Exam Code: 1D0-441
Exam Name: CIW Database Specialist
Certification Provider: CIW
Corresponding Certification: Master CIW Enterprise Developer
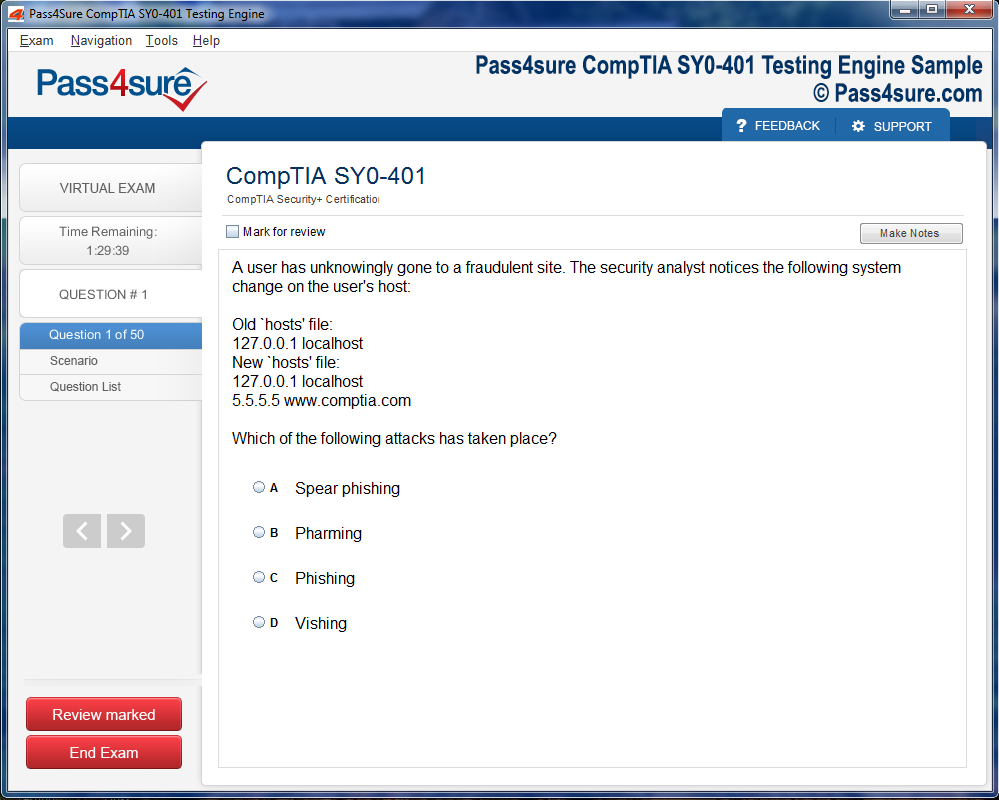
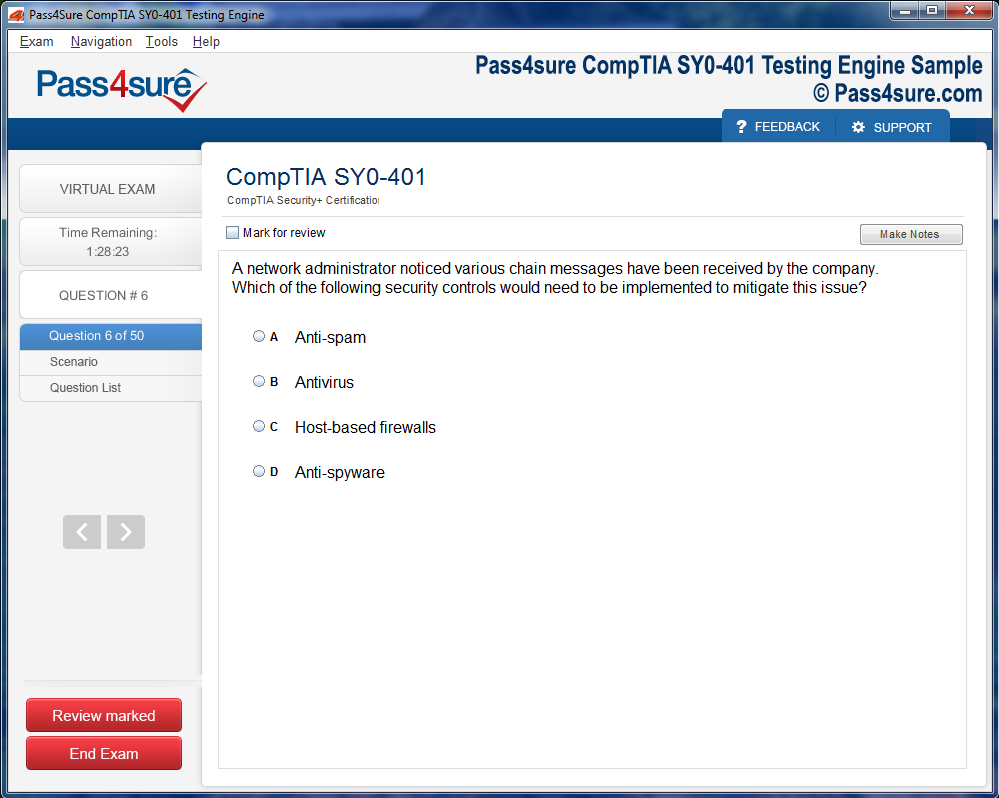
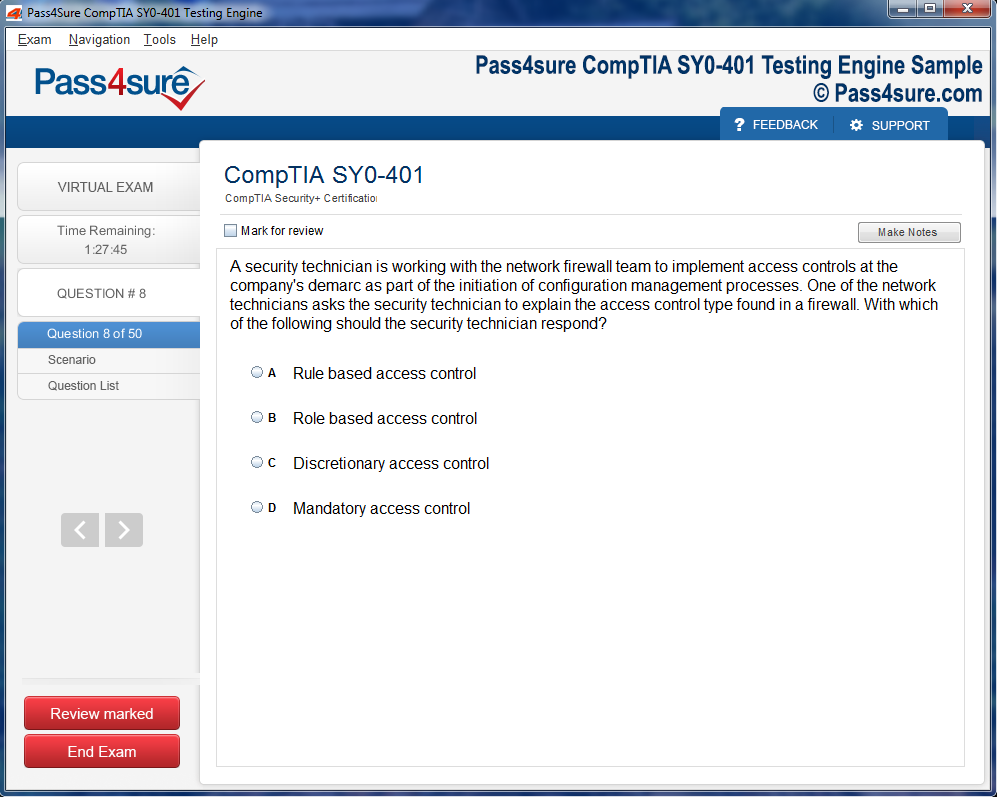
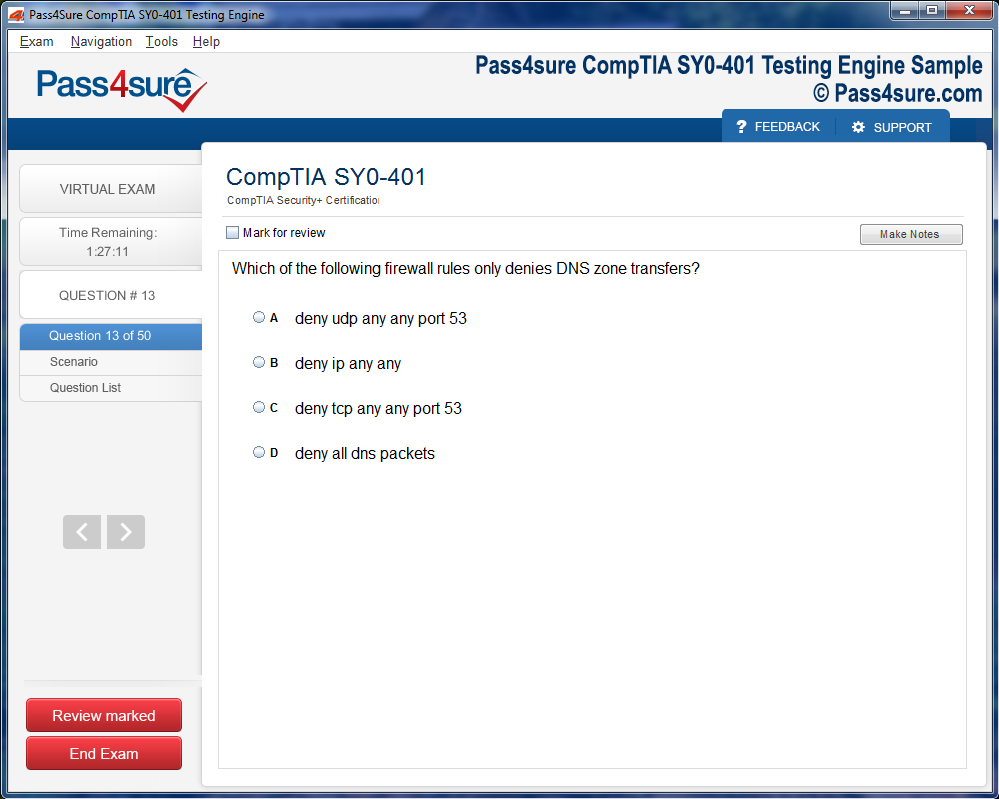
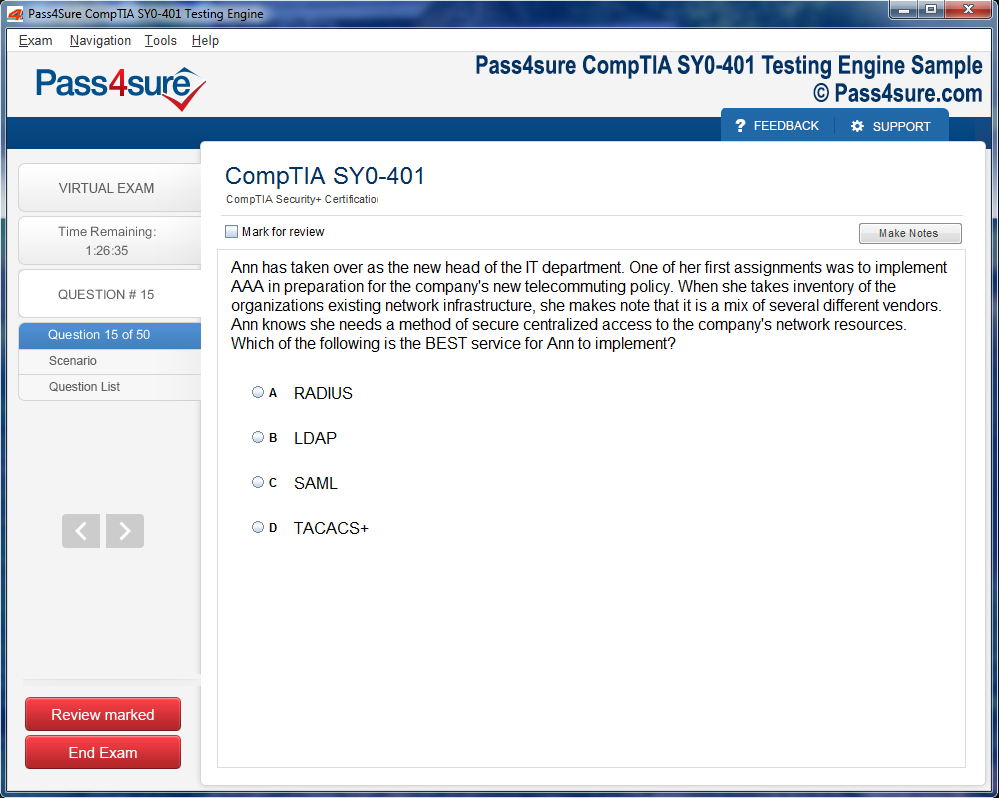
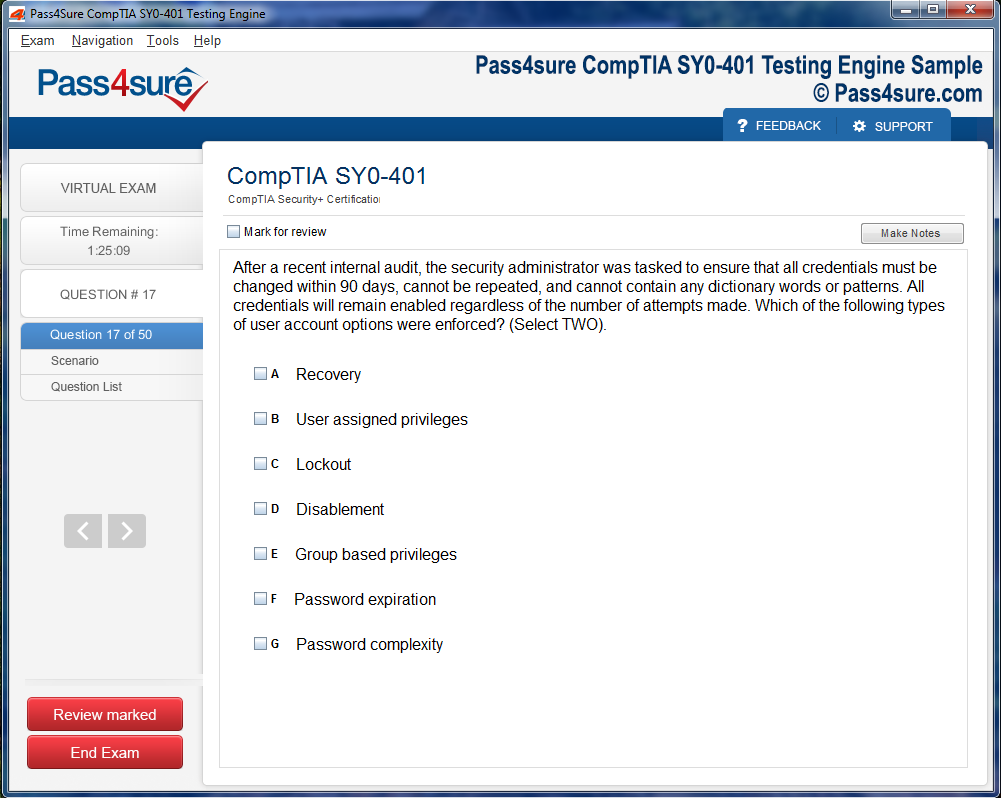
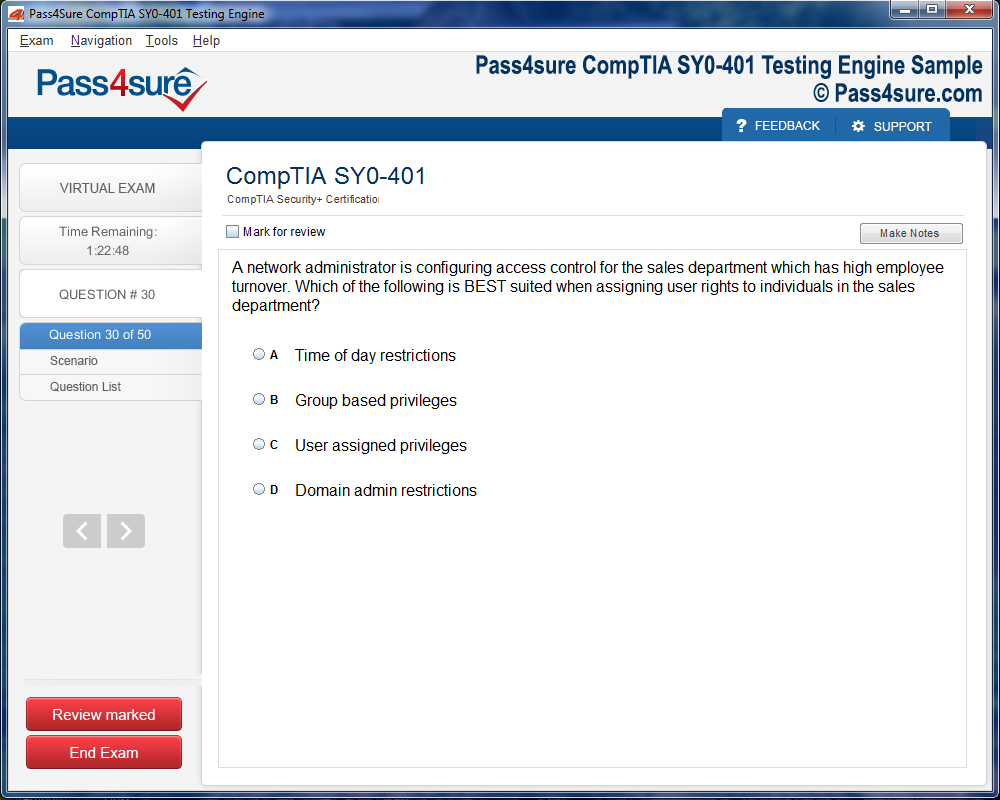
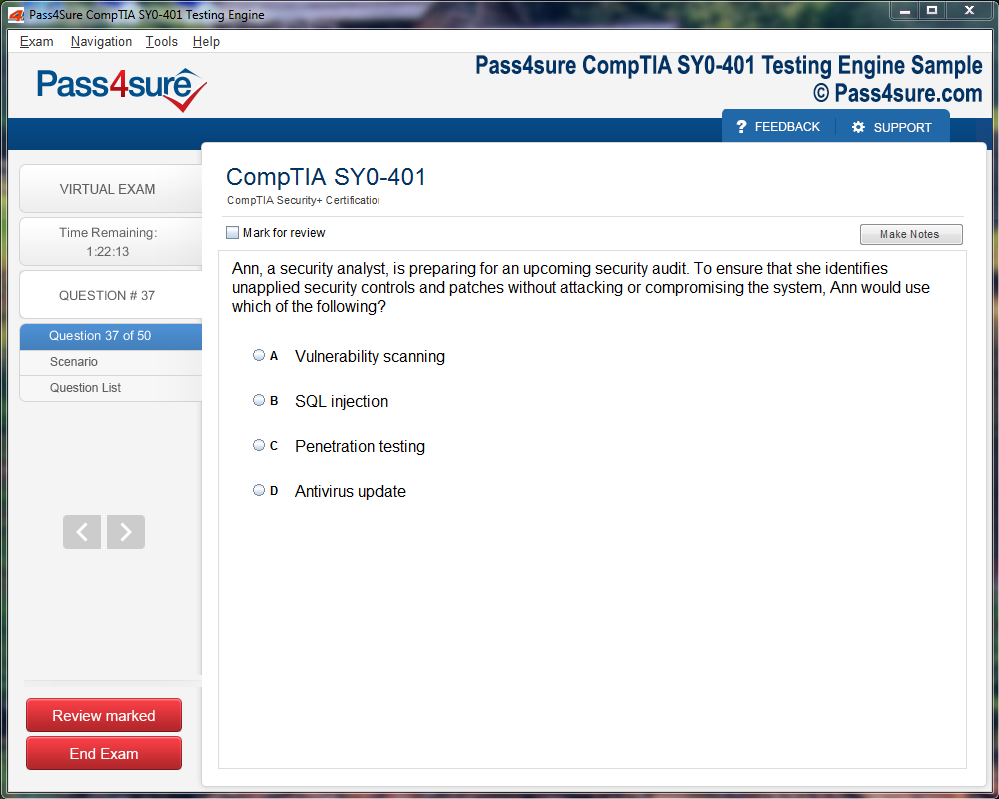
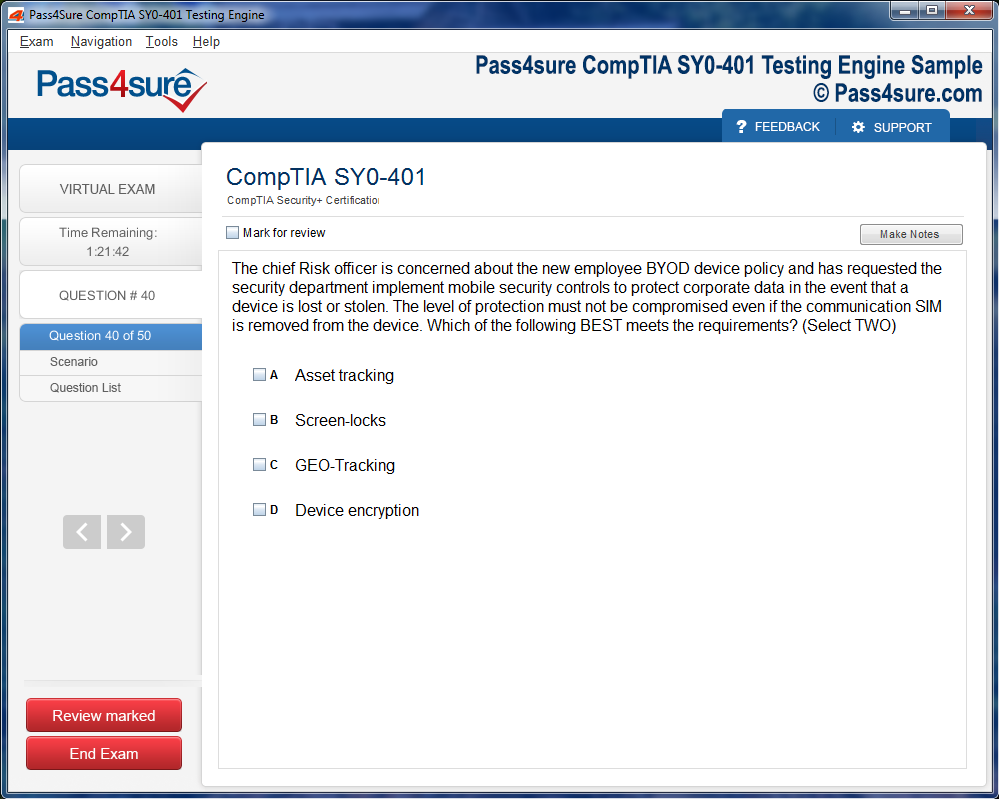
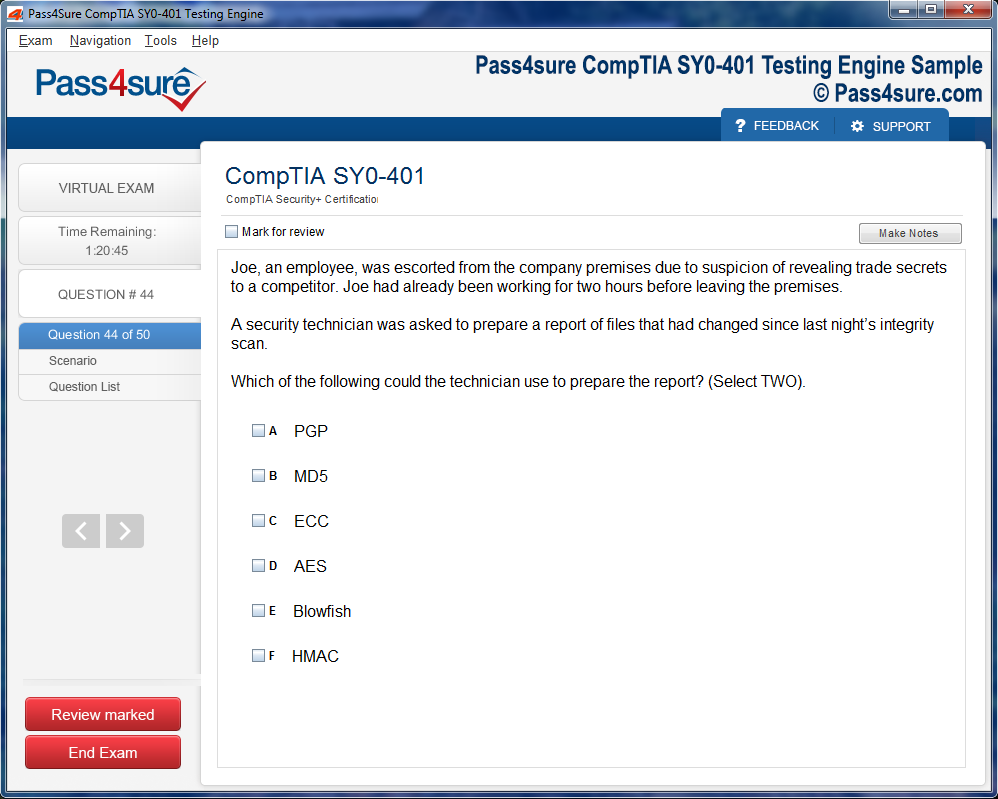
Product Screenshots
Frequently Asked Questions
How does your testing engine works?
Once download and installed on your PC, you can practise test questions, review your questions & answers using two different options 'practice exam' and 'virtual exam'. Virtual Exam - test yourself with exam questions with a time limit, as if you are taking exams in the Prometric or VUE testing centre. Practice exam - review exam questions one by one, see correct answers and explanations.
How can I get the products after purchase?
All products are available for download immediately from your Member's Area. Once you have made the payment, you will be transferred to Member's Area where you can login and download the products you have purchased to your computer.
How long can I use my product? Will it be valid forever?
Pass4sure products have a validity of 90 days from the date of purchase. This means that any updates to the products, including but not limited to new questions, or updates and changes by our editing team, will be automatically downloaded on to computer to make sure that you get latest exam prep materials during those 90 days.
Can I renew my product if when it's expired?
Yes, when the 90 days of your product validity are over, you have the option of renewing your expired products with a 30% discount. This can be done in your Member's Area.
Please note that you will not be able to use the product after it has expired if you don't renew it.
How often are the questions updated?
We always try to provide the latest pool of questions, Updates in the questions depend on the changes in actual pool of questions by different vendors. As soon as we know about the change in the exam question pool we try our best to update the products as fast as possible.
How many computers I can download Pass4sure software on?
You can download the Pass4sure products on the maximum number of 2 (two) computers or devices. If you need to use the software on more than two machines, you can purchase this option separately. Please email sales@pass4sure.com if you need to use more than 5 (five) computers.
What are the system requirements?
Minimum System Requirements:
- Windows XP or newer operating system
- Java Version 8 or newer
- 1+ GHz processor
- 1 GB Ram
- 50 MB available hard disk typically (products may vary)
What operating systems are supported by your Testing Engine software?
Our testing engine is supported by Windows. Andriod and IOS software is currently under development.
Boost Your Career with CIW 1D0-441 – Database Specialist Certification
In the labyrinthine corridors of database management, data integrity assumes the role of an invisible sentinel, guarding the veracity and coherence of information. CIW 1D0-441 aspirants navigate constraints, triggers, and referential dependencies, weaving a lattice where anomalies are preemptively quelled. Each rule enforced, whether through primary keys or cascading updates, manifests as a ritual of precision, a choreography of logical discipline. The ability to anticipate incongruities before they manifest transforms a practitioner from a mere custodian into a prescient steward of information.
The Symbiosis of Performance and Architecture
Databases are not inert repositories; they are kinetic organisms whose vitality is measured by efficiency and adaptability. Understanding indexing, partitioning, and query optimization is akin to learning the biomechanics of a living system. CIW 1D0-441 candidates explore execution plans as cartographers charting unknown terrain, discerning the subtle interplay between CPU cycles, memory hierarchies, and I/O throughput. The nuanced decisions surrounding storage engines or transaction isolation levels ripple across the system, revealing that performance is not a static metric but a dynamic equilibrium demanding foresight and experimentation.
Transactional Poetics
The orchestration of transactions embodies both rigor and artistry. Atomicity, consistency, isolation, and durability coalesce into a mnemonic symphony where each operation resonates with intent. Prospective database professionals are trained to anticipate deadlocks, resolve conflicts, and ensure concurrency does not fracture integrity. Viewing transactions through the lens of narrative cadence allows one to perceive their rhythm, their inevitable push and pull, transforming routine operations into an exercise of intellectual elegance.
Enigmas of Data Modeling
Modeling data transcends tables and columns; it ventures into abstraction, capturing the essence of entities and their ephemeral relationships. CIW 1D0-441 aspirants grapple with ER diagrams and schema blueprints, yet the endeavor extends beyond visual representation. Conceptual modeling demands philosophical introspection—deciding what constitutes an object, what attributes define it, and how temporal fluctuations alter associations. The subtle artistry in predicting use cases and projecting future evolutions imbues the model with longevity and adaptability, ensuring that the database remains responsive to unforeseen exigencies.
The Esoteric Art of Query Optimization
SQL is more than a functional language; it is a canvas for cognitive ingenuity. Optimization entails parsing, refactoring, and sometimes reimagining queries to coax peak performance from the underlying engine. Candidates dissect execution plans, leverage indexes judiciously, and engage in micro-optimizations that cumulatively yield macro-efficiency. This pursuit requires a balance of creativity and analytical rigor, transforming mundane commands into an exercise in strategic foresight.
Guardianship of Data Security
In a milieu where digital fortresses are perpetually assailed, security is the sine qua non of responsible database stewardship. CIW 1D0-441 training immerses candidates in cryptographic schemas, role-based access control, and audit mechanisms. Beyond technical acumen, it instills a heightened ethical consciousness, ensuring that custodians of data comprehend both the gravity and the vulnerability of the information they oversee. Each encrypted field, each permission meticulously assigned, constitutes a bulwark against the encroachment of malfeasance.
Scalability as an Expedition
Scaling a database is akin to embarking on an expedition through mutable terrain. Horizontal and vertical scaling, replication, and load balancing are tools for navigating complexity without sacrificing coherence. Candidates learn to anticipate the ramifications of growth, to architect systems that expand gracefully while maintaining consistency. The endeavor is both scientific and imaginative, requiring foresight that bridges current demands and prospective horizons.
The Lattice of Interoperability
Databases seldom exist in isolation. Modern ecosystems demand seamless interoperability with applications, analytics platforms, and ancillary services. Mastery of APIs, connectors, and middleware transforms a database from a static entity into a node within a vibrant informational lattice. CIW 1D0-441 candidates cultivate fluency in integrating heterogeneous systems, ensuring that data flows harmoniously without succumbing to latency or discord.
Temporal Dimensions in Database Design
Time is not merely a recorded attribute; it is a vector that shapes the evolution of data. Understanding temporal data, historical snapshots, and versioning strategies equips professionals to navigate longitudinal analyses with precision. Designing for temporality requires a foresighted mindset, envisioning how current decisions will influence archival retrieval, trend detection, and regulatory compliance in a world where historical fidelity is paramount.
The Cognition of Continuous Learning
Database landscapes are protean, shifting with each technological innovation and business exigency. CIW 1D0-441 emphasizes that mastery is never static. Professionals are encouraged to cultivate curiosity, to interrogate assumptions, and to experiment with emergent paradigms. The pursuit of database excellence is iterative, demanding an agile intellect that thrives on both structured learning and serendipitous discovery.
The Alchemy of Query Optimization
In the labyrinthine corridors of relational databases, query optimization emerges as an almost mystical practice, where the adept crafts statements not merely for functionality but for alacrity. Understanding how the database engine interprets instructions enables the practitioner to orchestrate operations with precision, reducing latency and maximizing throughput. Every SELECT, JOIN, and GROUP BY clause becomes a brushstroke in a grand tableau of efficiency, transforming cumbersome tasks into fluid expressions of logic.
Indices act as the keystones in this edifice, providing accelerants for retrieval while demanding judicious application. Misapplied indexes may render performance decrements as subtle as they are insidious, and the sophisticated specialist learns to detect these anomalies through a blend of intuition and analytic rigor. By interrogating execution plans and discerning patterns in query behavior, one gains a prescient understanding of potential bottlenecks, converting abstract metrics into tangible improvements in workflow efficiency.
Transmuting Raw Data into Strategic Insight
SQL mastery is incomplete without the art of transmutation—converting voluminous, unstructured datasets into actionable intelligence. Through complex aggregations, window functions, and nested subqueries, the adept can reveal patterns imperceptible to untrained eyes. The CIW 1D0-441 curriculum emphasizes this alchemical approach, teaching candidates to uncover correlations, forecast trends, and illuminate insights that catalyze strategic decision-making.
Beyond numerical analysis, data interpretation involves the subtlety of narrative. Each row and column is a fragment of a larger story, and the expert practitioner weaves these fragments into a coherent tableau, highlighting anomalies, cyclical trends, and emergent behaviors. The ability to narrativize data transforms the technical act of querying into an intellectual craft, where information becomes not merely a static repository but a dynamic instrument of influence.
Safeguarding Integrity Through Advanced Transactions
The fluidity of data necessitates vigilant stewardship, and here, the mastery of transactions is paramount. Transactions ensure that multiple operations execute atomically, preserving the sanctity of the database even amidst unexpected failures. The concepts of commit, rollback, and savepoint constitute a triptych of safeguards, empowering professionals to navigate complexities without compromising consistency.
In real-world applications, these mechanisms are not abstract exercises; they underpin the resilience of financial systems, inventory management platforms, and analytical engines. An adept CIW 1D0-441 candidate comprehends the interplay between transactional isolation levels and concurrency, applying nuanced strategies to mitigate conflicts and prevent anomalies that could reverberate across interconnected systems.
The Nuances of Indexing and Partitioning
Indexing and partitioning are often misunderstood as purely technical optimizations, yet their implications extend deeply into strategic database design. Correctly applied, indices facilitate rapid retrieval; poorly chosen, they incur overhead that can obfuscate performance gains. Partitioning, similarly, is a structural intervention that subdivides data into discrete segments, accelerating operations while reducing resource contention.
The professional cultivates a discerning eye, recognizing when composite indices outperform singular ones, or when horizontal partitioning alleviates pressure on monolithic tables. Such interventions are rarely prescriptive; they demand context, experimentation, and a continuous feedback loop between query performance and architectural choices. In mastering these subtleties, the specialist not only enhances efficiency but also cultivates a capacity for foresight, anticipating the evolution of data volumes and query complexity.
Elevating Analytics with Subqueries and Window Functions
Subqueries and window functions elevate SQL from a retrieval tool to an analytical powerhouse. Subqueries enable layered interrogations, permitting conditions based on dynamic, intermediate computations rather than static parameters. Window functions, meanwhile, allow sophisticated analysis across partitions of data, calculating cumulative sums, rankings, and moving averages with surgical precision.
Together, these constructs provide a lexicon for articulating insights that were previously obscured by the limitations of rudimentary queries. The CIW 1D0-441 framework challenges candidates to harness these features creatively, fostering a mindset that sees beyond immediate requirements and imagines the latent potential within datasets. By integrating these capabilities, professionals transform static tables into living ecosystems of intelligence.
Navigating the Complexity of Joins and Set Operations
The join, often considered a fundamental operation, is in truth a nexus of complexity and opportunity. Mastery involves more than syntax; it demands understanding the logical relationships between tables, anticipating the impact of inner, outer, cross, and self joins on the resulting dataset. Set operations, including UNION and INTERSECT, extend this capability, providing mechanisms to merge, compare, and contrast datasets in ways that reveal nuanced relationships.
This multidimensional approach is essential for analysts confronted with heterogeneous data sources, enabling synthesis without redundancy and clarity without oversimplification. The practitioner who comprehends these intricacies can navigate labyrinthine schemas with confidence, producing results that are both accurate and strategically illuminating.
Orchestrating Real-World Data Workflows
Ultimately, mastery of SQL and data manipulation manifests in the orchestration of real-world workflows. The technical operations—queries, transactions, indexing—coalesce into a symphony of information processing, each element contributing to a larger narrative of insight and utility. The CIW 1D0-441 candidate emerges capable of designing pipelines that ingest, transform, and output data with elegance, efficiency, and resilience.
This orchestration extends beyond databases themselves, integrating with reporting tools, analytics dashboards, and enterprise systems. Each query, each optimization, becomes a deliberate intervention in a broader ecosystem, ensuring that data flows not as a chaotic torrent but as a coherent, actionable stream. The professional’s role evolves from mere executor to strategic orchestrator, leveraging technical expertise to drive decisions, illuminate patterns, and create enduring value.
Data Security as a Cornerstone of Digital Custodianship
In an era suffused with ubiquitous digitization, the safeguarding of information transcends mere procedural necessity, morphing into a profound ethical and operational imperative. The CIW 1D0-441 certification cultivates a nuanced comprehension of data security, compelling aspirants to scrutinize vulnerabilities with a prescient lens. Scholars delve into the intricacies of cryptographic architectures, multi-tiered authentication protocols, and adaptive access control schemas, acquiring the acumen to discern latent threats and preemptively forestall breaches. Data, in this context, is not merely stored but vigilantly curated, its integrity preserved through meticulous oversight and technical sagacity.
Multifaceted Dimensions of Database Security
Security in contemporary database ecosystems is a polyhedral construct, encompassing a spectrum of interrelated strategies that extend beyond rudimentary access control. The discipline encompasses proactive auditing, continuous monitoring, anomaly detection, and strict adherence to regulatory and statutory frameworks. Professionals trained under the CIW 1D0-441 rubric are primed to implement holistic policies that ensure accountability, traceability, and resilience, crafting digital fortresses around critical informational assets. In sectors where the stakes are prodigious—such as healthcare, financial institutions, and governmental agencies—an infraction or lapse is seldom trivial, underscoring the exigency of a rigorous security ethos.
Ethical Imperatives in Data Stewardship
Security is inextricably interwoven with ethical responsibility, an axiom emphasized throughout CIW 1D0-441 training. Beyond the mere technicalities of encryption and authentication, candidates grapple with philosophical considerations surrounding the custodianship of sensitive information. Ethical praxis necessitates a judicious calibration of operational imperatives against principles of confidentiality, integrity, and equitable treatment. Decision-making transcends efficiency, demanding a cognizance of the potential ramifications of mishandled data on individuals and organizations alike. Professionals are thus sculpted into conscientious custodians, their technical competence harmonized with moral circumspection.
Cultivating a Proactive Security Mindset
The cultivation of vigilance is a hallmark of adept database management. CIW 1D0-441 aspirants are schooled in the anticipation of emergent threats, the design of robust defense architectures, and the iterative refinement of security protocols. This pedagogical approach fosters a mindset wherein security evolves from a static checklist into a dynamic, adaptive practice. By internalizing this proactive posture, professionals become agile guardians of information, capable of responding to novel vulnerabilities with dexterous ingenuity. Such foresight ensures that data remains not merely intact but optimally exploitable for legitimate operational purposes.
Integrating Security and Ethics for Professional Ascendancy
The symbiosis of security and ethical stewardship within the CIW 1D0-441 framework exemplifies the expansive responsibilities of modern database professionals. Mastery of these dual dimensions elevates practitioners from mechanistic operators to sagacious stewards of digital ecosystems, where technical proficiency is inseparable from conscientious oversight. The certification instills not only functional expertise but also a principled orientation, fostering professionals who navigate complex informational landscapes with discernment and rectitude. Such individuals become indispensable within organizations, safeguarding assets while enabling their productive deployment in alignment with societal norms and organizational mandates.
Regulatory Compliance and Organizational Accountability
In tandem with technical aptitude, regulatory literacy is indispensable in the domain of database management. CIW 1D0-441 underscores the necessity of understanding multifarious legal and compliance frameworks, equipping practitioners to navigate the labyrinthine mandates that govern data handling. Adherence to regulatory standards is not perfunctory but a critical aspect of organizational accountability, ensuring transparency and fortifying trust. Professionals are trained to implement auditing mechanisms that render operations both auditable and defensible, reinforcing the credibility of their custodianship.
Fostering a Culture of Information Vigilance
The cultivation of organizational culture is as pivotal as technical acumen in securing databases. CIW 1D0-441 inculcates an ethos of vigilance that permeates all strata of data interaction, fostering a collective consciousness attuned to security imperatives. By nurturing awareness and fostering procedural rigor among stakeholders, professionals create resilient information ecosystems capable of withstanding sophisticated cyber incursions. This cultural dimension transforms security from an individual responsibility into a shared organizational mandate, amplifying both efficacy and ethical compliance.
The Dynamic Landscape of Threat Mitigation
Threat vectors are not static; they evolve with technological advancement and emergent paradigms of cyber subversion. CIW 1D0-441 emphasizes adaptive strategies, teaching candidates to anticipate and neutralize threats before they metastasize into systemic compromise. This forward-looking perspective melds analytical rigor with creative problem-solving, engendering a cadre of specialists proficient in both detection and preemption. Through simulations, scenario analyses, and iterative practice, professionals gain the capacity to counteract even the most arcane and unanticipated vulnerabilities, ensuring the inviolability of data repositories.
Career Trajectories and Opportunities with CIW 1D0-441 Certification
The allure of the CIW 1D0-441 certification transcends mere technical dexterity, extending into the realm of career stratagems and professional distinction. Possessors of this credential inhabit a singular echelon of the IT hierarchy, where roles such as database orchestrator, data alchemist, systems architect, and IT savant become attainable not merely through ambition, but through validated competence. The certification serves as a talisman, signaling to prospective employers an individual’s adeptness at navigating the intricate labyrinth of data systems with precision and foresight.
Vocational ascension is often precipitated by the synergy between credibility and adaptability. CIW 1D0-441 furnishes aspirants with an expansive compendium of skills, facilitating seamless immersion across disparate industries. This dexterity obviates the arduous retraining typically necessitated by sector-specific technologies, enabling professionals to traverse from nimble startups to sprawling multinational conglomerates with consummate ease. Their expertise in architecting, optimizing, and stewarding databases metamorphoses into an indispensable asset, propelling organizational efficiency and innovation.
In parallel, the certification cultivates a spectrum of social capital. Recognition within professional circles burgeons, ushering pathways to mentorship, strategic alliances, and leadership ascension. A credential of this magnitude underscores a commitment to perpetual erudition, a trait highly prized amid the mercurial currents of contemporary IT ecosystems. The resultant reputation frequently begets lucrative remuneration, prestigious appointments, and access to transformative projects where technical ingenuity is paramount.
Moreover, the CIW 1D0-441 credential incubates entrepreneurial agency. Armed with an arsenal of database proficiencies, professionals are poised to craft bespoke systems for emerging enterprises, engineer analytical platforms that distill actionable insights, or proffer consultancy sagacity that transcends conventional paradigms. This entrepreneurial latitude engenders not only financial autonomy but also positions individuals as vanguards of innovation within the digital landscape.
The credential’s impact reverberates beyond immediate vocational gains. It functions as both testament and catalyst, simultaneously corroborating technical mastery while amplifying career potentialities. Individuals harnessing this certification translate abstract knowledge into tangible accomplishments, sculpting trajectories defined by strategic influence, operational excellence, and enduring professional resonance.
Cognitive Alchemy in Database Mastery
The journey toward database proficiency transcends rote memorization, evolving into a form of cognitive alchemy where abstract knowledge transmutes into actionable acumen. The practitioner cultivates an instinctive grasp of relational models, normalization intricacies, and query optimization techniques, enabling them to navigate labyrinthine data structures with fluid precision. Cognitive resilience becomes indispensable, allowing the mind to oscillate seamlessly between theory and application, translating complex constructs into tangible, operational results.
Experiential Immersion and Practical Fluency
True mastery emerges from experiential immersion. Engaging in iterative simulations, designing schema architectures, and troubleshooting multifaceted queries fosters a practical fluency that textbooks alone cannot bestow. Each exercise serves as a crucible where comprehension is tested, refined, and internalized. This process transforms abstract SQL syntax into a second language of logic, where efficiency and creativity converge to solve previously intractable problems.
Strategic Metacognition in Learning
Metacognition—the ability to observe and regulate one’s own learning processes—is a strategic lever in achieving examination excellence. Candidates who reflect on their study methodologies, assess their comprehension with rigorous self-auditing, and adjust approaches dynamically outperform those who adhere to static routines. This introspective practice amplifies retention, uncovers latent weaknesses, and converts study hours into high-yield intellectual investment, ensuring preparedness extends beyond mere exam performance.
Temporal Orchestration and Study Cadence
Time, when orchestrated with intentionality, becomes a formidable ally. Structured cadence, punctuated by cycles of deep focus and reflective consolidation, fosters neural pathways that solidify long-term retention. Strategic segmentation of complex topics, interleaving practical exercises with theoretical exploration, and periodic self-assessment fortify cognitive endurance. Such temporal choreography not only optimizes immediate exam readiness but embeds durable patterns conducive to lifelong learning.
Dialogic Engagement and Peer Synergy
Learning in isolation is a diminished endeavor. Dialogic engagement with peers catalyzes comprehension through the cross-pollination of perspectives. Articulating thought processes, challenging assumptions, and dissecting intricate problems collectively cultivates a richer understanding of database systems. Mentorship amplifies this effect, providing guided insight, heuristic shortcuts, and the nuanced wisdom that only experience can offer. Through this communal approach, abstract concepts crystallize into practical expertise.
Adaptive Cognition and Problem Anticipation
The dynamism of modern databases demands an adaptive cognition capable of forecasting challenges and preemptively crafting solutions. Professionals trained in anticipatory problem-solving are not reactive technicians but proactive architects, capable of preempting performance bottlenecks, mitigating security vulnerabilities, and optimizing system resilience. Cultivating pattern recognition, analytical foresight, and agile reasoning transforms routine operations into arenas of innovation and strategic intervention.
Intellectual Curiosity and Knowledge Perpetuation
Curiosity fuels the momentum of mastery. A practitioner’s inquisitive disposition drives exploration beyond the immediate syllabus, prompting engagement with emergent technologies, innovative design paradigms, and evolving standards. Knowledge perpetuation occurs when the individual integrates continual learning into their professional ethos, transforming each encounter with data into an opportunity for discovery, experimentation, and cognitive enrichment.
Ethical Prudence in Database Stewardship
Technical prowess alone is insufficient without ethical prudence. Navigating sensitive data demands a commitment to confidentiality, integrity, and responsible stewardship. Database specialists must balance innovation with accountability, ensuring solutions adhere to legal frameworks and organizational policies while anticipating potential societal ramifications. This ethical foundation undergirds trust, enhances professional reputation, and anchors mastery within a framework of principled action.
Analytical Elegance in Query Design
The aesthetic of analytical elegance emerges when database interactions are streamlined, precise, and optimized. Crafting queries that are not only functionally correct but also logically efficient demonstrates mastery of both syntax and systemic insight. This elegance reduces computational overhead, enhances maintainability, and provides a cognitive clarity that transforms complex data landscapes into comprehensible, navigable structures, reinforcing the practitioner’s authority in the domain.
Experiential Synthesis and Lifelong Evolution
The ultimate hallmark of CIW 1D0-441 preparation is experiential synthesis. The practitioner internalizes knowledge not as fragmented skills but as an interconnected, dynamic competency. This synthesis enables continuous evolution, where each project, challenge, or certification milestone contributes to a trajectory of enduring expertise. Mastery becomes a living process, sustained by curiosity, rigor, ethical commitment, and the relentless pursuit of intellectual refinement.
Relational database design is a craft where structure converges with logic, and elegance manifests in efficiency. At the heart of this discipline lies the ability to envision data not as static entities but as dynamic constellations, each table a universe of interconnected meaning. The process of normalization, often perceived as pedantic, is in fact an intellectual exercise that transmutes chaotic information into harmonious order. By systematically reducing redundancy and refining relationships, one cultivates a schema that is both resilient and agile, capable of accommodating unforeseen demands with minimal perturbation.
The true mastery of relational design extends beyond textbooks; it necessitates a cognitive dexterity, a synesthetic sense of how queries ripple through the lattice of tables. Indexing, key constraints, and referential integrity are not mere mechanisms but instruments of precision, sculpting performance and guaranteeing consistency. When executed with foresight, relational architecture becomes a silent symphony, orchestrating data flows in a manner that is both predictable and astonishingly efficient.
SQL Proficiency as a Cognitive Tool
Structured Query Language is often mischaracterized as a simple syntactic exercise, but for the adept practitioner, it is a cognitive instrument, an extension of analytical thought. SQL queries act as lenses, refracting raw data into insights that were previously imperceptible. Mastery entails more than memorizing SELECT, JOIN, or GROUP BY commands; it involves cultivating a fluency in logical reasoning, pattern recognition, and the anticipation of computational consequences.
Complex queries, particularly those involving nested subqueries, window functions, or recursive common table expressions, reveal the elegance of SQL as a language of both precision and creativity. When wielded with finesse, SQL enables professionals to extract narratives from numerical maelstroms, transforming raw repositories into intelligible stories that inform strategy, influence policy, and drive innovation.
Transaction Management and the Art of Consistency
In the theater of database operation, transaction management is the unsung dramaturgy that maintains equilibrium amidst chaos. Each transaction embodies a promise: atomicity, consistency, isolation, and durability. These principles, collectively known as ACID, form the philosophical bedrock upon which reliable systems are built. Mismanagement of transactions can precipitate anomalies, jeopardizing data integrity and eroding trust.
Understanding concurrency control mechanisms, deadlock resolution strategies, and rollback procedures requires a meticulous mindset, one that appreciates subtlety as much as power. Professionals trained in these domains possess not only technical acuity but also the foresight to predict interactions in highly dynamic systems, mitigating risk before it manifests.
Data Security: Fortifying the Digital Citadel
In an era where information is both currency and liability, data security assumes paramount importance. Beyond encryption algorithms and access control lists lies a strategic imperative: to anticipate threats and engineer resilience. Security in databases is a choreography of anticipation, vigilance, and responsiveness. Professionals must grapple with the dual challenge of enabling accessibility while defending against intrusion, crafting a balance that is both ethical and pragmatic.
The study of authorization models, auditing mechanisms, and vulnerability mitigation transcends technical necessity; it cultivates a mindset attuned to the consequences of negligence. Database specialists, by mastering these concepts, become custodians of digital trust, safeguarding the lifeblood of modern enterprises against both inadvertent lapses and malicious incursions.
Optimization: Sculpting Performance with Precision
Query optimization is the confluence of art and science, a domain where intuition must harmonize with empirical analysis. Beyond raw processing power, performance emerges from thoughtful indexing, judicious partitioning, and a keen understanding of execution plans. Optimization is not merely about speed; it is about elegance, efficiency, and the minimization of systemic friction.
Professionals who excel in this domain cultivate a mental model of query behavior, anticipating bottlenecks and deploying solutions before inefficiencies manifest. Such foresight transforms mundane operations into seamless interactions, elevating databases from utilitarian storage repositories to high-performance engines that propel organizational strategy.
Cross-Industry Relevance and Professional Adaptability
The true currency of CIW 1D0-441 certification is its portability across industrial landscapes. From healthcare analytics to financial systems, e-commerce infrastructures to government repositories, database proficiency translates effortlessly. This versatility arises not from rote technical skill but from a principled understanding of data logic, relational frameworks, and system architecture.
Professionals equipped with such knowledge are nimble, capable of migrating insights and strategies across disparate contexts. Their expertise becomes a bridge between domain-specific demands and universally applicable database principles, rendering them invaluable assets in an era defined by digital transformation and information proliferation.
Systemic Cognition and Relational Fluency
At the core of database mastery lies systemic cognition—a mental architecture that perceives the interdependencies and emergent patterns within complex relational structures. This fluency allows practitioners to anticipate cascading effects when altering schema, optimize transaction integrity, and orchestrate queries that interact seamlessly across multifaceted tables. The mind becomes an analytical loom, weaving threads of data into coherent, adaptive networks capable of sustaining both operational precision and strategic foresight.
Heuristic Acumen and Decision Ecology
Excellence in data management extends beyond technical competence into the domain of heuristic acumen. Practitioners cultivate an internal decision ecology, where intuition informed by empirical practice guides rapid problem-solving. Encountering ambiguous or unprecedented scenarios, the expert leverages learned heuristics, balancing efficiency with analytical rigor. Each interaction with data thus becomes an exercise in both creativity and pragmatism, where cognitive agility underpins operational mastery.
Experiential Scaffold and Conceptual Entrenchment
Conceptual understanding solidifies when theory is scaffolded upon deliberate, repeated practice. Designing mock databases, stress-testing queries, and simulating transaction anomalies embeds knowledge within cognitive circuits, transforming abstract concepts into instinctive responses. This entrenchment ensures that under the pressure of examination or professional exigency, complex relational queries and optimization strategies emerge naturally, bypassing conscious deliberation and fostering seamless problem resolution.
Meta-Learning and Cognitive Refinement
Meta-learning—the conscious study of how one learns—enhances both efficiency and depth of comprehension. By analyzing personal learning patterns, identifying optimal retention techniques, and iteratively refining study methodologies, candidates cultivate a self-sustaining cycle of intellectual enhancement. This approach transcends superficial memorization, enabling practitioners to internalize principles, adapt to evolving technologies, and approach data challenges with a resilient, strategic mindset.
Experiential Interleaving and Adaptive Practice
The principle of interleaving—alternating between varied topics and practical exercises—accelerates skill acquisition and consolidates long-term retention. By juxtaposing schema normalization with query optimization, security best practices with transaction management, and theoretical constructs with hands-on simulation, learners develop adaptive cognitive flexibility. This methodology ensures that knowledge remains pliable, readily applicable to novel problems, and robust under the cognitive stressors of high-stakes assessment environments.
Narrative Cognition and Analytical Storytelling
Data mastery is not solely quantitative; it is also narrative in nature. Each dataset conceals a story, a pattern of relationships waiting to be deciphered. Skilled practitioners employ analytical storytelling, interpreting trends, anomalies, and correlations to derive actionable insights. This narrative cognition allows for the translation of raw information into comprehensible intelligence, enabling decision-makers to act on empirical evidence with clarity, confidence, and foresight.
Cognitive Resilience and Stress Calibration
Examinations and high-pressure project scenarios demand cognitive resilience—the capacity to maintain clarity, creativity, and precision under duress. Stress calibration techniques, including deliberate pacing, reflective pauses, and scenario rehearsal, fortify mental endurance. Practitioners learn to navigate cognitive friction without degradation of performance, transforming potential anxiety into focused attention and enhancing both exam outcomes and professional efficacy.
Emergent Patterns and Systemic Insight
Mastery is characterized by the recognition of emergent patterns that transcend individual queries or tables. The practitioner perceives systemic behaviors, performance bottlenecks, and latent interdependencies that inform optimization strategies. This holistic insight allows for proactive interventions, where database architectures are continuously refined, security vulnerabilities preempted, and transactional efficiency maximized. Such pattern recognition elevates practice from procedural execution to strategic foresight.
Iterative Refinement and Excellence Trajectories
Continuous improvement manifests through iterative refinement, where errors, inefficiencies, and suboptimal queries serve as opportunities for deeper learning. Each revision embeds experiential lessons into cognitive architecture, generating an upward trajectory of competence and confidence. This process not only prepares the candidate for examination but cultivates a professional ethos centered on perpetual enhancement, adaptability, and the pursuit of technical elegance.
Ethical Foresight and Professional Integrity
The ethical dimension of database management underpins long-term mastery. Stewardship of sensitive information requires foresight, accountability, and principled decision-making. Practitioners anticipate consequences, enforce rigorous access controls, and cultivate a culture of integrity. Ethical foresight enhances trustworthiness, safeguards organizational assets, and ensures that technical prowess aligns harmoniously with moral responsibility, creating a holistic framework for sustainable professional influence.
Cognitive Alacrity and Problem Deconstruction
Advanced database work demands cognitive alacrity—the ability to dissect complex problems with speed and precision. Breaking down queries, decomposing relational interdependencies, and segmenting transactional flows into manageable units allows practitioners to navigate intricacy without losing systemic perspective. This skill transforms overwhelming datasets into structured, comprehensible components, streamlining both problem resolution and the communication of technical insight to stakeholders.
Cross-Domain Synthesis and Intellectual Hybridity
Database mastery thrives at the intersection of disciplines. Integrating knowledge from systems architecture, algorithmic logic, cybersecurity, and business intelligence produces intellectual hybridity, where cross-domain synthesis generates innovative solutions. Practitioners adept at this synthesis can reimagine traditional database approaches, leverage automation intelligently, and design architectures that anticipate evolving organizational needs, demonstrating versatility that extends well beyond conventional technical skill.
Adaptive Iteration and Cognitive Plasticity
The fluidity of contemporary data environments necessitates adaptive iteration—a dynamic process of testing, modifying, and optimizing in response to shifting conditions. Cognitive plasticity underlies this ability, enabling professionals to abandon rigid methods, experiment with alternative strategies, and internalize lessons from iterative cycles. This adaptability ensures that mastery remains current, flexible, and capable of addressing both anticipated and unforeseen challenges with equal facility.
Heuristic Innovation and Creative Optimization
Innovation in database management emerges from heuristic creativity—devising unconventional approaches to familiar problems. By experimenting with indexing strategies, transaction architectures, or query optimizations, practitioners refine operational efficiency while simultaneously expanding the cognitive toolkit available for future challenges. Creative optimization transforms routine work into intellectual exploration, cultivating an environment where learning and innovation are mutually reinforcing rather than sequential.
Experiential Codification and Knowledge Permanence
Knowledge codification—translating experiences into durable mental schemas—ensures that lessons persist beyond immediate application. Writing, diagramming, and documenting insights converts transient understanding into a structured cognitive framework. This permanence allows the practitioner to revisit, expand, and adapt knowledge over time, embedding a culture of reflection and strategic foresight that anchors lifelong mastery and elevates each subsequent engagement with data systems.
The Strategic Advantage of CIW 1D0-441 in Modern IT Landscapes
In the kaleidoscopic realm of contemporary information technology, CIW 1D0-441 emerges not merely as a certification but as a strategic fulcrum. The credential embodies a dual purpose: it validates technical fluency while simultaneously cultivating an aura of professional authority. Organizations increasingly confront data environments of staggering complexity, where relational databases, cloud architectures, and hybrid systems interlace in a dynamic lattice. In such arenas, certified practitioners act as navigators, translating abstruse data schemas into actionable intelligence.
Proficiency attained through CIW 1D0-441 transcends rote memorization of SQL commands or schema normalization. It fosters a cerebral agility, enabling professionals to anticipate systemic bottlenecks, preempt data anomalies, and orchestrate architectures optimized for both scalability and resilience. This anticipatory aptitude transforms the professional from a mere executor into a strategic advisor, capable of influencing enterprise decision-making at the highest echelons. The certification thereby becomes a conduit for strategic involvement, elevating individuals beyond technical support into advisory roles that shape organizational trajectories.
Navigating Cross-Industry Mobility with Database Expertise
One of the most compelling facets of CIW 1D0-441 is its capacity to facilitate cross-industry mobility. Unlike narrowly specialized credentials, this certification imparts skills that are malleable across a spectrum of domains. Financial institutions require secure, high-performance data systems; healthcare entities depend on precision-driven databases that safeguard sensitive patient information; e-commerce platforms thrive on the orchestration of real-time transactional analytics. In each scenario, the certified professional wields a toolkit that is universally applicable yet sufficiently nuanced to address domain-specific exigencies.
This versatility engenders unprecedented career fluidity. Professionals are no longer tethered to a single sector; they may pivot from fintech to bioinformatics, from enterprise resource planning to digital media analytics, with minimal retraining. The CIW 1D0-441 credential signals not only mastery of technical constructs but also an intrinsic adaptability—a cognitive elasticity that employers prize in a landscape characterized by relentless innovation and shifting technological paradigms.
Amplifying Professional Visibility Through Certification
Beyond the technical realm, the CIW 1D0-441 certification amplifies a professional’s visibility and perceived value within the broader IT ecosystem. Credentials of this caliber serve as social proof, a recognizable emblem of capability that resonates in professional networks and industry forums. Certified individuals often find themselves sought after for mentorship programs, panel discussions, and collaborative ventures, extending their influence beyond the confines of their immediate organizational responsibilities.
Visibility catalyzes opportunity. Professionals garner invitations to high-impact projects, assume leadership positions, and gain entrée into strategic committees where database architecture decisions are pivotal. In effect, certification becomes a multiplier of professional presence, enabling individuals to project influence and expertise in arenas where visibility directly correlates with career acceleration.
Entrepreneurial Horizons Fostered by CIW 1D0-441
The entrepreneurial ramifications of CIW 1D0-441 are equally profound. Database literacy is increasingly recognized as a cornerstone for innovative ventures. Certified individuals possess the technical acumen to architect systems capable of scaling alongside business growth, to optimize data flows for decision intelligence, and to craft analytic dashboards that transform raw information into predictive insights. These capabilities underpin the creation of value propositions that are both robust and market-responsive, providing certified professionals with the latitude to launch startups, offer consultancy, or pioneer niche data-driven solutions.
Entrepreneurship in the data domain demands both creative foresight and meticulous execution. CIW 1D0-441 cultivates both attributes. The professional emerges as a dual-force: imaginative in conceptualizing innovative data solutions, and methodical in executing scalable, maintainable architectures. This duality not only elevates entrepreneurial potential but positions certified individuals as indispensable actors in shaping the technological contours of emergent enterprises.
Enhancing Analytical Cognition Through Structured Learning
CIW 1D0-441 does not merely teach technical procedures; it cultivates analytical cognition. Candidates learn to dissect complex datasets, discern latent patterns, and construct relational models that anticipate operational contingencies. This mode of thinking extends beyond databases; it informs strategic planning, operational optimization, and problem-solving across organizational functions. The certification thereby functions as a cognitive enhancer, refining an individual’s ability to process multifaceted information streams, synthesize insights, and recommend solutions with precision and authority.
The capacity for analytical synthesis engendered by CIW 1D0-441 is increasingly prized in contemporary workplaces. Organizations seek professionals who can traverse data silos, anticipate interdependencies, and design interventions that maximize efficiency and reduce systemic fragility. Certified specialists, armed with these skills, occupy a privileged position, bridging the gap between raw technical capacity and executive-level decision intelligence.
Leadership Development Anchored in Technical Mastery
The intersection of technical mastery and leadership is another dimension illuminated by CIW 1D0-441. Professionals who couple database expertise with strategic vision often transition into roles that influence enterprise architecture, project management, and technological governance. The certification confers not only knowledge but credibility, legitimizing a professional’s counsel in high-stakes contexts. As leaders, certified individuals can mentor junior engineers, guide cross-functional teams, and formulate policies that optimize data utilization without compromising security or integrity.
Leadership founded upon technical proficiency carries an intrinsic authority. Colleagues and stakeholders recognize the depth of knowledge validated by CIW 1D0-441, fostering trust and engendering deference to informed judgment. In this sense, the certification serves as a lodestar, orienting both individual career trajectories and organizational outcomes toward excellence, innovation, and strategic coherence.
Global Relevance and Industry Recognition
CIW 1D0-441 also confers global portability. In an era where technological talent is a transnational commodity, a credential recognized across borders significantly enhances employability and career mobility. Multinational corporations and international enterprises acknowledge the rigor and applicability of CIW certifications, allowing certified individuals to access opportunities in diverse geographic and cultural contexts. This international recognition augments professional flexibility, positioning individuals to pursue assignments, collaborations, or relocations that align with both career aspirations and personal development.
The universal applicability of database principles reinforced by CIW 1D0-441 ensures that knowledge is not siloed within regional or sectoral confines. Professionals can translate their expertise seamlessly, leveraging standardized methodologies to address heterogeneous challenges in varied organizational milieus. The certification thus functions as both passport and compass, guiding careers through a globalized and interconnected professional landscape.
Continuous Evolution and Lifelong Learning
Finally, CIW 1D0-441 embodies the ethos of continuous evolution. Information technology is an ever-shifting domain; new database paradigms, cloud infrastructures, and analytic tools emerge with unrelenting frequency. Professionals who attain certification commit to a trajectory of lifelong learning, continuously updating their competencies to remain relevant and effective. This proactive stance toward knowledge acquisition ensures sustained career vitality, allowing individuals to anticipate trends rather than react to them.
The commitment to lifelong learning extends beyond skill acquisition; it nurtures intellectual resilience, curiosity, and strategic foresight. Certified individuals cultivate an iterative mindset, constantly refining methodologies, exploring emergent technologies, and translating new knowledge into practical solutions. In doing so, they secure a professional posture that is both adaptive and influential, capable of navigating the unpredictable currents of technological evolution.
Encryption and the Art of Concealment
In the labyrinthine world of digital ecosystems, encryption emerges as both sentinel and cipher, safeguarding the essence of information from intrusive entities. CIW 1D0-441 imparts a sophisticated comprehension of cryptographic principles, from symmetric algorithms that ensure rapid, efficient concealment, to asymmetric protocols that facilitate secure exchange across decentralized networks. The practitioner's acumen extends to key management, cryptographic agility, and the subtleties of hashing, each a critical pillar in the fortress of data protection. Mastery of these arcane techniques transforms ordinary custodians into adept architects of confidentiality, capable of rendering sensitive information inscrutable to unauthorized observers.
Encryption, however, is not a monolithic panacea. Professionals are taught to integrate cryptography within a larger matrix of security measures, recognizing that algorithmic prowess must harmonize with procedural vigilance. Data at rest, data in transit, and ephemeral computational states all demand bespoke approaches, where context-sensitive encryption schemas safeguard against both conventional and avant-garde threats. This meticulous attention to detail embodies the ethos of CIW 1D0-441, wherein technical precision coalesces with strategic foresight to engender resilient informational environments.
Access Control and the Semantics of Privilege
The architecture of privilege is a nuanced art, requiring careful orchestration to balance accessibility with security. Within the CIW 1D0-441 curriculum, candidates dissect the lexicon of access control—ranging from discretionary models that offer flexibility to mandatory paradigms enforcing rigid policy compliance. Role-based access control emerges as a pragmatic synthesis, delineating permissions along organizational hierarchies while minimizing the vectors of potential compromise. This scaffolding of authority ensures that each stakeholder interacts with data in accordance with both necessity and propriety, preserving integrity while fostering operational efficiency.
The semantics of privilege extend beyond mere authorization. Professionals are trained to audit access logs, discern anomalous patterns, and implement adaptive revocation mechanisms that respond to dynamic organizational exigencies. This vigilance cultivates a living ecosystem of accountability, where the very act of data interaction is both traceable and verifiable. By internalizing these principles, CIW-certified specialists evolve into custodians whose oversight is both judicious and anticipatory, mitigating risk while enabling productive engagement with sensitive information.
Ethical Vigilance and the Philosophy of Data Stewardship
Ethics in database management transcends compliance; it is the philosophical substrate upon which trust and credibility are constructed. CIW 1D0-441 emphasizes the cultivation of ethical vigilance, wherein professionals continually interrogate the implications of their technical decisions. The stewardship of information is thus framed not merely as an operational task but as a moral obligation, one that encompasses fairness, transparency, and respect for individual autonomy. Candidates are encouraged to evaluate the broader societal ramifications of their actions, considering the interplay between organizational imperatives and the rights of stakeholders.
This philosophical orientation is operationalized through scenario analysis, case studies, and reflective praxis, equipping professionals with the discernment to navigate ethical quandaries with nuance. Ethical vigilance is inseparable from technical competence; the most sophisticated security schema is of diminished value if deployed without consideration for privacy, consent, or societal norms. By entwining ethics with expertise, CIW 1D0-441 cultivates professionals capable of both fortifying data and upholding the moral architecture of information governance.
Auditing, Traceability, and the Science of Accountability
Accountability is the sine qua non of responsible database management, and auditing serves as its empirical instrument. Within the CIW 1D0-441 framework, candidates master the design and implementation of comprehensive audit mechanisms, enabling the reconstruction of data interactions with precision and clarity. Traceability is not merely a bureaucratic exercise; it is an epistemic safeguard, ensuring that each access, modification, or transmission of information is documented, verifiable, and reproducible. Such rigor transforms organizational data repositories from passive stores into dynamic systems of accountability.
Auditing encompasses both preventive and detective modalities. Professionals learn to implement real-time monitoring, anomaly detection algorithms, and predictive analytics, which collectively facilitate proactive intervention. The cultivation of this vigilance engenders a culture wherein deviations are promptly identified and remediated, thereby preserving both operational continuity and informational integrity. The mastery of auditing is thus both an art and a science, requiring analytical sophistication, methodological rigor, and an unwavering commitment to organizational stewardship.
Regulatory Cognizance and Legal Literacy
Navigating the labyrinth of data regulation requires more than rote knowledge; it demands legal literacy and strategic foresight. CIW 1D0-441 instills in candidates an intricate understanding of statutes, frameworks, and governance principles that dictate data handling across diverse sectors. Compliance is approached not as perfunctory adherence but as a proactive strategy, harmonizing organizational operations with regulatory expectations while minimizing exposure to liability. Professionals are schooled in frameworks encompassing privacy mandates, sector-specific controls, and cross-border data transfer protocols, thereby cultivating a dexterity essential for modern information management.
The implications of regulatory cognizance extend to organizational design and operational protocol. Compliance mandates influence schema architecture, access hierarchies, and incident response strategies, embedding legal awareness into the structural DNA of database ecosystems. Through case studies and simulated audits, CIW-certified specialists acquire the capability to anticipate regulatory challenges, implement preemptive measures, and sustain operational resilience in the face of evolving legal landscapes. This synthesis of legal insight and technical mastery is a hallmark of ethical and effective database stewardship.
Incident Response and the Architecture of Resilience
Even the most robust defenses cannot render information ecosystems impervious to all contingencies. CIW 1D0-441 emphasizes the importance of incident response as a disciplined, structured practice, transforming potential crises into opportunities for controlled mitigation. Professionals are trained to design response frameworks that encompass detection, containment, eradication, and recovery, ensuring continuity of operations while preserving the integrity of compromised data. This architecture of resilience integrates both technological and human factors, emphasizing coordination, communication, and strategic triage under pressure.
Incident response is both anticipatory and adaptive. Candidates explore threat modeling, simulation exercises, and contingency planning, cultivating a readiness to confront unforeseen challenges with composure and analytical rigor. By internalizing these methodologies, CIW-certified specialists enhance organizational robustness, converting vulnerabilities into teachable moments and fortifying defenses against future incursions. This proactive posture exemplifies the fusion of technical expertise, ethical responsibility, and strategic acumen central to contemporary database management.
Continuous Improvement and the Evolution of Security Practices
The dynamic nature of digital threats necessitates a commitment to continuous improvement. CIW 1D0-441 instills a mindset wherein security is perceived as an evolving discipline, one requiring perpetual refinement of methodologies, protocols, and strategic approaches. Professionals engage in iterative evaluation, benchmarking, and the integration of emerging technologies, ensuring that security postures remain resilient against novel and sophisticated threats. Continuous improvement fosters innovation, prompting the development of novel cryptographic solutions, advanced anomaly detection models, and adaptive access paradigms.
This iterative evolution is complemented by reflective practice, whereby professionals assess the efficacy of policies, learn from past incidents, and anticipate future challenges. By embedding continuous improvement into organizational culture, CIW-certified specialists cultivate systems that are not only secure but agile, capable of responding to the fluid exigencies of the digital landscape. This ethos transforms security from a static safeguard into a living, adaptive practice, enhancing both operational efficacy and ethical stewardship.
Dynamic Queries and Adaptive Data Strategies
In the ever-shifting topography of enterprise data, static queries rarely suffice. Dynamic SQL, the art of constructing executable statements at runtime, provides a mechanism for adaptability, allowing systems to respond to contextual variables and emerging requirements. The sophisticated practitioner learns to generate queries that are both flexible and secure, balancing the power of runtime composition with safeguards against injection attacks and logic errors.
Adaptive data strategies extend beyond syntax to the very philosophy of database interaction. By conceptualizing queries as modular, parameter-driven instruments, professionals cultivate an agile approach to data interrogation. This mindset encourages iterative refinement, experimentation, and continuous alignment with organizational objectives. In environments where business logic evolves rapidly, such flexibility becomes not just advantageous but essential.
Error Detection and Proactive Remediation
No database is immune to anomalies, and the CIW 1D0-441 curriculum instills a proactive stance toward error detection. Mastery of SQL extends beyond execution into the realm of diagnostic foresight. Professionals learn to interpret error messages, anticipate constraint violations, and implement robust exception handling to ensure that operations complete predictably and accurately.
Proactive remediation involves not only correcting issues but designing systems to prevent their recurrence. Triggers, constraints, and validation rules form an interlocking framework that safeguards integrity while allowing controlled evolution of the dataset. The ability to foresee potential points of failure and implement countermeasures distinguishes a master from a technician, transforming reactive problem-solving into strategic foresight.
Leveraging Analytical Functions for Predictive Insights
The advent of analytical functions within SQL represents a paradigm shift in the way data informs decision-making. Cumulative sums, moving averages, and percentiles allow professionals to extrapolate trends and detect subtle deviations that would otherwise remain obscured. CIW 1D0-441 emphasizes the integration of these functions into real-world analyses, cultivating proficiency in generating insights that are both precise and predictive.
When combined with temporal data handling, analytical functions provide the capability to discern cyclical patterns, seasonal fluctuations, and anomalies in longitudinal datasets. This capability is invaluable for forecasting, risk assessment, and strategic planning, enabling organizations to anticipate developments and act preemptively rather than reactively.
Schema Design as a Strategic Imperative
While query mastery is critical, an equally important dimension is the architecture of the database itself. Schema design—the thoughtful organization of tables, relationships, and constraints—forms the foundation upon which all operations are built. The CIW 1D0-441 framework emphasizes normalization and denormalization as strategic tools, balancing efficiency, maintainability, and scalability.
Normalization eliminates redundancy and fosters data integrity, while selective denormalization can enhance performance for read-heavy operations. Professionals adept in these techniques cultivate a dual perspective: they understand both the macrostructure of the database and the microstructure of individual queries. This holistic vision enables systems that are resilient, performant, and adaptable to the evolving landscape of business intelligence.
Advanced Joins for Complex Data Relationships
Beyond basic joins, advanced techniques allow for sophisticated relational manipulations. Self-joins, cross-joins, and multi-table joins empower professionals to extract insights from complex interdependencies within the dataset. When layered with filtering, aggregation, and subqueries, these operations reveal latent relationships that would be invisible to simplistic queries.
The skilled practitioner visualizes data relationships as a network, navigating interconnected nodes with precision. By constructing queries that traverse these networks efficiently, one can answer questions that span departments, business units, or temporal sequences. This capability is indispensable in analytics, fraud detection, and operational optimization, where interrelated factors often dictate outcomes.
Orchestrating Data Transformation Pipelines
Data rarely arrives in pristine form. Transforming raw input into structured, analyzable datasets requires a sequence of operations that may include cleansing, normalization, enrichment, and aggregation. SQL provides a rich toolkit for these transformations, from string manipulation functions to conditional logic and aggregate operations.
Professionals develop pipelines that are both repeatable and adaptable, capable of ingesting diverse sources while preserving accuracy and consistency. These pipelines form the backbone of business intelligence, enabling seamless integration of transactional data with analytical frameworks. Mastery in this domain requires both technical acuity and a conceptual understanding of the lifecycle of data within the enterprise.
Integrating SQL with Emerging Technologies
SQL does not operate in isolation; it is increasingly intertwined with emerging technologies such as machine learning, cloud computing, and real-time analytics. Certified professionals understand how SQL interacts with these ecosystems, enabling seamless integration of traditional relational databases with advanced analytical frameworks.
For example, predictive models can be fed with datasets prepared through SQL pipelines, while cloud platforms offer scalable execution of complex queries on massive datasets. Understanding these interfaces allows the professional to extend the utility of SQL beyond conventional reporting, transforming databases into engines of innovation and competitive advantage.
Temporal Data Management and Historical Analysis
Time is an intrinsic dimension of data, and the ability to manage temporal datasets is a hallmark of advanced SQL practice. Temporal tables, timestamped records, and interval queries allow professionals to analyze trends, reconstruct historical states, and forecast future developments.
Historical analysis facilitates accountability, compliance, and strategic insight. By capturing and querying temporal information effectively, organizations can trace the evolution of key metrics, assess the impact of interventions, and uncover patterns that inform long-term planning. Mastery of temporal data transforms SQL from a reactive instrument into a lens through which the past, present, and future converge.
Ensuring Security and Compliance in Data Operations
With great power comes great responsibility. SQL practitioners must navigate the twin imperatives of accessibility and security. Understanding user privileges, roles, and permissions is critical to safeguarding sensitive information while enabling legitimate analysis.
Compliance frameworks impose additional constraints, requiring meticulous attention to data handling practices, auditability, and encryption. CIW 1D0-441 prepares candidates to integrate these considerations seamlessly into daily operations, ensuring that data is both useful and protected. This fusion of technical proficiency and ethical responsibility elevates the practitioner’s role from technician to guardian of organizational knowledge.
Automating Routine Processes Through Stored Procedures
Stored procedures and functions enable automation of routine tasks, embedding logic directly within the database. These constructs reduce redundancy, ensure consistency, and accelerate execution by minimizing network traffic between client applications and the database engine.
Advanced practitioners leverage stored procedures not merely for efficiency but for governance, embedding validation, logging, and error handling into centralized routines. This approach enhances maintainability, reduces risk of human error, and allows scalable execution of complex workflows. By codifying best practices into procedural logic, professionals create a resilient foundation for enterprise-wide data operations.
The Art of Debugging Complex Queries
Complex queries are rarely error-free on the first attempt. Debugging, therefore, is an essential skill, requiring methodical dissection of logic, stepwise validation of intermediate results, and a keen eye for subtle interactions between clauses.
Effective debugging combines systematic analysis with intuition, identifying not only syntactic errors but also inefficiencies and logical misalignments. By cultivating patience, attention to detail, and strategic testing, professionals transform debugging from a tedious chore into a process of discovery, deepening their understanding of both the database and the underlying business questions it serves.
Harnessing Aggregate Functions for Deep Insight
Aggregate functions are more than simple summations or averages; they are instruments for constructing meaningful narratives from the raw numeric substrate of the database. COUNT, SUM, AVG, MIN, MAX, and their advanced counterparts enable segmentation, benchmarking, and comparative analysis across dimensions of interest.
When paired with GROUP BY, HAVING, and conditional logic, aggregate functions facilitate nuanced interrogations of the data landscape. Professionals skilled in this domain extract insight with surgical precision, uncovering anomalies, trends, and patterns that inform strategy and operational improvement.
The Odyssey of Distributed Databases
In the sprawling expanse of contemporary information systems, distributed databases emerge as architectural odysseys, spanning geographies and networks with an elegance that belies their complexity. CIW 1D0-441 aspirants are introduced to the intricate choreography of nodes, replication protocols, and consensus algorithms. Each shard and replica is a testament to meticulous design, where latency and partition tolerance are delicately balanced against consistency. The challenge is not merely technical; it is philosophical, demanding an appreciation of emergent behavior and the unpredictable vicissitudes of decentralized systems. Mastery of this domain transforms database professionals into orchestrators of digital symphonies that resonate across continents.
The Luminous Realm of Indexing
Indexing is more than an optimization tactic; it is the illumination of latent structure within data. B-trees, hash maps, and composite indexes serve as lenses through which vast tables become navigable and intelligible. Candidates explore trade-offs between write amplification and read efficiency, discovering that each index is both a guidepost and a cost center. The artistry lies in discerning patterns of access, predicting query trajectories, and sculpting the database into a responsive organism that anticipates rather than reacts. Effective indexing transforms ordinary retrieval into instantaneous cognition, a fusion of architecture and prescience.
Encryption and the Aegis of Privacy
In an epoch defined by data proliferation and digital exposure, encryption serves as the aegis safeguarding confidentiality. CIW 1D0-441 curricula immerse aspirants in symmetric and asymmetric cryptography, key management, and hashing strategies. Beyond technical mechanics, the discipline demands vigilance and ethical discernment, as even minor lapses can propagate catastrophic breaches. Encryption is not merely a barrier; it is a covenant with users and organizations alike, a silent vow that sensitive truths remain impervious to intrusion.
The Semantics of Query Planning
The formulation of queries extends beyond syntax into the realm of semantics, where intent must harmonize with execution reality. Candidates dissect optimizer behaviors, execution plans, and cardinality estimations, developing an intuition for how abstract requests traverse the underlying data lattice. Query planning is an exercise in anticipatory cognition, where subtle restructuring can yield exponential gains in efficiency. Here, SQL transforms from a utilitarian instrument into a medium for strategic expression, each clause carefully calibrated to balance complexity and performance.
Procedural Programming within Databases
SQL, augmented by procedural extensions, becomes a medium for computational creativity. Stored procedures, triggers, and functions imbue databases with agency, allowing them to enforce business logic, automate repetitive tasks, and respond autonomously to events. CIW 1D0-441 candidates cultivate fluency in procedural design, learning to orchestrate operations with precision and foresight. This dimension transforms databases from passive receptacles of information into active participants in operational ecosystems, capable of executing intricate sequences without external orchestration.
The Metaphysics of Referential Integrity
Referential integrity is the metaphysical scaffolding upon which relational coherence rests. Foreign keys, constraints, and cascading rules articulate the invisible bonds connecting data, ensuring that each fragment inhabits a logical context. The discipline demands both rigorous attention and philosophical reflection, as violations of integrity ripple across dependent systems, eroding trust and comprehension. Candidates internalize that databases are not merely containers but networks of meaning, where each datum assumes significance only in relation to the whole.
Performance Monitoring as a Cognitive Exercise
Observing database performance is not a passive task; it is a cognitive exercise in pattern recognition and anomaly detection. Metrics, logs, and traces reveal subtle oscillations in throughput, latency, and resource consumption. CIW 1D0-441 aspirants learn to interpret these signals, correlating them with workload patterns and architectural decisions. Monitoring becomes a dialogue with the system, a continuous feedback loop where insights inform optimization, preemption, and adaptive scaling. In this dynamic interplay, vigilance is both art and science, cultivating a mindset attuned to the living rhythm of data.
The Architecture of High Availability
High availability is the discipline of ensuring persistence amid adversity. Clustering, failover strategies, and redundancy mechanisms constitute a lattice of resilience, transforming fragility into reliability. Candidates explore quorum protocols, heartbeat detection, and replication topologies, internalizing principles that guarantee uninterrupted access even amidst node failures. High availability is not simply a technical objective; it embodies a philosophy of anticipatory design, where the inevitability of disruption is acknowledged and mitigated through foresight and meticulous orchestration.
Analytical Ecosystems and Data Warehousing
Databases extend beyond transactional confines into the broader expanse of analytical ecosystems. Data warehousing, OLAP structures, and ETL pipelines facilitate the translation of raw data into actionable insight. CIW 1D0-441 candidates examine star and snowflake schemas, slowly uncovering the elegance with which denormalized structures accelerate complex aggregations. Here, the practitioner becomes both scientist and storyteller, interpreting patterns, trends, and anomalies to illuminate hidden narratives embedded within vast datasets.
Temporal Analytics and Predictive Modeling
The confluence of time and data enables predictive vision. Temporal analytics, moving averages, and trend extrapolation allow organizations to forecast behaviors and anticipate operational exigencies. Candidates learn to structure data for longitudinal consistency, creating schemas that capture not just a moment, but the continuum of evolution. Predictive modeling transforms static repositories into instruments of foresight, enabling decisions to be guided by historical resonance and statistical prophecy.
Integration with Emerging Paradigms
Databases exist within a rapidly evolving technological landscape. CIW 1D0-441 candidates are encouraged to interface with contemporary paradigms such as microservices, event-driven architectures, and cloud-native platforms. Integration requires both technical dexterity and conceptual agility, as practitioners navigate disparate protocols, asynchronous communication patterns, and ephemeral state. The modern database professional transcends isolation, embedding their work within a lattice of interdependent services that collectively define the informational ecosystem.
Cognitive Dimensions of Error Handling
Errors within databases are not merely operational disruptions; they are cognitive challenges demanding reflection, diagnosis, and strategic remediation. CIW 1D0-441 aspirants study transaction rollbacks, exception handling, and alerting mechanisms, cultivating an anticipatory mindset. Each anomaly is interpreted as a symptom of underlying structural or procedural misalignment, requiring both technical intervention and analytical reasoning. Effective error handling transforms the practitioner into a diagnostician, capable of restoring equilibrium while uncovering latent vulnerabilities.
The Poetics of Schema Evolution
Schema evolution is a delicate negotiation between stability and adaptation. Adding columns, modifying types, and migrating data without disruption is a process imbued with both technical exactitude and aesthetic judgment. Candidates internalize that schemas are living artifacts, evolving with business logic and user requirements. Successful evolution requires foresight, simulation, and incremental implementation, ensuring that the database maintains coherence while accommodating emergent functionality.
The Ethos of Responsible Data Stewardship
Above all technical mastery lies the ethos of responsibility. CIW 1D0-441 training instills an unwavering commitment to ethical stewardship, emphasizing privacy, compliance, and conscientious governance. Professionals internalize that databases are repositories of trust, where each access, transformation, and disclosure carries ethical weight. The cultivation of this ethos transforms skilled technicians into principled architects, safeguarding the integrity not only of data but of the human systems that rely upon it.
Analytical Reasoning: Beyond Syntax and Semantics
The essence of database mastery extends far beyond syntactical correctness; it thrives in the realm of analytical reasoning. Professionals who excel in this sphere perceive patterns hidden within labyrinthine datasets, discerning correlations and anomalies that elude casual inspection. Analytical reasoning is a cognitive superstructure that allows one to forecast outcomes, simulate scenarios, and design solutions with anticipatory precision. It transforms mundane data interactions into intellectual adventures, where queries are hypotheses and tables are experimental environments.
This skill is particularly vital in complex database ecosystems where multiple interdependent tables interact in non-linear ways. Understanding not only the immediate output of a query but also its systemic repercussions cultivates a form of intellectual foresight. Such practitioners are not merely operators—they are strategists, capable of transforming abstract datasets into actionable insights that reverberate throughout an organization.
Indexing Strategies: Crafting Pathways Through Data
Indexes are the unsung navigational beacons of databases, guiding queries swiftly through immense seas of information. Crafting effective indexing strategies is less a mechanical task than a meticulous art, requiring comprehension of query patterns, frequency, and relational interdependencies. A poorly designed index may be as obstructive as it is intended to be facilitative, leading to performance degradation rather than acceleration.
Mastery of indexing necessitates an understanding of both physical storage structures and logical access paths. Clustered and non-clustered indexes, composite keys, and covering indexes each provide unique advantages and caveats, their optimal deployment contingent upon the nuanced architecture of the database. Skilled professionals are akin to cartographers of information, charting invisible highways that streamline retrieval and elevate system performance to sublime levels.
Advanced Joins and Data Integration
Joins form the connective tissue of relational databases, bridging discrete tables into cohesive analytical frameworks. Beyond basic INNER and OUTER joins lie sophisticated constructs—self-joins, cross-joins, and recursive joins—that enable multi-dimensional exploration of data. These mechanisms allow for intricate relationships to be modeled and interrogated with surgical precision, revealing insights that single-table analysis could never unearth.
Data integration, the process of synthesizing information from heterogeneous sources, further expands the horizon of relational potential. Effective integration demands proficiency not only in SQL syntax but also in understanding data provenance, consistency, and transformation logic. Professionals adept in these practices can seamlessly merge disparate datasets, transforming fragmented information into unified narratives of business intelligence.
Query Optimization Techniques: The Pursuit of Elegance
Optimization is the apex of database artistry. Beyond the mechanical application of execution plans and indexes lies the pursuit of elegance—a state where queries execute with minimal cost, maximal clarity, and enduring adaptability. Optimization techniques require both retrospection and foresight: analyzing historical query performance while anticipating future usage patterns.
Common strategies include rewriting queries for efficiency, leveraging temporary tables judiciously, and minimizing computational overhead through thoughtful subquery construction. Advanced practitioners employ cost-based optimization principles, interpreting database engine feedback to refine and sculpt queries into forms that are not only functional but exemplary. Optimization thus becomes an intellectual exercise, a demonstration of both technical acumen and strategic artistry.
The Imperative of Data Integrity
In the architecture of modern information systems, data integrity is the invisible scaffolding that supports trust, reliability, and operational continuity. Ensuring integrity involves rigorous enforcement of constraints, meticulous transaction management, and proactive validation mechanisms. It is not merely a technical requirement but a philosophical commitment: a recognition that the value of data is inseparable from its veracity.
Techniques to enforce integrity span from primary and foreign key constraints to triggers and stored procedures that automatically validate and correct anomalies. Professionals who internalize these concepts become guardians of accuracy, preemptively defending against corruption, inconsistency, and systemic fragility. In a world increasingly dependent on data-driven decisions, such stewardship is invaluable.
Performance Tuning: Balancing Load and Efficiency
Performance tuning is the intricate choreography of system responsiveness and resource allocation. It encompasses query refinement, index adjustment, memory configuration, and server-level optimizations that collectively determine how swiftly a database responds under load. Tuning is not merely reactive; it requires anticipatory insight into traffic patterns, query complexity, and potential contention points.
A skilled database specialist approaches tuning with both empirical analysis and creative problem-solving. By simulating workloads, monitoring execution plans, and iteratively refining system parameters, one transforms an ordinary database into a high-velocity engine of operational excellence. This level of mastery distinguishes a competent technician from a strategic asset capable of influencing enterprise outcomes.
Security Architecture: Designing Defensible Systems
Data security is a crucible in which technical knowledge, ethical responsibility, and strategic foresight converge. Beyond encryption and access control lies the architecture of defense: layered, resilient, and adaptive. Security-conscious professionals design databases that anticipate vulnerabilities, monitor anomalies, and respond to threats before they escalate.
Key aspects of security architecture include role-based access, data masking, auditing protocols, and threat modeling. By embedding these principles into the foundational design rather than retrofitting them post hoc, specialists create environments where data is not only accessible to authorized users but protected against unauthorized incursions. In doing so, they fortify the organization’s informational citadel, rendering the database a sanctuary of integrity and trust.
The Cognitive Edge of Certification
Achieving CIW 1D0-441 certification confers more than a credential; it cultivates a cognitive edge. Professionals emerge with a framework for structured thinking, an enhanced capacity for problem decomposition, and a cultivated ability to anticipate systemic interdependencies. The certification encourages a mindset of precision and curiosity, where each query, table, and transaction is examined not only for immediate effect but for systemic resonance.
This intellectual rigor is transferable across technology domains and industry sectors. Whether tasked with optimizing an e-commerce platform, designing analytics frameworks for healthcare, or safeguarding financial transactions, certified specialists possess the mental toolkit to navigate complexity with confidence and creativity.
Conclusion
The CIW 1D0-441 Database Specialist Certification is more than a credential; it is a transformative journey that equips professionals with the knowledge, skills, and mindset required to thrive in a data-driven world. From mastering relational database concepts and SQL proficiency to embracing data security and ethical responsibility, the certification lays a strong foundation for both technical excellence and strategic thinking.
By completing this certification, professionals gain a competitive edge, unlocking diverse career opportunities across industries, enhancing their credibility, and positioning themselves as trusted stewards of information. Beyond immediate career benefits, CIW 1D0-441 fosters lifelong learning, curiosity, and adaptability, ensuring that specialists remain at the forefront of technological innovation.
Ultimately, investing in this certification is an investment in oneself. It empowers aspiring database professionals to not only manage and manipulate data with precision but also to transform it into actionable insights, driving organizational success and personal growth. For anyone looking to carve a meaningful and rewarding path in the world of IT, CIW 1D0-441 is the gateway to mastery, recognition, and enduring impact.