Certification: GCIA
Certification Full Name: GIAC Certified Intrusion Analyst
Certification Provider: GIAC
Exam Code: GCIA
Exam Name: GIAC Certified Intrusion Analyst
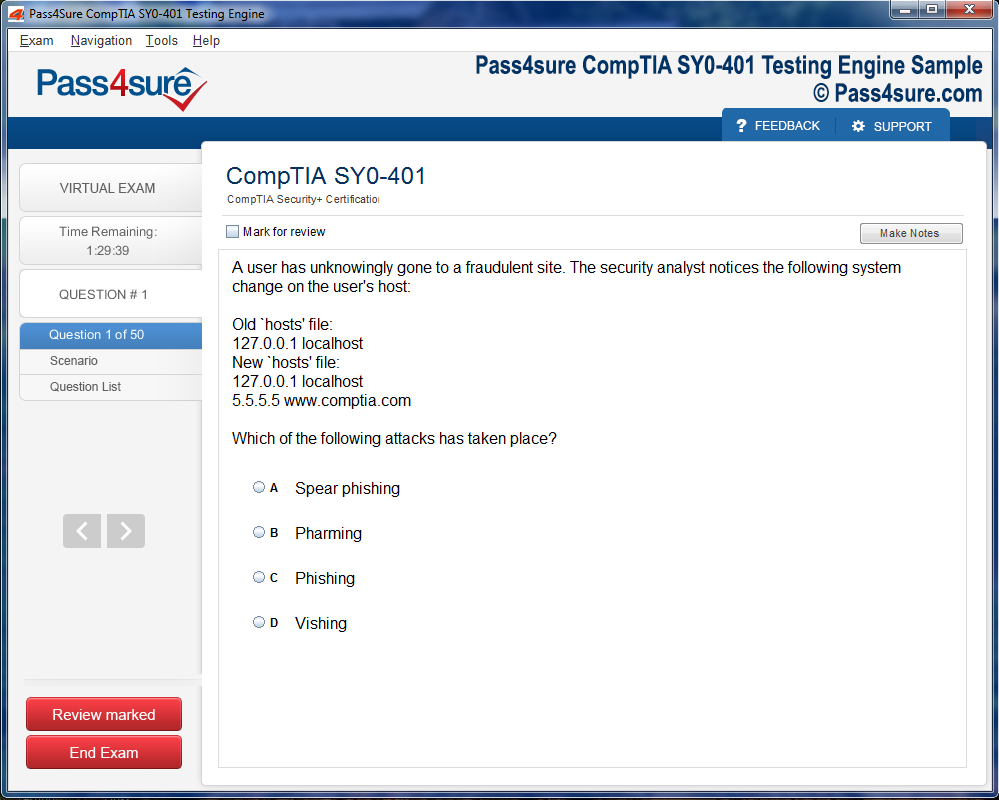
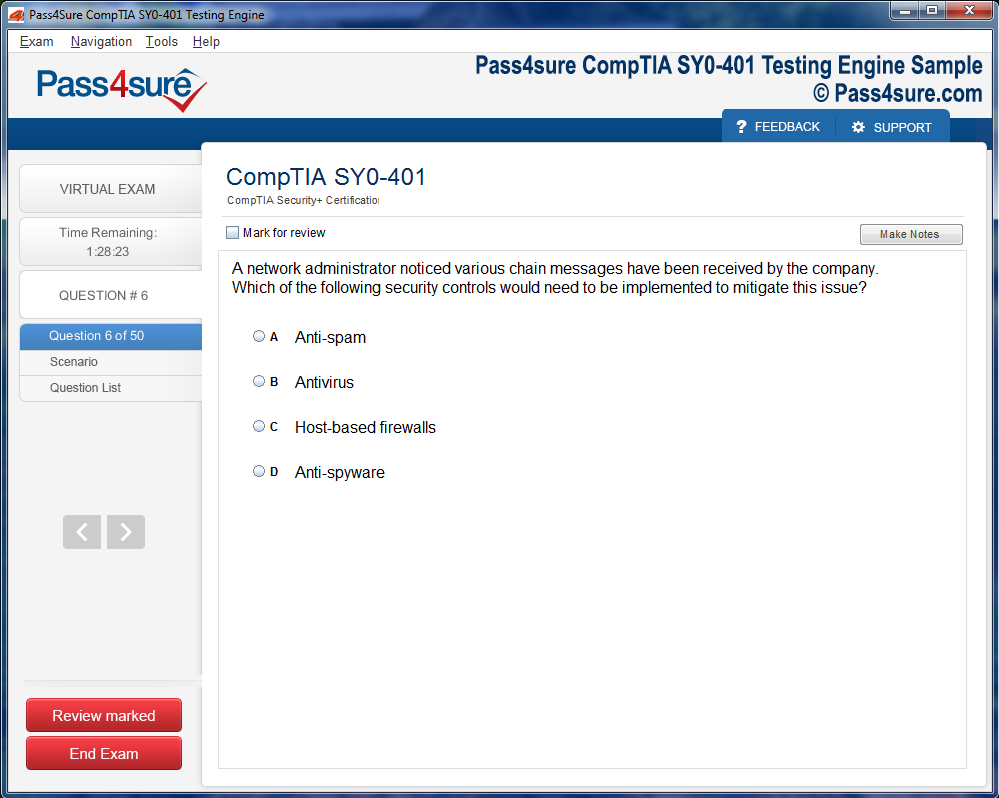
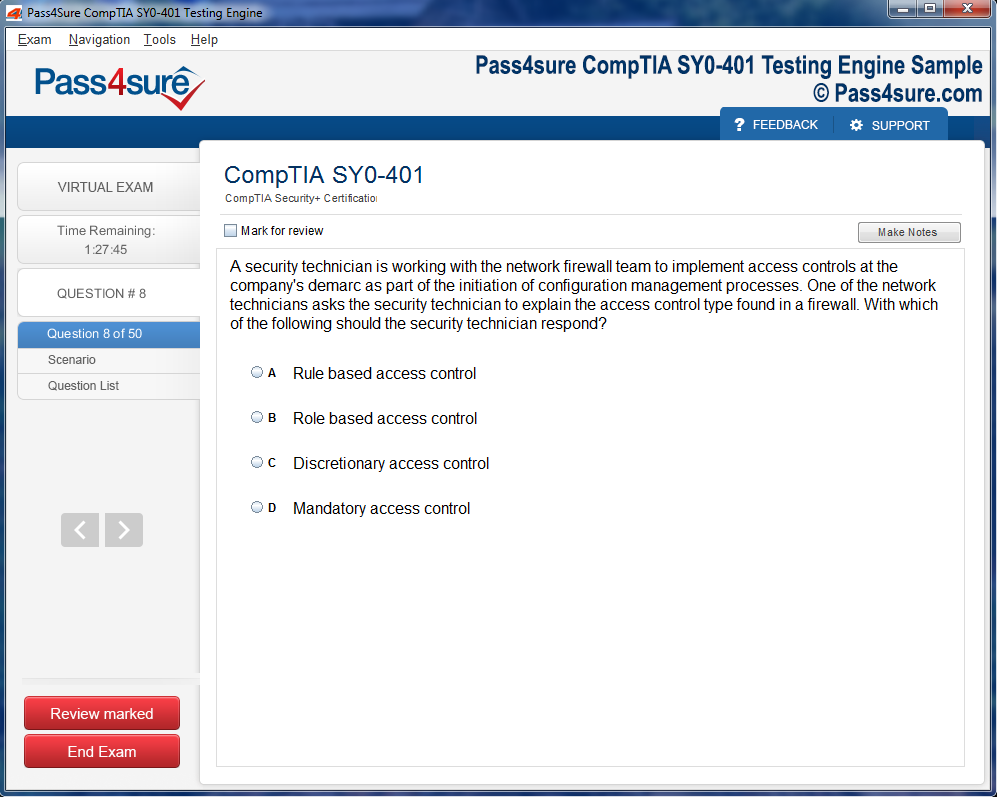
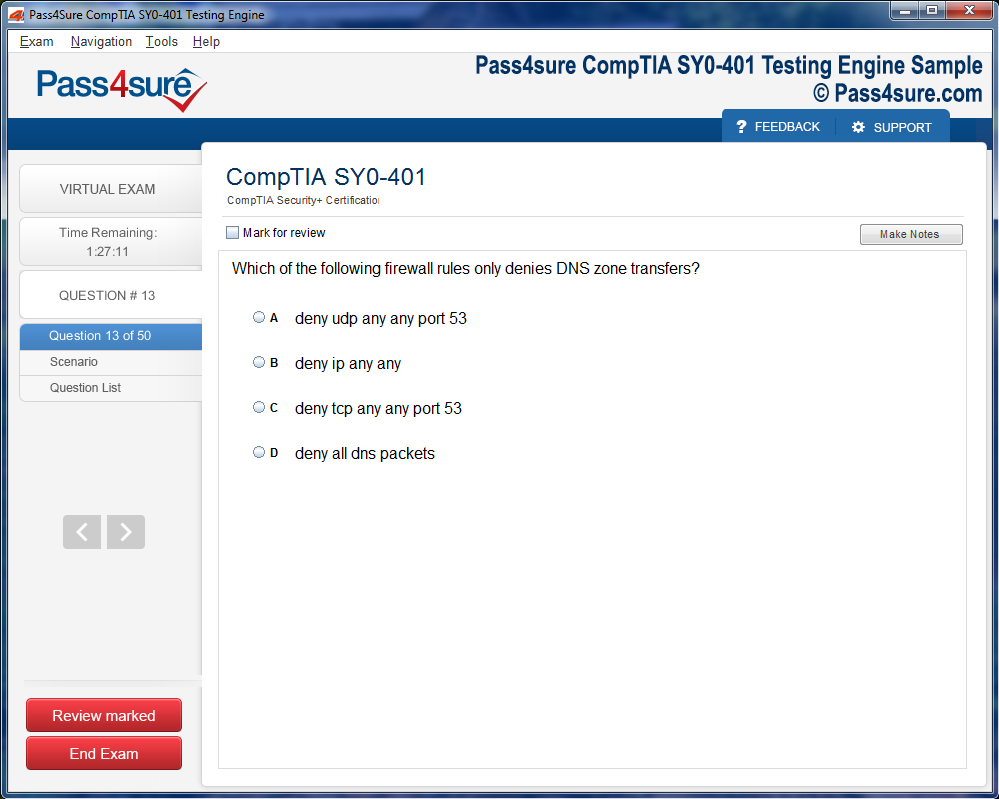
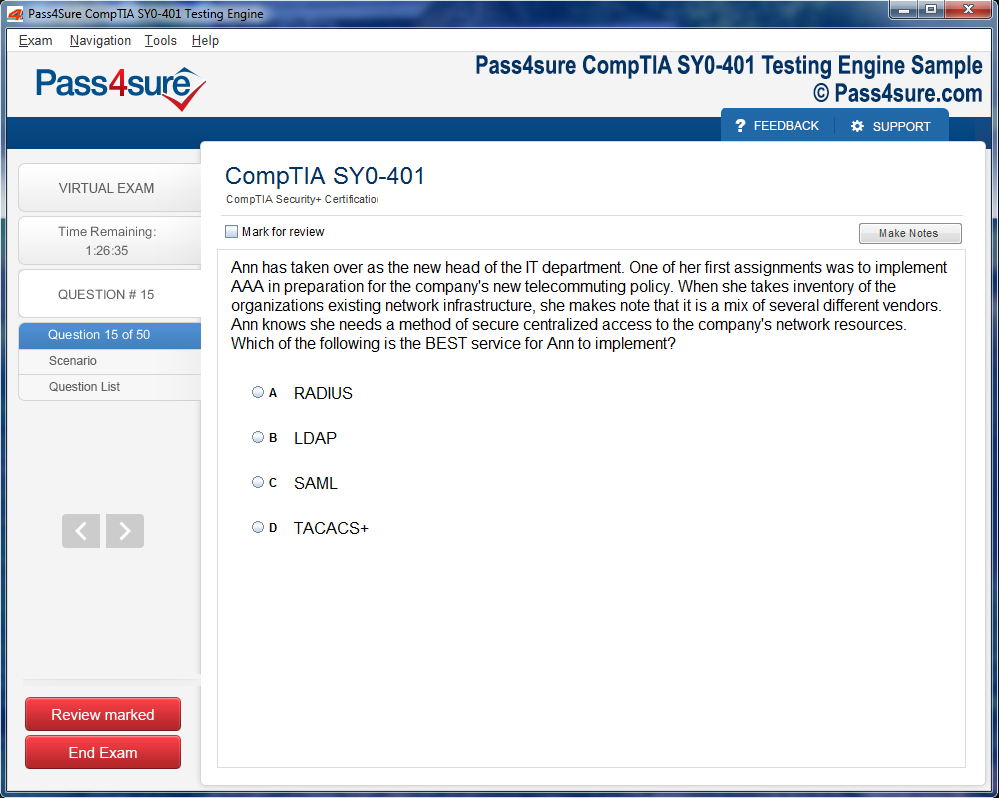
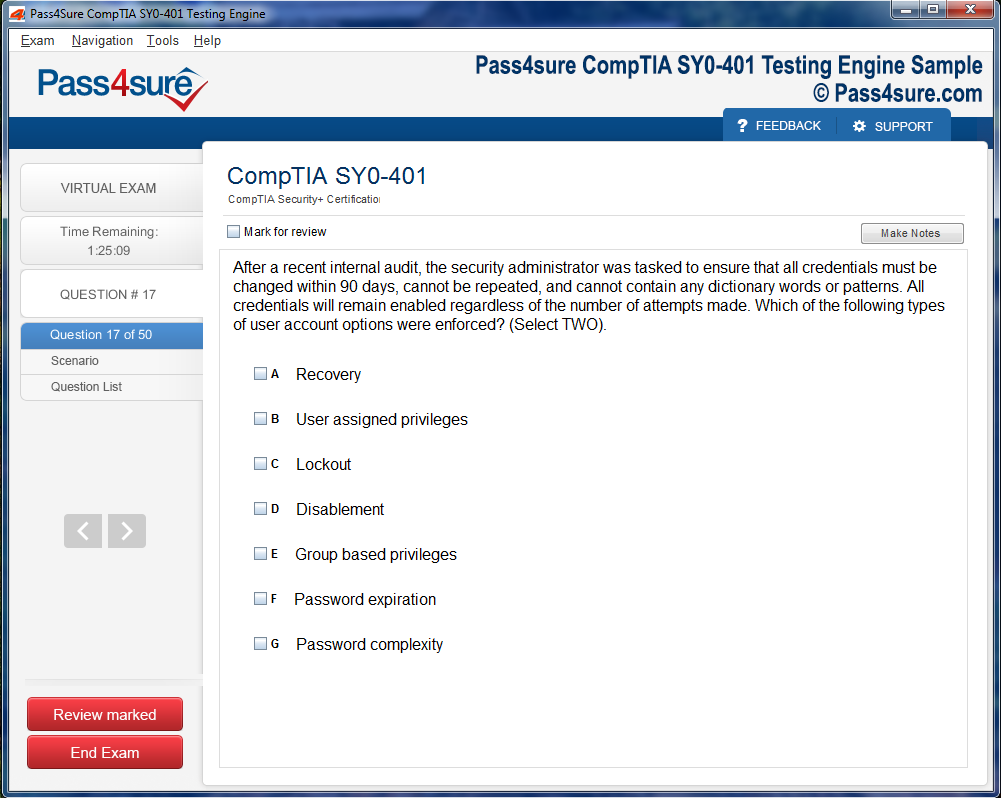
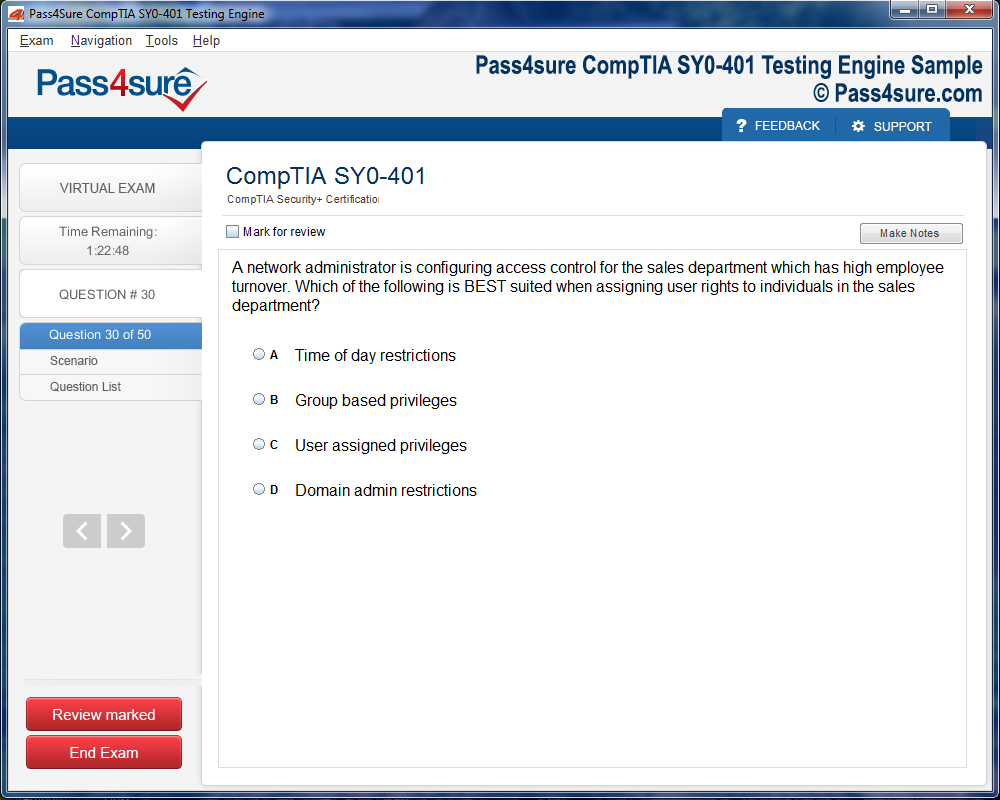
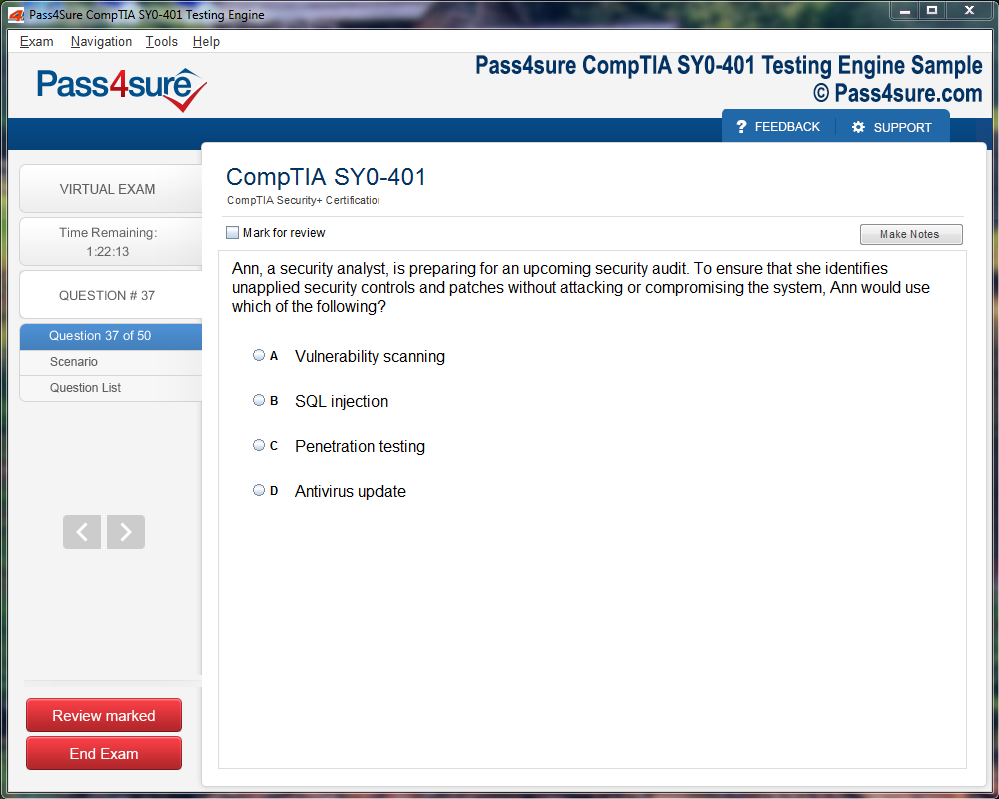
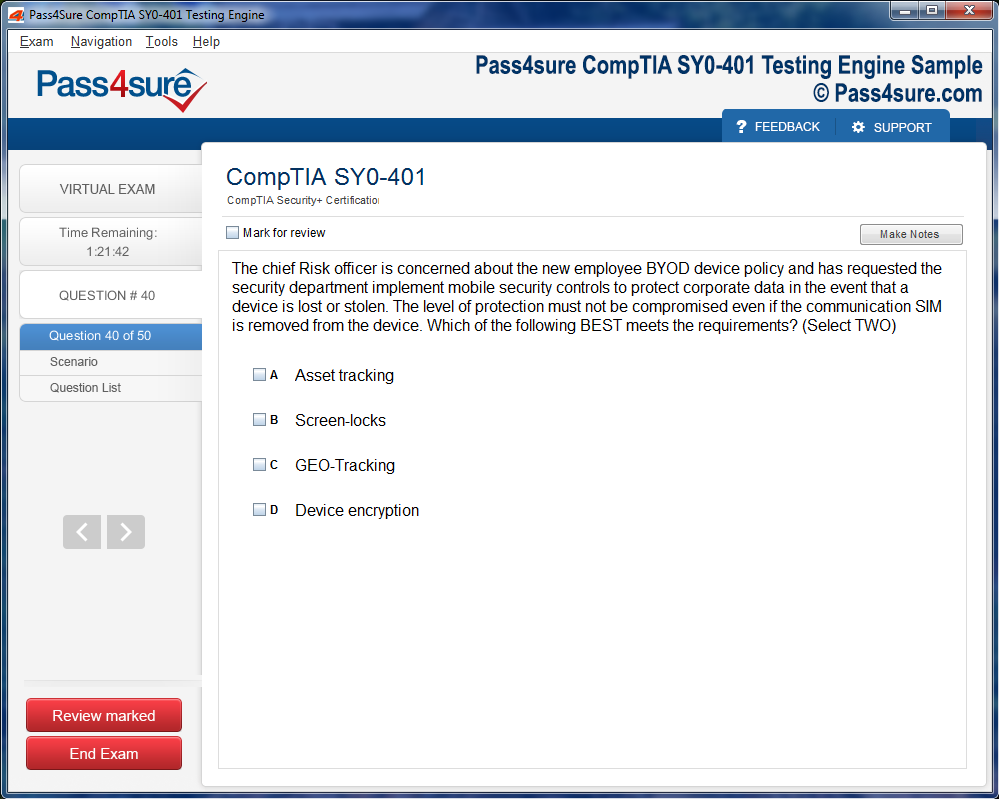
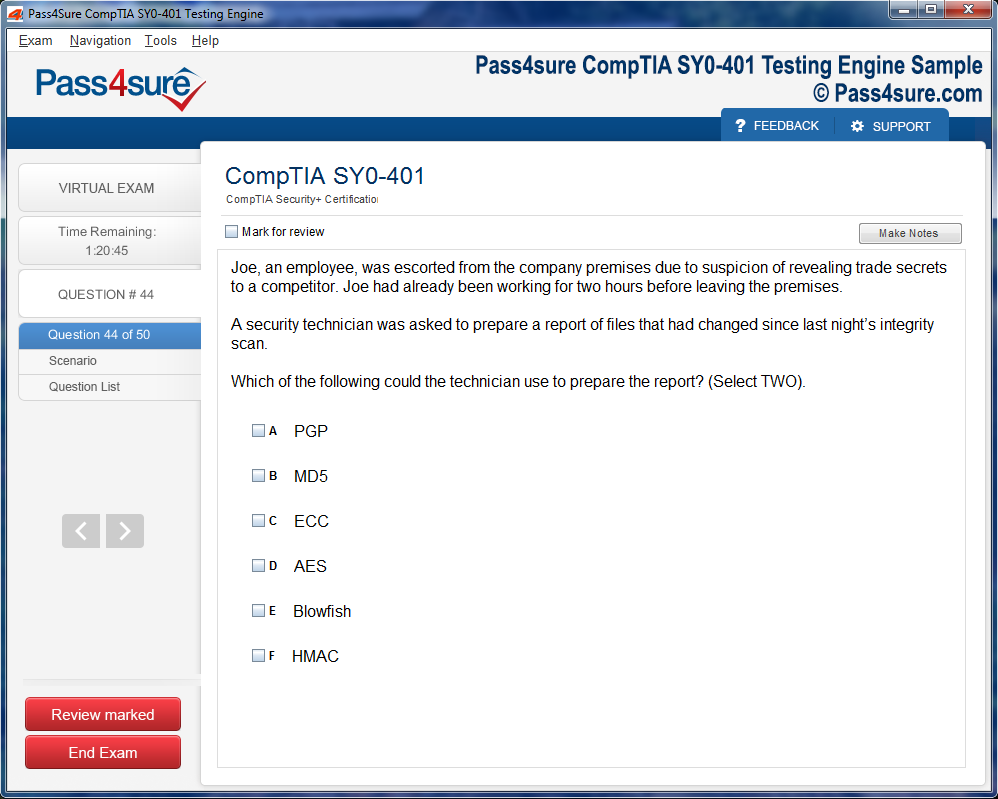
Product Screenshots
Step-by-Step Guide to Excelling in GCIA Certification
As cyber threats continue to evolve, organizations find themselves in a constant state of vigilance, striving to protect their networks from ever-more sophisticated attacks. Intrusion detection, a critical component of modern network security, has become indispensable in the battle to maintain safe digital environments. Professionals with GCIA expertise are particularly valuable in this field, as they possess the skills to identify, analyze, and respond to complex network intrusions. Unlike traditional preventive measures, which focus on stopping attacks before they can infiltrate systems, intrusion detection emphasizes the identification of ongoing or already executed attacks. Its primary goal is not just to prevent but to detect and respond to malicious activities that may already be taking place within the network. A GCIA-certified analyst can enhance this proactive approach, helping organizations quickly identify breaches and take necessary countermeasures to mitigate damage.
Intrusion detection systems (IDS) can be broadly classified into two categories: signature-based detection and anomaly-based detection. Signature-based IDS relies on predefined signatures or patterns of known threats to detect malicious activities. While effective against known attacks, this approach often struggles with identifying new or previously unseen threats. Anomaly-based IDS, on the other hand, focuses on identifying deviations from normal network behavior. By establishing a baseline of typical activity, it can identify unusual behavior that might signal an attack. The advantage of anomaly-based detection lies in its ability to detect novel threats that do not have existing signatures. However, even with a strong anomaly-based IDS, the insights of a GCIA professional are critical for interpreting alerts and minimizing false positives.
Intrusion detection is not merely about identifying malicious activity but also about understanding the intricacies of network protocols and communication. Every network interaction, whether legitimate or malicious, follows certain patterns and rules. Analysts with GCIA training can leverage their deep understanding of packet structures, TCP/IP communication, and network behavior to distinguish between normal and suspicious activity. This technical foundation allows GCIA-certified professionals to not only identify threats but also accurately analyze and assess the context in which these threats occur. Moreover, the GCIA credential signals a high level of proficiency in advanced intrusion detection techniques, enhancing an organization’s overall security posture. By integrating the expertise of GCIA professionals into their security teams, organizations can ensure a more robust defense against evolving cyber threats, while reducing the likelihood of false positives and overlooked attacks.
The Art and Science of Traffic Analysis
Traffic analysis is an essential component of modern cybersecurity, enabling professionals to gain deeper insights into network traffic and detect potential threats. By examining the flow of data between devices on a network, security professionals can uncover hidden patterns, identify unusual behavior, and detect the early stages of an attack. Traffic analysis is a skill that goes beyond simply monitoring network performance; it involves a keen understanding of the structure and behavior of network packets and a familiarity with the tools used to analyze them.
Every packet that travels through a network carries vital information, such as its source, destination, and the type of data being transmitted. Traffic analysis enables security professionals to examine these packets in real time, identify anomalies, and uncover any potentially malicious activity. In practice, traffic analysis tools like Wireshark and tcpdump allow professionals to capture and inspect packets at a granular level. By analyzing these packets, network defenders can detect signs of cyberattacks, such as unusual spikes in traffic, malicious payloads, or unauthorized communication attempts.
One of the key aspects of traffic analysis is packet inspection, which allows professionals to identify hidden threats that might otherwise go undetected. Malicious actors often use sophisticated techniques, such as tunneling or obfuscation, to disguise their activities and evade traditional security measures. Traffic analysis enables security analysts to peel back these layers and expose the true nature of the traffic. For example, by inspecting the headers of packets, analysts can identify irregularities in packet sequencing, unexpected source addresses, or unusual ports, all of which may be indicative of an attack.
Traffic analysis is not just about detecting known threats but also about recognizing abnormal patterns that could signal new or emerging attacks. By correlating different data sources and continuously monitoring network behavior, professionals can develop an acute sense of what constitutes normal traffic. This allows them to more effectively identify anomalies and act quickly to neutralize potential threats before they can cause significant harm.
The Tools Behind Intrusion Detection and Traffic Analysis
The effectiveness of intrusion detection and traffic analysis depends largely on the tools that security professionals use to capture and analyze network traffic. Among the most widely used tools in the field are Wireshark and tcpdump, both of which allow professionals to capture network traffic and dissect it at a granular level. These tools are indispensable for anyone involved in network security, offering the ability to view real-time network activity, analyze packet structures, and identify potential threats.
Wireshark is a network protocol analyzer that enables professionals to capture and interactively browse network traffic. It provides a graphical interface that makes it easier to visualize and interpret packet data, allowing users to filter and drill down into specific packets of interest. Wireshark is an essential tool for network security professionals, as it allows them to perform deep packet inspection and identify anomalies that might otherwise be missed. Whether investigating a potential security breach or analyzing network performance, Wireshark provides the flexibility and depth needed for comprehensive traffic analysis.
Tcpdump, on the other hand, is a command-line packet analyzer that offers a more lightweight approach to network analysis. While it lacks the graphical interface of Wireshark, tcpdump is incredibly powerful and efficient, allowing users to capture packets and filter traffic based on specific criteria. Tcpdump is often used for quick, on-the-fly analysis, particularly in environments where a graphical interface might be too resource-intensive or unnecessary. Despite its simplicity, tcpdump offers a wealth of features that enable professionals to capture detailed information about network traffic and identify potential security issues.
In addition to Wireshark and tcpdump, intrusion detection systems (IDS) themselves play a crucial role in identifying and responding to threats. IDS tools typically use a combination of signature-based detection, anomaly-based detection, and heuristic analysis to monitor network traffic and identify potential attacks. Some of the most widely used IDS tools include Snort, Suricata, and Bro (now known as Zeek). These tools are designed to inspect network traffic in real time and generate alerts when suspicious activity is detected. Each of these tools offers unique features and capabilities, making them suitable for different types of network environments.
Snort, for example, is a highly flexible and customizable IDS that can be configured to detect a wide range of attacks, from buffer overflows to denial-of-service (DoS) attacks. Suricata, a newer IDS tool, is designed for high-performance environments and offers features like multi-threading and hardware acceleration. Zeek, on the other hand, focuses on providing detailed network traffic analysis and offers robust logging and alerting capabilities. By leveraging these tools in combination with packet analysis techniques, security professionals can gain a deep understanding of network activity and respond effectively to threats.
Advanced Intrusion Detection Techniques
While traditional intrusion detection methods are effective at identifying known attacks, modern cyber threats are becoming increasingly sophisticated and evasive. To stay ahead of these threats, security professionals must employ advanced intrusion detection techniques that go beyond simple signature-based detection. These techniques rely on a combination of behavioral analysis, machine learning, and advanced pattern recognition to identify emerging threats and adapt to changing attack strategies.
One such advanced technique is behavior-based detection, which focuses on identifying deviations from established patterns of behavior within the network. By establishing a baseline of normal network activity, security professionals can monitor for unusual behavior that may indicate an attack. For example, an unexpected increase in traffic from a specific device or the sudden appearance of unusual packet types could signal an ongoing attack. Behavior-based detection can help identify zero-day attacks and other threats that may not yet have an established signature.
Machine learning (ML) is another powerful tool in the arsenal of modern intrusion detection. By training algorithms to recognize patterns in network traffic, machine learning models can continuously improve their ability to identify malicious activity. These models can be trained to detect new types of attacks based on the characteristics of previous incidents, enabling them to anticipate and respond to novel threats. As machine learning continues to evolve, its integration into intrusion detection systems is expected to become more widespread, providing greater accuracy and faster detection times.
In addition to behavior-based detection and machine learning, other advanced techniques, such as heuristic analysis and anomaly detection, are playing an increasingly important role in modern intrusion detection systems. Heuristic analysis involves analyzing the characteristics of network traffic to determine whether it is likely to be malicious. This approach can help detect previously unknown attacks by identifying suspicious patterns that do not match normal behavior. Anomaly detection, on the other hand, focuses on identifying outliers or anomalies in network traffic that could indicate an attack in progress.
The Human Element: The Importance of Skilled Security Analysts
While tools and technologies play a crucial role in intrusion detection and traffic analysis, the human element remains indispensable in network security. Skilled security analysts are the ones who interpret the data produced by intrusion detection systems, analyze network traffic, and respond to threats in real time. Without trained professionals who understand the intricacies of network behavior, even the most advanced security tools would be of limited use.
Security analysts must possess a deep understanding of network protocols, security policies, and the tactics employed by cybercriminals. They must be able to analyze large volumes of data quickly and accurately, identify false positives, and make decisions under pressure. In addition to technical expertise, security analysts must also have strong problem-solving skills and the ability to think critically about emerging threats. Their ability to correlate events across different systems, anticipate attack vectors, and respond effectively to incidents is what makes them invaluable assets to organizations.
Moreover, the rapid evolution of cyber threats means that security analysts must constantly update their skills and knowledge. As new attack techniques and vulnerabilities are discovered, analysts must stay ahead of the curve and adapt to changing security landscapes. Continuous training, certifications, and hands-on experience are essential for maintaining the expertise required to excel in this field.
The combination of cutting-edge tools, advanced techniques, and skilled human analysts is what makes intrusion detection and traffic analysis such a powerful defense against cyber threats. As the cybersecurity landscape continues to evolve, the demand for skilled professionals in this area will only continue to grow, ensuring that the protection of networks and critical systems remains at the forefront of digital security efforts.
The Importance of Cybersecurity Certification in Professional Growth
In the fast-paced and ever-evolving field of cybersecurity, hands-on experience is undeniably important, but it is certifications that offer a formal acknowledgment of one's skills, knowledge, and commitment to the profession. Cybersecurity certifications serve as a standardized way of validating expertise, ensuring that professionals are equipped to face the modern challenges that cyber threats present. In this dynamic industry, where threats grow increasingly sophisticated and complex, certifications offer a means to stay ahead, ensuring that knowledge remains current and applicable to real-world scenarios.
Certifications are essential not only because they demonstrate technical expertise but also because they reflect a commitment to continual growth and education in the field. The value of obtaining a certification goes beyond simply enhancing one’s resume; it signals to potential employers, clients, and colleagues that the individual is proficient in the most current practices, tools, and technologies. With the global nature of cybersecurity risks, these credentials play a pivotal role in differentiating professionals who are truly capable from those who merely possess surface-level knowledge.
The acquisition of certifications can significantly boost one's career trajectory. As the demands on cybersecurity professionals grow and the skill set required to protect networks and systems becomes more intricate, obtaining a certification becomes a natural step for anyone who wants to advance. These certifications represent not only an individual’s dedication to the craft but also a promise to uphold the highest standards of cybersecurity and professionalism.
Intrusion Detection and Its Importance in Cybersecurity
At the core of modern cybersecurity lies the concept of intrusion detection—a critical process designed to monitor network traffic for signs of suspicious or unauthorized activity. It is in this realm that certifications like intrusion detection analysis come into play. They train professionals to monitor and interpret network data in order to identify potential threats and security breaches. Certification programs tailored to this skill set provide valuable knowledge on packet engineering, traffic analysis, and event correlation.
An intrusion detection certification enhances one’s ability to detect the earliest signs of an attack. This could involve analyzing network traffic to spot unusual patterns, dissecting malicious code, or implementing various layers of defense mechanisms. It goes beyond just identifying a breach; it empowers cybersecurity professionals with the expertise to preemptively mitigate threats before they become critical. The growing prevalence of targeted attacks, such as advanced persistent threats (APTs), underscores the necessity of specialized intrusion detection skills. These certifications offer professionals a structured and systematic approach to understanding the tools and techniques required to thwart these sophisticated forms of cyberattacks.
The ability to analyze and respond to network intrusions in a timely manner is integral to the success of any organization’s cybersecurity infrastructure. Intrusion detection certificates confirm that the holder possesses the ability to anticipate, analyze, and neutralize security breaches using industry-standard methodologies. This level of expertise is essential for businesses that handle sensitive data, as a well-equipped intrusion detection professional can prevent the catastrophic fallout that a security breach might bring.
Network Monitoring and the Role of Automation in Cyber Defense
As organizations rely more on digital infrastructure and interconnectivity, network monitoring has become one of the most vital components of any cybersecurity strategy. Network monitoring involves continuously observing network traffic to ensure that it operates within expected parameters and that unauthorized activities are flagged immediately. Certification in network monitoring trains professionals to develop and implement surveillance systems capable of identifying potential security vulnerabilities and attack vectors in real time.
In an age where cyberattacks can occur at any hour, automation plays a key role in network monitoring. Network monitoring certifications focus on teaching professionals how to implement automated systems that not only detect but also respond to threats in real time. These automated responses can significantly reduce the time between detecting a threat and mitigating it, providing a fast and effective defense mechanism.
Moreover, network monitoring certifications train professionals to configure systems that generate actionable insights from complex data. The importance of this skill cannot be overstated, as network data can be incredibly voluminous, making it challenging to sift through manually. These certifications guide professionals in filtering out noise and focusing on relevant, actionable data that enhances security measures. As a result, organizations benefit from not only a proactive defense system but also an efficient one that minimizes the strain on human resources.
Expanding Career Opportunities through Specialized Certifications
In the cybersecurity field, specialized certifications open doors to roles that require a high level of expertise and responsibility. While some professionals may start their careers in general security roles, certification can help them transition into more specialized positions that offer greater responsibilities and career advancement opportunities. For example, certifications in intrusion detection and network monitoring provide a pathway to positions such as security analyst, incident responder, network engineer, or even chief security officer (CSO).
Each of these roles requires different levels of expertise in analyzing network traffic, detecting anomalies, configuring firewalls, and responding to incidents. The more specialized the certification, the more focused the career path becomes. For instance, a certification in intrusion analysis not only qualifies an individual to monitor network traffic but also prepares them to identify specific types of attacks, such as SQL injection or malware-based exploits. This expertise is crucial for roles that demand immediate action in high-pressure situations, such as incident responders or security engineers.
The cybersecurity industry is vast, and each area requires a unique set of skills. The range of certifications available enables professionals to focus their careers on specific cybersecurity domains. Whether an individual is interested in network defense, malware analysis, or ethical hacking, certifications provide the tools and knowledge needed to excel in those niches. Specializing in intrusion detection or network monitoring can thus lead to highly rewarding positions where individuals are entrusted with safeguarding the most critical infrastructure of an organization.
The Learning Process and Continuous Growth in Cybersecurity
The cybersecurity industry is in a constant state of flux, with new attack techniques, vulnerabilities, and tools emerging on an almost daily basis. As a result, cybersecurity professionals must engage in continuous learning to stay ahead of the curve. Obtaining certifications is just the beginning of this learning journey, as these credentials typically require professionals to undergo periodic renewal and keep up with the latest trends in the field.
For example, professionals who earn certifications in intrusion detection and network monitoring are often required to take part in continuing education programs to renew their credentials. This encourages a culture of ongoing development and ensures that professionals are always in tune with the latest technologies, methodologies, and best practices. The cyclical nature of certification renewal promotes a mindset of lifelong learning, which is essential in a field as dynamic and rapidly evolving as cybersecurity.
In addition to formal education programs, cybersecurity professionals often participate in workshops, conferences, and hands-on labs to further enhance their expertise. These experiences allow them to engage with the cybersecurity community, learn about emerging trends, and test out new techniques in a controlled environment. This continuous learning cycle enables professionals to adapt quickly to new challenges and ensures that their skills are always in demand.
Certifications as a Credibility Enhancer for Organizations
For organizations, cybersecurity certifications not only validate the skills of individual employees but also contribute to the overall credibility of the company. In an era where security breaches and data leaks are common headlines, clients and stakeholders expect companies to take proactive steps to secure their systems and data. By hiring certified professionals, organizations signal their commitment to protecting sensitive information and preventing potential breaches.
Furthermore, certifications can be an essential part of demonstrating compliance with industry regulations. Many industries, such as healthcare, finance, and government, have strict data protection standards that require companies to follow specific security protocols. Having certified professionals on staff ensures that the organization is not only upholding these standards but also implementing best practices for cybersecurity.
In some cases, certifications may even become a requirement for securing certain contracts or partnerships. Organizations that handle highly sensitive data, such as payment processors or healthcare providers, may only work with companies that employ certified cybersecurity professionals. Thus, obtaining certification can be a strategic advantage for both individuals and the companies they work for, providing an extra layer of trust and reliability in the eyes of clients and regulators.
The Strategic Advantage of Cybersecurity Certifications in a Competitive Market
In the cybersecurity job market, competition is fierce, and employers are looking for professionals who stand out not only because of their experience but also their demonstrated commitment to keeping up with the latest developments in the industry. Cybersecurity certifications are one of the most effective ways to achieve this distinction. They show that a professional has taken the time to master the specific skills required to excel in the field, which is particularly valuable when working with cutting-edge technologies.
For professionals looking to advance in their careers, certifications provide more than just knowledge—they provide a competitive edge. They allow individuals to demonstrate a higher level of expertise than their peers and prove to employers that they are committed to staying current in a field that evolves daily. In highly competitive job markets, where many professionals possess similar experience, a certification can make all the difference between landing a desired position or remaining overlooked.
Employers, in turn, value certifications because they offer a level of assurance that an individual’s skills are recognized and validated by a reputable authority. This means that the hiring process becomes more straightforward, as companies can trust that certified individuals are capable of handling the complex cybersecurity issues that arise in the modern technological landscape.
In a world where the stakes of cybersecurity have never been higher, earning a certification is not just a way to advance one's career; it is a way to make a lasting impact on the security of the organizations they protect. The value of these certifications continues to grow as the digital landscape becomes more interconnected and complex.
Understanding the Importance of Practical Skills in Cybersecurity
While theoretical knowledge lays the groundwork for a strong cybersecurity foundation, practical skills truly define the competency of a cybersecurity professional. No matter how much an individual understands about cybersecurity protocols, tools, and techniques in theory, it is the real-world application of this knowledge that determines effectiveness in safeguarding systems against cyber threats. In particular, fields like intrusion detection and traffic analysis demand hands-on experience for professionals to develop the intuition needed to detect and neutralize threats in complex environments.
In a controlled, simulated environment, cybersecurity professionals have the opportunity to experiment, make mistakes, and refine their skills without the high stakes associated with real-world networks. By engaging in live traffic analysis and intrusion detection exercises, they learn to configure and manage Intrusion Detection Systems (IDS), analyze network traffic in real time, and respond to attacks as they unfold. These skills are vital because they provide the practitioner with a deeper understanding of the intricacies of network behavior and the specific techniques used by cybercriminals to evade detection.
Practitioners who gain proficiency in intrusion detection and traffic analysis possess a keen eye for recognizing network anomalies that could indicate the presence of an attack. This ability to distinguish between legitimate and malicious traffic is indispensable for securing both small and large networks alike. As cyber threats evolve, the need for such hands-on experience only grows more urgent, and the professionals who hone these practical skills are the ones who will be the most adept at mitigating new types of attacks.
Intrusion Detection Systems: The Foundation of Network Security
Intrusion Detection Systems (IDS) serve as the front line of defense in many network security strategies. These systems are designed to monitor network traffic for suspicious activity and respond accordingly. The fundamental skill of a cybersecurity professional is understanding how these systems work, how to configure them effectively, and how to interpret their alerts.
IDS systems operate on a set of predefined rules and signatures that help detect known threats. However, the real challenge comes with detecting unknown or novel attacks, which require more advanced techniques, such as anomaly-based detection and behavior-based analysis. Anomalies in network traffic can indicate a variety of malicious activities, including unauthorized access attempts, privilege escalation, or even advanced persistent threats (APTs). To effectively use IDS, security professionals need to understand the normal baseline of traffic within a network, so that they can accurately detect deviations from this baseline.
Moreover, security experts must also be proficient in tuning IDS to minimize false positives. Without tuning, an IDS system can become overwhelmed with irrelevant alerts, which could potentially lead to a lack of focus on true threats. By understanding the nature of traffic and continuously refining detection signatures, cybersecurity practitioners can ensure that their IDS systems provide the highest level of accuracy and reliability.
Traffic Analysis: Uncovering Hidden Threats
Traffic analysis is a critical skill that expands on the work done by intrusion detection systems. While IDS monitors network traffic for anomalies, traffic analysis involves more in-depth scrutiny of packet-level data to understand the context and implications of suspicious behavior. The ability to analyze and interpret network traffic is a skill that requires both knowledge of network protocols and a deep understanding of how cybercriminals manipulate these protocols to execute attacks.
In a typical network, traffic flows through various devices, each serving a distinct function, such as routers, firewalls, and servers. Each device and the traffic passing through it leaves a digital fingerprint that can be captured, logged, and analyzed. Tools like Wireshark, tcpdump, and Silk allow analysts to capture packets of data as they traverse the network. With these tools, analysts can examine not just the individual packets, but also the larger flow of traffic across time, providing deeper insights into patterns of activity.
Traffic analysis isn't limited to monitoring specific data packets but extends to recognizing broader trends over extended periods. For example, if there is an unusual spike in outbound traffic, it might indicate a data exfiltration attempt. Similarly, patterns of port scanning or large numbers of failed login attempts may signal an impending Distributed Denial of Service (DDoS) attack. By examining traffic over time, security professionals can detect such anomalies early, allowing them to mitigate attacks before they cause significant damage.
The ability to correlate traffic patterns with other security events, such as system logs or application behavior, enhances an analyst's ability to detect complex threats that might otherwise go unnoticed. Combining this skill with intrusion detection creates a robust defense mechanism that allows professionals to catch cybercriminals even before they can strike.
Mastering the Protocols: TCP/IP and Link Layer Concepts
The TCP/IP protocol suite forms the backbone of modern networking, and a deep understanding of these protocols is crucial for effective traffic analysis. Cybersecurity professionals must possess intimate knowledge of TCP/IP, from how individual packets are constructed to how they are transmitted across networks. This understanding allows analysts to spot irregularities in packet construction or transmission, which might indicate an attempt to exploit a vulnerability in the protocol stack.
For example, TCP packets contain a series of flags and sequence numbers that are essential for maintaining the connection between two devices. Attackers often manipulate these fields to launch various types of attacks, such as TCP spoofing or session hijacking. By learning how to interpret these fields, cybersecurity professionals can identify signs of malicious activity in real-time.
The link layer, which operates just below the network layer, is also essential for analyzing traffic. This layer governs how data is physically transmitted over networks, and attacks at this level can often evade detection by traditional network security tools. For instance, attackers may exploit weaknesses in Ethernet or Wi-Fi protocols to inject malicious packets into the network. Therefore, knowing how to scrutinize network interfaces and detect low-level attacks is vital for ensuring a comprehensive security posture.
Anomaly Detection: Moving Beyond Signature-Based Security
Traditional IDS systems rely on signature-based detection, which is effective at identifying known threats but struggles with new or advanced attacks. As cyber threats become more sophisticated, it is crucial to incorporate anomaly detection into traffic analysis. Anomaly detection focuses on identifying irregular patterns in network traffic that may suggest malicious activity, even if the exact nature of the attack is not yet known.
For instance, an attacker might attempt to bypass traditional detection systems by slowly exfiltrating data over a long period of time, making it appear as normal traffic. Anomaly detection systems would catch this by identifying an unusual pattern in the rate of data transfer or by recognizing that a user or device is accessing resources outside of its typical behavior.
By analyzing traffic for deviations from normal behavior, anomaly detection enables cybersecurity professionals to spot even the most subtle attacks. Whether it’s an internal threat, a misconfigured device, or a sophisticated advanced persistent threat (APT), anomaly detection provides an additional layer of protection that is crucial for identifying threats that might otherwise slip through the cracks.
Advanced Traffic Analysis: Fragmentation and Packet Reconstruction
One of the more challenging aspects of traffic analysis is dealing with packet fragmentation. Cybercriminals often fragment their malicious packets to bypass IDS systems and firewalls. This technique, known as fragmentation-based evasion, splits a malicious payload into smaller pieces, making it harder for detection systems to identify it as a threat.
Reassembling these fragmented packets and analyzing them for potential threats is a critical skill for any cybersecurity professional. Using packet reconstruction techniques, analysts can reassemble fragmented packets into their original form to reveal hidden attacks. This process requires a deep understanding of how packet fragmentation works, as well as knowledge of the specific tools used to piece fragmented data back together.
Network forensics, which involves reviewing past events to investigate breaches or vulnerabilities, is another advanced skill in this area. By examining network traffic logs and reconstructed packets, analysts can reconstruct the timeline of an attack, identify its origin, and understand how it progressed through the network. This information is invaluable for preventing future attacks and strengthening the overall security posture of an organization.
Continuous Improvement Through Hands-On Practice
In the realm of cybersecurity, theoretical knowledge alone is not enough to ensure success. The ability to analyze network traffic, configure intrusion detection systems, and respond to real-time incidents is developed through practical experience. By simulating attacks in controlled environments, security professionals can experiment, test strategies, and refine their skills until they can handle even the most sophisticated threats.
Curiosity and persistence are the cornerstones of hands-on learning. As cybersecurity professionals continue to develop their practical skills, they become more adept at spotting subtle anomalies, anticipating attack strategies, and responding to threats swiftly and effectively. These practical experiences allow professionals to build the kind of intuitive understanding of network behavior that is essential for tackling real-world cybersecurity challenges.
Ultimately, the gap between theoretical knowledge and practical expertise is bridged through continuous learning and application. Whether it's through using network monitoring tools, reconstructing fragmented packets, or analyzing traffic patterns, hands-on practice equips cybersecurity professionals with the skills they need to excel in the fast-evolving field of intrusion detection and traffic analysis. As the cyber threat landscape continues to grow more complex, those with a solid foundation in both theory and practice will be best positioned to defend against the next generation of cyber-attacks.
ChatGPT said:
The Ever-Evolving Nature of Cybersecurity
Cybersecurity is a domain where stagnation is the enemy. As technology continues to evolve, so too do the tactics employed by cybercriminals. This constant shift in the threat landscape requires professionals to maintain a dynamic approach to their roles. The key to thriving in this environment is adaptability—both in terms of the tools used and the strategies employed. Cybersecurity is a field that demands continuous learning and evolution, not just in response to new tools and systems but also to the emerging and increasingly sophisticated ways in which attackers exploit them.
At the heart of staying ahead lies a relentless pursuit of knowledge. As new vulnerabilities are discovered and new technologies are adopted, security professionals must ensure their skills are constantly updated. This involves staying abreast of the latest security patches, understanding cutting-edge malware techniques, and acquiring expertise in new methodologies for intrusion detection. Professionals who embrace lifelong learning are those who stand the best chance of being able to both predict and mitigate the effects of a future attack.
While technical knowledge is essential, a deeper understanding of the broader implications of cybersecurity trends can also make a significant difference. Security isn't just about defending against threats—it’s about anticipating them and being prepared for what comes next. The ability to proactively defend against emerging attacks requires professionals to have a vision for the future and an understanding of where the next vulnerabilities might lie. This is a challenge that requires both analytical rigor and creative thinking.
Mastering New Technologies and Protocols
As cyber threats continue to advance, new technologies and protocols emerge that can either help organizations secure their networks or introduce additional vulnerabilities if not properly implemented. Take, for example, the rise of IPv6. While IPv6 adoption has been slow in many regions, it is an important step toward ensuring that the internet continues to grow. For cybersecurity professionals, however, this new protocol presents unique challenges.
IPv6, while offering improved addressing capabilities, also introduces new attack vectors. The sheer size of the IPv6 address space can make it more difficult to manage networks and monitor traffic effectively. Security experts must become well-versed in IPv6 headers, routing, and traffic patterns to effectively manage and secure networks utilizing this protocol. Without this knowledge, attackers may exploit weaknesses in the transition from IPv4, gaining access to sensitive information or causing disruption.
Similarly, advancements in cloud networking, virtualization, and endpoint security present both opportunities and challenges. These technologies offer the potential for improved scalability and flexibility, but they also create new avenues for cybercriminals to exploit. Securing cloud-based infrastructures, for instance, requires a different mindset compared to traditional on-premise security measures. Security experts must develop skills to identify and manage vulnerabilities unique to cloud environments and adopt new strategies for monitoring and detection.
As each of these technologies develops, cybersecurity professionals must continuously refine their skills and adapt to new challenges. The ability to master these technologies is a hallmark of a forward-thinking security professional who is committed to staying ahead of the curve. This is not just about acquiring new knowledge, but also about applying that knowledge in practical, real-world scenarios.
Proactive Threat Hunting and Scenario Planning
The world of cybersecurity is no longer simply about reacting to threats—it is about anticipating them. Proactive threat hunting has become a cornerstone of modern security practices. This approach involves actively searching for signs of malicious activity within an organization's network, rather than waiting for an alert or incident to occur. It is a shift from the traditional reactive model to one that focuses on preemptive action.
This shift requires a unique set of skills. Security professionals must develop an intuitive understanding of what “normal” network activity looks like, so they can spot anomalies that might indicate a potential breach. They must also be adept at creating hypotheses about where threats could emerge and testing those hypotheses through controlled simulations. These activities can help security teams stay one step ahead of attackers and respond more quickly when breaches do occur.
Beyond monitoring networks for signs of intrusion, proactive threat hunting involves scenario planning. By simulating various attack scenarios, security teams can better prepare for real-world incidents. This could involve testing how a network would respond to a distributed denial-of-service (DDoS) attack or how an organization would handle the spread of ransomware. Scenario planning helps teams identify vulnerabilities in their defenses before they are exploited in a real attack.
Engagement in these proactive activities sharpens the skills of security professionals and builds a more resilient security posture. As threats become more targeted and sophisticated, the need for preemptive, scenario-based thinking is more critical than ever. The best security teams don't just wait for something to happen—they actively seek out ways to prevent it from happening in the first place.
Building a Culture of Continuous Improvement
To truly stay ahead in the cybersecurity world, organizations must foster a culture of continuous improvement. Security is not something that is “done” after initial implementation. Instead, it is an ongoing process that requires constant vigilance, learning, and adaptation. This mindset must be ingrained in every level of an organization—from the top executives to the entry-level employees who manage the day-to-day operations.
A culture of continuous improvement involves regularly reviewing and refining security strategies, processes, and tools. It encourages professionals to learn from past incidents and use those lessons to improve future defenses. In addition, it fosters collaboration among different teams, from IT specialists to business leaders, to ensure that security practices are aligned with organizational goals and that vulnerabilities are swiftly addressed.
For individuals working in cybersecurity, this culture means committing to lifelong learning and professional development. There are always new tools, strategies, and attack techniques to learn about. Security certifications, training programs, and workshops play a significant role in maintaining expertise. Whether through formal education or self-driven learning, security professionals must continuously seek to expand their knowledge base.
Moreover, a culture of continuous improvement also embraces innovation. As new technologies and threats emerge, it is vital for security teams to test, evaluate, and adopt cutting-edge solutions. Artificial intelligence (AI), machine learning, and behavioral analytics are increasingly being used to detect and mitigate attacks. Professionals must stay up-to-date with these advancements and understand how they can be applied to strengthen security measures.
The Role of Collaboration and Networking
In a world where threats are constantly changing, collaboration is essential. Cybersecurity professionals cannot operate in isolation; they must work together, share knowledge, and learn from one another. This collaboration takes many forms, from formalized peer groups to informal online forums, but its impact is profound. Security professionals who engage with their peers are better able to stay current with emerging trends and innovations.
Professional networking is also crucial for career growth. Cybersecurity is a complex and specialized field, and the more connections professionals have, the more opportunities they have to learn, collaborate, and share experiences. Engaging with the broader cybersecurity community through conferences, webinars, and online forums provides invaluable insights into what works in the field and what doesn’t. These platforms also expose individuals to new perspectives and innovative solutions that they may not have encountered otherwise.
In addition to peer collaboration, working closely with other departments within an organization is essential. Cybersecurity is not an isolated concern but a cross-functional effort. Coordinating with departments like IT, legal, compliance, and even human resources ensures that security measures are integrated throughout the organization’s operations. This multi-disciplinary approach is vital for creating comprehensive defense strategies that can withstand a variety of threats.
Staying Informed about Global Cybersecurity Trends
The digital landscape is constantly shifting, and so are the threats targeting it. Cybercriminals are not confined to one geographic location or industry; they operate globally, often with sophisticated strategies that cross borders. For security professionals, staying informed about global cybersecurity trends is crucial for anticipating potential threats and adjusting defenses accordingly.
One of the most critical areas of focus for professionals is the rise of nation-state actors. These sophisticated attackers are often highly funded and motivated by political or economic objectives. They can launch cyberattacks that target critical infrastructure, private companies, or government agencies. By staying informed about the activities of nation-state hackers, professionals can better understand the types of threats they are likely to face and develop tailored defense strategies.
Emerging threats such as ransomware-as-a-service, advanced phishing techniques, and supply chain attacks also demand attention. By keeping up with industry reports, threat intelligence feeds, and security advisories, cybersecurity professionals can stay ahead of these trends and prepare their organizations for the latest attack vectors.
Global cybersecurity trends also help security professionals to benchmark their own efforts. By comparing strategies, tools, and outcomes with those of peers in similar industries or regions, security professionals can assess the effectiveness of their current defenses and identify areas for improvement.
ChatGPT said:
Achieving Mastery and Career Growth Through Certification
In the dynamic world of cybersecurity, achieving mastery in areas like intrusion detection and network monitoring requires more than just basic knowledge; it demands continuous learning, hands-on experience, and formal recognition of expertise. Certification serves as a pivotal benchmark, not only validating the skills one has acquired but also setting the foundation for further professional growth. Through structured learning paths and real-world application, certifications guide professionals toward mastery, while simultaneously boosting their credibility in the competitive cybersecurity landscape.
The journey to certification is not merely an academic pursuit. It is a rigorous process that fosters discipline, precision, and critical thinking. In network security, the challenge lies in spotting the subtle irregularities that may indicate a security breach. Certifications ensure that individuals are equipped with the technical abilities and cognitive skills necessary to analyze network traffic patterns, identify potential vulnerabilities, and deploy proactive countermeasures. As technology continues to evolve, the complexity of cyber threats grows, which means that certification plays an essential role in keeping professionals up to date and prepared for any challenge.
For those in the cybersecurity field, mastering intrusion detection and network monitoring represents the pinnacle of expertise. Certifications offer more than just theoretical knowledge; they build the confidence and practical skills needed to apply that knowledge under real-world conditions. With each step in the certification process, professionals gain a deeper understanding of the technologies at their disposal, allowing them to excel in identifying and mitigating increasingly sophisticated threats.
The Role of Certifications in Professional Development
In the realm of cybersecurity, certifications act as a measure of professional development. While formal education provides a broad understanding of the field, it is certifications that allow individuals to specialize and refine their expertise. The cybersecurity domain is vast, encompassing areas like network security, ethical hacking, data protection, and incident response, each of which requires distinct skills. Certifications offer a clear pathway to gaining expertise in specific areas, helping professionals carve out a niche for themselves in the industry.
Certification programs are typically designed to match industry standards and reflect the current demands of the cybersecurity job market. As new threats emerge, so too do specialized certification tracks. Professionals who pursue certifications in areas such as threat detection, security operations, and digital forensics signal their commitment to staying ahead of evolving cyber risks. Employers recognize the value of this dedication, as certified professionals are often more adept at anticipating and mitigating threats before they can cause significant damage.
Furthermore, certifications demonstrate to potential employers that an individual has taken the time to hone their craft. They reflect a commitment to growth and a proactive approach to professional development. In an industry where the stakes are high, where the cost of a security breach can be catastrophic, employers place immense value on individuals who can provide not only technical skills but also a mindset that embraces continuous improvement and readiness.
Building Technical Competence Through Certification
While the soft skills associated with problem-solving, teamwork, and leadership are essential in cybersecurity, technical competence is the bedrock upon which successful careers are built. Certifications provide an invaluable framework for building this technical expertise, helping professionals develop the deep technical knowledge needed to understand complex network environments and to combat sophisticated cyber threats.
The process of preparing for certification exams often involves mastering advanced concepts such as traffic analysis, host monitoring, and vulnerability scanning. These techniques require both theoretical knowledge and practical experience, ensuring that professionals can apply their skills in real-world scenarios. As they progress through certification levels, individuals refine their understanding of network protocols, encryption standards, and intrusion detection systems, which allows them to take on more challenging roles in network security management.
Additionally, certifications provide access to cutting-edge tools and technologies used in the industry. For example, those who hold certifications in network monitoring and intrusion detection are often trained on the latest security software and hardware, providing them with hands-on experience in applying state-of-the-art solutions to real-world problems. This technical competence, coupled with the practical application of tools, positions individuals as experts who can make significant contributions to the organizations they work for.
By continuously advancing their certifications and knowledge, cybersecurity professionals stay at the forefront of their field, which enables them to address emerging threats effectively. Whether the threat comes from external hackers or internal vulnerabilities, professionals with the right certifications are prepared to act swiftly and decisively, preventing damage and ensuring that the organization remains secure.
Career Advancement and Opportunities with Certification
One of the most significant advantages of achieving certification in network security is the wealth of career opportunities it unlocks. The demand for cybersecurity professionals continues to soar as organizations of all sizes grapple with the increasing threat of cyberattacks. With the evolving landscape of technology, new challenges emerge regularly, and businesses require skilled professionals to safeguard their data, infrastructure, and reputations.
The value of a certified professional in the cybersecurity field cannot be overstated. Certifications provide a clear pathway for career advancement, enabling individuals to transition from entry-level positions to more senior roles. For example, professionals who begin their careers as network administrators can leverage certifications to move into specialized roles in security operations or network monitoring, where the demand for expertise is particularly high. As professionals continue to advance through higher-level certifications, they may find opportunities in leadership positions, such as security architect or cybersecurity manager, where they can oversee large-scale security operations and contribute to strategic decision-making processes.
The financial benefits of certification are also significant. Cybersecurity professionals with advanced certifications often command higher salaries compared to their non-certified counterparts. Specialized expertise in areas such as intrusion detection or threat management is highly valued, and employers are willing to pay a premium for professionals who can ensure the security of their networks. As the stakes of cybersecurity continue to rise, certified professionals find themselves in a prime position to negotiate competitive salaries and secure long-term job stability.
Moreover, certification often leads to opportunities beyond traditional roles in corporate environments. For example, professionals with certifications in network security can transition into consultancy, offering their expertise to organizations in need of specialized advice. They may also take on freelance or contract work, providing flexibility and autonomy in their careers. The ability to choose from a wide range of career paths is one of the key benefits of certification, offering professionals the freedom to explore different industries and job functions.
The Path to Specialization and Leadership Roles
As cybersecurity becomes increasingly complex, specialization is becoming an essential aspect of career growth. Professionals who choose to specialize in specific areas, such as network monitoring, threat detection, or incident response, set themselves apart from generalists and gain access to more advanced and lucrative opportunities. Specialization not only enables professionals to deepen their expertise in a particular domain but also positions them for leadership roles within organizations.
In the realm of intrusion detection and network monitoring, for example, specialists are often called upon to manage complex security systems, perform in-depth analysis of network traffic, and respond to potential breaches. These roles require a high degree of technical competence and the ability to work under pressure. As specialists gain experience and advanced certifications, they often transition into leadership positions, where they can guide teams, shape security strategies, and contribute to broader organizational goals.
For those aspiring to leadership roles, certifications can act as a stepping stone to higher positions of influence. Security managers, for instance, are responsible for overseeing an organization’s entire security infrastructure, making critical decisions about technology adoption, and coordinating incident response efforts. To qualify for these roles, individuals often need to demonstrate both technical expertise and leadership capabilities. Advanced certifications, along with experience in managing complex security operations, can help professionals bridge this gap and move into senior leadership positions.
In addition to technical proficiency, leadership roles often require soft skills such as communication, strategic thinking, and the ability to manage teams effectively. Certification programs that emphasize leadership and management within the cybersecurity field equip professionals with the tools they need to excel in these areas, ensuring that they can lead security teams while also contributing to the larger goals of the organization.
The Continuous Journey of Professional Growth
Mastery in cybersecurity is not a destination but a continuous journey. Even after achieving certifications, professionals must remain committed to lifelong learning and improvement. Cybersecurity is a rapidly changing field, with new technologies, tools, and threats emerging regularly. The most successful professionals in the industry are those who recognize that learning does not stop after obtaining a certification.
In addition to formal certifications, professionals are encouraged to stay engaged with the cybersecurity community, participate in ongoing training, and pursue advanced study in areas of interest. Cybersecurity forums, conferences, and peer networks offer valuable opportunities to exchange ideas, discuss new trends, and stay informed about the latest developments in the field.
Furthermore, the process of solving real-world security problems provides the most valuable learning experiences. Professionals who actively engage with complex network environments and stay involved in security operations gain firsthand knowledge of emerging threats and how to combat them effectively. This practical experience, combined with ongoing education, ensures that professionals are always prepared for the next challenge, whether it involves defending against a sophisticated cyberattack or developing new strategies to protect an organization’s assets.
Conclusion
In summary, achieving mastery in cybersecurity and network monitoring is a long-term process that requires commitment, continuous learning, and the acquisition of specialized skills. Through certification, professionals not only demonstrate their technical competence but also position themselves for career growth, specialization, and leadership. By embracing the principles of lifelong learning and applying their knowledge in real-world scenarios, cybersecurity experts can continue to build on their expertise, securing their place as leaders in the ever-evolving field of network security.
Frequently Asked Questions
How does your testing engine works?
Once download and installed on your PC, you can practise test questions, review your questions & answers using two different options 'practice exam' and 'virtual exam'. Virtual Exam - test yourself with exam questions with a time limit, as if you are taking exams in the Prometric or VUE testing centre. Practice exam - review exam questions one by one, see correct answers and explanations).
How can I get the products after purchase?
All products are available for download immediately from your Member's Area. Once you have made the payment, you will be transferred to Member's Area where you can login and download the products you have purchased to your computer.
How long can I use my product? Will it be valid forever?
Pass4sure products have a validity of 90 days from the date of purchase. This means that any updates to the products, including but not limited to new questions, or updates and changes by our editing team, will be automatically downloaded on to computer to make sure that you get latest exam prep materials during those 90 days.
Can I renew my product if when it's expired?
Yes, when the 90 days of your product validity are over, you have the option of renewing your expired products with a 30% discount. This can be done in your Member's Area.
Please note that you will not be able to use the product after it has expired if you don't renew it.
How often are the questions updated?
We always try to provide the latest pool of questions, Updates in the questions depend on the changes in actual pool of questions by different vendors. As soon as we know about the change in the exam question pool we try our best to update the products as fast as possible.
How many computers I can download Pass4sure software on?
You can download the Pass4sure products on the maximum number of 2 (two) computers or devices. If you need to use the software on more than two machines, you can purchase this option separately. Please email sales@pass4sure.com if you need to use more than 5 (five) computers.
What are the system requirements?
Minimum System Requirements:
- Windows XP or newer operating system
- Java Version 8 or newer
- 1+ GHz processor
- 1 GB Ram
- 50 MB available hard disk typically (products may vary)
What operating systems are supported by your Testing Engine software?
Our testing engine is supported by Windows. Andriod and IOS software is currently under development.