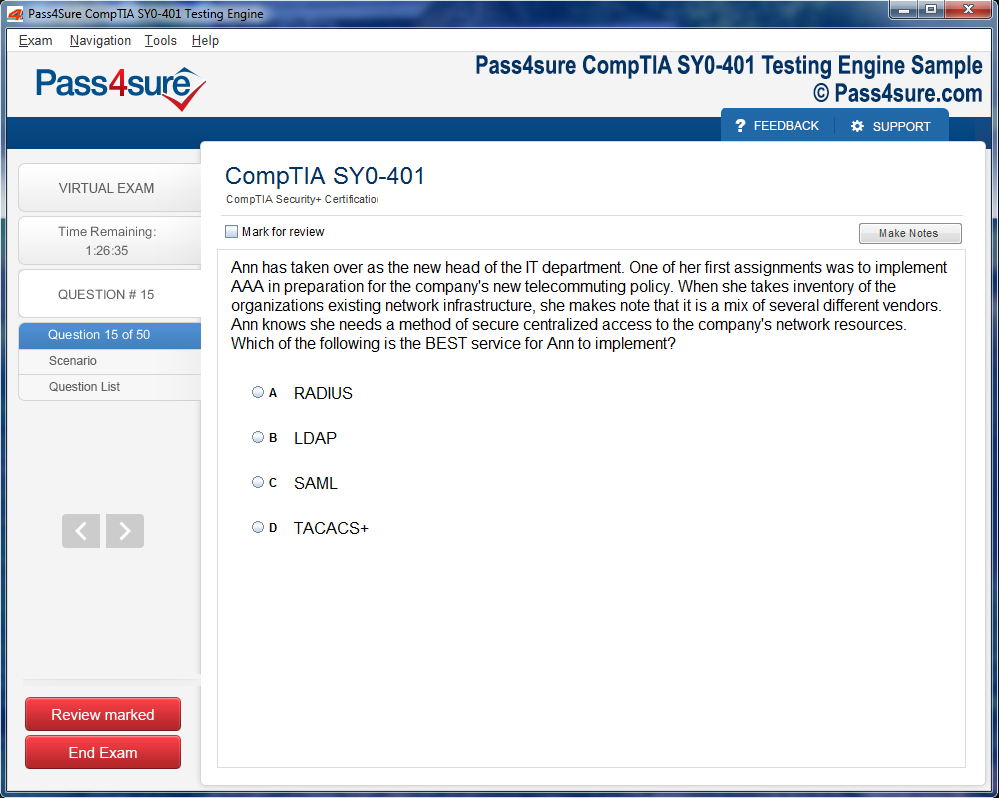
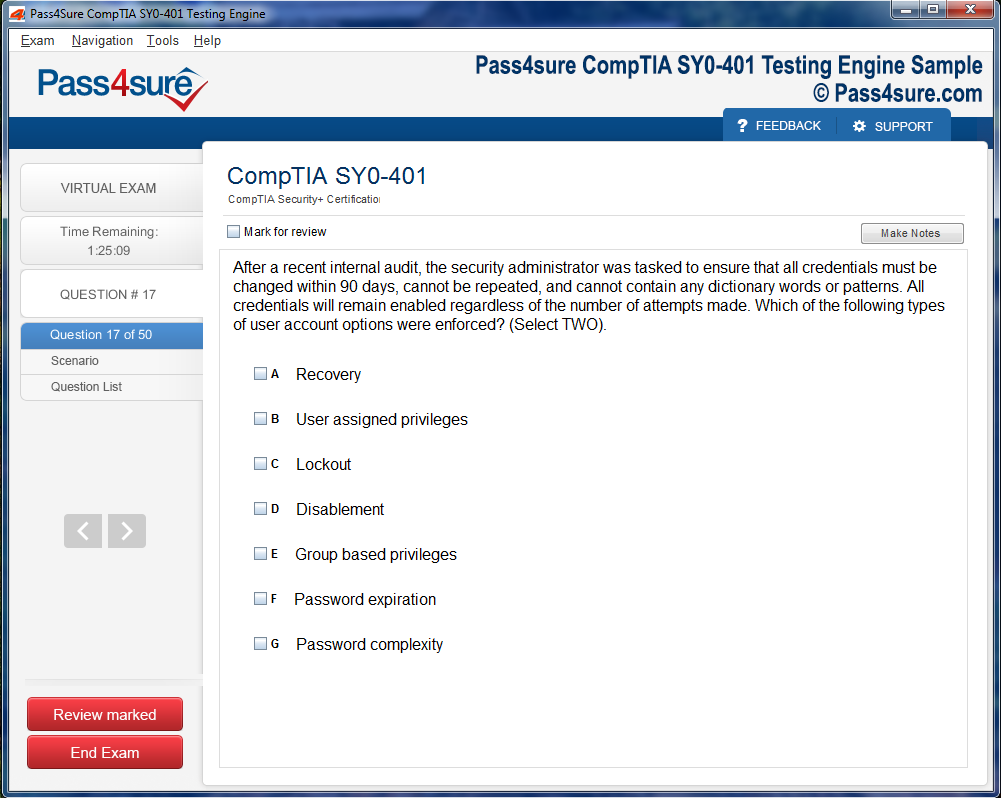
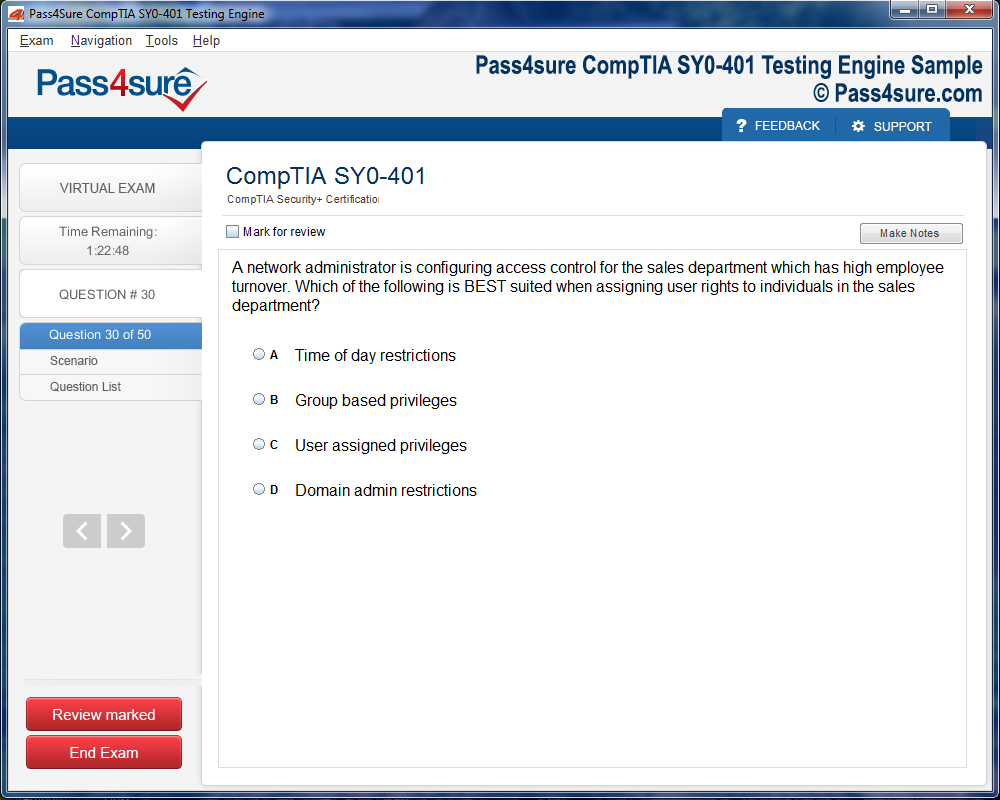
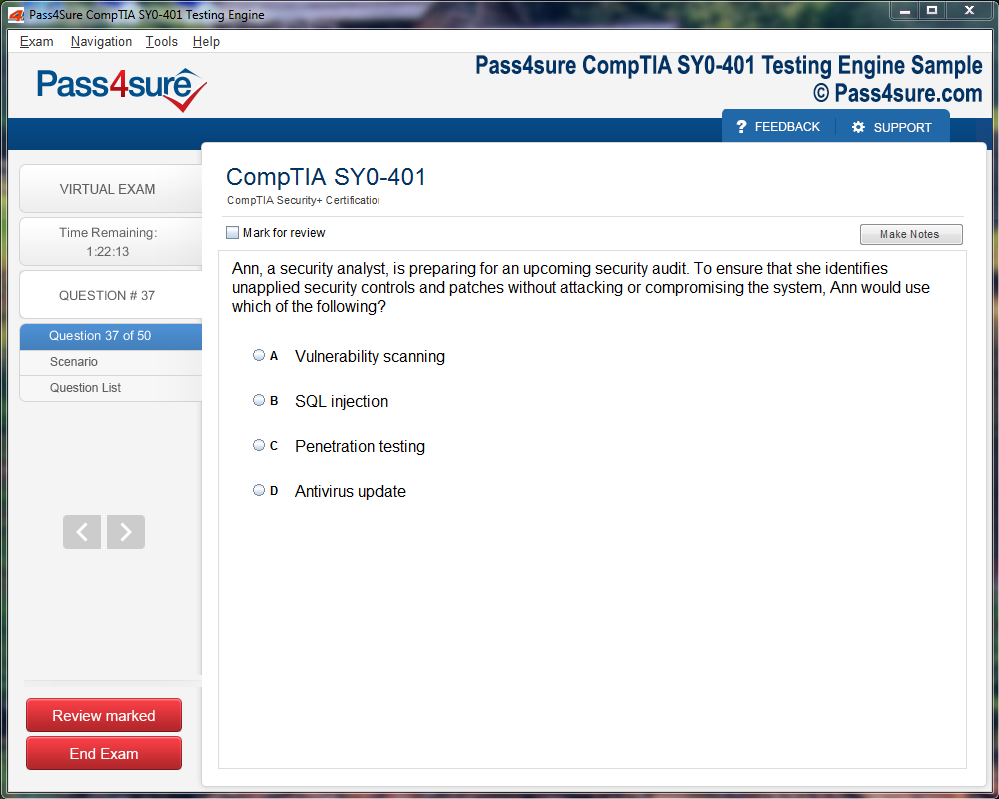
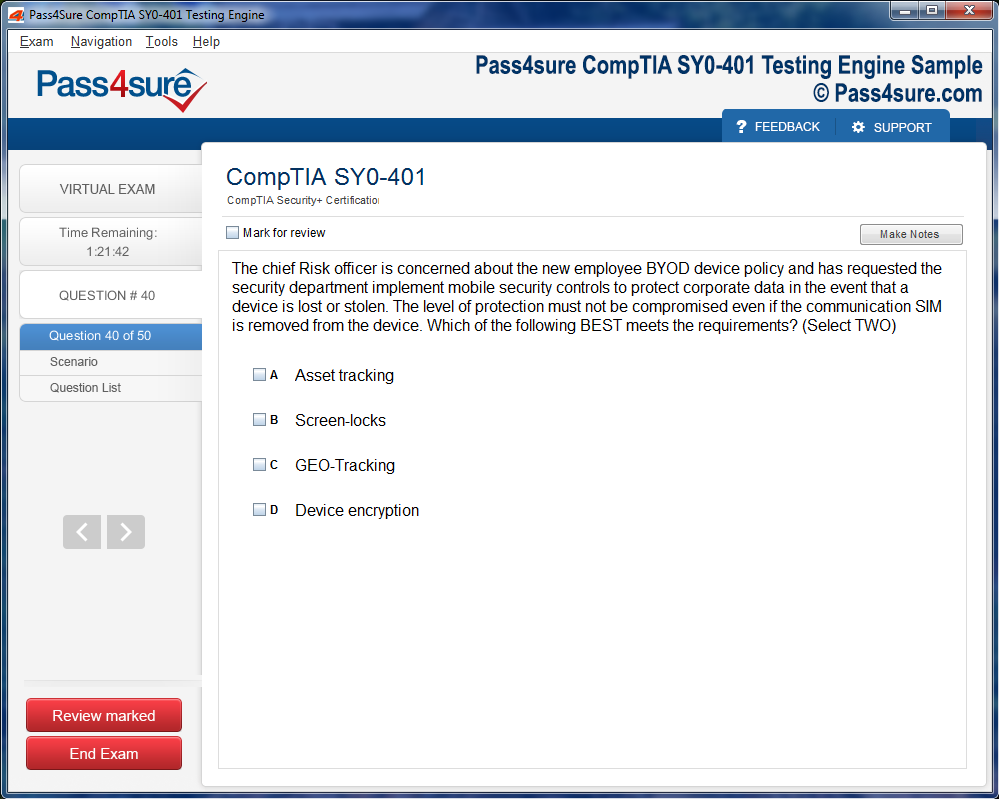
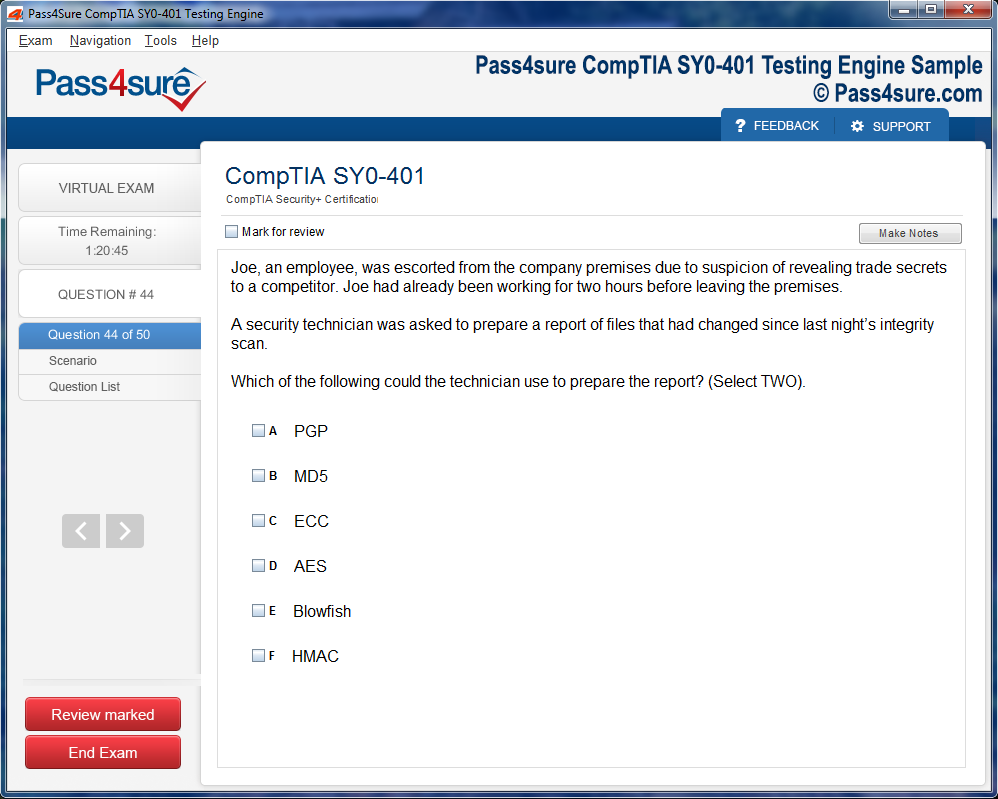
Once download and installed on your PC, you can practise test questions, review your questions & answers using two different options 'practice exam' and 'virtual exam'. Virtual Exam - test yourself with exam questions with a time limit, as if you are taking exams in the Prometric or VUE testing centre. Practice exam - review exam questions one by one, see correct answers and explanations.
How can I get the products after purchase?
All products are available for download immediately from your Member's Area. Once you have made the payment, you will be transferred to Member's Area where you can login and download the products you have purchased to your computer.
How long can I use my product? Will it be valid forever?
Pass4sure products have a validity of 90 days from the date of purchase. This means that any updates to the products, including but not limited to new questions, or updates and changes by our editing team, will be automatically downloaded on to computer to make sure that you get latest exam prep materials during those 90 days.
Can I renew my product if when it's expired?
Yes, when the 90 days of your product validity are over, you have the option of renewing your expired products with a 30% discount. This can be done in your Member's Area.
Please note that you will not be able to use the product after it has expired if you don't renew it.
How often are the questions updated?
We always try to provide the latest pool of questions, Updates in the questions depend on the changes in actual pool of questions by different vendors. As soon as we know about the change in the exam question pool we try our best to update the products as fast as possible.
How many computers I can download Pass4sure software on?
You can download the Pass4sure products on the maximum number of 2 (two) computers or devices. If you need to use the software on more than two machines, you can purchase this option separately. Please email sales@pass4sure.com if you need to use more than 5 (five) computers.
What are the system requirements?
Minimum System Requirements:
- Windows XP or newer operating system
- Java Version 8 or newer
- 1+ GHz processor
- 1 GB Ram
- 50 MB available hard disk typically (products may vary)
What operating systems are supported by your Testing Engine software?
Our testing engine is supported by Windows. Andriod and IOS software is currently under development.
Complete Guide to Juniper JN0-1103 Exam Success
Embarking on the expedition to conquer the Juniper JN0-1103 exam is akin to navigating an intricate lattice of protocols, devices, and command hierarchies. Unlike superficial assessments, this exam demands both cognitive comprehension and dexterous interaction with Junos OS configurations. It measures the candidate’s acumen in networking fundamentals while simultaneously evaluating operational finesse, creating a symbiosis of theory and praxis that is essential for modern network professionals.
The exam spans a multifaceted terrain: routing algorithms, switching paradigms, security orchestration, and automation ideologies. Memorization alone is insufficient; instead, an immersive understanding of packet traversal, device interoperability, and Junos OS command efficacy is requisite. This dualistic framework—conceptual cognition coupled with applied proficiency—forms the cornerstone of exam achievement.
Junos OS, the fulcrum of the exam, is a network operating system celebrated for its modularity, stability, and systematic CLI architecture. The OS bifurcates into the control plane, orchestrating routing decisions and maintaining network topology awareness, and the forwarding plane, executing the actual packet propagation. Mastery of these planes empowers candidates to troubleshoot, configure, and anticipate network behavior, transforming abstract knowledge into pragmatic capability.
Cultivating the proper mental schema is equally pivotal. Exam preparation can feel labyrinthine, but systematic planning mitigates cognitive overload. Start by dissecting exam objectives, prioritizing weaker domains, and integrating hands-on exercises. Simulation of routing, switching, and security scenarios enhances kinesthetic learning, embedding theoretical constructs into operational reflexes—a critical advantage under examination pressure.
Authentic resources fortify preparation. Juniper’s official documentation, study manuals, and scenario-based questions serve as primary conduits. Supplementation through community discourse, simulation software, and interactive labs yields a holistic perspective. The objective transcends mere certification; it is fluency in network operations, fostering enduring professional confidence.
The foundation is established by harmonizing Junos OS comprehension with networking principles and strategic exam preparation. This groundwork paves the way to explore intricate routing mechanisms, layered security models, and automation methodologies, transforming the daunting path to JN0-1103 certification into a structured voyage.
Deep Dive into Junos OS Architecture and Functionalities
Junos OS embodies a sophisticated yet intuitive architecture, integrating modularity with operational resilience. It leverages a microkernel design philosophy, separating system processes to maintain stability even during high-load scenarios. The control plane operates as the cerebral cortex, executing decision-making algorithms, maintaining routing tables, and updating forwarding information bases. In parallel, the forwarding plane functions as the peripheral nervous system, propelling packets along optimized paths with minimal latency.
Command-line proficiency is indispensable. Junos CLI is hierarchical, supporting configuration, operational, and file-system modes, each with distinct syntactical conventions. An understanding of commit and rollback mechanisms ensures safe configuration deployment, while the use of operational commands allows real-time network state inspection. This command fluency bridges the theoretical understanding of network topologies with hands-on operational command.
Furthermore, Junos implements logical separation through virtual routing instances, firewall filters, and policy hierarchies. Grasping these abstractions enables candidates to design networks that are both scalable and secure. The architecture also integrates automation frameworks, including scripting via SLAX and Python, which allow programmatic interaction with devices, streamlining repetitive tasks, and enabling more sophisticated network orchestration.
In preparation for the exam, one must internalize not only these architectural nuances but also their implications on troubleshooting, optimization, and deployment. Mastery of Junos OS is a conduit to anticipating network behavior under various stress conditions and configuration changes.
Routing Paradigms and Protocolic Intricacies
Routing, the cerebral heart of network communication, requires nuanced comprehension. Juniper Networks deploys protocols such as OSPF, IS-IS, and BGP, each with distinct topologies, path selection criteria, and convergence behaviors. Candidates must dissect link-state and distance-vector paradigms, understanding algorithmic differences, metric calculations, and hierarchical implementations.
OSPF, for instance, is predicated upon link-state awareness and necessitates meticulous configuration of areas, interfaces, and neighbor adjacencies. IS-IS, often underrated, employs a similar link-state approach but differs in nomenclature and operational mechanisms. BGP, the border gateway protocol, governs inter-domain communication and hinges upon policy-based route selection, path attributes, and route reflectors for scalable deployments.
Practical mastery involves not just memorization but scenario-based simulations. Configuring route redistribution, manipulating preference metrics, and anticipating convergence behavior are exercises that translate theoretical understanding into tangible proficiency. This skill set is invaluable for both exam scenarios and enterprise-level network architecture.
Switching Techniques and Layered Network Dynamics
Switching constitutes the structural scaffolding of network environments. Candidates must comprehend VLAN segmentation, trunking protocols, and spanning-tree dynamics to prevent loops and optimize traffic flow. Juniper switches employ mechanisms such as Virtual Chassis and Ethernet switching paradigms, creating both operational redundancy and logical simplification.
Advanced topics include multicast configurations, IGMP snooping, and layer-2 security mechanisms. These constructs ensure traffic isolation, efficient bandwidth utilization, and protection against common vulnerabilities like MAC flooding or broadcast storms. Hands-on configuration of VLANs, port assignments, and spanning-tree priorities reinforces theoretical understanding and operational dexterity.
Security Orchestration and Policy Enforcement
Network security transcends firewall rules; it encompasses holistic policy orchestration and proactive threat mitigation. Candidates must understand Juniper SRX devices, security zones, and policy-based routing to enforce granular control over traffic flows. Stateful inspection, NAT configurations, and security policies must be intricately aligned to protect against internal and external threats.
Encryption mechanisms, VPN technologies, and intrusion prevention systems are integrated into the Junos ecosystem, offering layered security paradigms. Exam preparation necessitates practice in designing security topologies, implementing access policies, and simulating threat scenarios to evaluate resilience. Understanding these concepts ensures candidates can maintain both operational integrity and exam readiness.
Automation and Programmatic Network Management
Automation is the avant-garde of modern networking, enabling efficiency and reducing human error. Junos supports automation through scripting languages like Python and SLAX, alongside configuration management frameworks such as Ansible. Candidates must explore API integration, scheduled task automation, and event-driven configuration deployment.
Hands-on exercises might include writing scripts for automated interface configuration, monitoring system logs, or orchestrating multi-device updates. Proficiency in automation demonstrates not only exam readiness but also forward-thinking professional capability in an increasingly programmable network landscape.
Exam Strategy and Cognitive Optimization
Examination success is contingent upon cognitive strategy as much as technical knowledge. Structured study plans, spaced repetition, and scenario-based simulations enhance retention and operational fluency. Practicing time management, prioritizing high-yield topics, and simulating exam conditions cultivate confidence and mitigate performance anxiety.
Equally important is meta-cognition: reflecting on mistakes, analyzing configuration outcomes, and iterating upon learning strategies. This approach converts preparation into a dynamic, self-reinforcing cycle of improvement, embedding both technical knowledge and cognitive resilience necessary for the high-stakes environment of the JN0-1103 exam.
The Quintessence of Routing in Contemporary Networks
Routing is not merely a mechanistic process; it is the cerebral cortex of networking, orchestrating data trajectories across labyrinthine topologies. Every packet traverses a meticulously calculated route, a journey dictated by algorithms, metrics, and administrative hierarchies. In the realm of Juniper devices, the precision of routing is amplified by Junos OS, which furnishes a meticulously structured interface for protocol manipulation, policy formulation, and interface orchestration.
Static Versus Dynamic Paradigms
Static routing embodies determinism; every pathway is explicitly defined, akin to a cartographer etching permanent routes across a map. While its predictability is unparalleled, it lacks adaptability. Dynamic routing, conversely, operates with synesthetic awareness, responding to topological flux with protocols such as OSPF, BGP, and RIP. The interplay between static and dynamic methodologies underscores a network engineer’s strategic discretion, determining when to enforce rigidity and when to permit fluidity.
Architectural Underpinnings of Junos OS
Juniper devices employ Junos OS, an operating system that epitomizes hierarchical elegance. Its CLI stratification allows engineers to ascend from interface-level minutiae to overarching routing policies with seamless granularity. Hierarchical configuration ensures minimal cognitive overhead while enabling surgical precision, whether configuring OSPF areas, defining BGP communities, or implementing sophisticated firewall filters. Each configuration layer resonates with the ethos of modular design, fostering both maintainability and scalability.
OSPF: The Link-State Luminary
Open Shortest Path First (OSPF) operates on the principle of link-state awareness. Utilizing Dijkstra’s algorithm, it calculates optimal paths through exhaustive topological scrutiny. Each router maintains a comprehensive map of network adjacencies, ensuring deterministic and loop-free packet flows. Juniper devices enhance OSPF implementation with features such as graceful restart and robust area partitioning, empowering engineers to sculpt resilient, high-performance routing fabrics.
BGP: Custodian of Interdomain Traffic
Border Gateway Protocol (BGP) governs the interdomain orchestration of routes, applying path-vector logic to manage policy-driven traffic distribution. Attributes such as AS_PATH, LOCAL_PREF, and MED imbue the protocol with fine-tuned control over route selection, essential for multi-homed networks or complex enterprise ecosystems. Understanding BGP nuances, including route reflection and confederation design, is paramount for orchestrating intercontinental network infrastructures with minimal latency and maximal reliability.
RIP and Distance-Vector Dynamics
Routing Information Protocol (RIP), though diminished in contemporary enterprises, offers an instructive case study in distance-vector mechanics. Its simplicity, predicated on hop counts, belies deeper lessons in convergence timing, split horizon, and route poisoning. Mastery of RIP contributes to a holistic understanding of routing philosophy, ensuring that foundational knowledge complements advanced protocol fluency.
Route Propagation and Administrative Hierarchy
Routing is orchestrated through administrative distances, a hierarchy that adjudicates route preference when multiple pathways coexist. The interplay of metrics, from OSPF’s cost calculation to BGP’s policy-influenced attributes, governs propagation. Network engineers must decipher routing tables with perspicacity, interpreting route origin, next-hop nuances, and temporal stability to preempt anomalies such as flapping or oscillation.
Troubleshooting: Deciphering the Routing Enigma
Effective network troubleshooting is both an art and a science. Junos OS provides an arsenal of diagnostic instruments, from show route outputs to traceoptions that illuminate packet journeys with microscopic fidelity. Engineers must cultivate a sagacious mindset, able to diagnose misconfigurations, adjacency lapses, and routing loops with alacrity. Each troubleshooting exercise refines analytical acumen, translating theoretical mastery into operational competence.
Virtual Chassis and Switch Integration
Juniper’s virtual chassis and EX series switches exemplify the confluence of routing and switching. Virtual chassis technology unites multiple devices into a singular operational entity, simplifying topology management while enhancing redundancy. Configuring IP addressing, VLAN assignments, and interface parameters within this architecture necessitates a nuanced understanding, ensuring that packets traverse logical and physical constructs seamlessly.
Route Filtering and Policy Implementation
Route filtering in Junos OS transcends mere control; it is an instrument of strategic orchestration. Policy statements, match conditions, and action sequences empower engineers to sculpt route propagation, enforce security postures, and optimize traffic flow. By defining complex filters and policy hierarchies, network architects exercise dominion over packet behavior, harmonizing performance with governance imperatives.
Convergence and Network Stability
Network convergence represents the culmination of routing protocol efficiency. Rapid recalculation following topology changes minimizes packet loss and latency, yet excessive flapping or misalignment can destabilize networks. Engineers must understand the temporal dynamics of convergence, adjusting timers, priorities, and redistribution policies to maintain equilibrium across sprawling infrastructures.
Hands-On Lab Immersion
Laboratory practice is indispensable for embedding routing concepts. Emulators, virtual labs, or physical device setups provide experiential learning, translating abstract theory into tangible skill. Exercises such as static route configuration, OSPF area establishment, and BGP peer negotiation mirror the complexities of production environments, cultivating dexterity, foresight, and troubleshooting proficiency.
Analytical Thinking in Routing Design
Routing mastery extends beyond mechanical configuration; it demands anticipatory reasoning. Network architects must envision packet trajectories, mitigate loops, and optimize pathways under diverse load conditions. Each design decision reverberates across the network, influencing latency, redundancy, and resource allocation. Juniper devices, with their granular controls and robust observability, furnish the canvas upon which such analytical foresight is executed.
Interface Orchestration and IP Schema Design
Interface configuration is the nexus of connectivity. Assigning IP addresses, subnet masks, and VLAN memberships constitutes the foundational scaffolding for routing. Strategic IP schema design enhances readability, scalability, and fault isolation, while precise interface orchestration ensures seamless inter-device communication, forming the structural spine of robust network architectures.
Monitoring and Real-Time Diagnostics
Monitoring encompasses more than passive observation; it is an active exploration of network vitality. Junos OS commands such as show ospf neighbor, show bgp summary, and monitor traffic empower engineers to dissect operational states, anticipate anomalies, and enact preemptive measures. The interplay between monitoring and proactive management distinguishes exemplary network maintenance from reactive troubleshooting.
Topology Design and Redundancy Strategies
Effective routing is inseparable from topology design. Hierarchical models, redundant pathways, and failover strategies underpin resilience. Engineers must evaluate trade-offs between cost, complexity, and performance, integrating loop prevention mechanisms, redundant link architectures, and optimal path selection to craft enduring and efficient network ecosystems.
Interdomain and Intradomain Coordination
Intricate networks often traverse multiple administrative domains, necessitating both interdomain and intradomain coordination. Protocol interoperability, route redistribution, and consistent policy enforcement ensure harmonious operation across disparate segments. Juniper devices facilitate this coordination through flexible protocol support, granular configuration, and comprehensive observability, enabling engineers to manage complexity without sacrificing precision.
Continuous Learning and Skill Refinement
Routing is an evolving discipline; protocols, best practices, and device capabilities continuously advance. Engineers must cultivate a mindset of perpetual learning, engaging with emerging technologies, experimenting with configurations, and analyzing case studies. Mastery is iterative, blending theoretical acumen with practical execution to achieve nuanced, context-aware decision-making.
The Quintessence of Switching in Modern Networks
Switching constitutes the fulcrum upon which contemporary networking pivots. In enterprise environments, switches orchestrate the meticulous choreography of data frames, navigating the labyrinth of MAC addresses with surgical precision. Layer 2 switching mitigates broadcast storms and optimizes throughput by attenuating superfluous traffic, ensuring that packets traverse the most propitious pathways. Advanced switching paradigms leverage micro-segmentation, dynamic MAC learning, and frame prioritization, culminating in an architecture that balances velocity with reliability. Within the Juniper ecosystem, the adept manipulation of these switching nuances is indispensable for both scholastic and operational efficacy.
VLANs: Segregation and Synthesis of Network Realms
Virtual Local Area Networks (VLANs) epitomize the art of logical network partitioning, creating discrete broadcast domains within a singular physical topology. The alchemy of VLANs enhances security by sequestering sensitive nodes, diminishes congestion through domain isolation, and refines performance by streamlining communication pathways. Configuration on Juniper switches entails assigning VLAN IDs to interfaces, orchestrating trunk links for multiplexed VLAN transmission, and deploying Layer 3 interfaces for inter-VLAN routing. The dexterity to troubleshoot misconfigured VLANs, rectify trunking anomalies, and validate connectivity is a sine qua non for network professionals.
Trunking and Inter-VLAN Connectivity
Trunk links function as conduits, ferrying multiple VLANs across a single physical interface with deft encapsulation protocols. IEEE 802.1Q tagging ensures the preservation of VLAN identity across disparate switches, preventing domain ambiguity. In practical scenarios, trunk misconfigurations often manifest as blackholes, where traffic fails to reach intended segments, or as broadcast surges, undermining network equilibrium. Mastery of trunking intricacies, including native VLAN designation and protocol compatibility, empowers practitioners to maintain coherence in sprawling network architectures.
Spanning Tree Protocol: Arbiter of Redundancy
The Spanning Tree Protocol (STP) is the sentinel safeguarding loop-free topologies in redundant switching environments. STP variants—Rapid Spanning Tree Protocol (RSTP) and Multiple Spanning Tree Protocol (MSTP)—mediate port states, elect root bridges, and orchestrate failover mechanisms with meticulous precision. Understanding STP convergence, bridge priority manipulation, and port cost calculations is vital for anticipating network behavior during dynamic reconfigurations. Juniper’s diagnostic utilities provide insights into blocked ports, root bridge elections, and topology recalibrations, enabling proactive remediation of switching aberrations.
Topological Archetypes: Star, Mesh, and Hybrid Configurations
Network topology undergirds the efficacy of switching operations. Star topologies centralize management through a hub-and-spoke schema, offering clarity at the expense of single points of failure. Mesh topologies embrace redundancy, weaving interconnections that bolster fault tolerance but necessitate sophisticated loop prevention. Hybrid architectures amalgamate topological virtues, demanding a nuanced comprehension of traffic flow, latency implications, and resilience strategies. Examiners frequently craft complex topologies requiring simultaneous VLAN configuration, STP verification, and trunk orchestration to evaluate conceptual depth and operational dexterity.
Layer 2 and Layer 3 Integration on Juniper Devices
Juniper switches blur the demarcation between Layer 2 and Layer 3 functionalities, enabling seamless inter-VLAN routing and policy enforcement. Interface configuration commands, port modes (access versus trunk), and VLAN tagging paradigms constitute the lexicon of operational proficiency. Configuring aggregated links, deploying virtual chassis architectures, and implementing QoS policies accentuate the switch’s versatility. Practical engagement reinforces theoretical understanding, allowing network engineers to orchestrate cohesive architectures, troubleshoot labyrinthine misconfigurations, and validate end-to-end connectivity with confidence.
Experiential Learning through Lab Simulations
Laboratory simulations and real-world deployments accelerate conceptual assimilation, transforming abstract principles into tangible expertise. By constructing multi-switch topologies, assigning VLANs, and probing inter-VLAN communication, candidates witness STP convergence in action and observe protocol interactions in real-time. Scenario-based experimentation cultivates analytical acumen, enabling practitioners to preempt misconfigurations, optimize traffic flow, and reinforce fault-tolerant designs.
Troubleshooting Paradigms and Analytical Proficiency
Troubleshooting in switching environments demands perspicacity, diagnostic precision, and methodical reasoning. Frame analysis, MAC table inspection, and interface statistics illuminate latent issues, while systematic VLAN and trunk verification rectify misalignments. Network anomalies—ranging from broadcast storms to asymmetric routing—require both heuristic insight and procedural rigor. Mastery of these troubleshooting paradigms empowers engineers to restore equilibrium, maintain service continuity, and refine architectural design iteratively.
Policy Implementation and Security Considerations
Switches transcend mere data conduits, acting as enforcers of network policy and guardians of security. VLAN-based segmentation limits the lateral movement of threats, while Access Control Lists (ACLs) regulate packet traversal with granularity. Port security, DHCP snooping, and dynamic ARP inspection constitute defensive layers, thwarting malicious actors and mitigating internal vulnerabilities. Juniper platforms afford sophisticated policy frameworks, marrying security with operational agility and ensuring that networks are both robust and compliant.
Advanced Switching Features and Optimization
Modern switches encompass a panoply of advanced features designed to elevate performance and reliability. Link aggregation enhances bandwidth and redundancy, while Quality of Service (QoS) mechanisms prioritize latency-sensitive traffic. Virtual Chassis and chassis clustering extend manageability, simplifying large-scale deployments. Comprehension of these features, coupled with practical deployment, ensures optimal resource utilization, minimal downtime, and a harmonious balance between performance and resilience.
Observability, Monitoring, and Proactive Management
Network observability transcends mere monitoring, providing predictive insights and actionable intelligence. Juniper switches furnish telemetry data, port statistics, and protocol logs that illuminate operational trends. Proactive management—rooted in data-driven analysis—prevents congestion, preempts loops, and ensures topological integrity. By cultivating a vigilant observability culture, engineers transform reactive troubleshooting into anticipatory optimization, fostering networks that are agile, resilient, and self-healing.
Synthesis of VLANs, Switching, and Topological Strategy
The confluence of VLAN configuration, switching mastery, and topological strategy engenders network architectures that are both efficient and resilient. Synthesizing these domains requires an appreciation for logical segmentation, redundancy, and performance optimization. Through iterative practice, scenario analysis, and judicious configuration, candidates cultivate a mental model capable of navigating complex network landscapes with aplomb, ensuring operational continuity and strategic agility.
Security Imperatives in Modern Networking
The contemporary digital landscape has transmogrified the notion of network security from a discretionary measure into an unequivocal imperative. With escalating cyber perils, organizational infrastructure mandates an intricate lattice of security stratagems to thwart malevolent incursions. Network custodians must cultivate a perspicacious understanding of defensive apparatuses to safeguard data sanctuaries. Juniper devices, imbued with comprehensive security mechanisms, epitomize the amalgamation of policy precision, firewall acuity, and NAT sophistication, delineating an ecosystem where protection is not an adjunct but an intrinsic architecture.
Security in Junos OS is architected with a nuanced comprehension of zones, policies, and stateful inspection protocols. This triad orchestrates the meticulous governance of traffic, engendering a milieu where access is neither indiscriminate nor capricious. Prospective JN0-1103 aspirants must not only grasp theoretical underpinnings but also cultivate dexterity in configuring and troubleshooting these mechanisms, aligning technical finesse with procedural sagacity.
Stratification through Security Zones
Security zones constitute the bedrock of network segmentation, effectuating a hierarchical partitioning predicated on trust gradations. Interfaces coalesce into logical assemblages, each imbued with a designated level of trust, orchestrating a matrix where intra- and inter-zone communication is judiciously regulated. Such compartmentalization mitigates lateral threat propagation, ensuring that an intrusion within a low-trust enclave cannot permeate critical high-trust corridors.
Policies function as the sentinels between zones, meticulously delineating the permissible vectors of traffic. Attributes encompassing protocol typology, IP provenance, and destination granularity are meticulously codified. Action paradigms—permit, deny, or reject—imbue administrators with granular authority over network behavior. Exam scenarios frequently emulate authentic operational exigencies, compelling candidates to architect, deploy, and validate policies that optimize security while maintaining operational efficacy.
Firewall Dynamics and Stateful Inspection
Juniper firewalls transcend rudimentary packet filtering, embodying an arsenal capable of discerning and regulating traffic based on multifaceted criteria. Security policies extend their reach beyond mere IP addresses, encapsulating protocol typologies and application-specific heuristics. Stateful inspection operates as the linchpin of defense, meticulously tracking session inception and termination to preclude spoofed or unsolicited ingress.
Administrators must attain proficiency in policy construction, interface application, and diagnostic evaluation of blocked or misrouted packets. Mastery entails understanding policy precedence, logging nuances, and inter-policy interactions, engendering an environment where security mechanisms operate synergistically rather than in isolation. Candidates confronting the JN0-1103 examination encounter scenarios demanding not only technical execution but also analytical reasoning to resolve complex security quandaries.
Network Address Translation as a Protective Veil
Network Address Translation (NAT) functions as both a conduit and a bulwark, enabling internal networks to interface with external entities while obfuscating private address spaces. NAT mitigates exposure, reducing the attack surface and conferring anonymity upon internal hosts. Junos OS supports an array of NAT modalities, including source, destination, and static configurations, each serving a distinct strategic purpose.
The integration of NAT with security policies necessitates meticulous calibration. Source NAT facilitates outbound connectivity with translated addresses, whereas destination NAT enables controlled inbound access to internal services. Static NAT ensures persistent address mapping for mission-critical hosts. Exam scenarios may juxtapose NAT with policy enforcement, testing candidates’ ability to synthesize conceptual understanding with operational accuracy, requiring careful orchestration to avert conflicts or unintended exposure.
Virtual Private Networks and Encrypted Connectivity
Virtual Private Networks (VPNs) epitomize secure perambulation across untrusted landscapes. Juniper’s IPsec VPN framework encompasses encryption, authentication, and integrity verification, forming a triad of cryptographic assurance. VPN architecture entails tunnels, gateways, and proposals, each representing a pivotal component in the secure conveyance of sensitive data.
Candidates must comprehend the interplay between phase one and phase two negotiations, the nuances of cryptographic algorithms, and the implications of policy deployment within encrypted tunnels. Practical exercises often involve configuring site-to-site and remote-access VPNs, simulating scenarios where confidentiality, authentication, and data integrity are paramount. Proficiency in VPNs ensures candidates can construct fortified communication channels while anticipating potential pitfalls inherent in complex networking environments.
Policy Configuration Best Practices
Security policy configuration transcends mere syntax adherence, evolving into a discipline of foresight and operational prudence. Consistent policy auditing uncovers latent vulnerabilities and ensures alignment with organizational mandates. Minimal access principles, restricting permissions to the bare essentials, mitigate risk exposure. Enabling logging for critical traffic engenders transparency, furnishing administrators with actionable intelligence for real-time threat assessment and post-event forensics.
Candidates internalizing these principles cultivate a dual perspective: one of tactical execution and another of strategic oversight. Policies are not static artifacts; they must evolve in tandem with emerging threats, network growth, and regulatory exigencies. Real-world administrators often employ iterative review cycles, leveraging analytics to refine rulesets, prioritize alerts, and calibrate responses, thereby maintaining an agile defensive posture.
Hands-On Practice and Skill Consolidation
Theoretical comprehension is insufficient without experiential reinforcement. Hands-on laboratories, encompassing firewall policy simulation, NAT implementation, and VPN configuration, bridge the chasm between conceptual understanding and operational execution. Simulation environments allow candidates to manipulate traffic flows, observe policy impact, and troubleshoot anomalies without jeopardizing production infrastructure.
Through iterative practice, aspirants develop an intuitive grasp of interdependencies, precedence hierarchies, and potential conflict resolution. Scenario-based exercises enhance problem-solving acumen, demanding candidates to assess network topologies, predict traffic behavior, and implement corrective measures. This practical immersion ensures readiness for both examination exigencies and real-world operational challenges, fostering a synthesis of analytical reasoning, technical dexterity, and strategic foresight.
Intricacies of Firewall Logging and Analytics
Firewall logging constitutes a critical conduit for observability and incident response. Junos OS furnishes granular logging capabilities, capturing session initiations, policy matches, and anomalous activity. Analysis of log data enables identification of reconnaissance attempts, policy misconfigurations, and patterns indicative of persistent threats.
Advanced practitioners employ log correlation and aggregation techniques, transforming raw data into actionable intelligence. Integration with Security Information and Event Management (SIEM) systems enhances visibility, facilitating proactive threat mitigation. For exam aspirants, the ability to interpret logs, trace session flows, and diagnose security events represents a vital skill set, underscoring the interplay between operational vigilance and technical proficiency.
NAT Complexity in Multi-Zone Environments
In sophisticated networks, NAT implementation is seldom monolithic. Multi-zone architectures necessitate nuanced NAT strategies to reconcile internal-external interactions while maintaining security integrity. Dynamic NAT provides ephemeral address translation, balancing load and obfuscation, whereas static NAT ensures deterministic connectivity for servers requiring consistent external exposure.
Candidates must reconcile NAT deployment with security policies, avoiding inadvertent rule conflicts, route asymmetry, or exposure vulnerabilities. Exam scenarios frequently present topologies with overlapping subnets or cross-zone requirements, testing the aspirant’s capacity to harmonize translation mechanisms with rigorous policy enforcement. Understanding NAT in these contexts elevates candidates’ operational sophistication and strategic foresight.
VPN Integration with Policy Enforcement
Integrating VPN tunnels with security policies introduces additional complexity. Policies must account for encrypted traffic, ensuring legitimate communications are permitted while precluding unauthorized access. Tunnel interfaces, often virtualized, necessitate precise application of rules congruent with zone designations and policy hierarchies.
Candidates must consider tunnel endpoints, cryptographic suites, and the interaction with NAT or routing constructs. Practical exercises in this domain simulate real-world challenges, where misconfiguration can compromise confidentiality or connectivity. Mastery involves not only syntax fluency but also conceptual comprehension of secure channel dynamics, reinforcing the aspirant’s capability to navigate multifaceted networking landscapes with confidence and precision.
The Evolution of Network Topologies
Network topologies have metamorphosed from simple star and bus designs to complex, multifaceted architectures underpinning contemporary digital ecosystems. Modern topologies integrate redundant pathways, dynamic routing strategies, and hierarchical layering to enhance resiliency. Candidates must not merely memorize topologies but internalize how logical structures influence convergence times, fault tolerance, and protocol efficiency. In high-stakes environments, a subtle misconfiguration in topology can precipitate cascading failures, making a meticulous comprehension of network layout indispensable.
Protocol Hierarchies and Autonomous Domains
Routing protocols are stratified across hierarchical domains, with distinct operational paradigms for intradomain and interdomain communication. OSPF orchestrates internal routing with meticulous link-state advertisements, whereas BGP navigates interdomain traffic with policy-driven path selection. Autonomous system interactions depend on attributes such as AS path, MED, and community strings, forming a lexicon of preferences that dictate data traversal. A nuanced understanding of these mechanisms transcends mere memorization, demanding a cognitive model of how protocols interact under dynamic loads, policy constraints, and emergent network events.
MPLS: Traffic Engineering and Label Paradigms
Multiprotocol Label Switching transforms traditional IP forwarding by introducing labels that dictate packet traversal. Traffic engineering becomes feasible through explicit path allocation, optimizing bandwidth utilization, and minimizing latency. Understanding LSP creation, label distribution protocols, and VPN segregation requires assimilating both control plane logic and data plane implementation. MPLS VPNs, with their capacity for overlapping address spaces and policy isolation, exemplify advanced networking paradigms that challenge conventional routing models and demand precise configuration acumen.
Advanced BGP Strategies and Policy Implementation
BGP’s prominence in global internet routing necessitates mastery beyond basic peering. Configurations encompass route reflectors, confederations, and intricate policy controls. Practitioners must navigate the subtleties of prefix filtering, route maps, and community manipulation. Analytical thinking is critical when diagnosing anomalous routing behaviors, oscillating sessions, or unintended route advertisements. An intimate familiarity with session attributes, path selection algorithms, and inter-AS propagation dynamics equips professionals to preempt instability and maintain optimal routing convergence.
Intricate OSPF Dynamics and Area Optimization
OSPF, as an interior gateway protocol, operates on the principle of shortest-path first computation. Advanced features include hierarchical area segmentation, stub area configuration, and the judicious application of cost metrics. Proper area design mitigates flooding overhead and enhances convergence efficiency. Monitoring neighbor adjacency states, LSDB consistency, and SPF recalculation frequencies is vital to preempt suboptimal routing or network partitioning. Mastery of these dynamics cultivates an intuitive understanding of internal routing equilibrium, essential for both exams and operational environments.
Troubleshooting: Methodology and Analytical Acumen
Troubleshooting is a discipline predicated upon logical deduction, empirical validation, and systematic isolation of anomalies. Effective troubleshooting in Junos OS leverages commands such as show route, monitor traffic, and traceroute, but success hinges upon a structured methodology. Identifying root causes involves hypothesizing potential failures, correlating observed symptoms, and iteratively testing interventions. Simulated lab environments reinforce this skill by introducing misconfigurations, intermittent faults, or latency issues, fostering adaptive problem-solving capabilities in a controlled yet unpredictable milieu.
Network Resiliency and Redundancy Techniques
Modern network infrastructures demand resiliency through redundancy, failover protocols, and dynamic reconfiguration. Techniques such as VRRP, redundant LAGs, and dual-homed MPLS circuits ensure continuity amidst hardware failures or link degradations. Understanding convergence mechanics, failover triggers, and protocol timers is paramount to designing networks capable of withstanding disruptions. Professionals must anticipate failure scenarios, modeling potential impacts to preempt service degradation, thereby demonstrating strategic foresight beyond rote configuration knowledge.
Performance Monitoring and Metric Analysis
Performance monitoring transcends passive observation, requiring proactive interpretation of traffic statistics, error rates, and policy enforcement outcomes. Metrics such as jitter, packet loss, and throughput must be contextualized within the operational goals of the network. Log analysis, SNMP polling, and telemetry integration provide a multidimensional view of network health. Professionals adept at synthesizing these data points can preempt congestion, identify policy misalignments, and implement corrective optimizations, reflecting the vigilance expected of network architects and engineers.
Security Integration within Advanced Networks
Security in complex networks demands integration at both the protocol and device layers. Implementing firewall filters, route authentication, and VPN encapsulation ensures data integrity and access control. Advanced networking requires balancing performance with security constraints, such as maintaining low-latency routing while enforcing strict policy compliance. Candidates must understand potential attack vectors within MPLS, BGP, and OSPF frameworks, enabling proactive mitigation strategies that preserve operational stability and protect sensitive information from compromise.
Automation and Orchestration in Contemporary Environments
Automation is reshaping networking, replacing manual interventions with deterministic, script-driven processes. Tools like Ansible, Junos PyEZ, and telemetry-based orchestration facilitate configuration consistency, rapid deployment, and continuous compliance. Professionals must comprehend both the underlying network architecture and the automation logic, ensuring that scripted interventions enhance reliability rather than introduce inadvertent errors. This convergence of software-defined methodology with traditional network engineering epitomizes the skill set required for advanced networking mastery.
Diagnostic Tools and Log Interpretation
Proficiency in diagnostic utilities is critical for real-time problem resolution. Tools for packet capture, log analysis, and flow inspection provide granular insights into network behavior. Understanding log semantics, correlating events across distributed devices, and interpreting anomalies requires cognitive acuity. Professionals must develop a mental model of packet traversal, recognizing normal versus aberrant patterns, and translating observations into actionable remediations. This skill bridges theoretical knowledge with operational efficacy, underpinning both certification and field performance.
Converged Networks and Multiprotocol Integration
Modern networks frequently converge voice, video, and data services, necessitating sophisticated Quality of Service (QoS) strategies, latency optimization, and packet prioritization. Integrating multiprotocol environments, such as MPLS with IPsec VPNs or BGP with OSPF redistribution, demands a comprehensive understanding of protocol interactions and potential conflicts. Advanced engineers must anticipate convergence effects, plan hierarchical policy enforcement, and verify service integrity across multiple dimensions, ensuring seamless user experiences.
Scenario-Based Proficiency and Exam Readiness
Practical mastery is cultivated through scenario-based exercises simulating real-world conditions. These exercises challenge candidates to deploy, troubleshoot, and optimize networks under dynamic constraints. By engaging with scenarios, practitioners internalize the interplay of protocol mechanics, performance metrics, and operational contingencies. This experiential learning reinforces conceptual knowledge, fostering an intuitive, rapid response capability that is invaluable for both examination performance and professional practice.
Emerging Technologies and Adaptive Networking
Emerging paradigms, such as segment routing, SD-WAN, and intent-based networking, redefine how networks are designed, monitored, and optimized. Professionals must remain agile, assimilating new methodologies while retaining foundational principles of routing, traffic engineering, and fault management. Understanding the theoretical underpinnings, practical configurations, and troubleshooting implications of emerging technologies ensures preparedness for evolving network demands, positioning engineers at the vanguard of the profession.
Interdisciplinary Implications and Strategic Thinking
Advanced networking extends beyond device configuration to encompass strategic planning, resource allocation, and interdisciplinary coordination. Engineers must anticipate the implications of design choices on security, performance, and operational costs. Integrating knowledge across domains—protocol engineering, system monitoring, and automation—enables a holistic perspective that transcends technical minutiae. Such strategic thinking differentiates proficient practitioners from those who merely execute commands without understanding systemic consequences.
Cognitive Approaches to Network Optimization
Optimizing complex networks involves cognitive approaches that synthesize data, predict trends, and adapt dynamically. Utilizing predictive analytics, traffic modeling, and heuristic evaluations, engineers can preempt bottlenecks and enhance throughput. Advanced troubleshooting and performance tuning rely on mental models of protocol behavior, network load patterns, and potential failure modes. This intellectual synthesis represents the zenith of networking proficiency, marrying analytical rigor with practical application.
Redundancy in Multi-Layered Architectures
Redundancy is not confined to physical links but permeates multi-layered architectures encompassing control, data, and application planes. Understanding interdependencies, failover hierarchies, and protocol interactions is crucial for resilient design. Engineers must simulate failure scenarios, verify policy adherence, and anticipate latency spikes to ensure continuity. Such multi-layered redundancy strategies exemplify the complexity and sophistication required in contemporary network engineering, transcending simplistic redundancy implementations.
Latency, Jitter, and Congestion Management
Latency and jitter present nuanced challenges in converged networks. Sophisticated congestion management strategies, including queue scheduling, traffic shaping, and dynamic bandwidth allocation, mitigate performance degradation. Professionals must interpret subtle variations in metrics, correlate them with network events, and implement precise interventions. Mastery of these elements enables seamless service delivery, particularly for latency-sensitive applications like voice and video, underscoring the integration of analytical skill with operational acumen.
Route Redistribution and Policy Nuances
Route redistribution between dissimilar protocols necessitates a comprehensive understanding of path attributes, metric translation, and policy implications. Misconfigurations can induce routing loops, suboptimal paths, or policy violations. Engineers must carefully map internal to external protocol attributes, applying filters, tag propagation, and route maps judiciously. This nuanced understanding of protocol interplay ensures predictable and stable routing behavior across complex network topologies, reflecting advanced operational expertise.
Real-Time Monitoring and Telemetry Integration
Telemetry transforms passive monitoring into proactive insight, capturing high-fidelity data streams from network devices. Real-time analytics allow immediate detection of anomalies, predictive maintenance, and automated remediation. Integrating telemetry with orchestration platforms enables dynamic adjustments to policy enforcement and traffic optimization. Mastery of telemetry tools requires both analytical sophistication and practical configuration skills, empowering engineers to maintain high-performance, resilient networks in ever-evolving environments.
Cognitive Load Management in Network Operations
Complex networking demands cognitive load management, balancing rapid decision-making with data interpretation and troubleshooting. Professionals must prioritize critical alerts, filter extraneous noise, and synthesize diverse information streams efficiently. This meta-cognitive capability enhances situational awareness, reduces error propagation, and improves response efficacy. Incorporating cognitive strategies into operational practice differentiates advanced engineers, reflecting a depth of expertise that combines technical skill with intellectual discipline.
Strategic Blueprint for Exam Mastery
Embarking upon the labyrinthine journey of the JN0-1103 exam necessitates more than mere rote memorization. It demands an orchestration of meticulous planning, cognitive dexterity, and temporal discipline. The edifice of success is erected upon a stratified blueprint, wherein study objectives are delineated with crystalline precision. Allocating chronological resources with perspicacity allows aspirants to reinforce frail knowledge while consolidating robust domains. Fragmented study sessions metamorphose into a cohesive narrative of expertise when structured strategically, transforming cognitive fatigue into sustained mental acuity.
Cognitive Conditioning Through Practice Simulations
Practice exams function as crucibles for intellectual fortitude, transmuting theoretical acumen into pragmatic proficiency. Engaging with scenario-laden questions cultivates anticipatory cognition, fostering an intuitive grasp of potential contingencies. Laboratory simulations, particularly those replicating network topologies, serve as cognitive scaffolds, cementing abstract concepts into tangible operations. Iterative exposure to complex problem sets enhances neuroplasticity, reinforcing memory pathways essential for high-stakes evaluations. The dialectic between success and error within simulated environments engenders resilience, enabling candidates to navigate unforeseen obstacles with composure.
Temporal Architecture and Study Chronometry
Temporal architecture, often underestimated, exerts a profound influence on examination outcomes. The judicious allocation of temporal blocks, aligned with circadian cognitive peaks, optimizes assimilation and retention. Interleaving topics and employing distributed practice engenders superior retention compared to monolithic study sessions. Chronometric awareness, coupled with micro-goal implementation, transforms preparation into a series of achievable milestones. Aspiring professionals harnessing this approach cultivate a rhythm of disciplined engagement, mitigating procrastinatory impulses and fostering incremental mastery.
Navigating Anxiety and Cognitive Equilibrium
Examination anxiety constitutes a formidable adversary, capable of obfuscating even well-honed knowledge. Techniques derived from mindfulness, biofeedback, and controlled breathing foster cognitive equilibrium, preventing stress-induced lapses. Metacognitive strategies, including active reflection and mental rehearsal, enhance self-efficacy and performance consistency. Systematic review interspersed with relaxation intervals fortifies resilience, ensuring the aspirant maintains optimal cognitive functionality during high-pressure evaluations. The interplay between psychological preparedness and intellectual proficiency is pivotal in achieving superior outcomes.
Curated Repository of Authoritative Resources
The edifice of knowledge must be scaffolded upon meticulously curated resources. Official Juniper study guides elucidate the foundational principles with unparalleled fidelity, providing a compass for the intricate terrain of the exam. Complementary resources, including detailed documentation, network emulators, and advanced video tutorials, broaden the spectrum of comprehension. Engaging with vibrant online communities affords exposure to diverse problem-solving paradigms, nurturing adaptive cognition. The confluence of these resources cultivates a holistic understanding, merging theoretical insight with practical application.
Engaging Experiential Learning Techniques
Hands-on exercises constitute the linchpin of durable learning. Configuring virtualized networks, troubleshooting simulated faults, and executing automation scripts transform abstract knowledge into operational fluency. Experiential learning fosters procedural memory, embedding critical protocols and configurations within cognitive frameworks. Reflection upon practical exercises enables meta-analysis, identifying latent misconceptions and reinforcing conceptual clarity. By integrating tactile engagement with analytical reasoning, aspirants attain a comprehensive grasp of the intricate functionalities required for examination success.
Active Recall and Spaced Repetition Paradigms
Active recall, the deliberate retrieval of knowledge, serves as a cognitive accelerant, strengthening memory traces and enhancing long-term retention. Paired with spaced repetition, this methodology exploits neurocognitive mechanisms to solidify conceptual understanding. Systematically revisiting material over incrementally expanding intervals mitigates forgetting curves, ensuring sustained accessibility of information. Employing mnemonic devices, schema mapping, and interleaved problem-solving further consolidates knowledge, preparing candidates to address both foundational and scenario-based queries with agility.
Collaborative Learning and Peer Synergy
The social dimension of preparation offers substantial cognitive dividends. Study collectives, discussion forums, and peer mentorship catalyze knowledge coalescence, exposing candidates to alternative analytical approaches. Peer-driven debate sharpens reasoning acuity, fostering the capacity to defend and critique solutions. Collaborative exercises simulate the dynamic problem-solving encountered in professional networking environments, instilling adaptive strategies. The synergistic interplay of collective cognition enhances both technical mastery and interpersonal competencies essential for career progression.
Integration of Automation and Emerging Technologies
Proficiency in contemporary networking extends beyond static configurations to encompass automation and emergent protocols. Engaging with scripting languages, orchestration tools, and programmable network interfaces equips candidates with the foresight to navigate evolving technological landscapes. Incorporating automation into study practice reinforces understanding of operational efficiencies, error mitigation, and system optimization. Awareness of cutting-edge trends, including zero-trust architectures, AI-assisted network management, and cloud-native paradigms, positions aspirants at the vanguard of professional relevance.
Diagnostic Analysis and Iterative Refinement
Continuous diagnostic assessment constitutes an indispensable pillar of preparation. Analyzing practice exam performance, identifying recurrent pitfalls, and implementing targeted remediation fosters iterative refinement. Error taxonomy, wherein mistakes are categorized by cognitive domain or procedural type, elucidates underlying conceptual gaps. This methodical self-analysis ensures that remediation is precise, effective, and aligned with exam exigencies. Over time, iterative refinement transforms latent weaknesses into consolidated competencies, culminating in heightened confidence and operational dexterity.
Cognitive Flexibility and Adaptive Problem-Solving
The capacity for cognitive flexibility underpins exceptional exam performance. Scenario-based questions frequently demand synthesis of disparate concepts, necessitating lateral thinking and adaptive problem-solving. Cultivating mental agility through cross-domain exercises, analogical reasoning, and heuristic exploration enables candidates to transcend rote application. This adaptability, honed through deliberate practice and reflective analysis, equips aspirants to navigate novel configurations, troubleshoot unexpected failures, and construct optimized solutions under temporal constraints.
Leveraging Network Emulators for Experiential Depth
Network emulators function as simulacra of real-world infrastructures, providing a risk-free environment to experiment with topologies, routing protocols, and security mechanisms. Engaging extensively with these platforms bridges the chasm between theoretical abstraction and operational execution. Emulators allow iterative testing, scenario replication, and failure analysis, fostering both procedural competence and strategic foresight. Regular interaction with virtualized networks enhances technical intuition, enabling aspirants to internalize complex processes and anticipate potential contingencies effectively.
Multimodal Learning and Cognitive Engagement
Diversifying the modality of information intake enhances cognitive retention and engagement. Visual schematics, interactive tutorials, auditory explanations, and kinesthetic exercises collectively reinforce comprehension. Multimodal learning exploits distinct neural pathways, ensuring robust encoding of intricate concepts. By varying instructional approaches, candidates mitigate monotony, sustain motivation, and strengthen integrative understanding. This holistic engagement cultivates both macro-level strategic thinking and micro-level technical precision, essential for excelling in nuanced examination scenarios.
Psychological Resilience and Performance Optimization
Sustained preparation for the JN0-1103 examination necessitates psychological resilience. Strategies encompassing goal visualization, cognitive restructuring, and positive self-dialogue reinforce mental stamina. Aspirants benefit from periodic detachment, restorative activities, and reflective journaling, which buffer against cognitive overload. Performance optimization emerges from the interplay of resilience, motivation, and strategic focus, allowing candidates to approach examinations with clarity, precision, and composure. Mastery of these psychological dimensions ensures that intellectual capabilities are fully actualized under pressure.
Continuous Professional Enrichment Beyond Certification
Attainment of certification represents a milestone rather than a terminus. The perpetually evolving landscape of networking demands continuous professional enrichment. Engaging with advanced Juniper certifications, contributing to open-source networking projects, and participating in technical forums cultivates lifelong learning. Exploring innovations in software-defined networking, cybersecurity frameworks, and network analytics sustains relevance and expertise. This commitment to perpetual growth transforms examination success into enduring professional competence, ensuring aspirants remain agile, informed, and competitive in a dynamic field.
Deep-Dive into Protocol Proficiency
Excellence in the JN0-1103 exam is inseparable from mastery of networking protocols. Each protocol embodies a complex choreography of signals, frames, and sequences that must be intuitively comprehended rather than superficially memorized. Dynamic routing protocols such as OSPF, BGP, and IS-IS require a granular understanding of metrics, convergence behaviors, and inter-domain interactions. Immersive practice in configuring and troubleshooting these protocols engenders an operational fluency that transcends rote application. Understanding the nuances of protocol hierarchies, adjacency formation, and route redistribution transforms candidates into architects of resilient network topologies capable of navigating multifarious scenarios.
Layered Security and Defensive Architectures
Security in modern networking is not a mere adjunct but a foundational pillar. Candidates must assimilate defensive paradigms encompassing firewalls, intrusion detection systems, and access control lists. Each security mechanism must be evaluated not only for its functionality but for its interplay with other network elements. Hands-on practice in implementing zone-based policies, threat containment strategies, and secure automation scripts cultivates both vigilance and procedural dexterity. The cognitive framework developed through repeated exposure to threat scenarios fosters anticipatory reasoning, allowing professionals to preempt vulnerabilities before they manifest in operational contexts.
Analytical Troubleshooting and Diagnostic Precision
Exemplary exam performance hinges upon analytical troubleshooting capabilities. Encountering anomalous network behaviors necessitates a disciplined approach that blends deductive reasoning with empirical validation. Systematic diagnosis involves layer-wise analysis, log interpretation, and simulation replication, creating a methodical pathway to resolution. Developing a mental repository of recurring fault patterns and their symptomatic manifestations enhances diagnostic efficiency. The iterative cycle of error identification, hypothesis testing, and solution validation reinforces a cognitive agility that proves invaluable in both examination and professional environments.
Advanced Automation Integration
The integration of automation into network operations has shifted paradigms from reactive maintenance to proactive orchestration. Proficiency in scripting languages such as Python, combined with automation frameworks like Ansible or Junos PyEZ, allows aspirants to transcend manual configurations. By programmatically designing repetitive tasks, validating network states, and orchestrating multi-device changes, candidates cultivate both efficiency and strategic foresight. Engaging in scenario-driven automation exercises also enhances the capacity to anticipate systemic bottlenecks and optimize workflow execution, a skill increasingly sought in modern network engineering roles.
Cognitive Layering Through Conceptual Mapping
Cognitive layering, the practice of interlinking discrete concepts into a cohesive schema, accelerates comprehension and recall. Conceptual mapping involves visualizing interdependencies among protocols, security measures, and network topologies. By constructing mental frameworks that mirror operational realities, aspirants can navigate complex scenarios with heightened precision. This technique reduces cognitive load during examinations, allowing candidates to allocate mental resources toward problem-solving rather than retrieval. Iterative refinement of these conceptual maps solidifies knowledge architecture and fosters adaptive expertise.
Scenario Simulation and Realistic Replication
Simulating real-world scenarios constitutes a cornerstone of advanced preparation. Network emulation platforms permit replication of high-density topologies, multi-vendor integrations, and failure contingencies. By recreating operational complexities, candidates confront the subtleties of protocol interactions, latency implications, and policy conflicts. The experience gained through such immersive exercises cultivates strategic foresight, enabling candidates to predict outcomes, optimize configurations, and devise contingency plans. This simulation-driven proficiency nurtures both cognitive resilience and tactical acumen, essential for both examination success and professional efficacy.
Knowledge Synthesis and Interdisciplinary Integration
Modern networking demands the synthesis of diverse knowledge streams. Understanding the interplay between routing protocols, security postures, cloud integrations, and automation frameworks allows candidates to craft solutions that are not only functional but optimized. Cross-disciplinary integration fosters analytical versatility, enabling professionals to address multifaceted challenges with holistic insight. Engaging with interdisciplinary problem sets, where network behavior intersects with security, policy, and automation, strengthens cognitive elasticity and reinforces the capacity to approach novel scenarios with confidence.
Temporal Resilience and Cognitive Endurance
The temporal demands of preparation extend beyond the calendar into cognitive endurance. Sustained focus, iterative review, and deliberate practice cultivate mental stamina essential for lengthy examination sessions. Strategic alternation between high-intensity problem-solving and restorative intervals mitigates cognitive fatigue, sustaining peak performance. Techniques such as microlearning bursts, adaptive challenge scaling, and periodic self-assessment ensure that aspirants maintain engagement without succumbing to burnout. This temporal resilience is a critical differentiator between competent and exceptional candidates.
Multilayered Resource Exploitation
Optimal preparation entails multilayered engagement with resources. Official guides provide foundational clarity, while emulators, community discussions, and peer collaborations provide experiential depth. Expanding resource utilization to include white papers, protocol RFCs, and advanced technical publications fosters critical evaluation skills. By juxtaposing authoritative documentation with practical experimentation, aspirants cultivate a nuanced understanding of theory and application. This comprehensive resource strategy encourages self-sufficiency, intellectual curiosity, and a proactive approach to learning.
Precision in Knowledge Retention Strategies
Knowledge retention strategies transcend memorization; they involve methodical encoding, reinforcement, and retrieval. Techniques such as elaborative interrogation, mnemonic scaffolding, and cognitive chunking enhance long-term accessibility of complex information. Employing spaced repetition in conjunction with scenario-based recall strengthens synaptic consolidation, ensuring that procedural and conceptual knowledge remains readily deployable. Precision in retention strategies allows candidates to respond to novel questions with adaptive accuracy, converting stored knowledge into actionable expertise.
Adaptive Metacognition and Self-Regulation
Adaptive metacognition, the awareness and modulation of one’s cognitive processes, underpins effective preparation. Candidates who actively monitor comprehension, adjust learning strategies, and recalibrate study intensity exhibit heightened efficiency. Self-regulatory practices such as progress tracking, reflective journaling, and cognitive benchmarking enable aspirants to identify latent weaknesses and optimize engagement. Cultivating metacognitive sensitivity transforms passive study into an iterative, goal-directed process, enhancing both preparation efficacy and examination readiness.
Network Topology Mastery and Spatial Cognition
Mastery of network topology extends beyond rote configuration to encompass spatial cognition—the ability to visualize interconnections, data flow, and potential failure points. Engaging in diagrammatic representation, interactive mapping, and virtual reconstruction of complex topologies solidifies spatial awareness. This cognitive skill allows candidates to anticipate protocol interactions, optimize routing paths, and design resilient architectures. Spatial proficiency is particularly valuable for scenario-based questions, where visualizing network behavior informs rapid, precise decision-making.
Experiential Reflection and Iterative Skill Refinement
Reflective practice amplifies the value of experiential learning. Post-exercise analysis, including error deconstruction, success attribution, and alternative strategy exploration, fosters a meta-level understanding of skill acquisition. Iterative refinement transforms initial attempts into increasingly sophisticated performance, bridging the gap between competence and mastery. By documenting reflections and tracking progressive improvement, aspirants cultivate a repository of actionable insights, enhancing both exam performance and professional adaptability.
Engaging in Knowledge Communities
Active participation in knowledge communities accelerates professional growth. Forums, study groups, and collaborative projects provide platforms for exchanging insights, testing hypotheses, and encountering diverse problem-solving approaches. Exposure to collective intelligence enhances cognitive flexibility and fosters innovative thinking. Engaging in discourse, contributing solutions, and mentoring peers strengthens understanding, reinforces retention, and cultivates leadership competencies. Knowledge communities thus serve as crucibles for both intellectual and professional maturation.
Proficiency in Monitoring and Diagnostic Toolsets
Effective exam preparation incorporates familiarity with monitoring and diagnostic toolsets. Real-time telemetry analysis, log inspection, and performance visualization equip candidates with practical skills to identify anomalies and optimize operations. Engaging with diagnostic tools simulates operational decision-making, bridging theoretical knowledge with actionable insight. Proficiency in toolsets enhances situational awareness, allowing aspirants to quickly diagnose, validate, and resolve complex network issues, a skill directly translatable to both examination and real-world applications.
Strategic Use of Microlearning Interventions
Microlearning, the deployment of targeted, concise instructional modules, enhances cognitive efficiency and engagement. Focusing on discrete concepts in brief, repetitive intervals reinforces retention while minimizing cognitive overload. Microlearning can encompass protocol nuances, configuration snippets, or security policy scenarios, enabling aspirants to maintain continuous incremental progress. Strategic integration of microlearning with broader study frameworks cultivates a layered understanding, optimizing both depth and breadth of knowledge.
Cognitive Anchoring Through Visualization
Visualization techniques serve as cognitive anchors, converting abstract information into tangible mental constructs. Flow diagrams, state machines, and network schematics enable candidates to internalize complex interactions and sequences. By repeatedly visualizing processes, configurations, and troubleshooting pathways, aspirants strengthen associative memory networks. This anchoring facilitates rapid recall under examination pressure, allowing for precise application of knowledge without reliance on transient cues or rote memorization.
Conclusion
Scenario-based learning immerses candidates in lifelike challenges, blending technical precision with strategic decision-making. Realistic scenarios, including multi-vendor integration, policy conflicts, and dynamic topology adjustments, compel aspirants to apply knowledge holistically. Repeated engagement with immersive scenarios cultivates anticipatory reasoning, error resilience, and decision agility. This method bridges the gap between theoretical comprehension and operational fluency, ensuring candidates possess both conceptual mastery and tactical competence.
Top Juniper Exams
- JN0-105 - Junos, Associate (JNCIA-Junos)
- JN0-351 - Enterprise Routing and Switching, Specialist (JNCIS-ENT)
- JN0-650 - Enterprise Routing and Switching, Professional (JNCIP-ENT)
- JN0-664 - Service Provider Routing and Switching, Professional (JNCIP-SP)
- JN0-253 - Mist AI, Associate (JNCIA-MistAI)
- JN0-232 - Security, Associate (JNCIA-SEC)
- JN0-106 - Junos, Associate (JNCIA-Junos)
- JN0-364 - Service Provider Routing and Switching, Specialist (JNCIS-SP)
- JN0-336 - Security, Specialist (JNCIS-SEC)
- JN0-452 - Mist AI Wireless, Specialist (JNCIS-MistAI-Wireless)
- JN0-281 - Data Center, Associate (JNCIA-DC)
- JN0-683 - Data Center, Professional (JNCIP-DC)
- JN0-460 - Mist AI Wired, Specialist (JNCIS-MistAI-Wired)
- JN0-481 - Data Center, Specialist (JNCIS-DC)
- JN0-637 - Security, Professional (JNCIP-SEC)
- JN0-231 - Security, Associate (JNCIA-SEC)
- JN0-251 - Mist AI, Associate (JNCIA-MistAI)
- JN0-363 - Service Provider Routing and Switching, Specialist (JNCIS-SP)
- JN0-214 - Cloud, Associate (JNCIA-Cloud)
- JN0-1103 - Design, Associate (JNCIA-Design)