Exam Code: 250-586
Exam Name: Endpoint Security Complete Implementation - Technical Specialist
Certification Provider: Symantec
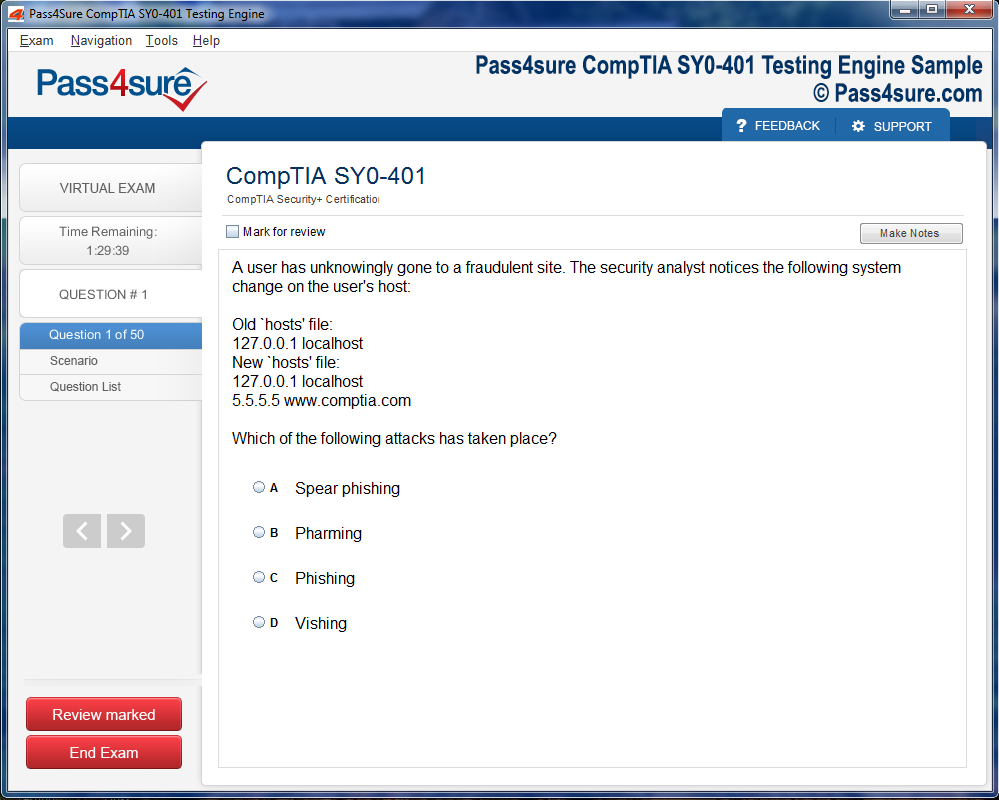
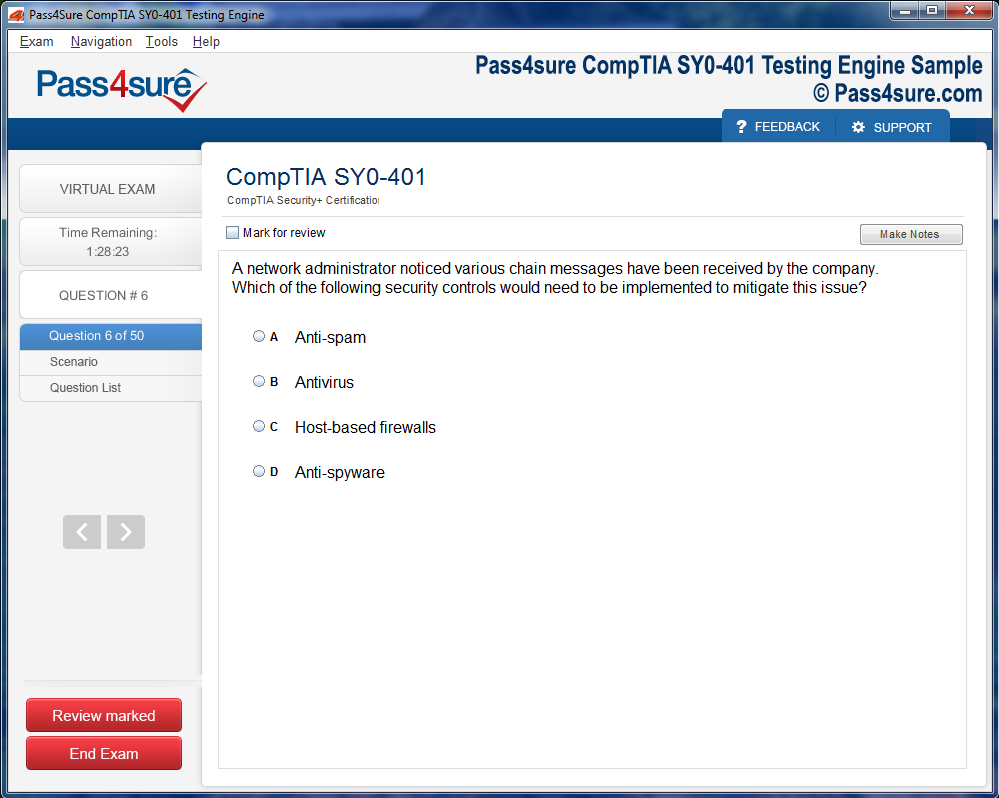
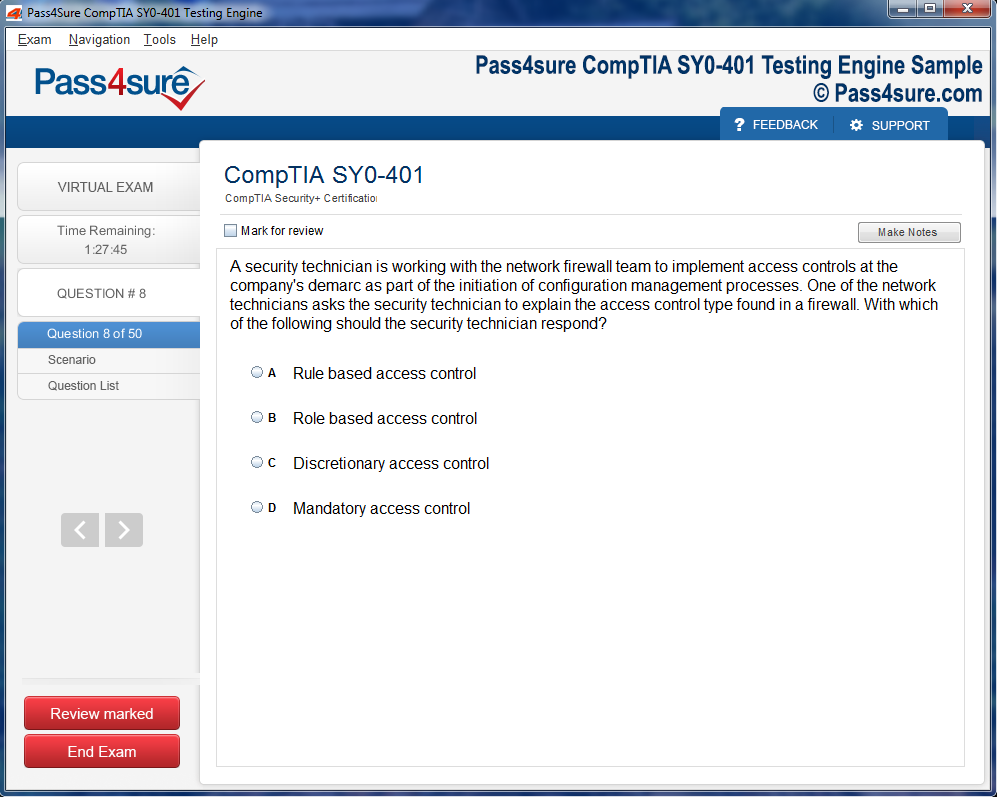
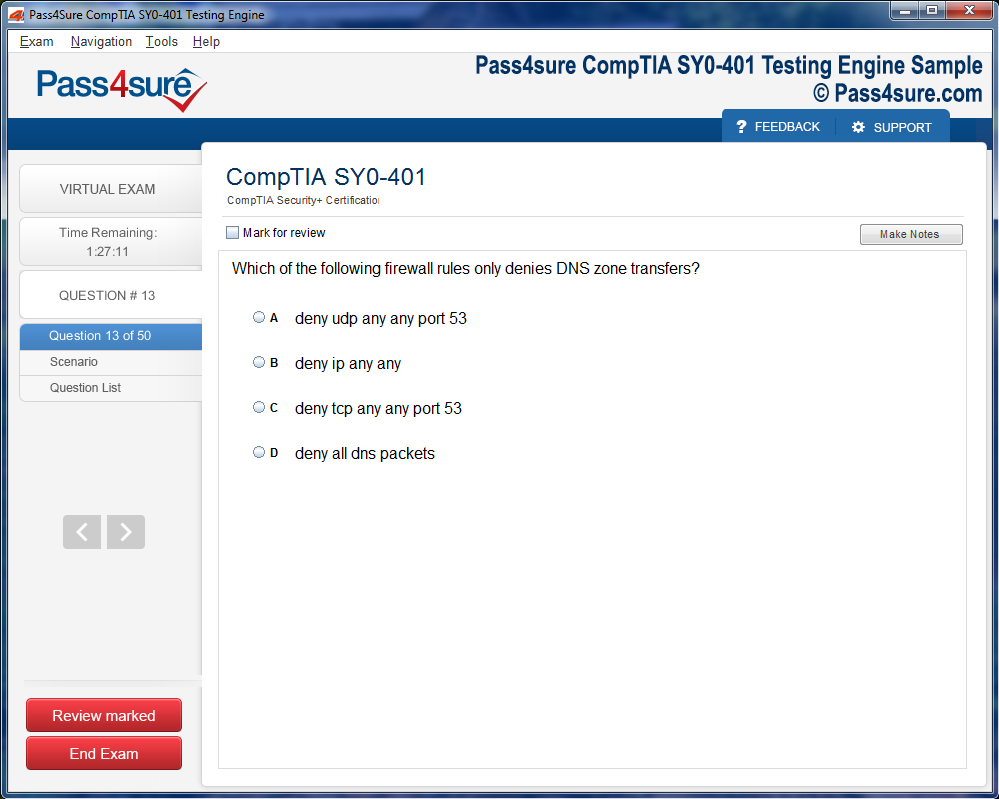
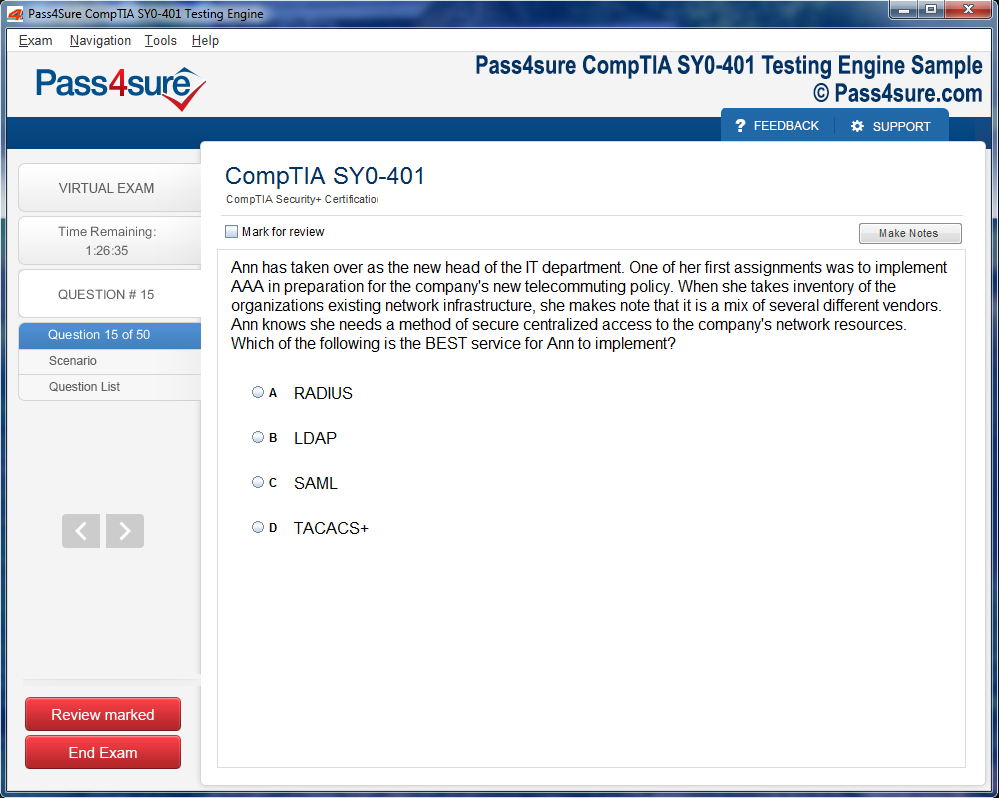
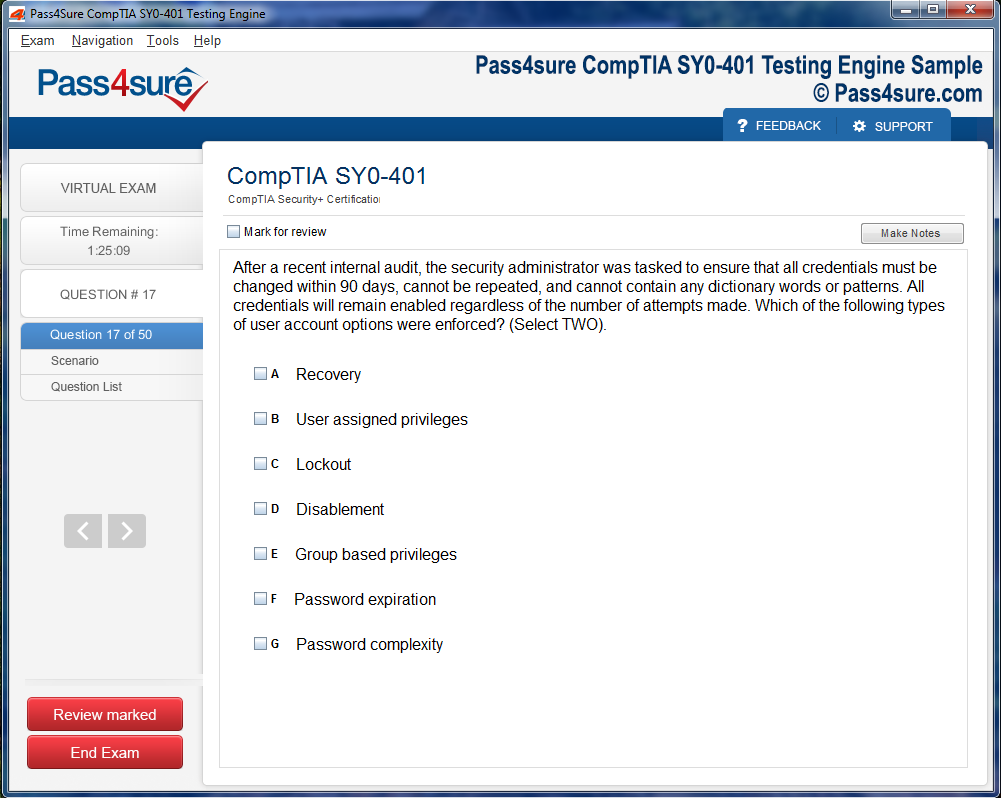
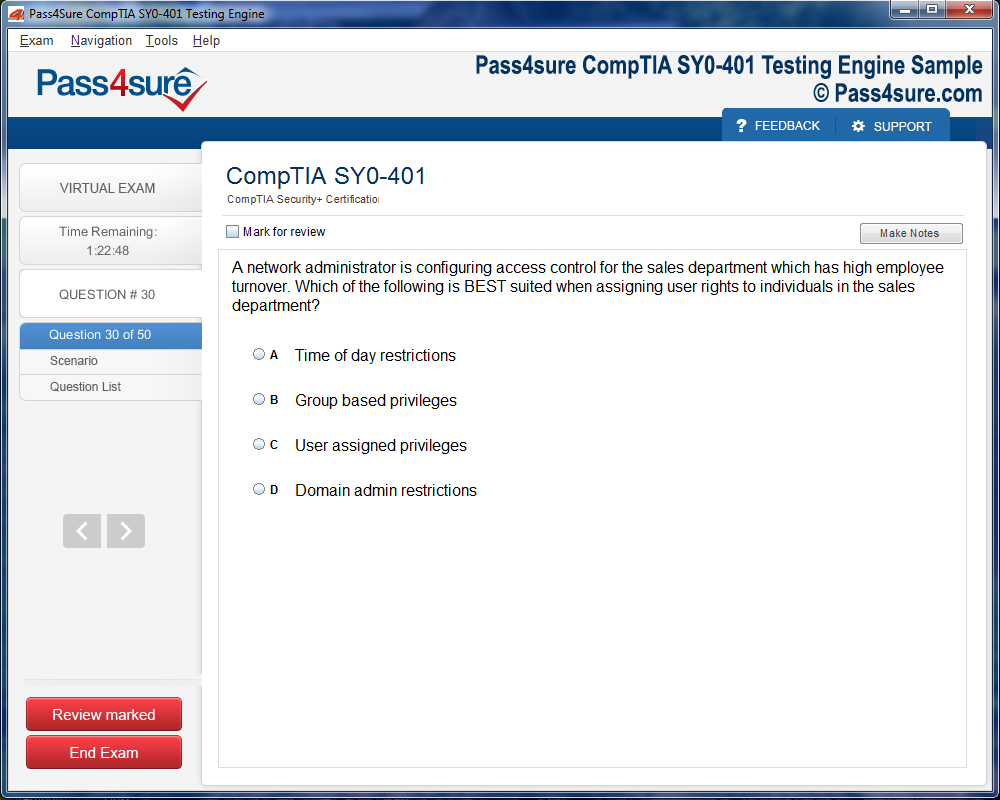
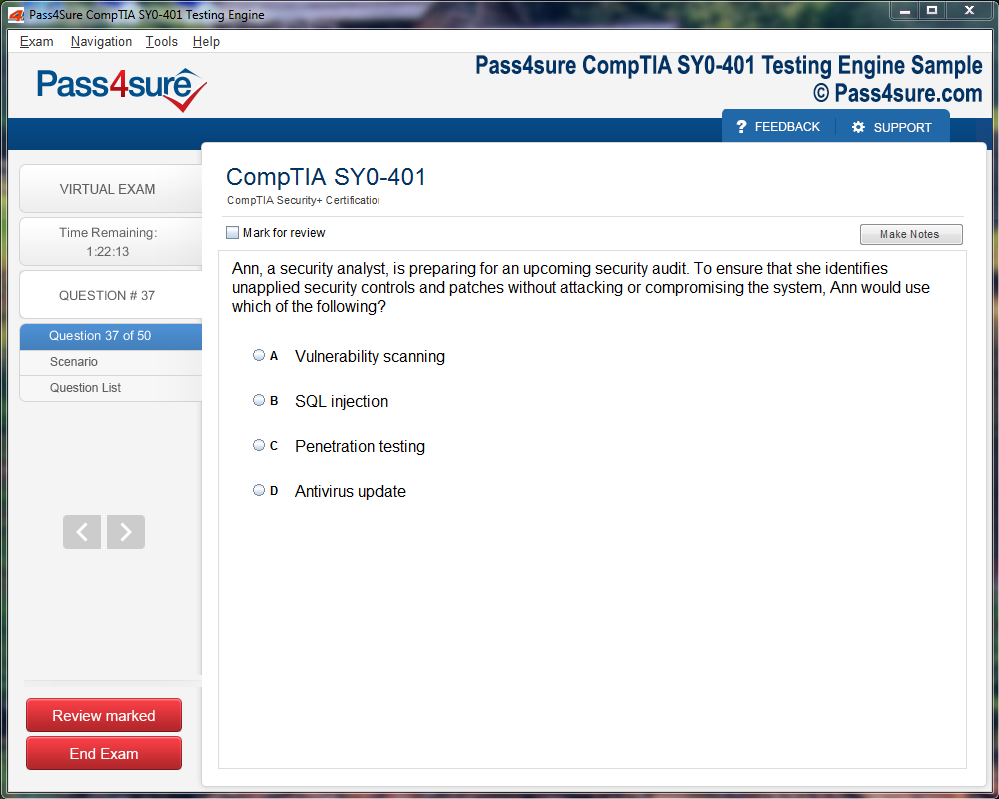
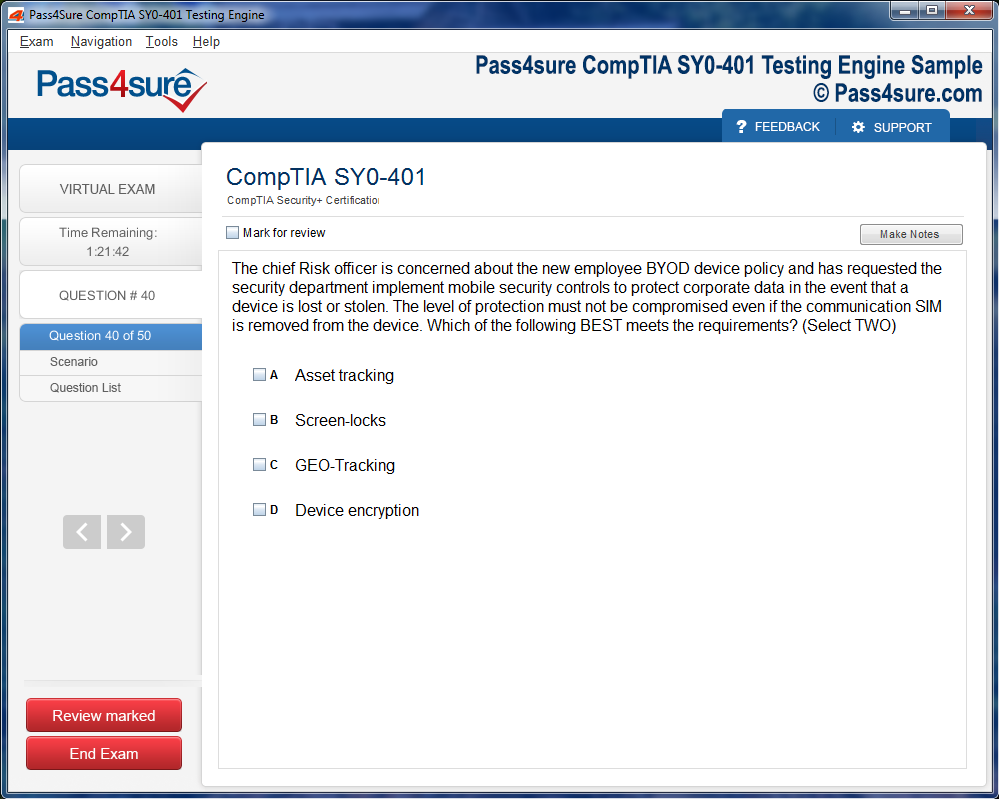
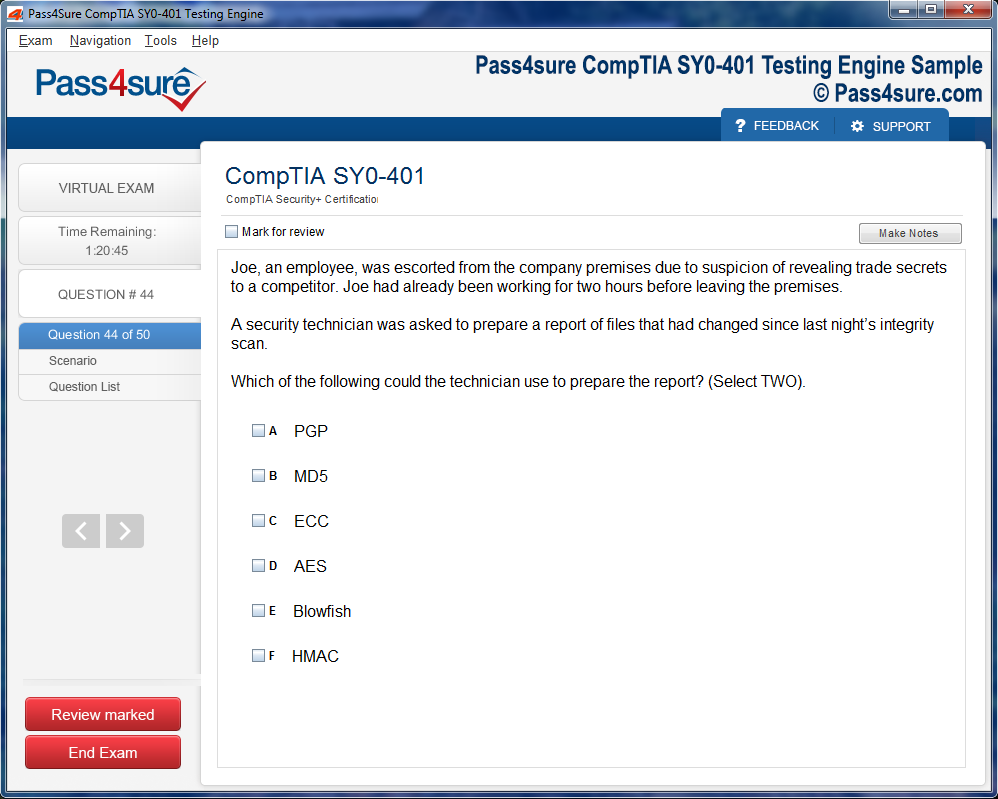
Product Screenshots
Frequently Asked Questions
How does your testing engine works?
Once download and installed on your PC, you can practise test questions, review your questions & answers using two different options 'practice exam' and 'virtual exam'. Virtual Exam - test yourself with exam questions with a time limit, as if you are taking exams in the Prometric or VUE testing centre. Practice exam - review exam questions one by one, see correct answers and explanations.
How can I get the products after purchase?
All products are available for download immediately from your Member's Area. Once you have made the payment, you will be transferred to Member's Area where you can login and download the products you have purchased to your computer.
How long can I use my product? Will it be valid forever?
Pass4sure products have a validity of 90 days from the date of purchase. This means that any updates to the products, including but not limited to new questions, or updates and changes by our editing team, will be automatically downloaded on to computer to make sure that you get latest exam prep materials during those 90 days.
Can I renew my product if when it's expired?
Yes, when the 90 days of your product validity are over, you have the option of renewing your expired products with a 30% discount. This can be done in your Member's Area.
Please note that you will not be able to use the product after it has expired if you don't renew it.
How often are the questions updated?
We always try to provide the latest pool of questions, Updates in the questions depend on the changes in actual pool of questions by different vendors. As soon as we know about the change in the exam question pool we try our best to update the products as fast as possible.
How many computers I can download Pass4sure software on?
You can download the Pass4sure products on the maximum number of 2 (two) computers or devices. If you need to use the software on more than two machines, you can purchase this option separately. Please email sales@pass4sure.com if you need to use more than 5 (five) computers.
What are the system requirements?
Minimum System Requirements:
- Windows XP or newer operating system
- Java Version 8 or newer
- 1+ GHz processor
- 1 GB Ram
- 50 MB available hard disk typically (products may vary)
What operating systems are supported by your Testing Engine software?
Our testing engine is supported by Windows. Andriod and IOS software is currently under development.
Ultimate Symantec 250-586 Study Guide
The Symantec 250-586 certification represents a symbol of professional mastery in cybersecurity resilience, endpoint protection, and advanced threat management. It demonstrates that a candidate has not only studied security principles but also internalized the methods that protect digital infrastructures from evolving cyber dangers. This certification revolves around building command over Symantec’s Endpoint Security and Data Center Security solutions, empowering professionals to protect digital assets across multiple environments.
The journey begins with grasping the architecture of Symantec’s security framework. This architecture integrates endpoint agents, centralized management consoles, and advanced analytics engines. These components function together to detect vulnerabilities, prevent data breaches, and respond to anomalies. A certified professional must therefore understand how these systems interact and how configurations influence overall protection performance. Each policy, each rule, and each threshold reflects a calculated decision balancing security and usability.
In the modern technological ecosystem, organizations rely on hybrid environments that merge on-premises systems with cloud-based architectures. The Symantec 250-586 exam emphasizes understanding this fusion. Candidates must navigate both traditional infrastructures and cloud-integrated security landscapes. The test evaluates one’s ability to harmonize these layers, ensuring that no endpoint, whether physical or virtual, becomes a weak link in the defense chain. It also measures comprehension of policy inheritance, central management synchronization, and real-time data correlation, all of which define a strong Symantec-protected environment.
Security is never static, and the Symantec ecosystem reflects that fluidity. Professionals are expected to remain vigilant, updating configurations, fine-tuning rules, and integrating intelligence feeds. The 250-586 certification thus goes beyond technical comprehension—it measures adaptability, analytical precision, and a mindset tuned to anticipating future threats before they manifest.
Building Technical Fluency Through Network and System Mastery
One of the strongest pillars supporting Symantec expertise is technical fluency in networking and operating system fundamentals. Before one can defend a system effectively, one must first understand its operational anatomy. The certification assumes that candidates possess a strong understanding of TCP/IP communication, subnetting, routing, and the inner mechanisms of data transmission. Network behavior shapes the way Symantec solutions detect and mitigate threats, as every anomaly often traces back to packet flow irregularities or unverified communications.
The defensive architecture of Symantec products integrates deeply with network security tools such as firewalls, intrusion prevention systems, and proxy configurations. Grasping how these elements interact ensures that configurations are neither redundant nor conflicting. For example, endpoint policies must complement network firewalls rather than duplicate their rules. When an administrator synchronizes these layers effectively, overall efficiency improves while the risk of performance bottlenecks decreases.
Operating systems serve as the battleground where Symantec’s endpoint defense mechanisms operate. Understanding both Windows and Linux architectures helps candidates manage agents, services, and policy enforcement modules effectively. Each platform handles processes, privileges, and registry structures differently, and these distinctions directly influence how security policies behave. Misaligned permissions or improperly configured services can create exploitable loopholes. Therefore, fluency in OS-level architecture ensures that Symantec’s defense mechanisms are fortified with precision.
System optimization is another key competency tested indirectly through the certification. Candidates must know how to balance system resources with protection levels. An overprotective configuration can degrade performance, while an under-protective setup can expose vulnerabilities. Recognizing these thresholds demonstrates not just technical knowledge but also operational wisdom. The 250-586 certification thus cultivates professionals who can protect organizations efficiently without compromising productivity.
Mastering Endpoint Security and Threat Mitigation
Endpoint protection lies at the heart of Symantec’s defense philosophy. The 250-586 certification places heavy emphasis on understanding how endpoints interact within enterprise infrastructures and how Symantec’s technologies safeguard them from infiltration. Each endpoint acts as both a resource and a potential entry point. Therefore, control mechanisms such as behavior-based analysis, signature detection, and application whitelisting become vital components of a comprehensive defense strategy.
Candidates are expected to understand the lifecycle of threats, from the initial intrusion attempt to the final remediation stage. Symantec’s Endpoint Protection and Data Center Security modules provide granular visibility into every stage of this lifecycle. Learning how to interpret threat logs, monitor behavioral anomalies, and correlate events across systems forms a major part of exam readiness. Analytical skill takes precedence over memorization; the test measures whether one can deduce the root cause of a threat and design preventive countermeasures efficiently.
Threat mitigation involves more than reactive defense. It demands foresight. Symantec tools offer advanced features such as real-time file reputation, sandboxing, and automated incident response. To configure these effectively, professionals must understand their logical foundations—how algorithms distinguish legitimate actions from malicious ones, and how risk scores evolve as patterns emerge. By developing this understanding, candidates move from mere configuration to intelligent management.
Data protection within endpoints also forms a crucial section of the certification’s focus. With information flowing between multiple devices and platforms, preventing unauthorized access becomes paramount. Symantec’s integrated encryption and data loss prevention components ensure that even if data leaves its original environment, it remains unusable to intruders. Professionals mastering this aspect can safeguard organizational integrity across distributed workforces and hybrid infrastructures.
Emphasizing Analytical Thinking and Scenario-Based Reasoning
A distinguishing aspect of the Symantec 250-586 certification lies in its analytical depth. Instead of testing only theoretical understanding, it challenges candidates to apply knowledge to real-world scenarios. The exam presents simulated environments where administrators must identify vulnerabilities, diagnose misconfigurations, and determine optimal responses. This structure encourages logical reasoning, problem-solving creativity, and methodical analysis—skills indispensable for cybersecurity professionals.
Analytical thinking in this context means examining every incident from multiple angles. For instance, when a security alert emerges, a professional must trace its cause through logs, network behavior, and endpoint activity. Rather than treating symptoms, they must isolate the origin of the anomaly. Symantec’s management consoles offer dashboards and event correlation tools that simplify this analysis, but true mastery comes from understanding the underlying data patterns.
Scenario-based reasoning also trains candidates to balance urgency with accuracy. In real cybersecurity incidents, speed matters, but reckless actions can worsen situations. The certification evaluates whether candidates can follow structured procedures—containing threats, validating evidence, and escalating when necessary. This process mirrors enterprise-grade incident response frameworks, making certified professionals reliable in crisis situations.
Another component of analytical skill involves recognizing false positives and distinguishing them from genuine threats. Overly strict configurations may trigger constant alerts, creating alert fatigue and reducing team efficiency. A certified Symantec specialist learns how to fine-tune detection thresholds to achieve precision without losing sensitivity. This balance between caution and clarity represents the maturity expected from those who earn the certification.
By internalizing these analytical methodologies, candidates prepare not only for the exam but also for the demands of real-world cybersecurity environments where every decision can shape an organization’s digital survival.
Developing Hands-On Competence Through Practice Environments
While theoretical understanding forms the backbone of preparation, practical experience gives it structure and strength. The Symantec 250-586 certification highly values candidates who immerse themselves in practical experimentation. Installing and configuring trial environments allows one to witness firsthand how Symantec’s systems behave under various conditions. Each experiment deepens comprehension, revealing nuances that textbooks cannot convey.
Building a virtual laboratory environment provides a risk-free arena for exploration. Within such spaces, candidates can create custom policies, simulate malware infections, and test endpoint responses. These exercises enhance confidence and sharpen diagnostic instincts. The tactile interaction of observing alerts, logs, and dashboards cements conceptual understanding through sensory reinforcement.
Hands-on learning also develops troubleshooting acumen. When systems malfunction or policies fail to apply, identifying the root cause becomes a puzzle that strengthens analytical resilience. Such experiences prepare candidates for the exam’s scenario-based elements, where problem-solving speed and accuracy are critical. Moreover, practical familiarity reduces anxiety during the test, as environments presented within the exam often resemble those encountered in practice setups.
Real-world simulation also fosters an understanding of integration challenges. Symantec solutions rarely operate in isolation; they coexist with directory services, firewalls, and third-party monitoring tools. Experimenting with such integrations teaches professionals how to synchronize security layers seamlessly. The more varied the practice environments, the broader the candidate’s adaptability during real-world deployments.
Consistency in practice nurtures muscle memory. Each configuration repeated strengthens neural associations between concept and action. Over time, responding to security incidents or adjusting policies becomes instinctive rather than forced. This natural fluency distinguishes professionals who merely pass exams from those who truly embody expertise.
The Role of Threat Intelligence and Continuous Adaptation
Cybersecurity is defined by evolution. Threats mutate, tools upgrade, and techniques transform. Symantec’s philosophy embraces this perpetual adaptation, and the 250-586 certification embeds this principle within its framework. Candidates must demonstrate awareness of threat intelligence—understanding how data from global security networks contributes to local defense strategies. This global perspective allows administrators to anticipate rather than merely react to attacks.
Threat intelligence involves collecting and interpreting vast datasets of malicious activities, identifying trends, and forecasting potential attack vectors. Symantec’s tools utilize this intelligence to update signatures, refine behavioral analytics, and improve detection precision. Professionals who comprehend this process can adjust configurations proactively, reducing response time when threats arise. Such foresight distinguishes a reactive defender from a strategic security architect.
Adaptation also extends to organizational needs. As infrastructures grow, merge, or diversify, policies must evolve accordingly. Certified professionals learn to review configurations periodically, ensuring that they align with both compliance standards and operational demands. This cyclical process of review and refinement reinforces security resilience across evolving digital landscapes.
Continuous learning is an integral virtue within Symantec’s certification ethos. Cyber defense does not conclude once an exam is passed; it requires constant renewal of awareness. New vulnerabilities appear daily, and defense tools evolve in response. Candidates who cultivate a habit of staying informed sustain their relevance in a fast-moving domain. Thus, the 250-586 certification becomes more than a credential—it becomes a lifestyle of vigilance and progression.
The integration of automation and artificial intelligence in modern cybersecurity further expands this adaptive horizon. Symantec’s platforms employ machine learning models to detect subtle deviations within massive datasets. Understanding how these algorithms function enables professionals to interpret alerts accurately and adjust system learning parameters when necessary. The ability to balance human judgment with machine efficiency is now a defining attribute of advanced cybersecurity practitioners.
Strategic Preparation and Mindset for Success
Preparing for the Symantec 250-586 certification requires more than rote study; it demands a strategic mindset oriented toward comprehension and application. Candidates must craft study plans that blend theoretical review, practice sessions, and periodic assessment. Dividing study hours into focused segments allows for steady progress without fatigue. Emphasizing concept mastery over memorization enhances long-term retention, which proves crucial when tackling scenario-driven exam segments.
Resource curation is equally important. Official documentation, white papers, and configuration guides provide the foundational material, while hands-on experimentation translates that theory into practice. Candidates should simulate realistic conditions, testing how policy changes impact systems under load. Observing these cause-and-effect relationships imprints knowledge deeply, fostering intuitive decision-making skills.
Another essential aspect is time management during both preparation and examination. Practicing under timed conditions helps simulate exam pressure, training the mind to remain composed and efficient. A calm, methodical approach yields better results than rushed decision-making. During study sessions, revisiting complex topics regularly prevents memory erosion, ensuring that key concepts remain sharp.
Psychological readiness is an often-overlooked factor. Confidence grows through repetition and familiarity. The more time spent exploring Symantec environments, the less intimidating they become. Maintaining a positive mindset, balanced lifestyle, and consistent focus cultivates mental endurance—an asset during long, demanding assessments.
Finally, adopting a growth mindset transforms the learning journey into a fulfilling experience. Viewing each challenge as an opportunity to refine skill fosters perseverance. The 250-586 certification represents not merely an exam but a transformation into a professional capable of safeguarding complex infrastructures. Through disciplined effort, reflective practice, and an unyielding drive for excellence, candidates ascend beyond certification into true cybersecurity leadership.
Deep Dive into Symantec Endpoint Security
Symantec Endpoint Security represents the heart of intelligent digital defense systems in contemporary cyber landscapes. It operates as a robust fortress built with precision, agility, and adaptability to meet the constantly shifting dynamics of cybersecurity threats. Its design transcends traditional antivirus mechanisms by integrating machine learning, behavior analytics, and adaptive policy control into one cohesive platform. To truly understand its depth, one must explore how its framework operates at both the technical and conceptual levels, shaping the modern philosophy of endpoint defense. In preparation for the Symantec 250-586 certification, this deep understanding becomes not only an academic requirement but also a practical necessity for cybersecurity mastery.
Symantec Endpoint Security merges several protective mechanisms that function in unison rather than isolation. It connects endpoints, management consoles, and cloud intelligence in a loop of continuous learning and threat prevention. Its real-time communication channels between clients and servers ensure that no endpoint operates with outdated intelligence. The architecture allows seamless updates, synchronization of security policies, and the integration of behavioral insights collected across millions of systems worldwide. This interplay between local protection and global awareness transforms Symantec Endpoint Security into an intelligent, self-evolving defense ecosystem.
Architecture and Modular Framework
The architecture of Symantec Endpoint Security is an intricate network of coordinated modules, each crafted to perform a specific defensive function while maintaining unity with others. At the forefront lies the endpoint client, installed directly on workstations, laptops, and servers. This client continuously communicates with a centralized management console, whether hosted on-premises or within Symantec’s secure cloud environment. This constant dialogue forms the foundation of a proactive defense model. Through it, endpoints receive policy updates, definition files, and configuration changes instantly, ensuring that each device remains aligned with the organization’s current security stance.
Each component within the architecture performs a unique role. The antivirus module scans files, memory, and network traffic to detect malicious signatures. The behavioral analysis engine monitors activities, observing anomalies that traditional signature-based detection might overlook. The device control module restricts access to unauthorized external drives and peripherals, minimizing data exfiltration risks. Meanwhile, the network protection module inspects inbound and outbound communication, detecting intrusion attempts before they can escalate into breaches. These collective modules operate like interdependent organs within a living organism—each vital, each responsive, each continuously improving through shared intelligence.
Understanding the architecture also requires recognizing the power of policy management and inheritance. Policies define the behavioral framework of each endpoint, dictating how it responds to various security events. Administrators can configure global policies to apply universally, or they can define specialized policies for distinct departments or environments. In complex infrastructures, overlapping policies may lead to conflicts, and this is where precedence rules determine which policy takes effect. Mastery over these mechanisms is essential, especially for certification candidates who must interpret these nuances under exam conditions that replicate real-world administrative challenges.
Policy Configuration and Management Strategies
Policy configuration stands as the central pillar of endpoint governance. Through the policy management console, administrators define how the system should behave under different scenarios—when to scan files, how to quarantine threats, when to update definitions, and which devices can access the network. These decisions form the behavioral DNA of the security ecosystem. When structured with foresight, policies transform Symantec Endpoint Security from a reactive system into an anticipatory shield capable of preempting attacks.
The policy creation process involves a blend of technical precision and strategic awareness. Administrators must consider the unique risk profile of each environment, balancing stringent protection with system performance. For instance, a research and development department handling sensitive intellectual property may require more aggressive scanning and tighter firewall rules than a marketing department focused primarily on data access and communication. Understanding these distinctions ensures that protection remains contextually relevant, not universally rigid.
Another key concept within policy management is reputation-based decision-making. Symantec’s Global Intelligence Network accumulates vast datasets from millions of endpoints globally, analyzing files, URLs, and applications to determine their reputational credibility. This intelligence forms the basis for automated decision-making—where files with poor reputations are quarantined instantly, while trusted ones pass unobstructed. In the certification context, candidates must be able to interpret these reputation scores accurately and adjust thresholds where necessary without undermining the integrity of the security posture. Learning when and how to create exceptions while maintaining compliance is an art that combines technical skill with sound judgment.
Deployment and Integration in Complex Environments
Deploying Symantec Endpoint Security across diverse infrastructures demands not only technical execution but also strategic foresight. In smaller environments, agents can be manually installed on endpoints, but in large enterprises, automation becomes indispensable. Integration with directory services like Active Directory allows administrators to distribute client software seamlessly, ensuring that every device joining the network is instantly brought under the protective umbrella of security policies. This synchronization eliminates the vulnerabilities caused by unmanaged devices and rogue endpoints.
Effective deployment also requires planning for scalability. As organizations grow, the number of endpoints multiplies, often spanning across physical and virtual environments, remote offices, and cloud-based assets. Symantec’s flexible deployment models enable administrators to maintain centralized control while adapting to the heterogeneous nature of enterprise IT. The ability to manage hybrid environments—where some endpoints are on-premises and others reside in cloud ecosystems—demonstrates the true power of a unified security approach.
Communication between clients and servers represents another critical aspect of deployment. If endpoints lose connectivity to the management console, they risk operating with outdated security configurations. Therefore, understanding the communication protocols, port requirements, and certificate validation processes becomes essential. Troubleshooting these elements requires both analytical thinking and hands-on experience. Candidates aiming for excellence in the Symantec 250-586 certification must demonstrate not only conceptual understanding but also the ability to identify and resolve these operational challenges efficiently.
Update Mechanisms and Continuous Protection
In cybersecurity, time defines security. The interval between an emerging threat and its neutralization determines the vulnerability window of an organization. Symantec Endpoint Security addresses this challenge through its sophisticated update mechanisms, which operate both automatically and manually depending on configuration. The system relies on live update servers to distribute virus definitions, intrusion prevention signatures, and product patches across all connected devices. These updates fortify the defense layer, ensuring that even newly emerging threats are detected before they manifest as incidents.
Administrators can configure live updates to occur at scheduled intervals or on-demand, depending on bandwidth availability and organizational policy. In high-security environments, offline updates can be deployed using internal distribution points, allowing endpoints without direct internet access to receive critical patches. This flexibility ensures that no endpoint, regardless of its location or connectivity, remains exposed to known vulnerabilities. Understanding how to manage, schedule, and verify these updates is vital for maintaining continuous protection and achieving high availability.
Equally important is the capacity to monitor update success and failure logs. Failed updates may result from connectivity issues, corrupted files, or misconfigured policies. Through detailed logging and diagnostic tools, administrators can identify the root causes of these failures and implement corrective measures swiftly. This proactive monitoring reflects the operational discipline required to manage enterprise-scale security solutions effectively.
Performance Optimization and Resource Management
While comprehensive protection remains the foremost priority, performance optimization ensures that security does not impede productivity. Excessive scanning or redundant policy enforcement can slow down systems, leading to user frustration and potential circumvention of security controls. Achieving equilibrium between protection and performance defines the excellence of a well-tuned Symantec Endpoint Security deployment.
Optimization begins with understanding workload distribution. Administrators can schedule full system scans during low-usage hours to minimize disruption while maintaining security vigilance. Exclusions can be defined for trusted applications, directories, or system files that are known to be safe. Such configurations reduce redundant scanning operations without compromising security integrity. However, exclusions must be handled with precision, as careless exceptions can introduce vulnerabilities into the system.
Symantec Endpoint Security provides performance metrics and analysis dashboards that help identify bottlenecks and optimize system efficiency. Administrators can use these insights to adjust configurations, modify policies, and reallocate system resources effectively. The goal is to maintain a dynamic equilibrium where security operates invisibly, allowing users to perform their tasks seamlessly while the protective mechanisms function silently in the background. Understanding these optimization strategies and their implications remains a recurring theme in the 250-586 exam, where candidates must demonstrate the ability to sustain protection without performance degradation.
Cloud Integration and Hybrid Protection Frameworks
The evolution of enterprise IT environments into hybrid and cloud-driven ecosystems demands that endpoint security extend its reach beyond physical networks. Symantec Endpoint Security rises to this challenge by offering integrated protection across public cloud platforms such as Microsoft Azure, Amazon Web Services, and Google Cloud. This cross-environment protection ensures consistent enforcement of security policies, even when workloads transition between on-premises infrastructure and virtualized cloud environments.
In cloud contexts, security responsibilities are often shared between service providers and clients. Symantec’s integration helps bridge this shared responsibility by delivering unified visibility and control. Administrators can monitor workloads, detect anomalies, and apply real-time threat intelligence across all environments from a single management console. This unified perspective reduces blind spots, enabling faster detection and response to emerging threats.
A critical component of modern cloud protection is container and microservices security. As organizations adopt DevOps and containerization frameworks, security must integrate seamlessly into the development pipeline. Symantec provides mechanisms for scanning container images, monitoring runtime behavior, and detecting misconfigurations that could lead to exploitation. Understanding how these cloud-native defenses operate enhances both theoretical knowledge and practical expertise for certification candidates.
Zero-trust security principles further enrich the cloud integration approach. Rather than assuming trust based on network location, every access request is validated continuously. Symantec’s implementation of zero-trust frameworks ensures that users, devices, and applications are authenticated and authorized before any interaction occurs. This adaptive verification mechanism minimizes lateral movement risks and strengthens defense across distributed infrastructures. In mastering this approach, administrators develop a forward-thinking mindset aligned with the future of cybersecurity.
Endpoint Detection, Response, and Threat Analytics
Beyond prevention lies the domain of detection and response—where security transforms from static defense to active resilience. Symantec’s Endpoint Detection and Response (EDR) capabilities enable administrators to trace the full lifecycle of an attack, from the initial compromise to lateral propagation across systems. This visibility provides context, allowing investigators to reconstruct attack sequences, identify root causes, and implement targeted remediation.
The EDR module captures events, correlates data, and presents insights through visual analytics that simplify complex threat patterns. Administrators can view behavioral anomalies, suspicious process chains, and communication flows that reveal underlying compromise attempts. This depth of understanding transforms incident management from reactionary containment into intelligent foresight. Learning how to interpret these data points, prioritize alerts, and automate response workflows is vital for demonstrating advanced competency in the 250-586 certification.
Automation plays a defining role in modern response frameworks. By leveraging pre-configured playbooks, Symantec allows repetitive or time-sensitive responses to occur automatically—isolating infected endpoints, terminating malicious processes, or initiating forensic collection. This automation reduces response time and minimizes the impact of potential breaches. For candidates preparing for certification, understanding how to balance automation with human oversight is key, as the goal is not merely speed but precision and accountability.
Compliance, Reporting, and Audit Readiness
Every enterprise operates within a landscape of regulatory expectations and compliance mandates. Symantec Endpoint Security aids organizations in aligning with international standards such as ISO 27001, GDPR, and NIST frameworks through its comprehensive reporting and auditing capabilities. Administrators can generate detailed compliance reports that document security posture, policy adherence, and event history with clarity and precision. These reports serve as both operational insights and evidence for auditors verifying the effectiveness of implemented controls.
Symantec’s reporting modules also enable customization, allowing administrators to focus on specific metrics such as malware detection rates, patch compliance, or endpoint health status. This flexibility empowers organizations to adapt reporting outputs to their unique governance models. For certification aspirants, familiarity with report generation, interpretation, and policy mapping demonstrates practical understanding of how endpoint security supports organizational accountability.
Beyond compliance, these reports enhance transparency and strategic planning. By analyzing historical trends and recurring vulnerabilities, administrators can refine security strategies and anticipate emerging risks. This feedback loop between reporting and continuous improvement embodies the proactive ethos that defines advanced security governance. Candidates who internalize this mindset not only prepare effectively for the exam but also cultivate the analytical foresight essential for real-world cybersecurity leadership.
Troubleshooting and Analytical Mastery
Even the most robust systems encounter challenges, and troubleshooting remains the art that separates competent administrators from exceptional ones. Within Symantec Endpoint Security, issues can emerge from misconfigurations, failed updates, agent communication breakdowns, or compatibility conflicts. Understanding how to diagnose and resolve these problems efficiently forms a core competency assessed in the 250-586 exam.
Troubleshooting begins with logs—the silent witnesses of every system action. By analyzing log files, administrators can trace the sequence of events leading to an error. Whether it involves failed policy synchronization, corrupt definition files, or blocked network communication, logs provide the breadcrumbs leading to the root cause. Familiarity with interpreting diagnostic outputs and applying corrective measures ensures that operations remain uninterrupted and protection remains intact.
Another aspect of troubleshooting involves validation. Before applying major changes or updates, administrators must test configurations in controlled environments to prevent unintended consequences. This disciplined approach reflects professional maturity and risk awareness. Understanding rollback mechanisms, backup policies, and recovery strategies ensures continuity even during unforeseen failures. These practices reflect the operational wisdom expected of professionals managing enterprise-scale endpoint security infrastructures.
Through practice, experience, and disciplined analysis, candidates develop not only technical skill but also the intuitive confidence required to manage Symantec Endpoint Security effectively. Troubleshooting becomes not merely a corrective task but an exercise in pattern recognition, systemic thinking, and proactive prevention—a mindset that embodies the essence of mastery.
Data as the Cornerstone of Digital Integrity
Data forms the unseen backbone of modern organizations, silently sustaining operations, decision-making, and innovation. In an era where information travels at the velocity of light, its protection becomes the cornerstone of trust and resilience. Symantec Data Loss Prevention, often abbreviated as DLP, is crafted precisely to uphold this integrity, transforming data security into an orchestrated discipline. It gives organizations not merely the means to protect data but also the clarity to understand where it resides, how it moves, and how it can be governed with precision. In the context of professional mastery and certification, learning DLP principles is about more than memorizing configurations—it is about perceiving data as a living entity that demands constant vigilance and responsible stewardship.
Symantec’s DLP architecture embodies visibility, discovery, and control. Visibility enables administrators to trace sensitive data whether it rests on endpoints, moves through networks, or lives in cloud repositories. Discovery allows the identification of hidden, forgotten, or unstructured information stored in neglected corners of servers or archives. Control enforces boundaries that determine how and when data can travel beyond trusted domains. This trifecta forms the essence of digital guardianship, making it possible to monitor the unseen movements of critical information and mitigate exposure risks that could devastate reputations and operations alike.
DLP’s foundational technologies such as fingerprinting, regular expression analysis, and exact data matching allow precise recognition of sensitive content. They operate as the digital senses of an organization, examining content patterns, contextual metadata, and structured identifiers to isolate materials that demand protection. Through these technologies, administrators achieve not just reactive defense but proactive governance—ensuring that sensitive data never drifts beyond its permissible horizon.
Policy Design and Structural Safeguards
Every effective DLP system begins with meticulously constructed policies. These policies act as the written constitution of an organization’s information security framework, defining what constitutes sensitivity, what boundaries exist for data movement, and what corrective actions are mandated in case of policy violation. Each rule within this structure carries a specific purpose, creating a lattice of logical controls that sustain the balance between protection and productivity.
Within the Symantec environment, detection rules represent the analytical dimension, identifying events that breach the defined data boundaries. Response rules embody the corrective mechanism that determines the subsequent action—whether to quarantine a file, encrypt communication, block transmission, or simply alert an administrator. Mastery of policy layering ensures that protection operates dynamically, adapting to context and minimizing unnecessary restrictions.
A candidate preparing for the certification must internalize the subtle art of crafting detection templates that align with organizational realities. For example, the pattern that identifies credit card data should not hinder legitimate business workflows. Fine-tuning keyword lists, creating regular expressions that avoid overlaps, and validating rule logic are intellectual exercises that shape an efficient, intelligent DLP ecosystem.
This architectural diligence also extends to maintaining hierarchical policy structures. Policies may differ based on department, data type, or jurisdictional compliance requirements. Crafting a unified yet flexible framework ensures that policies remain coherent and enforceable across global and local contexts simultaneously.
Deployment Models and Operational Interplay
Understanding DLP’s deployment architecture is akin to understanding the circulatory system of a living organism. The system functions through three primary components: detection servers, endpoint agents, and the central management console. Each serves a distinct yet interconnected role in ensuring continuous protection.
Detection servers scan network traffic and stored content, interpreting policy logic to identify potential data leaks. Endpoint agents reside on user devices, monitoring local actions such as file transfers, email attachments, and clipboard activity. The management console orchestrates this ecosystem, providing the central hub where incidents are logged, policies are deployed, and reports are visualized.
To excel in configuring such an environment, one must grasp communication channels, authentication mechanisms, and network segmentation principles that enable seamless cooperation among these components. For instance, secure socket connections between agents and servers ensure confidentiality during communication, while bandwidth optimization prevents latency during policy updates.
Moreover, interpreting DLP incident logs becomes an analytical skill that transcends technical familiarity. Each incident report narrates a story—how data moved, who accessed it, what triggered the alert, and whether the action was intentional or accidental. The ability to read these narratives cultivates an investigative mindset essential for both examination success and real-world data protection management.
Discovery and Classification of Data Repositories
An organization’s data footprint often sprawls beyond what is visible. Files accumulate in forgotten directories, old archives remain unencrypted, and sensitive information resides unnoticed in temporary folders. Symantec DLP’s discovery feature is designed to reveal these hidden repositories, scanning through structured databases and unstructured file systems with surgical precision.
Content discovery involves connecting to target repositories—be it on-premises servers, external storage units, or cloud-based platforms—and executing scanning jobs that identify files matching predefined sensitivity criteria. The process demands optimization to balance thoroughness with performance. Overly broad scans can strain system resources, while overly narrow filters may overlook critical files.
A well-calibrated discovery scan relies on efficient dictionaries, contextual rules, and prioritization of data volumes that bear the highest risk. Administrators must also be able to minimize false positives, as excessive alerts dilute the significance of genuine threats. Adjusting detection thresholds and refining pattern sensitivity builds credibility in incident management, ensuring that alerts are both accurate and actionable.
Through such discovery exercises, organizations gain not just compliance assurance but also situational awareness—knowing where sensitive data resides and who has access to it. This knowledge enables strategic decisions regarding storage optimization, data retention policies, and access control frameworks.
Cloud Integration and the Modern Data Frontier
As enterprises transition toward hybrid and multi-cloud architectures, DLP extends its protective reach beyond traditional networks. Symantec DLP integrates seamlessly with leading cloud productivity environments through API-based mechanisms that monitor and control data within hosted applications and storage systems.
This integration ensures that policies established on-premises remain equally enforceable in the cloud. Whether users collaborate on documents, share files, or synchronize data across distributed teams, DLP maintains persistent oversight. It intercepts unauthorized sharing, flags anomalous behavior, and ensures encryption when data traverses public networks.
Cloud integration introduces additional complexities such as shared responsibility models, cross-tenant data exposure, and regulatory compliance variations. To manage these challenges effectively, administrators must align cloud security policies with enterprise governance principles. Granular control over access permissions, identity federation, and encryption standards becomes vital.
Candidates studying for the certification must understand that cloud integration is not a separate discipline but an extension of unified data governance. It reflects the convergence of security and productivity, enabling organizations to operate freely yet securely in a boundaryless digital environment.
Incident Remediation and Workflow Coordination
The lifecycle of a DLP incident begins with detection but culminates in remediation. This process represents the operational heartbeat of data protection, transforming abstract alerts into concrete corrective actions. In Symantec DLP, incident workflows can be configured to follow a structured path of escalation, review, and resolution.
Once a policy violation is detected, incidents are categorized by severity and routed to appropriate personnel. For example, a minor policy deviation may simply generate an automated user notification, whereas a critical breach might trigger a multi-tiered response involving investigation, containment, and forensic analysis.
Understanding the hierarchy of remediation ensures consistency and accountability. Each step in the workflow—from triage to closure—must be documented for compliance audits. Administrators must be adept at configuring notification templates, defining escalation chains, and integrating DLP alerts with ticketing or SIEM systems to achieve unified security orchestration.
Remediation also requires human judgment. Technical controls can identify and restrict violations, but it is the administrator’s discretion that determines context—whether the data movement was a legitimate business necessity or a deliberate attempt at exfiltration. This blend of automation and discernment ensures both efficiency and fairness in enforcement.
Governance, Compliance, and Ethical Stewardship
Data protection extends beyond technology—it embodies governance, accountability, and ethical responsibility. Symantec DLP plays a critical role in aligning operational security with global compliance frameworks such as GDPR, HIPAA, and PCI-DSS. By enforcing data classification, access control, and audit trails, DLP assists organizations in demonstrating conformity to regulatory expectations.
However, compliance is not merely a checkbox exercise. It represents an ongoing commitment to respecting data privacy, ensuring transparency in handling personal and confidential information. Every policy rule, audit report, and remediation action contributes to building this ethical ecosystem.
Documentation is a silent yet powerful pillar of governance. Incident records, configuration logs, and audit histories form an evidence trail that regulators and auditors rely upon to assess the organization’s diligence. Candidates must develop a habit of maintaining accurate and timely records, as it reflects both operational discipline and strategic foresight.
Furthermore, governance involves periodic policy reviews and adaptability to evolving threats. As data patterns change, new file types emerge, and regulations evolve, the DLP framework must remain agile. The ability to revise policies, update detection dictionaries, and train personnel ensures sustained resilience.
Ethical stewardship, meanwhile, underlines the human aspect of DLP management. Protecting data is ultimately about protecting people—their identities, their trust, and their dignity. A mature professional understands that every alert, every encrypted file, and every policy serves a greater moral purpose: preserving the sanctity of information that sustains human progress.
Integrated Intelligence and the Unified Security Horizon
Symantec DLP’s integration with broader endpoint and network security ecosystems creates a unified intelligence model that transcends isolated controls. Through centralized dashboards, administrators can correlate data movement with endpoint activities, uncovering hidden threat patterns such as insider misuse or credential compromise.
This unified approach allows organizations to move from reactive defense to predictive insight. When DLP alerts merge with behavioral analytics, machine learning algorithms, and endpoint telemetry, the result is a holistic understanding of digital behavior. Administrators can foresee potential breaches before they occur, adjusting policies and workflows accordingly.
The certification journey emphasizes this integrated thinking. Understanding DLP in isolation is no longer sufficient; one must appreciate its place within the broader architecture of cybersecurity. This interconnected vision enables professionals to build ecosystems where data, identity, and infrastructure converge under a single governance framework.
In mastering Symantec DLP, professionals gain not only technical dexterity but also strategic perception. They learn to navigate complex infrastructures with confidence, translate technical data into meaningful risk narratives, and design systems that balance control with operational freedom. This mastery represents the evolution from mere compliance to true digital leadership, where every byte of data becomes both protected and purposeful.
The Foundation of Incident Response and Operational Awareness
Incident response is the invisible guardian of every digital fortress, ensuring that when a threat emerges, it is met with precision, control, and composure. The foundation of incident response lies in the capacity to perceive abnormalities in their earliest form. Visibility is the first line of defense, and without it, even the most complex architectures stand defenseless. Symantec’s operational framework offers an ecosystem that allows security practitioners to not only detect but also interpret digital disturbances before they evolve into crises. Through its Endpoint Detection and Response systems and telemetry intelligence, every packet of data becomes a thread in the vast tapestry of network behavior.
The ability to comprehend what these threads signify defines mastery. In the realm of the Symantec 250-586 certification, candidates must demonstrate not only technical familiarity but a deeper sensitivity toward system behavior. The art of interpreting alerts and metrics transforms routine monitoring into predictive insight. A seasoned responder knows that an alert is never merely an alert; it is a whisper of intent, a trace of the unseen. Recognizing patterns, distinguishing false alarms, and connecting dispersed anomalies into one coherent narrative form the essence of professional vigilance.
Symantec’s centralized management console stands as the command nucleus for this vigilance. It gathers telemetry from endpoints, gateways, and cloud assets, providing analysts a panoramic vision. Each data stream is a narrative, and understanding how to weave them into a collective storyline marks the boundary between a novice and a true defender. When visibility deepens, so does the ability to respond intelligently.
Containment as the First Line of Control
When a threat materializes, time becomes the rarest commodity. Containment transforms chaos into order. Within Symantec’s environment, containment is not an act of aggression but of precision. It requires identifying the boundaries of infection, measuring its reach, and sealing its pathways. Administrators trained in the principles of containment learn to balance caution and action, ensuring that the network remains functional even as infected nodes are restrained.
Symantec’s isolation mechanisms allow administrators to disconnect suspicious endpoints from the broader network while preserving the ability to inspect and control them remotely. This separation maintains forensic access while ensuring that no malicious code spreads further. The certification evaluates a candidate’s understanding of when and how to execute these isolations. Knowing when to isolate can be as critical as knowing how to do it. Overzealous containment can disrupt business continuity, while hesitation can permit infiltration to deepen.
Containment also extends to communication channels, access controls, and data transmissions. A well-orchestrated containment policy defines temporary walls that preserve the sanctity of unaffected systems. Symantec’s architecture enables administrators to enforce these barriers instantly, reflecting the importance of pre-defined response playbooks. These playbooks become operational reflexes, reducing dependency on deliberation during crisis moments.
Every containment step should be traceable and justifiable. Analysts document each action, creating an audit trail that supports accountability and post-incident evaluation. Such records illuminate not only what was done but also how swiftly and coherently the team reacted. Within the structured approach of Symantec’s solutions, containment becomes both science and discipline—guided by data, executed through instinct, and refined through experience.
The Art of Event Correlation and Analytical Comprehension
In the flood of alerts that modern networks produce, pattern recognition becomes the language of defense. Event correlation is the process of transforming fragmented data into meaningful intelligence. Symantec’s systems synthesize signals from multiple sensors—firewalls, intrusion prevention modules, endpoint logs, and cloud APIs—into an integrated framework that reflects reality as it unfolds.
Mastering event correlation means perceiving the rhythm of the network and identifying where that rhythm falters. A single alert might appear insignificant, but when correlated with seemingly unrelated events, it may reveal the anatomy of an unfolding compromise. The exam challenges candidates to use analytical thinking to connect these dots across varied domains. Understanding log formats, time synchronization, and alert hierarchies enables responders to craft a clear picture out of digital noise.
Event correlation relies on context. Context transforms a log entry from a random event into evidence of intent. Symantec’s dashboards grant analysts the tools to view this context dynamically. They allow comparison between current behaviors and historical baselines, revealing patterns that humans alone might overlook. With correlation comes the power of foresight, as analysts begin to recognize the steps adversaries take before execution.
Such correlation also helps define response prioritization. Not every anomaly is an emergency, and not every alert deserves equal attention. By correlating events effectively, analysts learn which incidents demand immediate containment and which require observation. This discernment reduces alert fatigue and aligns operational energy with real threats. Within Symantec’s structure, event correlation is not merely a technical task but a philosophy of interpretation—a disciplined practice that transforms raw data into strategic foresight.
Structured Methodology and Framework Alignment
Incident response cannot rely solely on intuition; it thrives on structure. The process demands a systematic framework that defines how teams classify, assess, and escalate incidents. Frameworks such as those outlined in industry standards inspire consistency, accountability, and predictability in times of uncertainty. Within the Symantec 250-586 certification, understanding structured response is not an optional skill—it is central to professional credibility.
Symantec’s methodologies align with widely recognized standards, encouraging adherence to staged response cycles. Each phase—from preparation to recovery—must be executed with documented clarity. Classification determines whether an event qualifies as an incident, while severity rating dictates the level of urgency and resource allocation. Analysts who internalize these protocols can manage incidents without panic, ensuring that responses remain proportional and aligned with policy.
Escalation is another core element of structured methodology. Knowing when to escalate an incident prevents stagnation and ensures expertise is applied efficiently. The ability to communicate escalation requirements precisely allows organizations to mobilize higher-level resources quickly. Within Symantec’s environment, automation and workflow orchestration support this escalation by routing alerts to the right specialists at the right time.
Framework alignment also supports compliance. Many industries operate under legal obligations requiring specific reporting and handling procedures for digital incidents. Symantec’s integrated compliance modules assist analysts in documenting each procedural step in line with governance mandates. Candidates preparing for the certification must grasp not only technical remediation but also the ethical and regulatory responsibilities attached to digital response. Structured methodology thus becomes the backbone of operational integrity.
Eradication and Systemic Restoration
Once containment has been achieved, eradication follows as the decisive act of cleansing. Eradication is the surgical removal of all traces of compromise. Symantec’s remediation tools execute this with precision—detecting residual components, reversing unauthorized modifications, and verifying integrity. Yet the act of eradication requires strategic understanding. Removing a single artifact without addressing its root vector invites recurrence.
A skilled responder investigates persistence mechanisms, hidden registries, and scheduled tasks that may attempt to reinfect. Symantec’s analytical agents assist in this by examining behavioral anomalies and scanning memory, file systems, and registry entries for evidence of survival techniques. The candidate must understand how to interpret these findings and design eradication sequences that leave no fragment behind.
Timing plays a crucial role. Eradication should never precede assurance that all necessary evidence has been preserved. Forensic readiness dictates that logs, snapshots, and other digital traces be captured before cleanup begins. Symantec’s forensics modules safeguard this balance by archiving relevant evidence automatically. Eradication, therefore, becomes an orchestrated dance between cleansing and preservation.
After removal comes restoration. Systems must be validated before being reintroduced into production. Restoring from clean backups, verifying cryptographic signatures, and testing integrity ensure that the network regains stability without hidden contaminants. Symantec’s restoration features allow for rollback verification, confirming that no latent threats remain dormant. This process symbolizes not only recovery but renewal—a return to equilibrium fortified by lessons learned.
Post-Incident Reflection and Continuous Enhancement
An incident’s conclusion marks not an end but a beginning. Post-incident reflection transforms experience into strategy. Symantec’s audit trails and report generation capabilities enable responders to analyze the sequence of events, identify response inefficiencies, and propose future improvements. Within the scope of the 250-586 certification, candidates are expected to grasp this cyclical nature of security operations.
Reviewing incidents involves evaluating both human and technical performance. Analysts assess whether detection thresholds were sufficient, whether containment occurred promptly, and whether communication remained clear. Each of these factors becomes a variable in refining future readiness. The concept of continuous improvement sits at the heart of modern security operations. Through repetition and reflection, organizations evolve from reactive entities into adaptive organisms.
Symantec’s learning architecture supports this evolution. Its integrated dashboards allow visualization of incident metrics over time, revealing whether detection rates improve and response times shrink. Automated reporting translates technical results into business-relevant insights, bridging the gap between security teams and leadership. This translation fosters shared accountability across departments, creating a culture where every employee becomes part of the defensive mechanism.
Moreover, post-incident analysis nurtures resilience. By transforming each encounter into a repository of knowledge, security teams grow intellectually prepared for future challenges. In this way, Symantec’s operational philosophy aligns with the larger idea that security is not a product but a process—one that evolves continuously through discipline and awareness.
Automation and the Acceleration of Response Dynamics
In the realm of incident response, speed determines survival. Automation introduces velocity without sacrificing accuracy. Symantec’s security orchestration capabilities integrate decision logic into predefined workflows, ensuring that repetitive actions execute instantly when specific conditions arise. Automation eliminates hesitation, transforming detection into immediate containment and mitigation.
Through playbook design, administrators craft automated responses that mirror expert judgment. These playbooks define sequences of actions triggered by recognizable threat patterns. When a known ransomware signature is detected, the playbook may isolate the device, block its address, notify the operations center, and initiate forensic preservation—all within moments. Such responsiveness minimizes the window of exposure and prevents lateral spread.
Automation also enhances consistency. Human responders, under pressure, may interpret policies differently or overlook minor steps. Automated workflows ensure procedural uniformity, preserving the integrity of the organization’s response posture. Within Symantec’s environment, automation is never about replacing human expertise but augmenting it. It liberates analysts from mechanical tasks, allowing them to focus on strategic interpretation.
The certification emphasizes understanding not only how to create automation rules but how to monitor and refine them. Over-automation without oversight can lead to unintended consequences, such as legitimate processes being blocked. Therefore, candidates must master the art of balance—using automation as an accelerator, not as an uncontrollable force. Properly calibrated, automation transforms operational tempo from reactionary to predictive, embodying the ideal of proactive defense.
Communication, Coordination, and Operational Harmony
In every incident, technology may be the tool, but communication is the force that shapes the outcome. A well-managed incident response requires coordination across teams, departments, and sometimes entire organizations. Symantec’s operational tools emphasize structured communication channels that preserve clarity under pressure.
Effective communication ensures that technical actions align with organizational objectives. Incident reports, notifications, and status updates must convey accuracy without overwhelming recipients. Candidates studying for certification must understand the art of communicating incidents clearly, avoiding unnecessary complexity. Transparency preserves trust, while discretion prevents panic.
Symantec’s reporting modules support this by allowing customizable communication templates that deliver essential details in accessible formats. These reports become the bridge between analysts and executives, translating technical intricacies into managerial insight. Coordinated communication also reinforces chain-of-command awareness, ensuring that every decision passes through the correct hierarchy.
In broader operations, collaboration tools integrate seamlessly with incident response platforms. Teams share investigative findings, escalate alerts, and distribute responsibilities within unified dashboards. This interconnectivity fosters collective intelligence—multiple perspectives analyzing a single event to achieve greater precision. The more harmonized the communication, the faster the resolution and the stronger the overall defense.
Through this structured exchange of information, incident response transforms into a symphony of synchronized actions. Each participant contributes to a shared rhythm of recovery, where leadership guides, analysts execute, and systems comply with flawless cadence.
Forensic Readiness and Evidence Preservation
Forensic readiness ensures that every incident becomes an opportunity for legal, regulatory, and strategic learning. Symantec’s framework allows digital evidence to be captured, preserved, and analyzed without contaminating its integrity. Forensic evidence is fragile; once altered, its credibility diminishes. Thus, a core element of incident mastery is understanding how to balance remediation with preservation.
When a compromise occurs, analysts capture snapshots of affected systems, log files, and cryptographic hashes. These elements form the foundation of digital forensics. Symantec tools streamline this process, securing metadata and ensuring chronological consistency. Candidates must comprehend how to maintain the chain of custody—a sequence of controlled transfers that guarantees authenticity.
Forensic readiness is not a post-incident luxury; it is a pre-incident discipline. Systems must be configured to generate detailed logs, preserve timestamps, and support retention policies before any breach occurs. This preparedness ensures that when analysis becomes necessary, data is already structured for scrutiny.
Within Symantec’s architecture, forensic readiness merges with compliance obligations. Legal frameworks often demand proof of actions taken during and after incidents. Having a verifiable audit trail reduces liability and strengthens organizational credibility. For candidates, understanding these forensic principles signifies maturity in operational comprehension. Every preserved byte of data becomes a witness, and every log a testimony of diligence.
Predictive Defense and Anticipatory Awareness
The pinnacle of incident response mastery lies not in reaction but in anticipation. Predictive defense transcends traditional detection by identifying the precursors of compromise. Symantec’s analytics engines employ machine learning and behavioral modeling to foresee potential intrusions before execution. These predictive systems analyze login anomalies, privilege escalations, and irregular data flows to reveal the unseen architecture of intent.
Mastery in this domain demands intellectual curiosity. Analysts must learn to interpret predictive indicators not as isolated alarms but as evolving patterns. Anticipation emerges from cumulative awareness—recognizing when routine deviations signify something greater. The certification challenges candidates to cultivate this forward-looking mindset, transforming them from responders into strategists.
Predictive defense also relies on continuous data enrichment. Symantec’s ecosystem draws from global threat intelligence, ensuring that local defenses benefit from collective insight. Each organization contributes telemetry, which feeds into algorithms that refine future predictions. This networked intelligence converts individual experiences into shared resilience.
Through anticipation, organizations transcend vulnerability. Predictive awareness ensures that incidents diminish in frequency and severity, as threats are intercepted before manifestation. This principle encapsulates the spirit of operational mastery—understanding not just how to respond, but how to foresee, prevent, and evolve continuously.
The Transformative Core of Symantec’s Security Analytics
In the contemporary cybersecurity spectrum, analytics have evolved into the nerve center of defense. Symantec’s architecture of protection is built upon an intelligent analytical core that continuously processes global telemetry, interpreting the unseen signals hidden within digital activity. Every packet of data, every file execution, and every user interaction carries a narrative that, when analyzed with precision, reveals the first signs of compromise. For aspirants of the 250-586 certification, mastering this analytical essence is paramount, as it not only sharpens detection capabilities but also nurtures strategic foresight. Within Symantec’s infrastructure, analytics do not operate as passive observers; they act as dynamic interpreters of global cyber behavior, capable of discerning the faintest fluctuations that precede a major intrusion. The essence of analytics lies in decoding patterns before they culminate into breaches, enabling proactive responses that redefine digital resilience.
Security analytics within Symantec are designed to interpret enormous data volumes through layered behavioral models. Telemetry flows from countless endpoints across industries, geographies, and networks, each contributing microscopic insights that, when aggregated, form a panoramic view of global threat movement. This orchestration of intelligence operates continuously, transforming scattered events into cohesive narratives. Understanding how these signals are interpreted, filtered, and correlated allows cybersecurity professionals to perceive risk as a living entity, not a static condition. Candidates must therefore immerse themselves in Symantec’s analytical philosophy—where visibility, context, and velocity unite to build predictive defense frameworks capable of deflecting attacks before damage unfolds.
The Global Intelligence Network as the Digital Nervous System
Symantec’s Global Intelligence Network, often referred to as the world’s most expansive sensor web, embodies the true manifestation of interconnected defense. It stretches across continents, integrating millions of sensors, probes, and endpoint monitors that capture live indicators of compromise. This data stream is funneled into Symantec’s analytical core, where automated models and human expertise intersect to deliver intelligence of unmatched accuracy. The Global Intelligence Network functions much like a human nervous system—it senses, reacts, and transmits impulses that guide the body’s defenses against unseen harm. Its significance in cybersecurity parallels the importance of neural responses in sustaining life.
Within the ecosystem, GIN thrives on velocity. Threats are identified within milliseconds, and their fingerprints are matched against a colossal repository of known malicious behaviors. Yet, the brilliance of GIN lies in its adaptability. It identifies unknown threats by studying deviations, contextualizing their behaviors, and mapping them to probabilistic risk scores. Each observation strengthens the network’s intelligence, creating a living system that learns, evolves, and strengthens itself continuously. For candidates, understanding how GIN refines threat detection through pattern recognition, heuristics, and machine-guided analysis is crucial. It is not simply a data collection mechanism; it is an ecosystem of self-enhancing perception that underpins Symantec’s analytical supremacy.
Through this network, insights emerge that transcend traditional boundaries. A malicious file detected in one region may trigger instant protective measures for users in another hemisphere. This distributed awareness minimizes reaction latency and amplifies collective immunity. The network thrives on collaboration, interlinking anonymized threat data from enterprises, governments, and individual users. It is through this constant exchange that global digital safety is maintained, demonstrating that in the realm of cybersecurity, unity of intelligence equates to strength of defense.
Contextual Enrichment in Threat Intelligence Interpretation
The foundation of effective threat intelligence lies not merely in data accumulation but in contextual comprehension. A fragment of code or a suspicious process means little without the environment that defines its behavior. Symantec’s intelligence ecosystem is built upon the principle of contextual enrichment—an analytical approach that transforms raw telemetry into meaningful, actionable insight. It examines not only the presence of a threat but its relationships, its propagation methods, and its interaction with legitimate systems. Through this enrichment process, administrators can discern intent, motive, and potential impact before an attack fully manifests.
In threat intelligence analysis, context functions as the lens that clarifies ambiguity. A single network anomaly, when observed in isolation, may appear benign. Yet, when cross-referenced with geolocation data, historical reputation, and temporal activity, it might expose a covert infiltration attempt. Symantec’s threat intelligence framework integrates domain reputation, IP profiling, file hashing, and behavioral sequencing into a unified view that enables precise interpretation. This contextual matrix empowers defenders to perceive the threat landscape as a connected tapestry rather than fragmented data fragments.
For those preparing for the 250-586 certification, mastery of this contextual reasoning is essential. The ability to interpret multi-dimensional data and deduce the latent intent behind it distinguishes a proficient analyst from a mechanical observer. Symantec’s intelligence tools encourage such analytical maturity by providing layered visibility into how files behave across different systems, how they mutate to evade detection, and how correlated evidence can unmask sophisticated intrusion tactics. In a domain where adversaries thrive on deception, context becomes the antidote to confusion and the foundation of foresight.
The Emergence of Machine Learning in Symantec’s Defensive Framework
Symantec’s innovation in cybersecurity is deeply intertwined with the evolution of machine learning. The company’s analytical frameworks employ both supervised and unsupervised learning methodologies to detect deviations that might escape human perception. These models digest vast datasets, continuously refining their understanding of normal and abnormal behavior across endpoints, cloud networks, and applications. Machine learning within this ecosystem does not replace human analysts; it magnifies their capabilities by identifying patterns too subtle or too vast for manual scrutiny.
Supervised models are trained with labeled datasets, enabling them to recognize known threat behaviors with pinpoint accuracy. Conversely, unsupervised models explore data without preconceptions, detecting anomalies that defy prior classification. The interplay between these two forms creates a balance of precision and discovery. It allows Symantec to identify both familiar and unprecedented threats, fortifying networks against evolving adversarial tactics. For certification candidates, comprehending this adaptive synergy offers a competitive advantage, as the examination often evaluates one’s ability to understand analytical evolution through machine intelligence.
The brilliance of machine learning lies in its self-reinforcing loop. Every detection enriches the dataset, and every false positive contributes to model refinement. Over time, the system achieves heightened discernment, learning from its environment in a manner akin to human intuition. Yet, unlike human intuition, its memory never fades, its focus never wavers, and its precision sharpens with each passing cycle. This autonomous evolution ensures that Symantec’s defenses grow more predictive with every threat encounter, embodying the future of intelligent cybersecurity.
Data Visualization, Governance, and Compliance Alignment
In an era where governance and accountability hold as much significance as protection itself, Symantec integrates visualization and analytics into governance workflows. Through rich dashboards and interactive interfaces, complex data sets are transformed into comprehensible visual forms that bridge the gap between technical insights and executive understanding. These dashboards reveal threat distribution, vulnerability patterns, and risk concentration across departments or regions. They empower decision-makers to visualize security posture in real time and measure the tangible outcomes of implemented controls.
Visualization is not merely aesthetic; it is interpretative intelligence. It translates abstract data into cognitive clarity, enabling professionals to perceive risk trajectories and mitigation progress. In compliance-sensitive sectors, these analytical visualizations provide audit-ready evidence of adherence to regulatory mandates. They simplify the demonstration of due diligence and continuous monitoring—two critical components of digital governance. Candidates pursuing certification should therefore appreciate the dual function of analytics: one of operational defense and another of strategic assurance.
Symantec’s reporting systems allow dynamic customization, enabling analysts to isolate specific behaviors, timeframes, or geographical zones. Through such granular insight, an enterprise can trace the lineage of a threat, identify systemic weaknesses, and refine its control mechanisms. In large organizations, this ability to trace and visualize risk evolution transforms compliance from a static checkbox process into a living cycle of improvement. Governance through analytics, therefore, becomes a proactive pursuit rather than a retrospective obligation, setting the stage for a more accountable security culture.
The Expansion of Cloud-Based Analytics and Adaptive Protection
The paradigm shift toward cloud environments redefined how Symantec delivers security intelligence. Traditional perimeter defenses, once sufficient for on-premise infrastructures, falter in hybrid and multi-cloud architectures. Recognizing this, Symantec evolved its analytics engine into the cloud through solutions like its CloudSOC and CASB modules. These frameworks extend visibility across Software-as-a-Service environments and cloud workloads, ensuring that data protection follows users wherever they operate. Cloud analytics merge the depth of endpoint telemetry with the breadth of network intelligence, providing continuous insight into cloud-native threats, misconfigurations, and unauthorized data exchanges.
In cloud ecosystems, data flows are dynamic, dispersed, and often opaque. Symantec’s cloud analytics illuminate this obscurity, identifying shadow IT activities, unmanaged access, and policy deviations. These analytical layers create a panoramic visibility that encompasses every user session, file transfer, and configuration change. The intelligence derived from such oversight empowers administrators to maintain sovereignty over their data even when hosted in shared or third-party infrastructures. The evolution toward cloud analytics marks not just a technological transition but a philosophical one—security without boundaries, powered by analytics without interruption.
For certification candidates, understanding this evolution is indispensable. It represents the practical fusion of data science and cloud security, where every transaction, permission, and connection becomes a potential data point in the analytical continuum. Mastering these frameworks requires an appreciation of both architecture and algorithm, as cloud analytics depend on the harmony between real-time processing and adaptive intelligence. Symantec’s approach exemplifies how analytical insight transforms the vast, unpredictable expanse of the cloud into a domain of order, visibility, and trust.
Predictive and Automated Intelligence in Modern Defense
The transformation from reactive to predictive defense defines the pinnacle of modern cybersecurity. Symantec’s predictive analytics leverage global telemetry trends to anticipate vulnerabilities before they are exploited. By studying recurring attack vectors, temporal patterns, and adversarial methodologies, predictive systems forecast likely points of compromise. These insights enable pre-emptive patching, configuration hardening, and behavioral policy adjustments that neutralize risks at inception. Predictive analytics convert hindsight into foresight, ensuring that defenses mature faster than threats evolve.
Automation further amplifies this predictive power. Symantec’s systems can trigger automatic containment, isolation, or remediation based on analytical thresholds. This orchestrated response minimizes latency and human error, ensuring that even sophisticated attacks meet instant resistance. However, automation demands equilibrium. Excessive reliance on automatic actions may create blind zones, while insufficient automation slows response cycles. The art of mastering automation lies in calibrating analytical precision with operational restraint. Candidates aspiring for certification must demonstrate an understanding of this balance—where efficiency and awareness coexist harmoniously.
In predictive environments, analytics are not static dashboards but living organisms of logic. They continuously ingest data, assess probabilities, and refine outcomes. This self-improving cycle mirrors biological adaptation, where every encounter with adversity strengthens the defensive structure. The integration of artificial intelligence within this predictive realm enhances situational awareness, guiding analysts to focus their attention where it matters most. Such orchestration between prediction and automation forms the backbone of Symantec’s modern resilience strategy, illustrating that in the age of intelligent threats, anticipation is the truest form of protection.
The Philosophy of Continuous Observation and Analytical Mastery
At the heart of Symantec’s analytics philosophy lies an enduring truth: cybersecurity is an infinite pursuit. Threat landscapes mutate with unrelenting velocity, and defensive architectures must evolve in parallel. Continuous observation becomes not a task but a mindset—a perpetual vigilance guided by analytical intuition. Within Symantec’s ecosystem, observation extends beyond log monitoring; it encapsulates behavioral study, trend recognition, and deviation analysis. Professionals who internalize this philosophy cultivate a sixth sense for anomalies, perceiving risks that remain invisible to untrained eyes.
In this continuum, analytics serve as both the microscope and the telescope of cybersecurity. They zoom into the minutiae of endpoint behavior while simultaneously surveying global threat horizons. This duality enables organizations to act locally with global awareness. For candidates pursuing the 250-586 certification, developing an appreciation for this interconnected observation enhances analytical agility. It transforms them from reactive responders into anticipatory strategists capable of guiding enterprises through turbulence with composed precision.
The evolution of threat intelligence and security analytics under Symantec’s stewardship exemplifies the convergence of technology, insight, and adaptability. Each analytical process, each learning algorithm, and each visualization dashboard contributes to a living intelligence that learns from the world and protects it in return. Within this synergy, defense becomes more than protection—it becomes prediction, perception, and progression. Those who master this art do not merely analyze data; they interpret the language of digital existence itself, turning patterns into protection and uncertainty into understanding.
Conclusion
The Ultimate Symantec 250-586 Study Guide weaves a complete path from foundational awareness to advanced proficiency. Across six immersive parts, it builds the knowledge, confidence, and analytical acuity required to excel in Symantec’s certification landscape.
This journey starts with understanding the ecosystem of Symantec’s security architecture, deepens through practical exploration of endpoint protection and data loss prevention, and culminates in the refinement of response and analytical skills. The interconnected nature of these elements mirrors how modern cybersecurity ecosystems function—each component reinforcing the other.
What truly defines a successful Symantec 250-586 professional is not memorization, but integration. When theory becomes instinct, and tools become extensions of thought, mastery emerges. The certification stands as validation of technical acumen and professional integrity—qualities that extend far beyond the examination hall.
As you prepare, remember that persistence outweighs perfection. The learning process itself sharpens your ability to think critically, troubleshoot efficiently, and adapt confidently. Passing the exam will mark an achievement, but sustaining the mindset of vigilance, curiosity, and ethical responsibility will define your legacy as a Symantec-certified expert.
Through diligence and understanding, you transform from a student of cybersecurity into a guardian of digital trust—equipped not just to defend systems, but to inspire confidence in an ever-evolving technological world.